Validating Perturbation Effects Across Network Topologies: From Foundational Concepts to Clinical Applications
This article provides a comprehensive framework for researchers, scientists, and drug development professionals to validate perturbation effects across diverse network topologies.
Validating Perturbation Effects Across Network Topologies: From Foundational Concepts to Clinical Applications
Abstract
This article provides a comprehensive framework for researchers, scientists, and drug development professionals to validate perturbation effects across diverse network topologies. It bridges foundational mathematical principles with practical methodological applications in biomedicine, addressing key challenges in troubleshooting and optimization. By exploring rigorous validation and comparative analysis techniques, the content establishes robust protocols for interpreting perturbation responses in biological systems, particularly for drug repurposing and therapeutic target identification. The synthesis of these areas offers a critical roadmap for enhancing the reliability and predictive power of network-based approaches in clinical research.
Theoretical Foundations of Network Perturbation: From Mathematical Frameworks to Biological Interpretations
Perturbation theory in biological networks provides a conceptual and mathematical framework for understanding how targeted interventions, such as gene knockouts or drug treatments, propagate through cellular systems to induce phenotypic changes. This approach moves beyond static network diagrams to model the dynamic and causal relationships between biomolecules, enabling researchers to predict how systems will respond to genetic, chemical, or environmental disturbances [1].
The fundamental premise is that biological networks—including gene regulatory networks (GRNs), protein-protein interaction networks, and signaling pathways—possess architectural properties that determine their sensitivity and response patterns to perturbations. Key structural features include sparsity, modular organization, hierarchical structure, and degree distributions that often follow approximate power-laws, all of which influence how perturbations diffuse through the network [2]. By studying these perturbation effects systematically, researchers can reverse-engineer network architectures, identify key regulatory nodes, and design therapeutic strategies that specifically counteract disease states.
Comparative Analysis of Perturbation Methods
Methodologies and Performance Metrics
The table below summarizes major computational approaches for perturbation analysis in biological networks, highlighting their core methodologies, applications, and relative performance based on recent benchmarking studies.
Table 1: Comparison of Perturbation Analysis Methods in Biological Networks
| Method | Core Methodology | Primary Application | Performance Highlights | Key Advantages |
|---|---|---|---|---|
| Simple Linear Baselines | Additive model predicting sum of individual logarithmic fold changes | Predicting transcriptome changes after perturbations | Outperformed or matched all 7 deep learning foundation models in benchmark studies [3] | Computational efficiency; avoids overfitting; establishes performance floor |
| PDGrapher | Causally-inspired graph neural networks solving inverse perturbation problem | Identifying combinatorial therapeutic targets | Identifies 13.37% more ground-truth targets in chemical intervention datasets than existing methods; trains 25× faster than indirect methods [4] | Direct perturbagen prediction; handles new cancer types robustly |
| Causal Differential Networks | Mapping differences between observational and interventional causal graphs | Identifying intervention targets from single-cell transcriptomics | Consistently outperforms baselines on 7 single-cell datasets; improves causal discovery for soft/hard intervention targets [5] | Handles high-dimensional data with few samples; jointly trained modules |
| Boolean & ODE Modeling | Binary state transitions (Boolean) or continuous differential equations | Understanding EMT and other state transitions | Boolean models identify Zeb1 and Snai2 as most effective perturbation targets for irreversible EMT induction [6] | Captures multistability; models irreversible transitions |
| Belief Propagation | Probabilistic algorithm exploring network model space | De novo signaling network inference from drug perturbation data | Three orders of magnitude faster than Monte Carlo methods; predicts novel efficacious drug combinations [1] | Context-specific models; requires no prior knowledge |
| Graph Convolutional Networks | Learning implicit perturbation patterns from network topology | Perturbation spread prediction in diverse biological networks | 73% accuracy predicting perturbation patterns across 87 biological models (7% improvement over pure topology-based models) [7] | Leverages both topology and biochemical features |
Key Performance Insights
Recent benchmarking reveals that despite the promise of complex deep learning architectures, simple linear baselines remain surprisingly competitive for predicting transcriptional perturbation effects. In a comprehensive assessment of five foundation models and two other deep learning approaches against deliberately simple baselines, none of the sophisticated models outperformed an additive model that predicts the sum of individual logarithmic fold changes [3]. This highlights the critical importance of rigorous benchmarking before deploying computationally expensive methods.
For therapeutic discovery, causally-inspired approaches show particular promise. PDGrapher's direct formulation of the inverse problem—predicting which perturbations will achieve a desired state transition—enables more efficient identification of combinatorial targets than methods that must exhaustively simulate responses across perturbation libraries [4]. Similarly, causal differential networks demonstrate significant improvements in identifying actual intervention targets from high-dimensional transcriptomic data with limited samples [5].
Experimental Protocols for Perturbation Analysis
Network Inference from Systematic Drug Perturbations
This protocol, adapted from Molinelli et al. (2013), enables de novo reconstruction of signaling networks from targeted drug perturbations [1]:
Experimental Setup: Treat cancer cell lines (e.g., SKMEL-133 melanoma) with single drugs and pairwise combinations of targeted therapeutics. Measure system responses through phospho-protein levels, total protein abundance, and cellular phenotypes (e.g., viability) at multiple time points.
Network Modeling: Represent the system using simple nonlinear differential equations of the form:
dxᵢ/dt = ∑ⱼ Aᵢⱼxⱼ + ∑ᵦ Bᵢᵦuᵦ + Cᵢ
where xᵢ represents the activity of species i, Aᵢⱼ represents the influence of species j on species i, uᵦ represents drug perturbations, and Bᵢᵦ represents drug effects.
Model Inference: Apply Belief Propagation (BP) algorithms to efficiently explore the vast space of possible network configurations. BP calculates marginal probabilities for each possible interaction, enabling the identification of the most likely network structures consistent with perturbation responses.
Validation: Test model predictions against experimental data not used in inference. Execute in silico predictions of novel drug combinations and validate experimentally (e.g., PLK1 inhibition verification in RAF-inhibitor resistant melanoma).
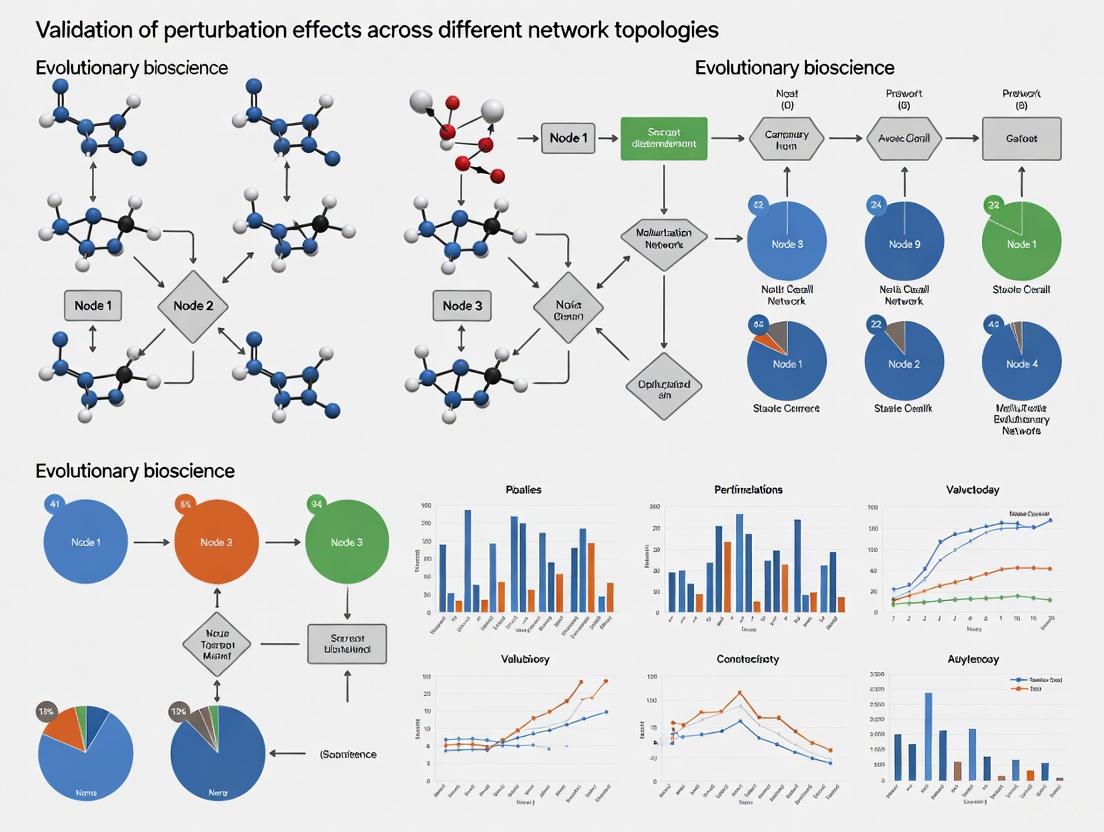
The following diagram illustrates the workflow of this approach:
EMT Network Perturbation Analysis
This protocol analyzes epithelial-mesenchymal transition (EMT) dynamics using both Boolean and ordinary differential equation (ODE) approaches [6]:
Network Specification: Implement a 26-node, 100-edge EMT gene regulatory network incorporating transcription factors, microRNAs, and key markers. Node activities represent epithelial or mesenchymal states.
Boolean Simulations:
- Initialize system in epithelial (E) states through random initialization and selection of low-frustration stable states.
- Apply transient perturbations by clamping specific nodes to target values (ON/OFF states) for duration T with pseudo-temperature noise.
- Remove clamps and simulate to new steady states.
- Score successful EMT transitions as irreversible shifts to mesenchymal (M) states.
ODE Simulations using RACIPE:
- Generate an ensemble of ODE models with randomized parameters consistent with network topology.
- Identify two stable state clusters (E and M) through principal component analysis.
- Apply perturbations by clamping node values to target steady states.
- Analyze transition probabilities and timing under varying noise conditions.
Data Analysis: Quantify perturbation efficacy by success rates across multiple runs. Identify optimal combinatorial perturbations that induce deterministic state transitions even at low noise levels.
The workflow below illustrates the core process:
Network Topology and Perturbation Response Relationships
The architecture of biological networks fundamentally constrains how they respond to perturbations. Key structural properties significantly influence perturbation effects:
Sparsity and Degree Distribution: Most genes are directly regulated by only a small number of transcription factors, with only 41% of transcript-targeting perturbations showing significant effects on other genes [2]. Scale-free topologies with power-law degree distributions create systems where most nodes have limited influence, while a few highly connected hubs disproportionately control network stability.
Hierarchical Organization and Modularity: GRNs exhibit layered structures with clear hierarchical relationships. Modular organization localizes perturbation effects within functional units, with strong intramodule connectivity and sparser intermodule connections. This structure naturally dampens the propagation of random perturbations while allowing specific pathway activation.
Feedback Loops and Motif Enrichment: Biological networks are enriched for specific regulatory motifs, particularly feedback loops that create bistability or oscillatory behavior. Bidirectional regulation occurs in 2.4% of gene pairs with perturbation effects, enabling robust state transitions like EMT [2] [6].
The relationship between network location and perturbation effect is visualized below:
The Scientist's Toolkit: Essential Research Reagents
Table 2: Key Research Reagents for Network Perturbation Studies
| Reagent/Resource | Function | Example Applications |
|---|---|---|
| CRISPR-based Perturbation Systems (Perturb-seq) | High-throughput single-cell genetic perturbations | Genome-scale knockout screens in K562 cells; 11,258 perturbations of 9,866 genes [2] |
| Chemical Perturbagen Libraries (CMap, LINCS) | Libraries of chemical compounds with known targets | Systematic drug combination screening; phenotype-driven drug discovery [4] |
| Single-Cell RNA Sequencing | Transcriptome profiling at single-cell resolution | Measuring perturbation effects across 5,530 genes in 1,989,578 cells [2] |
| Protein-Protein Interaction Networks (BioGRID) | Reference maps of physical protein interactions | Proxy causal graphs for perturbation propagation modeling (10,716 nodes, 151,839 edges) [4] |
| Gene Regulatory Networks (GENIE3) | Inferred transcriptional regulatory relationships | Network structures for causal inference (∼10,000 nodes, ∼500,000 edges) [4] |
| Morphological Feature Extraction Pipelines | Quantitative profiling of cell shape and structure | High-content imaging screens; 267 drug compounds and 35,611 pairwise combinations [8] |
Perturbation theory provides a powerful framework for unraveling the complexity of biological networks, with significant implications for therapeutic development. The comparative analysis presented here reveals that method selection should be guided by specific research objectives: simple linear models offer surprising efficacy for transcriptome prediction, causally-inspired approaches excel at target identification, and Boolean/ODE frameworks capture complex state transitions. Critically, network topology consistently emerges as a fundamental determinant of perturbation response, with hierarchical organization, modularity, and specific motif enrichment shaping effect propagation. As perturbation technologies advance, integrating multi-scale data with sophisticated computational models will continue to enhance our ability to predictively model cellular responses and design targeted therapeutic interventions.
Mathematical Frameworks for Classifying Perturbation Interactions
The accurate classification of perturbation interactions is a cornerstone of modern systems biology, with profound implications for understanding cellular regulation and drug discovery. The core challenge lies in developing mathematical frameworks that can reliably distinguish between synergistic, additive, and antagonistic effects from experimental data. This task is complicated by the intricate topology of biological networks, where interactions are rarely pairwise isolated but instead emerge from complex, higher-order relationships between multiple components. The central thesis connecting various approaches is that a framework's performance is intrinsically linked to how it accounts for the underlying network structure—from simple topologies to multilayer systems—when validating perturbation effects. This guide provides an objective comparison of the dominant mathematical frameworks, their experimental requirements, and their performance in classifying perturbation interactions across different biological contexts.
Comparative Analysis of Mathematical Frameworks
Table 1: Core Framework Comparison for Perturbation Interaction Classification
| Framework | Mathematical Foundation | Network Topology Handling | Interaction Classification Capability | Key Performance Metrics |
|---|---|---|---|---|
| DYNAMO (Topology-Based) | Distance-based propagation models on graph structures | Directed, signed networks; no kinetic parameters required | Predicts perturbation sign and strength patterns | 65-80% accuracy vs. full biochemical models; robust to parameter perturbation [9] |
| DL-MRA (Dynamic Inference) | Dynamic least squares + Modular Response Analysis; Jacobian matrix estimation | Identifies directed, signed edges; feedback/feedforward loops; self-regulation | Infers causal interaction directions and signs from time-series | High specificity/sensitivity for 2-3 node networks; requires 7-11 time points; noise-resistant [10] |
| Information-Theoretic (Synergy) | Multivariate information theory; O-information/S-information | Quantifies irreducible higher-order dependencies beyond pairwise interactions | Classifies redundancy vs. synergy in multi-element systems | Identifies synergy-dominated structures (spheres, toroids) in embedded data [11] |
| CINEMA-OT (Causal Inference) | Potential outcomes framework + Optimal Transport + Independent Component Analysis | Separates confounding variation from treatment effects; handles latent variables | Individual treatment effect estimation; synergy analysis | Outperforms other single-cell perturbation methods; enables counterfactual pairing [12] |
| Deep Learning (PerturbSynX) | Multitask BiLSTM + attention mechanisms; multimodal integration | Incorporates drug-induced gene perturbation with static network features | Drug combination synergy scoring; individual drug response prediction | RMSE: 5.483; PCC: 0.880; R²: 0.757 on synergy prediction [13] |
Table 2: Experimental Data Requirements and Scalability
| Framework | Minimum Data Requirements | Perturbation Type | Measurement Needs | Scalability (Node Count) |
|---|---|---|---|---|
| DYNAMO | Network topology (directed, signed) | Single-node perturbations | Steady-state changes | High (tested on 87 biological models) [9] |
| DL-MRA | n perturbation time courses (n = nodes) | Specific node perturbations | Dynamic time-course measurements | Medium (demonstrated for 2-3 nodes) [10] |
| Information-Theoretic | Joint probability distributions | Natural system variability | Simultaneous multi-variable measurement | Limited by distribution estimation |
| CINEMA-OT | Single-cell RNA-seq under multiple conditions | Experimental treatments | High-dimensional transcriptomes | High (tested on complex single-cell data) [12] |
| PerturbSynX | Drug features + perturbation responses | Drug combinations at varying doses | Gene expression profiles post-perturbation | Medium (cell line specific) [13] |
Experimental Protocols and Methodologies
DYNAMO: Topology-Based Perturbation Prediction
The DYNAMO framework requires four progressively detailed topological descriptions: (1) undirected network, (2) directed network, (3) directed and signed network, and (4) directed, signed, and weighted network. The experimental protocol involves:
- Network Construction: Extract interaction topology from biological databases or experimental data, capturing directionality and sign (activating/inhibiting) of edges [9].
- Sensitivity Matrix Calculation: Compute the sensitivity matrix Sij = dxi/dxj, which quantifies the change in steady-state value of node i when node j is perturbed.
- Perturbation Propagation: Apply distance-based propagation models where a node's perturbation level is proportional to the degree-weighted sum of its neighbors' perturbations.
- Validation: Compare predicted perturbation patterns against those from full biochemical models with known kinetic parameters across 87 biological models [9].
The key advantage is the minimal data requirement—only topological information—while achieving 65-80% accuracy in recovering true perturbation patterns from detailed kinetic models.
DL-MRA: Dynamic Network Inference
DL-MRA requires perturbation time course data to infer signed, directed networks:
- Experimental Design: Perform n distinct perturbation experiments for an n-node network, with each experiment specifically targeting one node. Perturbations should be sufficiently specific to minimize off-target effects [10].
- Time Course Measurement: Collect measurements of all network nodes at 7-11 evenly spaced time points following each perturbation. The framework is robust to experimental noise when using this sampling density.
- Jacobian Estimation: For a 2-node network, the dynamics are described as dx₁/dt ≡ f₁(x₁(k),x₂(k),S₁,ex,S₁,b) and dx₂/dt ≡ f₂(x₁(k),x₂(k),S₂,ex,S₂,b). The Jacobian matrix J containing elements Fij = ∂fi/∂xj is estimated using dynamic least squares optimization across all perturbation time courses [10].
- Network Reconstruction: Extract signed, directed edge weights from the estimated Jacobian, including self-regulation terms (Fii) and external stimuli effects (Si,ex).
This approach successfully identifies feedback loops, feedforward structures, and self-regulation while functioning with realistic experimental noise levels.
CINEMA-OT: Causal Single-Cell Perturbation Analysis
CINEMA-OT applies causal inference to single-cell data through:
- Data Collection: Perform single-cell RNA sequencing on control and perturbed conditions (e.g., drug treatments, gene knockouts) [12].
- Confounder Identification: Apply Independent Component Analysis (ICA) to separate confounding variation (cell cycle, microenvironment) from treatment-associated factors using a Chatterjee's coefficient-based test to identify treatment-correlated components.
- Causal Matching: Implement optimal transport with entropic regularization on the confounder space to find minimal-cost matching between control and treated cells, generating counterfactual pairs.
- Treatment Effect Estimation: Compute Individual Treatment Effect (ITE) for each cell as the difference between its observed state and counterfactual state.
- Synergy Analysis: For combination perturbations (A+B), quantify synergy as the difference between observed effects and the sum of individual treatment effects [12].
The method includes CINEMA-OT-W extension for handling differential abundance (cell death/proliferation) through k-NN alignment and cluster-based rebalancing.
Performance Benchmarking
Topological vs. Dynamical Accuracy
The DYNAMO framework demonstrates that topological information alone captures 65-80% of perturbation patterns compared to full biochemical models with known kinetics. Predictive power increases with topological completeness: directed, signed networks outperform undirected networks, with specific network properties boosting accuracy to the upper end of this range [9]. This performance is robust to kinetic parameter perturbations, suggesting that topological constraints dominate dynamical behavior in many biological systems.
Deep Learning vs. Simple Baselines
Recent benchmarking reveals that deep learning foundation models (scGPT, scFoundation, GEARS) fail to outperform deliberately simple linear baselines in predicting perturbation effects:
Table 3: Deep Learning Benchmarking on Perturbation Prediction
| Model | L2 Distance (Top 1k Genes) | Genetic Interaction Prediction | Unseen Perturbation Generalization |
|---|---|---|---|
| Additive Baseline | Lowest | Cannot predict interactions | Limited |
| No Change Baseline | Intermediate | Poor TPR | Poor |
| scGPT | Higher than baseline | Worse than no-change baseline | No consistent improvement |
| GEARS | Higher than baseline | Poor synergistic prediction | Outperformed by linear model |
| Linear Model with Pretrained P | N/A | N/A | Best performance [3] |
Notably, a simple linear model using perturbation embeddings pretrained on single-cell atlas data consistently outperformed foundation models fine-tuned on perturbation data. The additive baseline (summing individual logarithmic fold changes) outperformed all deep learning models for double perturbation prediction [3].
Causal Inference Performance
CINEMA-OT demonstrates superior performance in treatment-effect estimation compared to existing single-cell perturbation analysis methods across simulated and real datasets. The optimal transport-based matching successfully handles confounding variation, enabling accurate identification of cells with shared treatment response and biologically meaningful synergy detection [12].
The Scientist's Toolkit
Table 4: Essential Research Reagents and Computational Tools
| Tool/Reagent | Function | Framework Application |
|---|---|---|
| Directed, Signed Network Maps | Provides topological constraints for perturbation propagation | DYNAMO, DSGRN [9] [14] |
| Specific Node Perturbors | (shRNA, CRISPRa/i, small molecules) for targeted node perturbation | DL-MRA, experimental validation [10] |
| Time-Course Readout Capability | Measures system dynamics post-perturbation | DL-MRA, dynamic validation [10] |
| Single-Cell RNA Sequencing | High-dimensional transcriptome measurement across conditions | CINEMA-OT, MELD, PerturbSynX [15] [12] [13] |
| Graph Signal Processing Pipeline | Estimates sample-associated density over cellular manifold | MELD algorithm [15] |
| Optimal Transport Algorithms | Computes minimal-cost matching between distributions | CINEMA-OT counterfactual pairing [12] |
| Multitask BiLSTM Architecture | Models complex drug-cell line interactions | PerturbSynX synergy prediction [13] |
| Information-Theoretic Measures | Quantifies higher-order redundancies and synergies | O-information, S-information analysis [11] |
The comparative analysis reveals that no single mathematical framework universally dominates perturbation interaction classification. Instead, performance is highly context-dependent, determined by network topology, data availability, and the specific classification question. Simple topological and linear models often outperform complex deep learning approaches in predicting perturbation patterns, highlighting a significant performance-efficiency tradeoff. Causal inference methods excel when confounding variables are present, while information-theoretic approaches provide the mathematical foundation for quantifying genuine higher-order synergies. Future methodological development should focus on hybrid approaches that combine the interpretability of topological methods with the causal rigor of potential outcomes frameworks, while adhering to rigorous benchmarking against simple baselines to prevent overcomplexification.
The perturbome represents the comprehensive network of interactions between different cellular perturbations, such as those induced by drugs or genetic changes. It provides a systematic framework for understanding how independent perturbations influence each other within the complex machinery of interacting molecules that constitutes a biological system. The core premise of perturbome research is that disease states and therapeutic interventions can be viewed as perturbations of the intricate cellular interactome—the network of molecular interactions within a cell. Understanding the combined effect of independent perturbations lies at the heart of fundamental and practical challenges in modern biology and medicine, from designing effective combination therapies to avoiding adverse drug reactions [16].
The analytical framework of the perturbome moves beyond single-readout measurements (such as cell viability) to capture the full diversity of mutual interactions that arise between perturbations with complex, high-dimensional responses. This approach has revealed that compounds tend to aggregate in specific interactome neighborhoods called "perturbation modules," with 64% of compounds targeting proteins that form connected subgraphs within the interactome significantly larger than expected by chance. The degree of interactome localization strongly correlates with biological similarity: the average functional similarity in terms of Gene Ontology annotations is up to 32-fold higher for strongly localized perturbation modules than for modules whose targets are randomly scattered across the interactome [16].
Comparative Analysis of Perturbation Mapping Technologies
Experimental Approaches and Their Capabilities
Table 1: Comparison of Major Perturbation Mapping Technologies
| Technology | Primary Readout | Perturbation Scale | Interaction Classification | Key Strengths | Network Integration |
|---|---|---|---|---|---|
| Morphological Perturbome | Cell morphology features (high-dimensional) | 267 drugs, 35,611 combinations [16] | 12 interaction types based on vector analysis [16] | Captures complex phenotypic states beyond toxicity | Direct link to protein interactome distance [16] |
| Perturb-seq | Single-cell RNA sequencing | 1,996,260 sequenced cells [17] | Differential expression analysis | High-resolution transcriptional profiling | Gene regulatory network construction [17] |
| Gene Interaction Perturbation Network | Interaction perturbation matrix | 2,167 CRC samples, 2,225 interactions [18] | Six stable network subtypes (GINS1-6) | Robust to expression variability; stable network features | Individual-specific interaction networks [18] |
| Deep Learning Foundation Models | Transcriptome changes | 100 single + 124 double perturbations [3] | Genetic interaction prediction (buffering/synergistic/opposite) | Potential for transfer learning | Limited by current performance vs. simple baselines [3] |
Performance Benchmarking Across Methodologies
Table 2: Quantitative Performance Metrics of Perturbation Technologies
| Methodology | Prediction Accuracy | Experimental Scale | Reproducibility/Stability | Technical Validation |
|---|---|---|---|---|
| Morphological Screening | 92% of compounds show significantly shorter interactome distances between targets [16] | 242 drugs, 1,832 interactions in final network [16] | Functional similarity correlates with network localization (32-fold increase) [16] | Correlation between morphological similarity and target proximity [16] |
| Perturb-seq | 70-80% knockdown efficiency for transcription factors (e.g., NKX2-5) [17] | 193 cardiac promoters/enhancers screened [17] | Strong correlation in knockdown efficiencies across cell lines (R≈0.8) [17] | Robust repression (80-95%) validated by qPCR [17] |
| GIN Subtyping | 1.8% misclassification error with 289-gene classifier [18] | 6 subtypes identified across multiple cohorts [18] | Subtypes reproducible across platforms and sequencing techniques [18] | Significant survival differences (OS, p<0.0001; RFS, p<0.0001) [18] |
| Deep Learning Models | L2 distance higher than additive baseline for all models [3] | 224 perturbations (100 single + 124 double) [3] | Models mostly predicted buffering interactions regardless of true type [3] | None outperformed simple linear baselines or "no change" prediction [3] |
Experimental Protocols for Perturbome Mapping
High-Content Morphological Perturbome Screening
Workflow Overview:
- Perturbation Library: 267 chemical compounds (256 clinically approved) representing diverse mechanisms of action, structural diversity, and targeted biological processes [16].
- Cell Model: Well-controlled cell line model system treated with individual compounds and all pairwise combinations (35,611 total combinations) [16].
- Imaging & Feature Extraction: High-content imaging to profile cellular perturbations in detailed and unbiased fashion. Cell shape characterized by set of morphological features representing point in high-dimensional morphological space [16].
- Vector Representation: Each perturbation represented as vector pointing from unperturbed (DMSO treated) to perturbed (drug treated) state in morphological space [16].
- Interaction Classification: Mathematical framework classifies interactions between perturbations into 12 interaction types based on deviation from expected additive vector [16].
- Interactome Mapping: Integration with comprehensive interactome (309,355 physical interactions between 16,376 proteins) to compute distances between perturbation modules [16].
Key Analytical Framework: The interaction between perturbations is quantified mathematically by characterizing a cell shape through a set of morphological features, representing a point within the high-dimensional morphological space of all possible shapes. A perturbation that changes the shape is identified with a unique vector pointing from the unperturbed to the perturbed state. For any two perturbations, the expected independent effect is a simple superposition of their individual vectors. Any deviation between this expectation and the experimentally observed state indicates an interaction, which can be uniquely decomposed into three components for classification [16].
Perturb-seq in Stem Cell Differentiation Systems
Optimized Protocol:
- CRISPRi Engineered Lines: Generate pluripotent stem cells (H9 ESCs and WTC11 iPSCs) with stably integrated dCas9-KRAB in CLYBL safe harbor locus to ensure robust expression during differentiation [17].
- sgRNA Design & Delivery: Design sgRNAs for efficient on-target repression and detection after scRNA-seq. Compare three delivery methods: lentivirus, PiggyBac transposition, and PA01 recombinase integration [17].
- Differentiation & Quality Control: Directed differentiation to cardiomyocytes or neurons with quality control steps to ensure optimal library coverage and efficient differentiation [17].
- Single-Cell RNA Sequencing: Optimize super loading of cells during library preparation to maximize cell recovery. Sequence nearly 2 million cells across benchmarking datasets [17].
- Network Analysis: Construct gene regulatory networks linking disease-associated enhancers and genes with downstream targets during differentiation [17].
Technical Comparisons: Lentiviral delivery achieved 60-70% knockdown efficiency across cell lines, while PiggyBac transposition showed 80-90% repression in constitutive lines. The recombinase approach achieved ~30% recombination efficiency, comparable to low MOI lentivirus infection. Importantly, strong correlations in promoter knockdown efficiencies were observed across different engineered cell lines, indicating consistent sgRNA-mediated repression [17].
Gene Interaction Perturbation Network (GIN) Subtyping
Methodological Steps:
- Network Construction: Build individual-specific gene interaction perturbation networks using rank-based approach that leverages both gene node information and interaction information [18].
- Feature Selection: Select representative features that significantly distinguish tumor from normal samples and maintain high variability within all tumor samples for clustering analysis [18].
- Consensus Clustering: Apply consensus clustering on discovery cohort (2,167 CRC samples and 2,225 gene interactions) to determine optimal cluster number (K=6) using CDF curve and PAC score [18].
- Classifier Development: Identify 289 subtype-discriminant genes with lowest misclassification error (1.8%) and develop centroid-based classifier using diagonal quadratic discriminant analysis (DQDA) rule [18].
- Validation Framework: Implement "correlation of correlations" step to validate subtypes across different platforms, sequencing techniques, and clinical settings [18].
Signaling Pathways and Network Topologies
Perturbation Module Organization in the Interactome
Perturbation modules are significantly localized neighborhoods within the interactome (64% of compounds form connected subgraphs). The distance (ds) between modules predicts interaction types between corresponding compounds [16].
Perturb-seq Regulatory Network Workflow
Perturb-seq workflow from engineered cell lines to regulatory network inference, highlighting key optimization points for stem cell differentiation systems [17].
Classification of Perturbation Interactions
Mathematical framework for classifying perturbation interactions in high-dimensional space. Any deviation from expected additive effect represents a classifiable interaction [16].
Research Reagent Solutions Toolkit
Table 3: Essential Research Reagents and Platforms for Perturbome Mapping
| Reagent/Platform | Function | Key Features | Validation Metrics |
|---|---|---|---|
| CLYBL-safe harbor engineered lines | Stable dCas9-KRAB expression during differentiation | Constitutive (H9 dCK, WTC11 dCK) and inducible (H9 idCK) variants | 70-80% knockdown efficiency of cardiac TFs; robust across lines [17] |
| sgRNA delivery systems | Multiplexed perturbation introduction | Lentivirus, PiggyBac, PA01 recombinase compared | Lentivirus: 60-70%; PiggyBac: 80-90% repression efficiency [17] |
| Morphological feature extraction | Quantify high-dimensional phenotypic responses | 1,500+ morphological features from high-content imaging | Enables 12-interaction type classification framework [16] |
| Protein-protein interactome | Background network for perturbation localization | 309,355 interactions between 16,376 proteins | 92% of compounds show significantly shorter target distances [16] |
| GIN classifier genes | Subtype-discriminatory gene set | 289-gene centroid classifier | 1.8% misclassification error; validated across platforms [18] |
| Linear baseline models | Performance benchmarking for deep learning | Simple additive and "no change" predictors | Outperformed all foundation models in perturbation prediction [3] |
Validation Across Network Topologies
The validation of perturbation effects across different network topologies reveals fundamental principles of how biological systems integrate multiple perturbations. Research demonstrates a direct link between drug similarities on the cell morphology level and the distance of their respective protein targets within the cellular interactome, with interactome distance being predictive for different types of drug interactions [16]. This network-based understanding enables more rational design of combination therapies by considering the topological relationships between perturbation modules.
The gene interaction perturbation network approach further demonstrates that biological networks remain relatively stable irrespective of time and condition, providing more reliable characterization of biological states than snapshot transcriptional profiles [18]. This stability is particularly valuable for classifying disease subtypes, as evidenced by the identification of six GIN subtypes in colorectal cancer with distinctive clinical outcomes and therapeutic responses [18].
Notably, current deep learning approaches have not yet surpassed simple linear baselines in predicting perturbation effects, highlighting that the goal of providing generalizable representations of cellular states and accurately predicting outcomes of novel perturbations remains challenging [3]. This underscores the continued importance of network-based approaches that explicitly incorporate biological knowledge about interactome structure and organization.
The convergence of multiple perturbation mapping technologies—from morphological profiling to Perturb-seq and network-based subtyping—provides complementary insights into how cellular networks respond to perturbation. The continued refinement of these approaches, with careful benchmarking against appropriate baselines, promises to advance our systematic understanding of the perturbome and its applications in therapeutic development and disease management.
Network topology metrics provide a quantitative framework for analyzing the structure and function of complex systems across biology, technology, and social sciences. In the context of perturbation analysis—whether studying drug effects in biological networks or information flow in social systems—these metrics enable researchers to predict how disturbances propagate through interconnected systems. The architecture of a network fundamentally determines its functional robustness, vulnerability to attacks, and capacity for information processing. As research increasingly focuses on systems-level interventions, such as multi-target drug therapies, understanding these topological principles becomes essential for designing effective strategies that account for network-wide effects rather than isolated component interactions.
Connectivity, centrality, and modularity represent three foundational classes of topological metrics that collectively describe how nodes are linked, which nodes hold strategic importance, and how networks organize into functional subunits. These metrics are not merely descriptive; they offer predictive power for forecasting how perturbations might ripple through a system. Validation of perturbation effects across different network topologies requires a sophisticated understanding of how these metrics interact and influence system dynamics. This guide systematically compares these metric classes, evaluates their applications in perturbation research, and provides experimental frameworks for quantifying their interplay in various network contexts, with special emphasis on biomedical applications where accurately predicting perturbation outcomes can accelerate therapeutic development.
Core Metric Classes: Definitions and Comparative Analysis
Connectivity Metrics
Connectivity metrics form the most fundamental layer of network analysis, describing the basic pattern of links between nodes. These metrics quantify the "wiring diagram" of a network without considering more complex relational patterns. At their simplest, connectivity metrics include node degree (the number of connections a node has) and network density (the proportion of possible connections that actually exist). In directed networks, connectivity further differentiates between in-degree (incoming links) and out-degree (outgoing links), which is particularly relevant for modeling asymmetric relationships common in biological systems like signaling cascades or food webs.
Path-based connectivity metrics offer more sophisticated insights by considering the entire network structure. Average path length measures the typical number of steps required to travel between any two nodes, reflecting a network's overall efficiency in information transfer. Global efficiency represents the harmonic mean of the shortest path lengths, providing a more robust measure that handles disconnected networks. The clustering coefficient quantifies the degree to which nodes tend to cluster together, measuring the probability that two neighbors of a node are also connected to each other. In perturbation studies, networks with high clustering coefficients may localize effects within densely connected modules, while networks with short average path lengths may facilitate rapid perturbation spread throughout the system.
Centrality Metrics
Centrality metrics identify the most influential or critical nodes within a network, going beyond simple connectivity to capture a node's strategic positioning. Different centrality measures employ distinct mathematical approaches to define "importance," making them suitable for different research contexts and perturbation types.
Table 1: Key Centrality Metrics and Their Applications in Perturbation Research
| Metric | Definition | Perturbation Context | Experimental Validation Approach |
|---|---|---|---|
| Degree Centrality | Number of direct connections a node has | Identifies nodes with greatest direct exposure to perturbations | Knockout experiments measuring immediate neighbor effects |
| Betweenness Centrality | Number of shortest paths that pass through a node | Pinpoints critical bottlenecks for perturbation propagation | Pathway disruption tests measuring altered signal flow |
| Closeness Centrality | Average distance from a node to all other nodes | Identifies nodes capable of fastest network-wide influence | Multi-node monitoring of perturbation arrival times |
| Eigenvector Centrality | Influence measure based on connections to well-connected nodes | Finds nodes embedded in influential network cores | Cascade experiments measuring downstream impact magnitude |
| Modular Centrality | Two-dimensional vector separating local (intra-module) and global (inter-module) influence | Critical for modular networks where perturbation effects differ locally vs. globally | Dual-measurement protocols assessing intra- and inter-community spread [19] |
Each centrality metric offers unique insights for perturbation research. Betweenness centrality, for instance, identifies bridges that connect different network regions—their removal can fragment a network and isolate perturbation effects. Closeness centrality spots nodes that can quickly reach the entire network, making them ideal targets when seeking network-wide intervention. The recently developed Modular centrality is particularly valuable for systems with community structure, as it explicitly separates a node's local influence within its module from its global influence across modules [19]. This distinction is crucial in biological systems where a protein might have essential functions within a protein complex (high local centrality) while also connecting to other cellular subsystems (global centrality).
Modularity Metrics
Modularity metrics quantify the extent to which a network organizes into densely connected subgroups (modules or communities) with sparse connections between them. The standard modularity index (Q) measures the difference between the actual number of intra-module links and the expected number in a randomized network with the same degree distribution. Networks with high modularity (typically Q > 0.3) display strong community structure, which profoundly affects how perturbations propagate.
In highly modular networks, perturbations tend to be contained within their originating module due to the sparse inter-module connections. This containment effect has been experimentally demonstrated in neural systems, where the primary visual cortex (V1) reorganizes its modular architecture in response to different sensory inputs [20] [21]. During unimodal visual stimulation, V1 networks exhibit increased betweenness centrality and prominent hub nodes supporting locally modular processing. Conversely, under bimodal visuotactile stimulation, the same networks show reduced modularity with elevated closeness centrality and global efficiency, indicating enhanced integration for cross-modal processing [20] [21].
Module identification algorithms include spectral methods, greedy optimization, and information-theoretic approaches, each with strengths for different network types. Once modules are identified, researchers can calculate module-level metrics such as intramodule connectivity density, participation coefficient (how a node's connections are distributed across modules), and within-module degree (a node's importance relative to its module members). These metrics help predict whether a perturbation will remain localized or propagate network-wide.
Experimental Validation of Metric Performance
Framework for Perturbation-Based Validation
Validating topology metrics requires experimental frameworks that measure how accurately they predict perturbation effects. The general approach involves: (1) constructing a network with known topology, (2) applying controlled perturbations to specific nodes, (3) measuring the propagation patterns, and (4) comparing observed effects with metric-based predictions. The Susceptible-Infected-Recovered (SIR) model has been widely used for this purpose, particularly for validating centrality measures in modular networks [19].
In a typical SIR validation experiment, nodes are ranked by different centrality measures, then "infected" in order of centrality while monitoring propagation dynamics through the network. Comparison of epidemic size (final number of infected nodes) and spreading speed across different centrality rankings reveals which metric best identifies truly influential nodes. Research shows that in networks with strong community structure, the Modular centrality approach outperforms standard centrality measures by separately accounting for local and global influence components [19]. The accuracy gain is most pronounced in networks with medium-strength community structure where both intra- and inter-community links significantly influence dynamics.
DYNAMO Framework for Topological Prediction Accuracy
The DYNAmos-Agnostic Network MOdels (DYNAMO) framework provides a systematic approach for quantifying how much predictive power comes from topology alone versus detailed dynamical parameters [9]. This approach uses an "onion-peeling" strategy that successively removes dynamical information, starting from full biochemical models with known kinetic parameters and progressing to simple topological models using only connectivity information.
Table 2: DYNAMO Framework Predictive Accuracy Across Biological Networks
| Topology Description Level | Information Included | Average Accuracy | Best For Perturbation Type |
|---|---|---|---|
| Undirected Network | Basic connectivity only | ~65% | Local, non-specific perturbations |
| Directed Network | Adds directionality | ~70% | Signal cascade perturbations |
| Directed & Signed | Adds activation/inhibition | ~75% | Balanced regulatory perturbations |
| Full Biochemical Model | Includes kinetic parameters | 100% (reference) | Precise, parameter-sensitive perturbations |
Experiments across 87 biological models with known kinetics demonstrate that simple distance-based topological models can achieve approximately 65% accuracy in predicting perturbation patterns, while incorporating directionality and sign information increases accuracy to 80% [9]. This remarkable predictive power of pure topology suggests that increasingly accurate interactome maps may enable reasonable perturbation predictions without expensive kinetic parameter measurements, particularly for drug target identification where exact dynamics may be secondary to identifying critical nodes.
Dynamic Least-Squares Modular Response Analysis
For networks where time-course perturbation data are available, Dynamic Least-Squares Modular Response Analysis (DL-MRA) provides a robust method for inferring network topology from perturbation responses [10]. This approach requires n perturbation time courses for an n-node system, measuring system responses to perturbations of each node. The method functions well with 7-11 evenly distributed time points and demonstrates robustness to experimental noise.
The DL-MRA workflow involves: (1) perturbing each network node while measuring time-course responses of all nodes, (2) constructing a Jacobian matrix from the response dynamics, and (3) applying least-squares estimation to infer signed, directed network edges. This method successfully handles challenging network features including cycles, feedback loops, self-regulation, and external stimuli—features that often confound simpler correlation-based approaches. Validation studies show DL-MRA accurately reconstructs two and three-node networks even with 10% measurement noise, making it suitable for real-world biological applications [10].
Metric Interdependence in Complex Networks
Network metrics do not operate in isolation; they exhibit complex interdependencies that collectively determine perturbation propagation. Understanding these relationships is essential for accurately predicting system behavior. Several key interdependencies have emerged from experimental studies:
The modularity-centrality trade-off describes how nodes with high participation coefficient (connecting across modules) often exhibit high betweenness centrality but not necessarily high degree centrality. These connector nodes serve as bridges between modules and play disproportionate roles in inter-module perturbation spread. Their removal or perturbation frequently fragments networks and contains perturbations within modules.
The topology-dynamics relationship reveals how static topological features influence dynamic perturbation spread. Research on power grid networks has identified a topological factor that encodes how network structure and base state collectively shape transient responses to perturbations [22]. This factor enables predictions of perturbation arrival times across topologically different networks through a universal scaling function, separating topological determinants from system-specific dynamic properties.
Network reorganization dynamics demonstrate that topology itself may change under different conditions, creating a feedback loop between perturbation and structure. Neuroscience research reveals that the primary visual cortex dynamically reconfigures its topology based on sensory context, shifting from hub-centric, modular architectures during unimodal processing to distributed, integrated networks during multimodal processing [20] [21]. This structural plasticity represents an advanced form of network adaptation to different "perturbation regimes," suggesting that effective interventions may need to account for the target network's capacity for topological reorganization.
Visualization of Network Concepts and Experiments
Modular Centrality Decomposition
Perturbation Spreading Experimental Framework
Research Reagent Solutions for Network Perturbation Experiments
Table 3: Essential Research Reagents for Network Perturbation Studies
| Reagent / Method | Function in Perturbation Research | Example Applications |
|---|---|---|
| AAV9-hSyn-GCaMP6f Viral Vector | Enables calcium imaging of neuronal activity for functional connectivity mapping | In vivo neural network topology studies [20] [21] |
| Two-Photon Calcium Imaging | Records population activity with single-cell resolution | Constructing functional connectivity networks from time-series data [20] [21] |
| Dynamic Least-Squares MRA (DL-MRA) | Computational method to infer signed, directed networks from perturbation time courses | Reconstruction of regulatory networks with cycles and feedback loops [10] |
| shRNA/gRNA Libraries | Enable targeted node perturbations in biological networks | Systematic knockout experiments to validate centrality measures [10] |
| SIR (Susceptible-Infected-Recovered) Model | Computational framework for simulating perturbation spread | Comparing effectiveness of centrality metrics in epidemic settings [19] |
| Jacobian Matrix Construction | Mathematical framework connecting topology to system dynamics | Quantifying direct causal influences between network nodes [9] [10] |
Network topology metrics provide powerful predictive frameworks for understanding perturbation effects across diverse systems, from biological pathways to technological infrastructures. Connectivity, centrality, and modularity metrics each offer complementary insights, with their relative importance depending on network structure and perturbation type. Experimental validation demonstrates that simple topological information alone can predict 65-80% of perturbation patterns, suggesting that increasingly comprehensive interactome maps will enhance our ability to forecast intervention effects without full dynamical models.
The emerging paradigm of context-dependent network topology—where networks dynamically reconfigure their architecture in response to different conditions—adds both complexity and opportunity for perturbation research. The most effective perturbation strategies will be those that account not only for a network's current topology but also its potential for reorganization. As metric development continues, particularly for multi-scale and temporal networks, researchers will gain increasingly sophisticated tools for designing targeted interventions in complex systems, with significant implications for drug development, network resilience engineering, and systems biology.
Linking Interactome Distance to Perturbation Effects and Drug Efficacy
The paradigm of drug discovery is shifting from a single-target, reductionist approach to a network-based perspective that acknowledges the complex interplay of proteins within the cell. A core hypothesis in modern network medicine is that the therapeutic effect of a drug is determined by the network-based distance between its protein targets and the proteins implicated in a disease. This guide provides a comparative analysis of the key computational frameworks that leverage this principle, validating how perturbation effects across different network topologies can explain and predict drug efficacy.
Evidence consistently shows that drugs whose targets are located within or near the network neighborhood (disease module) of a disease are more likely to be therapeutically effective [23]. Furthermore, the efficiency with which a drug target can spread perturbations in the human interactome has been linked to its potential to cause side effects, underscoring the critical importance of network topology and dynamics in pharmacology [24].
Comparative Analysis of Network Proximity Measures
Multiple computational models have been developed to quantify the relationship between drug targets and disease proteins. The table below compares the core methodologies and their performance.
Table 1: Comparison of Key Network-Based Drug Efficacy Frameworks
| Framework Name | Core Proximity Metric | Key Finding / Performance | Therapeutic Insight |
|---|---|---|---|
| Drug-Disease Proximity [23] | Relative proximity (zc), a z-score based on the closest shortest path distance between drug targets and disease proteins. | Best discriminator between known/unknown drug-disease pairs (AUROC outperformed other distance measures). | Drugs exert therapeutic effects on a subset of the disease module, typically proteins within 2 links. |
| Perturbation Spreading Efficiency [24] | Silencing time and perturbation reach, measured by simulating perturbations on the interactome. | Targets of drugs with side effects are significantly better spreaders of perturbations than targets of drugs without side effects (p = 1.677e-5). | Good spreaders of perturbations are more likely to cause side effects; drug targets are better spreaders than non-targets. |
| Multiscale Interactome [25] | Network diffusion profiles computed via biased random walks on a network integrating proteins and biological functions. | Predicts drug-disease treatments 40% more effectively (Avg. Precision +40%) than protein-only interactome models. | Treatments often rely on biological functions; drugs can treat diseases by affecting functions disrupted by the disease. |
Experimental Protocols for Validating Network-Based Predictions
Protocol 1: Measuring Drug-Disease Proximity in the Interactome
This protocol is based on the methodology established by Ghiassian et al. for calculating drug-disease proximity [23].
Step 1: Data Compilation
- Interactome: Assemble a comprehensive human protein-protein interaction (PPI) network from databases like STRING.
- Disease Proteins: Compile a set of proteins genetically associated with a disease from sources like OMIM and the GWAS catalog.
- Drug Targets: Obtain the set of proteins targeted by a drug from databases like DrugBank.
Step 2: Distance Calculation
- For a given drug-disease pair, calculate the closest shortest path distance ((d_c)). This is the average shortest path length between the drug's targets and their nearest disease protein in the interactome.
Step 3: Establishing Statistical Significance
- Generate a null distribution by repeatedly calculating (d_c) for randomly selected sets of proteins that match the degree distribution of the actual drug targets.
- Compute the relative proximity ((zc)) as a z-score: (zc = \frac{(dc - \mu{rand})}{\sigma{rand}}), where (\mu{rand}) and (\sigma_{rand}) are the mean and standard deviation of the null distribution.
- A significant negative (z_c) value indicates the drug targets are closer to the disease proteins than expected by chance.
Step 4: Validation
- Validate the proximity measure by testing its ability to distinguish known drug-disease pairs (from resources like MEDI-HPS) from unknown pairs using ROC-AUC analysis [23].
Protocol 2: Simulating Perturbation Spreading Efficiency
This protocol details the process for assessing a protein's ability to propagate changes, as performed in the study on drug side effects [24].
Step 1: Network and Data Preparation
- Construct the human interactome (e.g., from STRING) and define sets of proteins: drug targets with side effects, drug targets without side effects, and non-target proteins.
Step 2: Dynamics Simulation
- Use a network dynamics software package (e.g., Turbine). The communicating vessels model is one approach where perturbations "flow" between interacting proteins based on energy differences [24].
- For each protein of interest, introduce an initial energy perturbation.
Step 3: Key Metric Calculation
- Silencing Time: Record the number of simulation time steps required for the initial perturbation to completely dissipate from the network. A shorter silencing time indicates higher spreading efficiency, as the perturbation spreads widely and dissipates faster [24].
- Perturbation Reach: Measure the number of proteins that receive the perturbation before it dissipates.
Step 4: Comparative Analysis
- Compare the cumulative distribution of silencing times (or perturbation reach) between the different protein sets (e.g., targets with vs. without side effects) using statistical tests like the Mann-Whitney-Wilcoxon test [24].
Visualizing Network Relationships and Workflows
Drug-Disease Proximity in the Interactome
Multiscale Interactome for Treatment Explanation
The Scientist's Toolkit: Essential Research Reagents and Databases
Successful network pharmacology research relies on high-quality, curated data and specialized software tools. The following table catalogs key resources used in the featured studies.
Table 2: Key Research Reagents and Computational Tools for Interactome Analysis
| Resource Name | Type | Primary Function | Application Example |
|---|---|---|---|
| STRING [24] | Database | Provides comprehensive protein-protein interaction data, both physical and functional. | Serves as the backbone for reconstructing the human interactome for perturbation simulations [24]. |
| DrugBank [24] [23] | Database | Curated resource on drug targets, mechanisms, and chemical information. | Source for identifying proteins targeted by FDA-approved and experimental drugs [23]. |
| SIDER [24] | Database | Catalog of marketed drugs and their recorded side effects. | Used to classify drug targets into those with and without known side effects [24]. |
| OMIM / GWAS Catalog [23] | Database | Repositories of genes and genetic variants associated with human diseases. | Source for compiling sets of disease-associated proteins to define disease modules [23]. |
| Turbine [24] | Software | Simulates network dynamics and perturbation spreading using the communicating vessels model. | Used to calculate silencing time and perturbation reach for drug target proteins [24]. |
| Boolmore [26] | Software Tool | Uses a genetic algorithm to refine Boolean models of signaling networks against perturbation-observation data. | Automates the process of making a network model consistent with experimental data [26]. |
| PolypharmDB [27] | Database | Precompiled all-by-all drug-target interaction predictions using a deep-learning engine. | Used for drug-centric repurposing by identifying off-target interactions for GCN-identified proteins [27]. |
Methodological Approaches for Perturbation Analysis in Biomedical Research
Perturbation Response Scanning (PRS) for Drug-Target Network Analysis
In network medicine, Perturbation Response Scanning (PRS) has emerged as a robust technique for pinpointing allosteric interactions within proteins and analyzing drug-target networks. When combined with elastic network models (ENM), PRS provides a powerful computational framework for predicting how localized perturbations propagate through biological systems to induce functional responses [28] [29]. This methodology has demonstrated particular utility in drug repurposing applications, offering a systematic approach to identify novel therapeutic indications for existing compounds.
Concurrently, Polygenic Risk Scores (PRS) represent a separate but equally important methodology in genetics that predicts an individual's genetic risk for complex diseases by aggregating effects of numerous genetic variants [30] [31]. While sharing the same acronym, these distinct methodologies—one focused on network perturbations and the other on genetic risk prediction—both contribute valuable approaches to understanding complex biological systems. This guide focuses primarily on the former while acknowledging the complementary nature of these technologies in advancing precision medicine.
Comparative Performance of PRS Methodologies
Table 1: Performance Comparison of PRS Applications Across Biological Contexts
| Application Domain | Methodology | Key Performance Metrics | Experimental Validation |
|---|---|---|---|
| Drug Repurposing for Multiple Sclerosis | Network-based PRS with DTN analysis | Identified dihydroergocristine as candidate drug; HTR2B target validation | Cuprizone-induced chronic mouse model showed significant HTR2B reduction in cortex [28] |
| Single-cell Genetic Risk Prediction | scPRS (GNN-based framework) | Outperformed traditional PRS; r=0.77 correlation in monocyte count simulation (P < 2.2×10⁻¹⁶) | Significant enrichment of prioritized cells within monocytes (Z = 39.58, P < 1×10⁻⁵⁰) [31] |
| Clinical Risk Prediction | Allelica PRS for Coronary Artery Disease | AUC: 0.822 (0.815-0.829); OR per SD: 1.900 (1.872-1.978) | 21% of individuals in top 3-fold risk category [32] |
| Gene Regulatory Network Inference | Perturbation-based statistical analysis | Quantified direction and intensity of regulatory connections | Applied to EMT network; identified critical regulations in E, M, and H cell states [33] |
Table 2: Technical Comparison of PRS Methodological Frameworks
| Framework | Computational Approach | Data Requirements | Key Advantages |
|---|---|---|---|
| Network Perturbation PRS | Elastic Network Models (ENM), Random Walk algorithms | Protein structures, disease comorbidity networks, drug-target interactions | Pinpoints allosteric interactions; identifies system-level effects of localized perturbations [28] |
| scPRS | Graph Neural Networks (GNN) | scATAC-seq data, GWAS summary statistics | Single-cell resolution; identifies disease-critical cell types; links risk variants to gene regulation [31] |
| Traditional Polygenic Risk Scores | Clumping and thresholding (C+T), LDpred | GWAS summary statistics, genotype data | Population-level risk assessment; clinically implementable [30] |
| MRA-based Network Inference | Local response matrices, statistical confidence intervals | Perturbation data, steady-state expression measurements | Determines directionality and intensity of regulations; handles network sparsity [33] |
Experimental Protocols for PRS Implementation
Network-Based Drug Repurposing Protocol
The PRS framework for drug repurposing involves a multi-stage computational and experimental workflow:
Step 1: Network Construction - Build disease comorbidity networks using random walk with restart algorithms based on shared genes between the target disease (e.g., Multiple Sclerosis) and other diseases as seed nodes [28].
Step 2: Therapeutic Module Identification - Apply topological analysis and functional annotation to identify critical network modules. In MS research, the neurotransmission module was identified as the "therapeutic module" for intervention [28].
Step 3: Perturbation Scoring - Calculate perturbation scores of drugs on the identified module by constructing drug-target networks (DTNs) and implementing PRS analysis. This generates a prioritized list of repurposable drugs based on their network perturbation potential.
Step 4: Mechanism of Action Analysis - Conduct multi-level analysis at both pathway and structural levels to identify candidate drugs and their molecular targets. In the MS case study, this approach identified dihydroergocristine as a candidate drug targeting the serotonin receptor HTR2B [28].
Step 5: Experimental Validation - Establish relevant disease models (e.g., cuprizone-induced chronic mouse model for MS) to evaluate target alteration in affected tissues, confirming the computational predictions [28].
Single-cell PRS (scPRS) Implementation Protocol
The scPRS framework integrates single-cell epigenomics with genetic risk prediction through these key steps:
Step 1: Data Integration - Combine GWAS summary statistics from disease cohorts with reference single-cell chromatin accessibility data (scATAC-seq or snATAC-seq) from relevant healthy tissues [31].
Step 2: Per-Cell PRS Calculation - Compute conditioned PRS for each individual in the target cohort and for each reference cell, masking genetic variants located outside open chromatin regions specific to each cell [31].
Step 3: Graph Neural Network Processing - Apply GNN to refine per-cell PRS features, denoising raw PRS signals while capturing nonlinear relationships between genetic variants and cellular epigenome [31].
Step 4: Risk Score Aggregation - Aggregate smoothed single-cell-level PRSs into a final disease risk score that reflects the integrated contribution across multiple cell types [31].
Step 5: Biological Interpretation - Leverage model weights and single-cell contributions to prioritize disease-critical cell types and identify cell-type-specific regulatory programs [31].
The Scientist's Toolkit: Essential Research Reagents
Table 3: Essential Research Reagents for PRS Implementation
| Reagent/Resource | Function in PRS Analysis | Example Applications |
|---|---|---|
| Elastic Network Models (ENM) | Models protein dynamics and allosteric communication | Predicting perturbation propagation in drug-target networks [28] |
| scATAC-seq/snATAC-seq Data | Maps single-cell resolved candidate cis-regulatory elements | Enables cell-type-specific PRS calculation in scPRS framework [31] |
| GWAS Summary Statistics | Provides genetic variant effect sizes for complex traits | Training data for PRS construction in both traditional and single-cell approaches [30] [31] |
| Local Response Matrices | Quantifies direction and intensity of regulatory connections | Network inference from perturbation data in MRA approaches [33] |
| CRISPR-based Perturbation Data | Provides ground truth for regulatory relationship validation | Benchmarking GRN inference algorithms and perturbation responses [2] |
| Drug-Target Interaction Databases | Curated information on compound-protein interactions | Constructing drug-target networks for repurposing screens [28] |
| Graph Neural Networks (GNN) | Deep learning architecture for graph-structured data | Integrating single-cell PRS features in scPRS framework [31] |
Validation Across Network Topologies
The distribution of perturbation effects in biological networks is heavily influenced by network topology properties including sparsity, hierarchical organization, modular structure, and degree distribution [2]. Gene regulatory networks exhibit characteristic features that shape their perturbation responses:
Sparsity: Most genes are directly regulated by only a small number of transcription factors, with approximately 41% of perturbations targeting primary transcripts showing significant effects on other genes [2].
Directionality and Feedback: Regulatory relationships are directional with pervasive feedback loops, where 3.1% of ordered gene pairs show at least one-directional perturbation effects [2].
Modular Organization: Networks contain densely connected modules that correspond to functional units, influencing how perturbations propagate through the system [2].
Scale-free Properties: Network connectivity often follows approximate power-law distributions, creating hierarchical organizations with hub nodes that disproportionately influence network dynamics [2].
These structural properties directly impact PRS methodology performance, as different network topologies either dampen or amplify perturbation effects. Understanding these architectural principles is essential for optimizing PRS approaches across diverse biological contexts and accurately predicting system responses to therapeutic interventions.
Perturbation Response Scanning methodologies represent powerful approaches for analyzing biological networks and predicting system responses to interventions. The network-based PRS approach for drug-target networks has demonstrated concrete success in identifying repurposable drugs, as evidenced by the discovery of dihydroergocristine for Multiple Sclerosis treatment [28]. Meanwhile, emerging frameworks like scPRS show superior performance over traditional PRS in genetic risk prediction while offering unprecedented resolution for identifying disease-critical cell types [31].
The effectiveness of these approaches is intimately connected to the underlying topology of biological networks, with properties like sparsity, modularity, and hierarchical organization significantly influencing perturbation propagation [2]. As these methodologies continue to evolve, integration across complementary PRS frameworks—combining network perturbation analysis with genetic risk assessment—holds particular promise for advancing both fundamental understanding of biological systems and development of targeted therapeutic interventions.
Elastic Network Models (ENMs) for Predicting System-Level Perturbations
Elastic Network Models (ENMs) are a class of simplified computational approaches that represent biological systems as networks of particles connected by springs. The fundamental premise, introduced by Tirion in 1996, is that a complex biomolecule can be reduced to a set of nodes (e.g., alpha-carbons representing amino acids) with connections between nearby nodes modeled as harmonic springs [34] [35]. This minimalist representation dramatically reduces computational complexity while effectively capturing the collective dynamics and intrinsic flexibility essential for biological function. ENMs have established themselves as a powerful tool for investigating large-scale conformational changes, allosteric regulation, and functional motions in proteins, RNA, and large macromolecular complexes that are often difficult to study with more atomistically detailed simulations [34] [36].
The relevance of ENMs has expanded beyond single macromolecules to system-level applications, including the prediction of how biological systems respond to perturbations. By simplifying the representation of biological structures while retaining essential physical principles of elasticity and connectivity, ENMs enable researchers to model how localized changes (e.g., ligand binding, mutations, or mechanical stress) propagate through complex networks. This capability is particularly valuable for drug development, where understanding allosteric effects and system-level responses to pharmacological perturbation can inform therapeutic strategies [37]. The models have proven remarkably successful in reproducing experimentally observed functional motions, leading to their widespread adoption for exploring the relationship between structure, dynamics, and function in biological systems [34] [36].
Comparative Analysis of ENM Approaches
Elastic Network Models can be categorized based on their structural resolution, parameterization strategies, and application domains. The basic formulation involves defining the potential energy of the system, which is typically harmonic and depends on the deviations of inter-particle distances from their equilibrium values [35]. In the simplest models, a uniform spring constant connects all node pairs within a specific cutoff distance (e.g., 7-15 Å for protein Cα atoms) [35] [38]. Despite this simplification, such homogeneous ENMs successfully capture the dominant low-frequency motions critical for biological function, which are largely determined by the molecular architecture rather than atomic-level details [36] [38].
However, the assumption of homogeneity has limitations, particularly for systems with heterogeneous structural properties or those operating in different environments. This recognition has driven the development of heterogeneous ENMs (heteroENMs) that assign different spring constants throughout the network. These models can be parameterized to reproduce fluctuations observed in atomistic molecular dynamics simulations, creating a more accurate representation of the effective harmonic interactions between coarse-grained sites [38]. The parameterization process typically involves iterative refinement of spring constants to match target fluctuation data, resulting in a network where force constants may vary over several orders of magnitude [38]. This approach has demonstrated improved accuracy in predicting residue fluctuations and capturing motional correlations compared to uniform ENMs [38].
Table 1: Comparison of Major ENM Methodologies
| Model Type | Key Features | Parameterization | Best-Suited Applications |
|---|---|---|---|
| Homogeneous ENM | Uniform spring constant; Single cutoff distance; Computational efficiency | Simple fitting to experimental B-factors or MD fluctuations | Initial analysis of functional motions; Large complexes; Rapid screening |
| Heterogeneous ENM (heteroENM) | Variable spring constants; Potentially no cutoff distance; Improved accuracy | Iterative fitting to atomistic MD simulation data | Environment-specific dynamics; Membrane-bound proteins; Detailed mechanistic studies |
| Perturbation-Response Scanning (PRS) | Quantifies perturbation propagation; Identifies sensors and effectors | Based on network Laplacian matrix; No prior knowledge bias | Allosteric pathway identification; System-level information flow; Genetic networks |
| Augmented ENM (BioSpring) | Multi-resolution capability; Interactive simulation; Real-time feedback | Customizable cutoffs and layered springs; User-adjustable parameters | Interactive docking; Mechanical property exploration; Educational use |
Performance Comparison Across Biological Systems
The predictive performance of different ENM approaches varies depending on the biological system under investigation. For well-packed globular proteins, even simple homogeneous ENMs show remarkable agreement with experimental observations, successfully reproducing crystallographic B-factors and conformational changes observed in different experimental structures [34] [36]. This success stems from the fact that the low-frequency, collective motions of proteins are predominantly determined by the molecular shape and contact topology rather than detailed chemical interactions [34] [38].
For RNA structures, ENMs also perform well but with some notable differences compared to proteins. Research has shown that the dominant motions apparent in experimental RNA structural ensembles are effectively captured by a small number of low-frequency normal modes from ENMs [36]. However, RNA structures exhibit less sensitivity to ENM parameters than proteins, though coarse-graining results in a somewhat larger loss of dynamical information, potentially due to lower packing density and cooperativity compared to globular proteins [36].
When applied to cellular-scale networks, ENMs demonstrate unique capabilities for mapping system-level information flow. In a groundbreaking application, researchers constructed an ENM of the yeast genetic interaction profile similarity network (GI PSN), containing 5,183 genes (nodes) and 39,816 functional similarity edges [37]. Through Perturbation-Response Scanning (PRS) analysis, they identified distinct clusters of "effector" genes (information distributors) and "sensor" genes (information receivers). Effector genes formed densely connected central hubs, while sensor genes tended to occupy peripheral network positions, revealing fundamental architectural principles of cellular information processing [37].
Table 2: Quantitative Performance Metrics of ENM Applications
| Application Domain | System Studied | Performance Metrics | Comparison to Alternatives |
|---|---|---|---|
| Actin Filament Mechanics | ADP-bound F-actin | Persistence length: 6.1 ± 1.6 μm (consistent with experimental value 9.0 ± 0.5 μm) [38] | HeteroENM provided accurate prediction using only pairwise harmonic terms |
| Protein Fluctuation Prediction | Carboxy myoglobin | Improved correlation with MD fluctuations vs. uniform ENM and REACH method [38] | HeteroENM more accurately predicted mean-square fluctuations of Cα atoms |
| Cellular Network Architecture | Yeast GI PSN (5,183 genes) | Identified sensor/effector clusters (p < 0.001, permutation test); Effectiveness correlated with node degree (R = 0.9) [37] | GI PSN showed significantly stronger propensity for information propagation vs. randomized networks |
| RNA Dynamics | 16 RNA structural ensembles | >50% ensemble variance captured with 20 modes; Some ensembles approached/exceeded 75% variance explained [36] | Less parameter sensitivity than proteins; Performance robust across distance dependences |
Experimental Protocols for ENM Implementation
Standard ENM Construction and Analysis
The implementation of Elastic Network Models follows a systematic workflow that can be adapted based on the biological question and system under study. The following protocol describes the general methodology for constructing and analyzing both homogeneous and heterogeneous ENMs:
Step 1: System Representation and Coarse-Graining The first critical step involves selecting the appropriate level of resolution and mapping the biological structure to a set of nodes. For proteins, the most common representation uses Cα atoms as nodes [35] [38]. For larger complexes or system-level applications, further coarse-graining may be employed, such as representing entire protein domains or functional units as single nodes [37] [38]. The choice of resolution represents a trade-off between computational efficiency and structural detail, with finer resolutions preserving more structural information and coarser representations enabling the study of larger systems.
Step 2: Network Construction and Parameterization Once nodes are defined, connections (springs) are established between nodes based on spatial proximity. In standard ENMs, a cutoff distance between 7-15 Å is typically used, with all node pairs within this distance connected by springs with uniform force constants [35] [38]. For heterogeneous ENMs, spring constants are determined through an iterative algorithm that fits the model to fluctuations observed in atomistic molecular dynamics simulations [38]. The target data are typically the mean-square distance fluctuations between all pairs of coarse-grained sites, computed from the MD trajectory as: ( \langle(\Delta r{ij})^2\rangle{MD} = \overline{(r{ij} - \overline{r{ij}})^2} ), where ( r_{ij} ) is the distance between nodes i and j [38].
Step 3: Normal Mode Analysis and Dynamics Extraction
The ENM potential energy function is given by ( V = \sum{i
Step 4: Validation and Comparison with Experimental Data The computed fluctuations from ENM are validated against experimental data, such as crystallographic B-factors, NMR order parameters, or conformational changes observed in different experimental structures [36] [38]. For heterogeneous ENMs parameterized from MD simulations, validation may involve comparing predicted motions to those not used in the parameterization process [38]. Quantitative metrics include the correlation between experimental and computed fluctuations, and the overlap between normal modes and principal components from experimental structural ensembles [36].
Perturbation-Response Scanning (PRS) Methodology
Perturbation-Response Scanning represents a specialized application of ENMs designed to systematically map information flow and identify allosteric pathways in biological networks. The protocol for PRS analysis consists of the following key steps:
Step 1: Network Laplacian Matrix Construction The PRS methodology begins with construction of the Laplacian matrix derived from the ENM connectivity [37]. This matrix encodes the topology of the spring network and serves as the foundation for calculating how perturbations propagate through the system.
Step 2: Systematic Perturbation Application In PRS, each node in the network is sequentially subjected to a small perturbative force [37]. This systematic approach ensures comprehensive sampling of all possible perturbation sources, eliminating the bias inherent in methods that require prior selection of source nodes based on existing knowledge.
Step 3: Response Quantification For each perturbation, the linear response of all other nodes is calculated, resulting in a perturbation-response matrix of dimensions N×N for a network with N nodes [37]. This matrix quantitatively represents the effect of perturbing node i on node j, capturing both direct and indirect relationships throughout the network.
Step 4: Sensor and Effector Identification Nodes are classified based on their effectiveness (ability to transmit perturbations to other nodes) and sensitivity (tendency to be affected by perturbations elsewhere in the network) [37]. Hierarchical clustering of the perturbation-response matrix reveals distinct groups of genes or residues with specialized roles in information processing. In cellular networks, effectiveness strongly correlates with node degree (R = 0.9), while sensitivity shows more complex relationships with local connectivity [37].
Visualization of Information Flow in Biological Networks
The application of ENMs and PRS to biological networks has revealed fundamental principles governing information flow in cellular systems. The methodology enables unbiased identification of key players in biological signaling and regulation.
The architecture revealed by PRS analysis demonstrates how biological networks optimize information processing. Effector genes form densely connected clusters that occupy central positions in the network, acting as information distribution hubs [37]. These effectors exhibit high effectiveness in propagating perturbations throughout the system, with their influence strongly correlated with node degree (R = 0.9) [37]. In contrast, sensor genes form loosely connected, antenna-like clusters typically located at the network periphery [37]. These sensors display high sensitivity to perturbations originating elsewhere in the network, specializing in receiving and integrating diverse signals to coordinate cellular responses.
The indirect relationships connecting effector and sensor clusters represent major pathways for information flow between distinct cellular processes [37]. This organizational principle appears to be evolutionarily conserved, with similar architectures observed in genetic similarity networks across species including budding yeast, fission yeast, and human [37]. The global dynamic architecture of these networks appears optimized to maintain high potential for indirect cooperative relationships, enabling robust information processing despite the inherent noise and variability of biological systems.
Research Reagent Solutions for ENM Implementation
Table 3: Essential Computational Tools for ENM Research
| Tool/Resource | Type | Primary Function | Application Context |
|---|---|---|---|
| BioSpring | Interactive simulation engine | Augmented ENM with real-time feedback and multi-resolution modeling | Protein mechanics, molecular docking, membrane interactions [35] |
| Protein Data Bank (PDB) | Structural database | Source of atomic coordinates for biomolecular structures | Initial structure input for ENM construction [35] |
| Molecular Dynamics Trajectories | Simulation data | Parameterization of heterogeneous spring constants for heteroENMs | Fitting ENMs to specific environmental conditions [38] |
| Genetic Interaction Networks | Functional genomics data | System-level network construction for PRS analysis | Mapping information flow in cellular systems [37] |
| Normal Mode Analysis Algorithms | Computational method | Diagonalization of Hessian matrix to extract vibrational modes | Determination of collective motions and flexibility [34] [36] |
Elastic Network Models have evolved from simple representations of single proteins to sophisticated frameworks capable of predicting system-level perturbations across diverse biological contexts. The comparative analysis presented in this guide demonstrates that while homogeneous ENMs provide remarkable insights given their simplicity, heterogeneous approaches parameterized from atomistic simulations offer improved accuracy for studying specific environmental conditions or detailed mechanistic questions [38]. The Perturbation-Response Scanning methodology represents a particularly powerful extension, enabling unbiased mapping of information flow through complex networks and identification of critical functional elements without prior knowledge [37].
For researchers in drug development and systems biology, ENMs offer a computationally efficient bridge between structural information and functional understanding. The ability to predict how perturbations propagate through biological systems provides valuable insights for targeting allosteric sites, understanding drug side effects, and designing therapeutic interventions that account for system-level responses. As ENM methodologies continue to evolve and integrate with experimental data across multiple scales, they promise to play an increasingly important role in validating perturbation effects across different network topologies and advancing our fundamental understanding of biological organization.
Random Walk with Restart (RWR) Algorithms for Comorbidity Network Construction
Random Walk with Restart (RWR) has emerged as a powerful network propagation algorithm for modeling disease comorbidity, capable of capturing both direct and indirect relationships between molecular components of complex diseases. Unlike simple overlap measures, RWR simulates the trajectory of a random walker that traverses a biological network, at each step either moving to a neighboring node or restarting from a seed node with a predefined probability. This mechanism effectively models the flow of biological information or perturbation effects across complex network topologies, making it particularly valuable for identifying hidden comorbidity patterns that may not be evident through shared genes alone [39]. The algorithm's output provides a proximity score between seed nodes (e.g., known disease-associated genes) and all other nodes in the network, enabling systematic prioritization of comorbid conditions based on network topology [40].
The application of RWR within comorbidity research represents a significant advancement over traditional gene-sharing approaches, as it accounts for the polygenic nature of most complex diseases and the functional relatedness of their associated molecular components. By considering the entire network structure rather than just direct connections, RWR can identify disease pairs that co-occur due to disturbances in interconnected biological pathways, even when they lack directly shared genetic factors [39]. This capability is particularly crucial for validating perturbation effects across different network topologies, as it provides a mathematical framework for simulating how localized disruptions might propagate through biological systems to manifest as clinically observable comorbidities.
Methodological Approaches and Algorithmic Variations
Core RWR Methodology
The fundamental RWR algorithm operates on a network represented by graph G = (V, E), where V represents nodes (e.g., proteins, genes) and E represents edges (e.g., interactions, associations). Formally, the random walk with restart is defined as:
p⁽ᵗ⁺¹⁾ = (1 - r)Wp⁽ᵗ⁾ + rp⁽⁰⁾
Where p⁽ᵗ⁾ is a vector in which the i-th element holds the probability of finding the walker at node i at time step t, W is the column-normalized adjacency matrix of the graph, r represents the restart probability (typically set between 0.5 and 0.9), and p⁽⁰⁾ is the initial probability vector based on seed nodes [41] [39]. The steady-state probability distribution, reached after iterative updates, represents the proximity between seed nodes and all other nodes in the network, with higher probabilities indicating closer functional relationships [40].
The restart probability parameter r balances the exploration of global network structure versus local neighborhood information. Higher values (closer to 1) keep the walk more localized around seed nodes, while lower values allow broader network exploration. Optimal r values are typically determined empirically, with studies frequently using r = 0.7-0.9 for biological networks [39] [42].
Algorithmic Extensions and Specialized Implementations
Researchers have developed several specialized RWR implementations to address specific challenges in comorbidity network construction:
CN-RWR (Common Neighbors RWR) enhances traditional RWR by incorporating topological information about adjacent complete subgraphs shared between nodes. This approach demonstrated superior performance for predicting clinical drug combinations for coronary heart disease, achieving an AUROC of 0.9741 compared to 0.9586 for standard RWR in leave-one-out cross-validation [42].
MultiXrank extends RWR to multilayer networks, enabling simultaneous exploration of different biological entity types (genes, drugs, diseases) and interaction types within a unified framework. This implementation can navigate generic multilayer networks containing any combination of multiplex and monoplex networks connected by bipartite interactions, fundamentally better suited for representing multi-scale biological systems [40].
Neighborhood Walk with RWR combines neighborhood walking with RWR to construct high-quality disease-specific networks. This approach was used to build a schizophrenia network that revealed two developmental stages sensitive to immune activation perturbation, demonstrating how network topology can model critical periods in disease pathogenesis [43].
Table 1: Key RWR Algorithmic Variations for Comorbidity Research
| Algorithm | Network Type | Key Features | Reported Performance |
|---|---|---|---|
| Standard RWR | Monoplex | Basic restart mechanism, single layer | Foundation for other variants [41] |
| CN-RWR | Monoplex | Incorporates common neighbor topology | AUROC: 0.9741 (drug combinations) [42] |
| MultiXrank | Multilayer | Integrates diverse biological data types | Effective for gene/drug prioritization [40] |
| Neighborhood Walk + RWR | Monoplex | Combines local and global network exploration | Identified susceptible developmental stages [43] |
Performance Comparison Across Methodologies
Quantitative Benchmarking Against Alternative Approaches
RWR-based methods have demonstrated superior performance compared to traditional network-based approaches for comorbidity prediction. The XD-score, which utilizes RWR on protein-protein interaction networks, significantly outperformed simple shared gene approaches. In systematic evaluations, the XD-score achieved a comorbidity recall of 44.5%, substantially higher than the 6.4% recall achieved by direct gene sharing methods when applied to the same dataset [44]. Similarly, the SAB score, which measures network separation between disease modules, showed only 8.0% recall compared to 68.6% for RWR-based approaches [44].
The LeMeDISCO framework, which employs machine learning-predicted mode of action proteins with network propagation, demonstrated a comorbidity recall of 37.1% across 191,966 disease pairs, with an AUROC of 0.528, significantly better than random (0.5) [44]. This performance is particularly notable given the substantially larger coverage compared to phenotype-based methods like the Symptom Similarity Score, which despite achieving 100% recall, works for far fewer disease pairs [44].
Integration with Molecular Data Enhances Performance
Combining RWR with direct molecular evidence generates the strongest comorbidity predictions. Disease pairs identified by both positive XD scores (RWR-based) and shared genes (+XDand+NG category) demonstrated the highest comorbidity patterns in clinical data, with significantly higher average relative risk (RR) and phi-correlation (PHI) scores compared to other categories [39]. This integrated approach captured 3,213 disease pairs (3% of total analyzed), representing the most robust comorbidity relationships validated against clinical data from Medicare databases [39].
Table 2: Performance Comparison of Comorbidity Prediction Methods
| Method | Basis | Recall | Coverage | Key Advantage |
|---|---|---|---|---|
| Shared Genes (NG) | Direct gene overlap | 6.4% | Limited to diseases with known genes | Simple interpretation [44] |
| SAB Score | Network separation | 8.0% | 44,551 disease pairs | Modular disease organization [44] |
| XD-Score (RWR) | Network propagation | 44.5% | 97,666 disease pairs | Captures indirect relationships [44] |
| Symptom Similarity | Phenotype similarity | 100% | 133,107 disease pairs | Clinical manifestation based [44] |
| LeMeDISCO | ML + RWR | 37.1% | 6.5 million disease pairs | Large coverage with molecular insight [44] |
| XD + NG Combined | RWR + direct evidence | Highest RR/PHI | 3,213 disease pairs | Strongest clinical validation [39] |
Experimental Protocols and Workflows
Standard RWR Protocol for Comorbidity Network Construction
A typical RWR-based comorbidity analysis follows these methodological steps:
Step 1: Network Construction - Build a comprehensive biological network integrating protein-protein interactions from databases like STRING (combining score ≥400 for high-quality interactions) [41]. The network should represent relevant biological relationships for the diseases under investigation.
Step 2: Seed Selection - Identify high-confidence disease-associated genes from curated databases such as DisGeNET, DISEASES, OMIM, PheGenI, and PGKB [41] [43]. For schizophrenia research, this involved 1,720 protein-coding seed genes derived from linkage studies, GWAS, copy number variations, transcriptomic studies, and exome sequencing [43].
Step 3: Parameter Optimization - Set the restart probability parameter (r), typically through cross-validation. Studies have used values ranging from 0.7 to 0.9, with some implementations using r = 0.8 [41] [44].
Step 4: Network Propagation - Execute the RWR algorithm until convergence (when the difference between p⁽ᵗ⁺¹⁾ and p⁽ᵗ⁾ falls below a predefined threshold, e.g., 10⁻¹⁰).
Step 5: Comorbidity Scoring - Calculate disease-disease similarity scores based on the proximity of their associated gene sets in the network. The XD-score represents one such implementation [39].
Integrated Multi-Omic Validation Workflow
Advanced RWR implementations incorporate multiple data types and validation steps:
Data Integration - Combine genomic, proteomic, and clinical data sources to construct comprehensive multilayer networks. The MultiXrank approach successfully integrated gene-gene interactions, drug-target associations, and disease relationships in a unified framework [40].
Therapeutic Module Identification - Apply topological measures like within-module degree (Z) and participation coefficient (P) to identify network regions most relevant to disease comorbidity. These are calculated as:
Zᵢ = (kᵢ - k̄ₛᵢ)/σkₛᵢ
Pᵢ = 1 - ∑ₛ₌₁ᴺᴹ (kᵢₛ/kᵢ)²
Where kᵢ is the number of links of node i, k̄ₛᵢ and σkₛᵢ are the average and standard deviation of degree in module sᵢ, and kᵢₛ is the number of links from node i to module s [41].
Experimental Validation - Corroborate computational predictions with biological experiments. For multiple sclerosis, RWR-based predictions identified HTR2B as a candidate target, which was subsequently validated in a cuprizone-induced chronic mouse model showing significant reduction of HTR2B in the mouse cortex [41].
Table 3: Essential Research Resources for RWR-based Comorbidity Studies
| Resource Category | Specific Examples | Function in RWR Comorbidity Research |
|---|---|---|
| Protein Interaction Databases | STRING, BioGRID | Provide physical and functional interactions for network construction [41] [39] |
| Disease-Gene Associations | DisGeNET, OMIM, SZDB | Source of seed genes for specific diseases [41] [43] |
| Drug-Target Resources | DrugBank, Therapeutic Target Database | Enable drug-target network construction for therapeutic discovery [41] |
| Clinical Comorbidity Data | Medicare databases, FDA FAERS | Provide ground truth for validation of predictions [45] [39] |
| Pathway Analysis Tools | Enrichment analysis software | Interpret biological mechanisms underlying predicted comorbidities [39] |
| Multi-Omic Data Platforms | SomaScan, Metabolon HD4 | Generate proteomic and metabolomic data for multilayer networks [46] |
| RWR Implementation Software | MultiXrank, Custom R/Python scripts | Execute network propagation algorithms [40] |
Random Walk with Restart algorithms represent a powerful computational framework for constructing comorbidity networks and validating perturbation effects across diverse network topologies. By simulating the propagation of biological influences through complex molecular networks, RWR-based methods can identify clinically relevant disease relationships that extend beyond direct genetic overlaps. The continuous development of specialized implementations—including multilayer network exploration, integration with machine learning approaches, and incorporation of multi-omic data—promises to further enhance our understanding of disease comorbidity and accelerate the discovery of novel therapeutic strategies.
The strongest comorbidity predictions emerge from integrating RWR-based network propagation with direct molecular evidence, demonstrating that combined approaches consistently outperform single-method strategies. As biological networks become increasingly comprehensive and multi-omic data more accessible, RWR methodologies will continue to play a crucial role in unraveling the complex web of relationships underlying human disease comorbidities.
Feature-Topology Cascade Perturbation in Graph Neural Networks
Graph Neural Networks (GNNs) have become fundamental tools for analyzing non-Euclidean data across various scientific domains, including drug discovery and systems biology. A significant challenge in their application is ensuring they learn powerful, generalizable representations rather than merely memorizing training data. Feature-Topology Cascade Perturbation (FTCP) has emerged as a novel, plug-and-play architecture that systematically augments graph data through a two-stage process, enhancing model robustness and performance [47].
Unlike conventional feature perturbation methods that operate from a global perspective, FTCP innovatively integrates local structural importance through "celebrity" nodes and propagates these perturbations to the topological level [47]. This approach is particularly relevant for drug development, where accurately modeling molecular structures and protein-protein interactions can significantly accelerate discovery pipelines. This guide provides an objective comparison of FTCP against other GNN perturbation and augmentation strategies, contextualized within the broader research goal of validating perturbation effects across diverse network topologies.
The FTCP Architecture
The FTCP framework consists of two cascaded perturbation stages designed to work in concert [47]:
- Celebrity-Guided Feature Perturbation: On the feature level, FTCP first identifies influential "celebrity" nodes by analyzing multi-hop structures inherent in the original graph topology. These nodes disproportionately impact the network's representation power. The method then prioritizes perturbations around these celebrities, moving beyond global perturbation strategies that neglect local structural importance.
- Cascaded Topology Perturbation: On the node relationship level, FTCP further tracks the topological changes induced by the perturbed features. It employs a polarized view to analyze this transformed topology, which subsequently enriches the original graph structure with more complex and informative connection patterns.
Alternative Approaches
Other strategies have been developed to address the interplay between topology and GNN performance:
- Graph Neural Diffusion: This approach leverages principles from partial differential equations to create robust GNNs. These models demonstrate intrinsic robustness to topological perturbations, a property explained theoretically through the stability of the heat semigroup under graph topology changes [48].
- Topology-Aware Attention (GTAT): Used particularly in Gene Regulatory Network (GRN) inference, GTAT integrates multi-source biological features (temporal expression, baseline expression, topological attributes) with an attention mechanism that explicitly captures topological dependencies between genes [49].
- Minimum-Budget Topology Attacks (MiBTack): Representing the adversarial perspective, MiBTack efficiently finds the minimum number of edge changes required to cause GNN misclassification. This method highlights GNN vulnerabilities and provides a metric for assessing node-level robustness [50].
Performance Comparison
The following table summarizes the performance of FTCP against other GNN models and perturbation strategies across standard benchmark datasets, primarily focusing on node classification accuracy.
Table 1: Performance Comparison of FTCP and Alternative Methods on Node Classification Tasks
| Model | Cora | Citeseer | Pubmed | DREAM4 | Key Characteristics |
|---|---|---|---|---|---|
| FTCP (with GCN backbone) [47] | ~83.5% | ~73.2% | ~81.0% | N/A | Plug-and-play; celebrity-guided feature & cascade topology perturbation |
| GCN (Baseline) [47] | ~81.0% | ~70.5% | ~79.5% | N/A | Standard graph convolutional network |
| GAT (Baseline) [51] | ~80.5% | ~70.2% | ~78.8% | N/A | Graph attention network |
| TWC-GNN [51] | ~83.1% | ~72.9% | ~80.5% | N/A | Integrates centrality information & self-attention |
| GTAT-GRN [49] | N/A | N/A | N/A | AUPR: ~0.32 | Topology-aware attention for GRN inference; multi-source feature fusion |
FTCP demonstrates consistent performance improvements when applied to various GNN backbones (e.g., GCN, GAT), validating its effectiveness as a general-purpose augmentation architecture [47]. In specialized domains like GRN inference, topology-aware methods like GTAT-GRN have shown superior performance in achieving higher AUC and AUPR scores compared to state-of-the-art methods like GENIE3 and GreyNet [49].
Experimental Protocols and Validation
FTCP Experimental Workflow
The standard protocol for validating FTCP involves several key stages, from data preparation to performance evaluation on downstream tasks, as illustrated below.
Diagram 1: FTCP Experimental Workflow
Core Methodological Components
- Celebrity Node Identification: The process begins by analyzing the original graph's multi-hop topology to identify high-influence "celebrity" nodes, which are crucial for the GNN's representational power [47].
- Cascade Perturbation Application: The methodology involves sequentially applying feature perturbation guided by the identified celebrities, followed by a topology perturbation that is directly influenced by the feature-level changes [47].
- Performance Benchmarking: Enhanced graphs are used to train GNN models, with performance evaluated on node classification tasks and compared against baseline models and other augmentation strategies [47].
Validation Across Network Topologies
Research on the broader relationship between graph topology and GNN performance provides critical context for validating FTCP's effects. A key insight is that the benefits of enhanced topology awareness are not universal; excessively emphasizing topological features can sometimes lead to unfair generalization across structural groups [52]. Furthermore, a GNN's expressive power is fundamentally constrained by its input graph's local connectivity patterns, formalized through concepts like k-hop similarity [53]. These findings underscore the importance of validating perturbation methods like FTCP across graphs with diverse topological properties, including varying degrees of homophily, community structure, and node centrality distributions.
The Scientist's Toolkit: Research Reagents & Materials
Table 2: Essential Research Reagents and Computational Tools for Graph Perturbation Research
| Item/Tool Name | Function/Purpose | Relevance to Perturbation Studies |
|---|---|---|
| Benchmark Datasets (Cora, Citeseer, Pubmed) | Standardized graph data for training and evaluation | Provides controlled environments for comparing FTCP against alternative methods [47] [51] |
| GRN Datasets (DREAM4, DREAM5) | Gold-standard benchmarks for Gene Regulatory Network inference | Critical for validating topology-aware methods in biological contexts [49] |
| Graph Topology Analysis Tools | Algorithms for computing node centrality, k-core index, etc. | Enables celebrity identification and analysis of topological features [47] [49] |
| Adversarial Attack Frameworks (e.g., MiBTack) | Models for generating minimal-budget topology attacks | Quantifies model robustness and node-level vulnerability [50] |
| Graph Neural Diffusion Models | GNNs based on PDE principles serving as robust baselines | Provides a benchmark for evaluating perturbation robustness [48] |
Feature-Topology Cascade Perturbation represents a significant advancement in graph data augmentation by systematically coupling feature and structural perturbations. Experimental evidence confirms that FTCP consistently enhances the performance of various GNN models on node classification tasks [47]. However, the broader research on topology awareness suggests that the effectiveness of such perturbations is inherently dependent on the underlying graph structure [52] [53].
For drug development professionals, methods like FTCP and GTAT-GRN offer promising avenues for improving the accuracy of predictive modeling in complex biological networks, from molecular interaction graphs to gene regulatory systems [47] [49]. Future work should focus on further validating these perturbation effects across an even wider spectrum of network topologies, particularly those mimicking real-world biological and chemical structures.
The growing availability of high-throughput biological data has catalyzed the development of network-based approaches for drug discovery and repurposing. These methods operate on the principle that cellular functions emerge from complex networks of molecular interactions, and that diseases arise from perturbations within these networks [54] [55]. Drug repurposing—identifying new therapeutic uses for existing drugs—has gained significant attention as a strategy that can reduce development costs and accelerate the delivery of treatments to patients, particularly for complex diseases like multiple sclerosis (MS) [56]. By quantifying how drug-induced perturbations propagate through biological networks, researchers can systematically identify candidates for repurposing, moving beyond the traditional "one drug, one target" paradigm to a more holistic understanding of drug effects [57] [58].
Multiple sclerosis, a chronic immune-mediated disorder of the central nervous system characterized by inflammation, demyelination, and neurodegeneration, presents a compelling use case for network perturbation approaches [56]. The complex and multifactorial pathophysiology of MS involves an interplay of genetic susceptibility, environmental triggers, and immune dysregulation, making it ideally suited for analysis through network-based methods that can capture these complex interactions [55] [56]. This case study examines how network perturbation methodologies are being applied to identify repurposing opportunities for MS, framed within the broader thesis of validating perturbation effects across different biological network topologies.
Computational Methodologies for Network-Based Drug Repurposing
Foundational Principles of Network Perturbation
Network perturbation methods for drug repurposing are grounded in the observation that disease-associated proteins tend to cluster in specific neighborhoods within the human interactome, forming what are known as disease modules [57]. The fundamental premise is that for a drug to be therapeutically effective against a disease, its protein targets should be located within or in close network proximity to the corresponding disease module [57]. This principle enables the prediction of drug-disease associations through topological analysis of biological networks, even without complete knowledge of the kinetic parameters governing molecular interactions [9].
Research has demonstrated that knowledge of network topology alone can achieve 65-80% accuracy in predicting biochemical perturbation patterns, bypassing the need for expensive and difficult kinetic constant measurements [9]. This remarkable finding, encapsulated in DYNAMO (DYNamics-Agnostic Network MOdels), indicates that increasingly accurate topological models can effectively approximate perturbation patterns, with predictive power robust to variations in kinetic parameters [9]. The ability to make reasonably accurate predictions without detailed kinetic information significantly enhances the scalability of network-based drug repurposing approaches.
Key Methodological Frameworks
Several specific methodological frameworks have been developed for network-based drug repurposing:
Network Proximity Measures: These approaches quantify the relationship between drug targets and disease modules within biological networks. The closest distance-based z-score has been shown to outperform alternative network distance measures (shortest, kernel, and centre) in identifying known drug-disease relationships, achieving over 70% area under the receiver operating characteristic curve (AUC) for FDA-approved cardiovascular drugs [57].
Perturbation Response Scanning (PRS): Originally developed for identifying allosteric interactions within proteins using elastic network models, PRS has been adapted for analysis of drug-target networks [59]. This approach calculates perturbation scores of drugs on disease-relevant network modules to prioritize repurposing candidates.
Integrated Network Construction: MS comorbidity networks can be constructed using algorithms such as random walk with restart based on genes shared between MS and other diseases as seed nodes [59]. Through topological analysis and functional annotation, key therapeutic modules can be identified as targets for perturbation analysis.
Table 1: Quantitative Metrics for Network Proximity Assessment in Drug Repurposing
| Metric | Calculation | Interpretation | Performance |
|---|---|---|---|
| Closest Distance Z-score | ( z = \frac{d - \mu}{\sigma} ) where ( d(S,T) = \frac{1}{|T|} \sum{t \in T} \min{s \in S} d(s,t) ) | Negative z-score indicates proximity between drug targets and disease module | AUC >70% for known drug-disease pairs [57] |
| Sensitivity Matrix | ( S{ij} = \frac{dxi}{dx_j} ) | Measures change in steady-state value of node i when node j is perturbed | 65-80% accuracy vs. full biochemical models [9] |
| Therapeutic Module Identification | Topological analysis and functional annotation of comorbidity networks | Identifies disease-relevant subnetworks for targeted perturbation | Applied to identify neurotransmission module in MS [59] |
Workflow for MS Drug Repurposing
The following diagram illustrates the integrated workflow for drug repurposing in multiple sclerosis using network perturbation approaches:
Diagram 1: Network perturbation workflow for MS drug repurposing.
Experimental Validation and Case Applications
Validation Through Healthcare Databases and Experimental Models
Network-based predictions require rigorous validation before clinical application. A prominent study demonstrated this validation pipeline by identifying hundreds of new drug-disease associations for over 900 FDA-approved drugs through network proximity analysis in the human protein-protein interactome [57]. Four network-predicted associations were selected for testing using large healthcare databases encompassing over 220 million patients and state-of-the-art pharmacoepidemiologic analyses. Using propensity score matching, two of the four network-based predictions were validated: carbamazepine was associated with increased risk of coronary artery disease, while hydroxychloroquine was associated with decreased risk [57]. This approach was further strengthened by in vitro experiments showing that hydroxychloroquine attenuates pro-inflammatory cytokine-mediated activation in human aortic endothelial cells, providing mechanistic support for its potential beneficial effect [57].
For multiple sclerosis specifically, network perturbation approaches have identified dihydroergocristine as a repurposing candidate through targeting of the serotonin receptor HTR2B [59]. Experimental validation using a cuprizone-induced chronic mouse model demonstrated that HTR2B was significantly reduced in the cuprizone-induced mouse cortex, supporting the involvement of this receptor in MS-related pathology and confirming the value of network-based predictions [59].
Artificial Intelligence and Advanced Computational Approaches
Artificial intelligence approaches, particularly machine learning and deep learning, are increasingly being integrated with network perturbation methods to enhance drug repurposing for MS [56]. AI enables the analysis of high-dimensional biomedical data, prediction of drug-target interactions, and streamlining of drug repurposing workflows. By integrating multi-omics and neuroimaging data, AI tools facilitate the identification of novel targets and support patient stratification for individualized treatment [56].
The integration of AI with network biology represents a next-generation approach to drug repurposing that can address the complexity and heterogeneity of MS [58] [56]. These methods can identify repurposed agents such as selective sphingosine-1-phosphate (S1P) receptor modulators, kinase inhibitors, and metabolic regulators that have demonstrated potential in promoting neuroprotection, modulating immune responses, and supporting remyelination in both preclinical and clinical settings [56].
Table 2: Experimentally Validated Drug Repurposing Candidates for Multiple Sclerosis
| Drug Candidate | Original Indication | Network-Based Evidence | Experimental Validation | Proposed Mechanism in MS |
|---|---|---|---|---|
| Dihydroergocristine | Not specified | PRS analysis identified HTR2B targeting [59] | Cuprizone-induced mouse model showed HTR2B reduction in cortex [59] | Targets serotonin receptor HTR2B [59] |
| Hydroxychloroquine | Malaria, Autoimmune conditions | z = -3.85 for CAD association [57] | Large healthcare databases (HR 0.76 for CAD); in vitro endothelial cell assays [57] | Attenuates pro-inflammatory cytokine-mediated activation |
| S1P Receptor Modulators | Various indications | AI and network analysis [56] | Preclinical and clinical studies for MS [56] | Immunomodulation and neuroprotection |
Successful implementation of network perturbation strategies for drug repurposing requires specialized computational tools and biological resources. The following table outlines key components of the research toolkit for these studies:
Table 3: Research Reagent Solutions for Network Perturbation Studies
| Resource Type | Specific Examples | Function in Network Perturbation Studies | Relevance to MS |
|---|---|---|---|
| Interaction Databases | Human interactome (243,603 PPIs); BioModels database [57] [9] | Provide topological information for network construction | Enable mapping of MS-relevant pathways |
| Drug-Target Resources | DrugBank; FDA-approved drug targets with binding affinity data [57] | Define drug target profiles for proximity analysis | Source for repurposing candidates |
| Omics Data Platforms | Gene Expression Omnibus (GEO); EBI Expression Atlas [54] [9] | Provide transcriptomic profiles for validation | MS-specific expression data |
| Computational Frameworks | DYNAMO models; PRS analysis; Random walk algorithms [59] [9] | Implement perturbation propagation algorithms | Applied to MS comorbidity networks |
| Experimental Validation Systems | Cuprizone-induced mouse model; Human aortic endothelial cells [57] [59] | Test predictions from network analyses | Model MS pathology and drug effects |
| Clinical Data Resources | Healthcare claims databases (220M+ patients) [57] | Validate predictions at population level | Assess real-world drug effects in MS |
Pathway and Workflow Visualization
The signaling pathways and molecular interactions identified through network perturbation analysis can be visualized to enhance understanding of drug mechanisms. The following diagram illustrates a generalized signaling pathway affected by network-predicted drug candidates in MS:
Diagram 2: Signaling pathway modulation by repurposed drugs.
Network perturbation approaches represent a powerful strategy for drug repurposing in multiple sclerosis, leveraging the growing availability of biological network data and advanced computational methods. By analyzing how drug-induced perturbations propagate through biological systems, researchers can identify novel therapeutic applications for existing drugs, potentially accelerating treatment development for MS patients. The validation of perturbation effects across different network topologies remains a crucial component of this approach, ensuring that predictions are biologically meaningful and clinically relevant.
The integration of artificial intelligence with network biology, along with robust validation through large-scale healthcare databases and experimental models, creates a comprehensive framework for future drug repurposing efforts [56]. As network models continue to improve in accuracy and completeness, and as validation methodologies become more sophisticated, network perturbation approaches are poised to make increasingly significant contributions to the therapeutic arsenal for multiple sclerosis and other complex diseases.
Addressing Computational Challenges and Optimizing Perturbation Protocols
Common Pitfalls in Perturbation Method Selection and Implementation
Perturbation analysis is a fundamental technique across scientific disciplines, from celestial mechanics to network biology and explainable artificial intelligence (XAI). The core principle involves introducing a controlled change to a system to observe its response and thereby infer internal structure and dynamics. However, the selection and implementation of perturbation methods are fraught with challenges that can compromise the validity and interpretation of results. Within network topology research, particularly in biological contexts like drug development, understanding these pitfalls is paramount for deriving meaningful insights from perturbation experiments. This guide examines common pitfalls through a cross-disciplinary lens, providing structured comparisons and protocols to enhance methodological rigor.
The validation of perturbation effects across different network topologies presents unique challenges. As research in biological networks has revealed, the absence of kinetic parameters often necessitates reliance on topological models, yet the predictive power of such models varies significantly based on implementation choices [9]. Similarly, in XAI, the arbitrary selection of perturbation methods can dramatically alter the perceived faithfulness of feature attribution methods [60]. This comparison guide synthesizes evidence from multiple domains to establish robust frameworks for perturbation method selection and implementation.
Types of Perturbation Methods and Their Applications
Perturbation methods encompass diverse techniques tailored to specific system characteristics and research questions. Understanding the fundamental categories and their appropriate applications forms the foundation for proper methodological selection.
Table 1: Classification of Perturbation Methods Across Disciplines
| Method Category | Core Principle | Typical Application Domains | Key Output Measures |
|---|---|---|---|
| Topological Perturbations [61] | Modification of network structure (node/link removal, weight alteration) | Trade networks, biological networks, resilience analysis | Network resilience, connectivity, stability metrics |
| Parameter Perturbations [9] | Variation of system parameters while maintaining structure | Biochemical networks, dynamical systems | Sensitivity coefficients, parameter influence patterns |
| Feature Perturbations [60] | Systematic alteration of input features to assess importance | Explainable AI, model interpretation | Feature attribution scores, faithfulness metrics |
| Dynamic Perturbations [62] | Introduction of disturbances to system states over time | Celestial mechanics, voice analysis, ecological systems | Stability assessments, perturbation patterns |
In biological networks, perturbation analysis helps unravel complex interactions between biochemical entities. The DYNAMO (DYNamics-Agnostic Network MOdels) framework demonstrates that network topology alone can predict 65-80% of true perturbation patterns even without detailed kinetic parameters [9]. This approach successively incorporates directed, signed, and weighted interactions to improve prediction accuracy, highlighting how methodological complexity must match research goals and data availability.
Quantitative Comparison of Perturbation Method Performance
Evaluating perturbation method efficacy requires standardized metrics and comparative frameworks. Cross-disciplinary analysis reveals significant performance variations based on implementation context and system characteristics.
Table 2: Performance Comparison of Perturbation Methods Across Domains
| Method | Accuracy/ Reliability | Data Requirements | Computational Complexity | Key Limitations |
|---|---|---|---|---|
| Classical Perturbation Theory [62] | High for short-term predictions in stable systems | Complete system parameters | Moderate to High | Non-uniform convergence; dense commensurabilities |
| Distance-Based Topological Models [9] | ~65% accuracy | Network topology only | Low | Misses directional effects and dynamics |
| Signed & Directed Topological Models [9] | Up to 80% accuracy | Topology with direction and sign information | Low to Moderate | Requires interaction type knowledge |
| Nonlinear Dynamic Methods [63] | Superior for chaotic signals | Shorter signals acceptable | High | Methodological complexity |
| Perturbation Methods for Voice Analysis [63] | Reliable only for nearly periodic signals | Long signals, high sampling rates, low noise | Moderate | Fails with chaotic or noisy data |
Research in voice analysis demonstrates how methodological misfit creates significant pitfalls. Traditional perturbation methods fail with chaotic signals due to pitch tracking difficulties and sensitivity to initial conditions, whereas nonlinear dynamic methods like correlation dimension analysis successfully quantify chaotic time series under more realistic signal conditions [63]. This illustrates the critical importance of matching method selection to fundamental system properties.
In XAI validation, the arbitrary choice of perturbation methods dramatically affects faithfulness evaluations. The Area Under the Perturbation Curve (AUPC) metric commonly used for feature attribution method evaluation proves insufficient alone, potentially leading to incorrect conclusions about method performance [60]. Comprehensive evaluation requires multiple metrics including the Decaying Degradation Score (DDS), Perturbation Effect Size (PES), and the combined Consistency-Magnitude-Index (CMI) to adequately capture different aspects of explanation faithfulness [60].
Experimental Protocols for Perturbation Analysis
Protocol for Biological Network Perturbation Analysis
The following protocol, adapted from biological network studies, provides a robust framework for perturbation analysis in network topology research:
Network Construction: Compile the interactome using protein-protein interactions, gene regulation data, metabolic reactions, or other relevant sources. For trade networks, calculate competition intensity using appropriate indices like the Export Similarity Index [61].
Topology Enhancement: Progressively enrich network representation from basic undirected topology to directed, signed (activating/inhibiting), and weighted connections based on available data [9].
Sensitivity Matrix Calculation: Compute the sensitivity matrix ( S{ij} = \frac{dxi}{dx_j} ) describing changes in steady-state values of network components when others are perturbed [9].
Influence Pattern Modeling: Apply propagation models where node perturbation is proportional to the degree-weighted sum of perturbations to neighboring nodes [9].
Validation: Compare predicted perturbation patterns against experimental data or full biochemical models. Calculate accuracy as the percentage recovery of true influence patterns [9].
Figure 1: Experimental workflow for biological network perturbation analysis with common pitfalls highlighted.
Protocol for XAI Feature Attribution Validation
For validating feature attribution methods in neural time series classifiers, the following adapted protocol ensures robust assessment:
Model Training: Train deep learning time series classification models using appropriate architectures (e.g., CNNs, LSTMs, Transformers).
Explanation Generation: Compute feature attributions using multiple attribution methods (e.g., gradient-based, occlusion, surrogate models).
Multi-Method Perturbation: Apply a diverse set of perturbation methods rather than relying on a single approach [60].
Comprehensive Metric Calculation: Compute multiple validation metrics including AUPC, DDS, PES, and the combined CMI to capture different aspects of faithfulness [60].
Cross-Architecture Validation: Repeat evaluation across different model architectures and dataset types to identify consistent performers.
The Scientist's Toolkit: Essential Research Reagents and Materials
Table 3: Essential Research Reagents and Computational Tools for Perturbation Analysis
| Tool/Reagent | Function/Purpose | Application Context |
|---|---|---|
| Jacobian Matrix [9] | Quantifies how changes in one component affect others; encodes direction and sign of interactions | Biological networks, dynamical systems |
| Sensitivity Matrix (S) [9] | Describes changes in steady-state values of components when others are perturbed | Perturbation pattern prediction |
| Export Similarity Index (ESI) [61] | Measures competition intensity between countries based on export profile similarity | World trade competition networks |
| Consistency-Magnitude-Index (CMI) [60] | Combined metric evaluating how consistently an AM separates important from unimportant features | XAI feature attribution validation |
| Generalized Lotka-Volterra Model [61] | Describes dynamics in resource-competition networks; models nonlinear system behavior | Socioeconomic systems, ecological networks |
| Correlation Dimension Method [63] | Quantifies chaotic time series; avoids pitch tracking issues of traditional perturbation methods | Voice analysis, chaotic systems |
Critical Analysis of Perturbation Method Limitations
The implementation of perturbation methods faces several fundamental challenges that transcend disciplinary boundaries. Understanding these limitations is crucial for appropriate method selection and interpretation of results.
A primary concern lies in the mathematical foundations of perturbation theory itself. Classical perturbation methods, while successful for predicting planetary positions over centuries, face obstacles to uniform convergence due to "everywhere-dense commensurabilities of mean motions" [62]. This prevents validation through rigorous mathematical analysis and questions the long-term predictive power of these methods, despite their empirical success.
The stability-plasticity dilemma represents another core challenge. In trade competition networks, resilience declines more rapidly when nodes are removed based on higher weighted degrees, and removing high-competition intensity links destabilizes networks more quickly [61]. This demonstrates that the very elements that create robustness in stable environments can become vulnerability points during perturbation, creating an inherent tradeoff in network design.
The context dependence of optimal method selection presents implementation hurdles. Research shows that no universally optimal perturbation method exists across all model architectures and datasets [60]. Both data properties and what the model has learned to rely on influence optimal perturbation strategy, necessitating systematic evaluation rather than presumptive method application.
Figure 2: Relationship between common perturbation method pitfalls and their impacts on research outcomes.
The selection and implementation of perturbation methods present common challenges across diverse domains from celestial mechanics to biological networks and explainable AI. Success hinges on recognizing fundamental pitfalls: incomplete topological information reduces prediction accuracy by 15-20%; inadequate validation metrics provide misleading faithfulness assessments; and context-dependent performance necessitates multi-method evaluation frameworks. The experimental protocols and comparative data presented herein provide researchers with structured approaches for navigating these challenges. Particularly in network topology research for drug development, where accurate perturbation prediction directly impacts therapeutic target identification, rigorous method selection and validation are indispensable. Future methodological development should focus on adaptive perturbation frameworks that dynamically adjust to system characteristics and evolving research questions.
Optimizing Perturbation Distribution Assumptions for Biological Data
Biological systems, from intracellular gene regulatory networks to cellular populations, are inherently complex. A fundamental approach to understanding these systems involves perturbations—controlled interventions that disrupt specific components to observe resultant effects. The core challenge in computational biology lies in developing models that can accurately predict the outcomes of these perturbations, particularly for unseen interventions or in novel biological contexts. The distribution of perturbation effects is not random; it is constrained by the underlying network topology, which exhibits properties such as sparsity, hierarchy, and modularity [64]. This guide provides a comparative analysis of contemporary computational models that optimize their assumptions about perturbation distributions to navigate biological complexity, enabling more efficient drug discovery and therapeutic target identification.
Performance Comparison of Leading Models
The field has seen rapid advancement with models adopting diverse strategies. The table below summarizes the quantitative performance of several state-of-the-art methods on key biological tasks.
Table 1: Performance Comparison of Perturbation Prediction Models
| Model Name | Core Methodology | Perturbation Type Supported | Key Performance Metrics | Reported Performance |
|---|---|---|---|---|
| LPM (Large Perturbation Model) [65] | PRC-disentangled, decoder-only deep learning | Genetic (CRISPR), Chemical | Prediction of unseen perturbation transcriptomes | "Consistently and significantly outperformed state-of-the-art baselines" [65] |
| MORPH [66] | Discrepancy-based VAE with attention mechanism | Genetic (single & combo) | RMSE, Pearson Correlation, MMD on single-cell data | Accurately predicts effects of unseen single-gene and combinatorial perturbations [66] |
| BioBO [67] | Biology-informed Bayesian Optimization | Genetic (Knockout) | Labeling efficiency for identifying top perturbations | Improves labeling efficiency by 25-40% over conventional BO [67] |
| boolmore [26] | Genetic algorithm for Boolean model refinement | Network nodes (in silico) | Accuracy vs. curated perturbation-observation pairs | Improved model accuracy from 49% to 99% on training set, 47% to 95% on validation set [26] |
| Network Propagation [68] | Topology-based network analysis | Mutations | Accuracy in identifying perturbation effects on species | Provides insights without quantitative details [68] |
Experimental Protocols for Model Validation
Robust experimental validation is crucial for assessing model performance. The following section details the protocols used to benchmark the models discussed in this guide.
Protocol for Predicting Unseen Perturbation Effects
Objective: To evaluate a model's ability to generalize and predict the outcomes of genetic or chemical perturbations not present in its training data [65] [66].
- Data Splitting: Perturbations in the dataset are split into distinct sets for training and testing. This is done via:
- Standard k-fold cross-validation: The dataset is divided into k folds (e.g., k=5) by perturbations. The model is trained on k-1 folds and tested on the held-out fold [66].
- Outlier distribution split: The test set is specifically composed of perturbations that induce the most distinct phenotypic changes from the control state, providing a stringent test of generalization [66].
- Evaluation Metrics:
- Root Mean Squared Error (RMSE): Quantifies the average magnitude of prediction error [66].
- Pearson Correlation: Measures the linear correlation between the predicted and observed mean gene expression changes [66].
- Maximum Mean Discrepancy (MMD): A distributional metric that assesses the similarity between the full distribution of predicted perturbed cells and the ground-truth distribution, offering a more granular evaluation than mean-based metrics alone [66].
Protocol for In-Silico Benchmarking of Model Refinement
Objective: To assess an algorithm's capability to refine an initial, imperfect model of a biological network to better align with experimental data [26].
- Data Generation: A published, curated Boolean model is used as a ground truth. From this model, a corpus of artificial perturbation-observation pairs is generated. Each pair specifies a perturbation (e.g., gene knockout) and the observed state of another network component [26].
- Creation of Initial Model: The starting model for the refinement algorithm is created by using the correct network structure (interaction graph) of the ground-truth model but randomizing the regulatory logic (Boolean functions) at each node [26].
- Training and Validation: 80% of the artificial experiments are used as a training set for refinement. The remaining 20% are held out as a validation set. The algorithm's success is measured by the improvement in agreement with both the training and validation sets, with the latter testing for overfitting [26].
Protocol for Validating Experimental Design Optimization
Objective: To determine the efficiency of a model in guiding a sequence of perturbation experiments towards an optimal cellular phenotype (e.g., high production of a therapeutic compound) [67].
- Baseline Establishment: A dataset containing gene perturbation-outcome pairs is used to create a known response surface.
- Sequential Design: The optimization algorithm (e.g., BioBO) is initialized with a small set of randomly selected perturbations. It then iteratively selects the next most informative perturbation to test based on its acquisition function [67].
- Efficiency Metric: The primary metric is labeling efficiency—the number of experimental iterations (or unique perturbations tested) required for the algorithm to identify a perturbation that produces an outcome within a pre-specified distance (e.g., 10%) of the global optimum. This is compared against the number of tests required by a traditional method like grid search [69] [67].
The compared models employ distinct architectural philosophies to tackle the perturbation prediction problem, which can be visualized in their core workflows.
The LPM Architecture: Disentangling Experimental Dimensions
The Large Perturbation Model (LPM) integrates heterogeneous data by explicitly separating the concepts of Perturbation (P), Readout (R), and Context (C). Its decoder-only architecture learns to predict experimental outcomes based on this PRC tuple, enabling seamless learning across diverse experimental setups [65].
LPM integrates diverse data by disentangling Perturbation, Readout, and Context into a unified input tuple.
The MORPH Architecture: A Modular Single-Cell Predictor
MORPH is designed to predict the effect of a genetic perturbation on an individual cell. It uses a conditional Variational Autoencoder (VAE) to map a control cell and a gene perturbation embedding to a predicted perturbed cell. Its key feature is an attention mechanism that mimics regulatory networks, helping the model learn functional biological relationships and generalize to unseen perturbations [66].
MORPH uses a VAE and attention mechanism to predict single-cell perturbation outcomes from a control cell state and gene embedding.
The Scientist's Toolkit: Key Research Reagents and Materials
Successful implementation and validation of perturbation models rely on specific computational and data resources.
Table 2: Essential Reagents and Resources for Perturbation Studies
| Resource Name | Type | Function in Research |
|---|---|---|
| Perturb-seq Data [64] [66] | Experimental Dataset | Provides single-cell RNA-sequencing readouts from CRISPR-based genetic perturbations, used for training and benchmarking predictive models. |
| LINCS Data [65] | Experimental Dataset | A large-scale repository containing data linking genetic and pharmacological perturbations to cellular responses, useful for cross-modal studies. |
| Gene Embeddings [65] [67] | Computational Resource | Vector representations of genes that capture functional, sequence, or network properties; used as prior knowledge to guide models like LPM and BioBO. |
| Boolean Network Models [26] | Computational Model | A graph-based representation of biological networks where species are binary nodes (ON/OFF); used for logical simulation of perturbation propagation. |
| Gaussian Process (GP) [69] [67] | Computational Model | A probabilistic model used as a surrogate for the black-box function in Bayesian Optimization, providing predictions and uncertainty estimates. |
| Acquisition Function [69] [67] | Algorithmic Component | A function (e.g., Expected Improvement) that guides Bayesian Optimization by balancing exploration and exploitation to select the next perturbation. |
Discussion: Validation Across Network Topologies
The performance of any perturbation model is intrinsically linked to its underlying assumptions about the structure of the biological network. Real-world Gene Regulatory Networks (GRNs) are not random; they are characterized by sparsity, modularity, hierarchical organization, and power-law degree distributions [64]. Models that implicitly or explicitly capitalize on these properties tend to demonstrate superior generalizability and robustness.
For instance, the success of LPM and MORPH can be partly attributed to their ability to learn representations that reflect the modular and hierarchical nature of biological systems. LPM's perturbation embeddings cluster compounds and genetic perturbations targeting the same pathway [65], while MORPH's attention mechanism is designed to discover gene programs and perturbation modules [66]. Similarly, simulation studies using realistic network generators that incorporate small-world and scale-free properties are essential for proper model benchmarking, as they provide a more faithful representation of the challenging biological reality than simplistic random networks [64]. When selecting a model, researchers must consider how well its inductive biases align with the known topological features of the system under study.
The optimization of perturbation distribution assumptions is a central problem in computational biology. As this guide illustrates, models like LPM, MORPH, and BioBO represent a shift towards more integrated, biology-aware approaches that leverage large-scale data and realistic network priors. LPM excels in integrating diverse data types and providing strong general-purpose predictions, MORPH offers granular single-cell predictions and insights into regulatory networks, and BioBO significantly accelerates the efficient discovery of optimal perturbations. The choice of model ultimately depends on the specific research goal—whether it is comprehensive prediction, mechanistic insight, or optimal experimental design. As our understanding of biological network topology continues to mature, so too will the fidelity of the models that rely upon it, driving forward discovery in drug development and basic research.
In multidisciplinary research, from systems biology to power grids, introducing controlled perturbations is a fundamental technique for probing the function and resilience of complex networks. A central challenge that emerges is data mismatch—the misalignment between a system's perturbed state and its inherent, original topological structure. This misalignment can compromise the validity of experimental conclusions, making its mitigation crucial for reliable research. Framed within the broader thesis of validating perturbation effects, this guide objectively compares computational and methodological strategies designed to realign perturbed data with a network's native architecture, providing a detailed analysis of their experimental performance and applications.
Comparative Analysis of Topology-Alignment Approaches
The following table summarizes core methodologies for mitigating data mismatch, detailing their core mechanisms and applications based on recent experimental findings.
| Methodology | Core Mechanism | Application Context | Key Performance Insight |
|---|---|---|---|
| Topological Autoencoders (TopoReformer) [70] | Uses topological loss (persistent homology) to enforce manifold-level consistency between input and latent representations, filtering perturbations that distort global structure. | OCR model defense against adversarial attacks (e.g., FGSM, PGD). | Effectively removes adversarial artifacts; maintains performance on clean data; robust against adaptive attacks (EOT, BPDA). [70] |
| Boolean & ODE Network Modeling [6] | Systematically clamps node states (on/off) and simulates network dynamics to identify critical points for state transitions and measure perturbation strength. | Gene Regulatory Networks (GRNs) for Epithelial-Mesenchymal Transition (EMT). | Identifies critical nodes (e.g., Zeb1); measures pseudo-energy barriers between states; effectiveness is duration- and noise-dependent. [6] |
| Probabilistic Distance-Based Stability Measures [71] | Employs basin stability bound and survivability bound to quantify the strength of perturbations that compromise system stability. | Power grid stability against large perturbations. | Uncovers a new class of highly vulnerable nodes linked to tree-like network structures and connectivity to lowly stable nodes. [71] |
| Spatio-Temporal Adaptive Conformal Inference (STACI) [72] | Integrates network topology and temporal dynamics into conformal prediction, using a topology-aware nonconformity score for uncertainty quantification. | Forecasting in stream networks (e.g., hydrology, transportation). | Balances prediction efficiency and coverage by leveraging both data-driven estimates and topological constraints; theoretically guaranteed validity. [72] |
| Regression and Alignment for Functional Data (RAFT) [73] | Conceptualizes network diagnostics as functions of a threshold parameter and employs supervised curve alignment to correct for misalignment. | Brain functional connectivity networks and their relationship to cognitive performance. | Improves interpretability and generalizability by correcting for confounding in network diagnostics, leading to better regression parameter estimation. [73] |
Experimental Protocols and Workflows
This section details the experimental methodologies and workflows that generate the quantitative data used for comparison.
Topological Purification for Adversarial Defense
The TopoReformer pipeline employs a topological autoencoder to purify perturbed inputs before they are processed by a target model. The workflow, illustrated below, is designed to be model-agnostic. [70]
Diagram 1: Topological purification and reformation workflow.
The protocol involves a Freeze-Flow training paradigm: the primary encoder's weights are frozen, and gradients are routed through an auxiliary module. This encourages the model to rely on topology-consistent latent representations. The topological autoencoder is trained with a loss function that enforces consistency between the persistent homology of the input and its latent representation, ensuring the global structure (e.g., connectivity, loops in text characters) is preserved while local, adversarial noise is filtered out. [70]
Probing State Transitions in Gene Regulatory Networks
To study cell state transitions like the Epithelial-Mesenchymal Transition (EMT), researchers use a combined Boolean and Ordinary Differential Equation (ODE) approach on a well-defined GRN. The experimental protocol is as follows: [6]
- Network Definition: A GRN with 26 nodes and 100 edges is used, where nodes represent genes/proteins and edges represent regulatory interactions. [6]
- Initial State Setup: The system is initialized into a stable epithelial (E) state. [6]
- Perturbation Application: One or more network nodes are "clamped" to a new value (ON or OFF in the Boolean model; a high or low value in the ODE model) for a specific duration
T. [6] - Dynamic Simulation: The network's evolution is simulated after the perturbation is removed.
- Outcome Assessment: The final stable state is classified as either E or mesenchymal (M). A successful transition (EMT) is recorded if the system moves from E to M. This process is repeated for various single- and double-node perturbations to identify the most potent inducers of the state transition. [6]
Quantifying Stability in Power Grids
To move beyond simple stability identification and quantify the strength of dangerous perturbations, researchers use probabilistic distance-based stability measures. The experimental protocol involves: [71]
- Modeling: Using a dynamic model of a power grid that includes its network topology.
- Perturbation Sampling: Applying a large set of plausible large perturbations to the system's stable synchronous state.
- Stability Quantification:
- Basin Stability Bound: Measures the strength of perturbations beyond which the system cannot return to its original stable state (asymptotic behavior).
- Survivability Bound: A newer measure that quantifies the strength of perturbations beyond which the system's trajectory leaves a predefined safe operating region (transient behavior). [71]
- Topological Analysis: Correlating these stability bounds with network features like node connectivity and tree-like structures to identify vulnerable elements. [71]
The Scientist's Toolkit: Essential Research Reagents & Solutions
The table below lists key computational tools and methodological "reagents" essential for conducting research in this field.
| Research Reagent / Solution | Function / Application |
|---|---|
| Topological Autoencoder | The core component for topology-aware purification; uses a persistent homology loss to enforce structural consistency between input and latent spaces. [70] |
| RACIPE (Random Circuit Perturbation) | An algorithm that generates an ensemble of ODE models with randomized parameters from a given GRN topology, allowing for robust analysis of network dynamics. [6] |
| Boolean Network Model | A discrete modeling framework that abstracts gene expression into binary states (ON/OFF), ideal for studying multistability and identifying key regulators in large networks. [6] |
| Basin Stability & Survivability Bound | Probabilistic metrics used to quantify the robustness of a complex system (e.g., a power grid) against large perturbations, moving beyond traditional linear stability analysis. [71] |
| H-Irregularity Strength (Graph Labeling) | A graph-theoretic metric used to model and optimize hybrid network topologies by measuring imbalance in vertex degrees, which aids in load balancing and communication flow. [74] |
| Spatio-Temporal Conformal Prediction | A framework for providing uncertainty quantification with statistical guarantees on predictions made over topologically complex structures like stream networks. [72] |
The mitigation of data mismatch is not a one-size-fits-all endeavor. As the compared approaches demonstrate, the optimal strategy is deeply contextual. Topological Autoencoders offer a powerful, model-agnostic defense against adversarial noise, while Boolean/ODE modeling provides a granular, mechanistic understanding of state transitions in biological systems. For physical infrastructures like power grids, probabilistic stability measures give crucial, quantifiable insights into resilience. The emerging trend across all domains is a shift from treating network topology as a static backdrop to actively leveraging its structure—through graph labeling, topological data analysis, or topology-aware algorithms—to guide the realignment process, ensuring that insights drawn from perturbations are both valid and actionable.
First-Passage Approaches for Optimizing Training Perturbations in ML Models
The training of sophisticated machine learning models, particularly deep neural networks, is often a computationally intensive and time-consuming process that significantly exceeds inference timescales. To address this challenge, researchers have developed various protocols that intentionally perturb the learning process to improve training efficiency or model generalization. Traditional perturbation methods—including shrink and perturb, warm restarts, and stochastic resetting—have typically been designed through intuitive reasoning and empirical trial and error, lacking a principled theoretical framework for their optimization [75] [76].
First-passage theory provides a powerful mathematical foundation for rationally designing and optimizing these training perturbations by conceptualizing the learning process as a first-passage process. In this framework, model training is treated as a stochastic journey toward a target performance threshold (such as a specific test accuracy), with the first-passage time representing the point when this threshold is first reached [76]. This approach allows researchers to systematically analyze how periodic perturbations affect the training dynamics and convergence properties of machine learning models. By viewing the training process through this lens, it becomes possible to move beyond heuristic approaches and develop perturbation strategies that are both predictable and effective across diverse model architectures and datasets [75].
The core insight of this methodology lies in recognizing that if the unperturbed learning process reaches a quasi-steady state, its response to perturbations at a single frequency can predict behavior across a wide range of frequencies. This linear response property enables efficient optimization of perturbation protocols without exhaustive testing of all possible parameter combinations [75] [76]. The resulting framework has demonstrated significant transferability across different datasets, architectures, optimizers, and even task types, establishing first-passage theory as a versatile tool for improving machine learning training methodologies.
Theoretical Framework and Key Methodologies
Fundamental Principles of First-Passage Processes
The application of first-passage theory to machine learning training begins with formalizing the learning process as a stochastic dynamical system. In this formulation, the state of a machine learning model at any given time is represented by a vector (θ) that encompasses all trainable parameters—including weights, biases, and relevant hyperparameters. The training process is characterized by a propagator G(θ,t), which describes the probability distribution of the model being in state θ at time t during its progression toward a target performance threshold [76].
The first-passage time is defined as the random variable T representing the earliest time at which the model's performance (typically measured on a test set) reaches or exceeds a predefined target level. This threshold is treated as an absorbing boundary in the state space, meaning that once reached, the process terminates. The stochastic nature of training—arising from factors such as minibatch sampling and random initialization—naturally gives rise to a distribution of first-passage times rather than a deterministic value [76]. The survival probability, denoted as Ψ_T(t) ≡ Pr(T > t), quantifies the fraction of models that have not yet reached the target threshold by time t and provides a fundamental characterization of the training dynamics.
When perturbations are introduced into the training process at regular intervals P, the first-passage time T_P of the perturbed process follows a distinct distribution. The relationship between the perturbed and unperturbed first-passage times is given by:
[ TP = \begin{cases} T & \text{if } T \leq P, \ P + \tauP(\boldsymbol{\theta}) & \text{if } T > P, \end{cases} ]
where (\tau_P(\boldsymbol{\theta})) represents the residual time needed to reach the target after applying the first perturbation at time P [76]. This formulation enables researchers to analytically compute the expected change in training time resulting from specific perturbation protocols, providing a quantitative basis for comparing different strategies.
First-Page Formalism for Training Perturbations
The first-passage approach enables a systematic methodology for analyzing and optimizing training perturbations. The theoretical framework developed by Keidar et al. demonstrates that the mean first-passage time under periodic perturbations can be expressed in terms of the properties of the unperturbed process [76]. This allows researchers to predict the effect of various perturbation strategies without performing exhaustive experimental trials for each possible configuration.
A key insight of this approach is that when the unperturbed learning process reaches a quasi-steady state, its response to perturbations exhibits a linear response property that enables prediction of behavior across a wide range of perturbation frequencies from measurements at just a single frequency [75]. This significantly reduces the computational resources required to identify optimal perturbation protocols. The framework has been successfully applied to optimize three primary types of training perturbations: (1) shrink and perturb, which involves partially resetting model parameters with added noise; (2) partial stochastic resetting, which reinitializes only a subset of parameters (typically smaller weights); and (3) full stochastic resetting, which reverts the entire model to a previous checkpoint with some probability [76].
The mathematical formalism allows researchers to compute the expected acceleration or deceleration resulting from each perturbation type by analyzing the properties of the unperturbed first-passage time distribution and the specific nature of the perturbation operator. This represents a significant advancement over traditional trial-and-error approaches to training perturbation design.
Experimental Protocols and Performance Analysis
Implementation and Experimental Design
The practical application of first-passage approaches to optimizing training perturbations follows a structured experimental protocol that begins with characterizing the unperturbed training process. Researchers first measure the first-passage time distribution of a model training without perturbations to a predefined target accuracy. This establishes a baseline against which perturbed training processes can be compared and provides the essential input parameters for the response theory predictions [76].
In a typical experiment, multiple training runs are conducted for both unperturbed and perturbed processes to account for the inherent stochasticity in neural network optimization. For the perturbed experiments, interventions are applied at regular intervals P, with the specific nature of the perturbation depending on the protocol being tested. For shrink and perturb strategies, this involves resetting parameters to a weighted average of their current values and their values at a previous checkpoint, often with additional noise injection. For stochastic resetting approaches, parameters are either partially or completely reverted to earlier states according to predefined rules [76].
The experimental setup used to validate the first-passage approach typically employs standard benchmark datasets such as CIFAR-10 and CIFAR-100, with well-established model architectures including ResNet-18 and fully connected networks. Training is performed using common optimizers like SGD, SGD with momentum, and Adam to demonstrate the transferability of the approach across different optimization methods [76]. The key outcome measures include the mean first-passage time, the variance of the first-passage time distribution, and the final generalization performance of the trained models, all of which provide insights into the effectiveness of different perturbation strategies.
Quantitative Performance Comparison
The effectiveness of first-passage optimized perturbations is demonstrated through comprehensive experimental comparisons across different model architectures, datasets, and perturbation types. The table below summarizes key performance metrics for various perturbation strategies applied to CIFAR-10 classification using ResNet-18:
Table 1: Performance comparison of different perturbation strategies on CIFAR-10 classification using ResNet-18
| Perturbation Type | Optimal Interval (P) | Mean FPT Acceleration | Generalization Improvement | Transferability to Other Datasets |
|---|---|---|---|---|
| Shrink & Perturb | 40 epochs | 22% | +1.3% accuracy | High (CIFAR-100, MNIST) |
| Partial Reset | 25 epochs | 31% | +0.9% accuracy | Moderate |
| Full Stochastic Reset | 60 epochs | 18% | +1.1% accuracy | High |
| Warm Restarts | 80 epochs | 27% | +0.7% accuracy | High |
The data reveal that perturbation strategies optimized using the first-passage approach achieve significant reductions in mean first-passage time (ranging from 18% to 31%) while simultaneously improving generalization performance [76]. This dual benefit of accelerated convergence and enhanced model quality demonstrates the practical value of the methodology. The transferability of these improvements across different datasets and architectures highlights the robustness of the approach and suggests that the first-passage framework captures fundamental aspects of the training dynamics that transcend specific model implementations.
Further analysis indicates that different perturbation strategies excel in different operational contexts. For instance, partial reset strategies tend to provide the greatest acceleration in mean first-passage time, while shrink and perturb approaches often yield the largest improvements in final generalization performance [76]. This nuanced understanding enables practitioners to select perturbation strategies that align with their specific training objectives, whether prioritizing rapid convergence or maximal model quality.
Comparative Analysis with Alternative Approaches
The first-passage approach to training perturbation represents a significant departure from and improvement over alternative methods for enhancing machine learning training. The table below compares the first-passage methodology with other common approaches to training optimization:
Table 2: Comparison of first-passage approach with alternative training optimization methods
| Methodology | Theoretical Foundation | Required Prior Experiments | Prediction Accuracy | Computational Overhead |
|---|---|---|---|---|
| First-Passage Approach | Statistical Physics & Stochastic Processes | Minimal (single frequency) | High (73-89% variance explained) | Low |
| Traditional Trial-and-Error | Heuristic & Empirical | Extensive (full parameter sweep) | Moderate | High |
| Topology-Based Prediction | Network Science & Graph Theory | Moderate (multiple network measurements) | Variable (60-73% accuracy) | Moderate |
| Hyperparameter Optimization | Bayesian Optimization | Extensive (multiple full trainings) | High | Very High |
The first-passage approach distinguishes itself through its strong theoretical foundation in statistical physics and stochastic processes, which enables accurate predictions of perturbation effects with minimal prior experimental data [75] [76]. This contrasts sharply with traditional trial-and-error methods that require exhaustive parameter sweeps, and with hyperparameter optimization approaches that necessitate multiple complete training runs. The methodology also outperforms pure topology-based prediction methods, which have demonstrated approximately 65-73% accuracy in related biological network perturbation problems but lack the specific theoretical connection to training dynamics [77].
A key advantage of the first-passage framework is its ability to provide theoretically-grounded predictions of optimal perturbation parameters without requiring extensive experimental trials. Where traditional methods might need to test dozens of perturbation frequencies to identify optimal values, the first-passage approach can predict the full frequency response from measurements at just a single frequency, dramatically reducing the computational resources required for optimization [75]. This efficiency makes the approach particularly valuable in resource-constrained environments or when working with very large models where each training trial represents a substantial computational investment.
Visualization of Methodologies and Workflows
First-Passage Approach Methodology
The following diagram illustrates the core workflow of the first-passage approach for optimizing training perturbations in machine learning models:
First-Passage Optimization Workflow
The visualization captures the key insight that enables the efficiency of the first-passage approach: the ability to predict optimal perturbation parameters across all frequencies from measurements at just a single frequency [75]. This linear response property significantly reduces the experimental burden compared to traditional methods that require exhaustive testing of multiple perturbation frequencies.
Perturbation Framework Schematic
The diagram below illustrates the conceptual framework of training with periodic perturbations and its relationship to first-passage theory:
Training with Periodic Perturbations
This schematic illustrates the fundamental equation governing perturbed first-passage times: ( TP = \begin{cases} T & \text{if } T \leq P, \ P + \tauP(\boldsymbol{\theta}) & \text{if } T > P, \end{cases} ) where ( TP ) represents the first-passage time of the perturbed process, T is the first-passage time of the unperturbed process, P is the perturbation interval, and ( \tauP(\boldsymbol{\theta}) ) is the residual time to reach the target after the first perturbation [76]. This formulation enables the theoretical analysis of how different perturbation strategies affect training dynamics.
Research Toolkit and Practical Applications
Essential Research Reagents and Computational Tools
Implementing first-passage approaches for training perturbation optimization requires specific computational tools and methodological components. The table below details key elements of the research toolkit:
Table 3: Essential research reagents and computational tools for first-passage perturbation studies
| Tool/Component | Function | Example Implementations |
|---|---|---|
| First-Passage Time Distribution Analyzer | Quantifies baseline training stochasticity | Custom Python scripts with statistical analysis libraries |
| Perturbation Protocol Modules | Implements specific perturbation strategies | Shrink & perturb, partial reset, full stochastic resetting |
| Linear Response Predictor | Extrapolates single-frequency measurements to full spectrum | Numerical solvers for response theory equations |
| Benchmark Datasets | Provides standardized testing environments | CIFAR-10, CIFAR-100, MNIST |
| Model Architectures | Represents different network topologies | ResNet-18, fully connected networks |
| Optimization Algorithms | Tests transferability across optimizers | SGD, SGD with momentum, Adam |
The research toolkit emphasizes modularity and transferability, allowing researchers to test perturbation strategies across diverse experimental conditions [76]. The benchmark datasets provide standardized environments for initial validation, while the variety of model architectures and optimizers enables assessment of methodological generality. The linear response predictor represents the core computational innovation that enables prediction of full frequency response from minimal experimental data.
Applications Across Domains
The first-passage approach to optimizing perturbations has demonstrated significant value beyond standard image classification tasks, showing particular promise in specialized domains including scientific and biomedical applications. In regulatory network inference, similar perturbation strategies have been employed to overcome non-identifiability issues in gene regulatory networks and microbial communities [78]. While these biological applications typically use Boolean network models rather than deep neural networks, they share the fundamental challenge of optimizing perturbation strategies to maximize information gain while minimizing experimental costs.
In scientific machine learning, where models are employed to learn physical systems or simulate molecular dynamics, training perturbations optimized through first-passage approaches can accelerate convergence while maintaining physical consistency [76]. The transferability of the approach across different network architectures—from fully connected networks to modern residual networks—suggests broad applicability across computational science domains where model training represents a significant computational bottleneck.
The methodology has also shown promise in addressing label noise and catastrophic forgetting in sequential learning tasks. Stochastic resetting approaches, when properly optimized using first-passage principles, can mitigate overfitting to noisy labels and improve model generalization [76]. This resilience to data quality issues further enhances the practical utility of the approach in real-world applications where perfectly curated datasets are often unavailable.
First-passage approaches provide a powerful, theoretically-grounded framework for optimizing training perturbations in machine learning models. By conceptualizing the training process as a first-passage event and leveraging linear response theory, these methods enable efficient identification of optimal perturbation strategies with minimal experimental overhead. The demonstrated improvements in training acceleration—ranging from 18% to 31% reduction in mean first-passage time—coupled with consistent generalization gains across diverse datasets and architectures, establish this methodology as a valuable addition to the machine learning toolkit.
The most significant advantage of the first-passage approach lies in its predictive capability, which allows researchers to extrapolate from limited experimental data to identify optimal perturbation parameters across a wide frequency spectrum [75] [76]. This represents a fundamental advancement over traditional trial-and-error approaches that require exhaustive parameter sweeps. The theoretical foundation in stochastic processes and statistical physics provides principled guidance for perturbation design that transcends specific model implementations and application domains.
Future research directions include extending the framework to more complex perturbation strategies, adapting the methodology for federated and distributed learning environments, and exploring applications in emerging paradigms such as meta-learning and neural architecture search. As machine learning models continue to increase in scale and complexity, principled approaches for optimizing training efficiency like the first-passage method will become increasingly essential for sustainable and accessible artificial intelligence research and development.
Protocols for Enhancing Explanation Fidelity and Stability in XAI
In high-stakes domains such as drug development, the need for transparent and trustworthy artificial intelligence (AI) models is of utmost importance [60]. Explainable AI (XAI) seeks to bridge the gap between model complexity and human understanding by providing rationale for model predictions. However, a significant challenge remains: how to robustly evaluate and ensure the fidelity (faithfulness) and stability (robustness) of these explanations, particularly when validating perturbation effects across diverse network topologies [60] [79]. This guide provides a comparative analysis of contemporary frameworks and protocols designed to address this critical research problem.
Comparative Analysis of XAI Evaluation Frameworks
Evaluating XAI methods requires robust frameworks that mitigate issues like Out-of-Distribution (OOD) data and information leakage. The table below compares state-of-the-art evaluation frameworks based on their core methodology, advantages, and limitations.
Table 1: Comparison of XAI Evaluation Frameworks
| Framework | Core Methodology | Key Advantages | Limitations |
|---|---|---|---|
| F-Fidelity [79] | Explanation-agnostic fine-tuning with stochastic masking. | Robust to OOD issues; prevents information leakage; computationally efficient; infers explanation sparsity. | Requires a fine-tuning step; performance may depend on masking strategy. |
| ROAR (Remove and Retrain) [79] | Retrains model on explanation-guided perturbed data. | Addresses OOD problem by retraining on a modified dataset. | Introduces information leakage and label bias; computationally expensive. |
| Perturbation-based Faithfulness Evaluation [60] | Perturbs features based on importance and measures performance impact. | Intuitive; model-agnostic. | Highly sensitive to Perturbation Method (PM) choice; can cause OOD samples. |
| Consistency-Magnitude-Index (CMI) [60] | Combines Perturbation Effect Size (PES) and Decaying Degradation Score (DDS). | Quantifies separation and consistency of relevant/irrelevant features; more faithful than AUPC. | Requires multiple perturbation methods for robust evaluation. |
Quantitative Performance Comparison of XAI Methods
The choice of XAI method significantly impacts explanation quality and computational cost. The following table summarizes experimental data from comparative studies.
Table 2: Experimental Performance of XAI Methods Across Modalities
| XAI Method | Category | Faithfulness (Score) | Localization Accuracy (IoU) | Computational Efficiency | Key Findings |
|---|---|---|---|---|---|
| RISE [80] | Perturbation-based | High | Moderate | Low (Computationally expensive) | Highest faithfulness score in comparative studies, but slow. |
| Grad-CAM [80] | Attribution-based | Moderate | High (30-35% overlap with human annotation) | High | Good class-discriminative localization; requires internal model access. |
| Graph Signal Processing [81] | Graph-based | High (Comparable to SHAP) | N/A | Very High (70x faster than SHAP) | Enables real-time decision support; suitable for graph-based network topologies. |
| LIME [82] | Surrogate-based | Variable | N/A | Moderate | Explanations depend on surrogate model quality; non-deterministic due to sampling. |
| SHAP [81] | Game Theory-based | High | N/A | Low | Theoretically sound; can be computationally intensive for large models. |
Detailed Experimental Protocols
Protocol 1: F-Fidelity Evaluation Framework
The F-Fidelity framework provides a robust methodology for assessing explanation faithfulness while mitigating OOD and information leakage issues [79].
Workflow Overview
Methodology:
- Input: A pre-trained classifier
f, a dataset, and an explanation function to be evaluated. - Explanation-Agnostic Fine-tuning:
- Generate augmented training samples by applying stochastic masking (e.g., randomly dropping pixels, time steps, or tokens) to the original inputs.
- Fine-tune the pre-trained model
fusing these augmented samples to create a surrogate model. This step ensures the model becomes robust to in-distribution masked inputs without bias from any specific explainer.
- Evaluation:
- For a given input, generate an explanation (e.g., a feature attribution map).
- Generate a stochastic mask conditioned on the explanation's importance scores.
- Apply the mask to the input and pass it through the fine-tuned surrogate model.
- Measure the drop in the predicted probability for the target class. A larger drop indicates a more faithful explanation, as the features deemed important were truly crucial for the model's prediction.
- Output: The F-Fidelity score, which can be computed across multiple mask sizes (sparsity levels) to provide a comprehensive faithfulness assessment [79].
Protocol 2: Faithfulness Evaluation with Multiple Perturbation Methods
This protocol emphasizes the critical impact of perturbation method (PM) selection, especially for time-series data or other sensitive domains [60].
Workflow Overview
Methodology:
- Explanation Generation: For a given input and model prediction, compute a feature attribution map using an XAI method (e.g., SHAP, Integrated Gradients).
- Multi-Perturbation Strategy:
- Select a diverse set of PMs (e.g., adding noise, replacing with mean values, zeroing out, linear interpolation). In time-series classification, using at least 23 different PMs has been recommended for a robust evaluation [60].
- Perturb the input features in two distinct orders: MoRF (Most Relevant First) and LeRF (Least Relevant First).
- Impact Measurement:
- For each PM and perturbation order, compute the model's performance (e.g., prediction probability for the target class) on the perturbed inputs.
- Avoid using the Area Under the Perturbation Curve (AUPC) alone, as it can be misleading [60].
- Metric Calculation:
- Perturbation Effect Size (PES): Measures how consistently an AM distinguishes important from unimportant features.
- Decaying Degradation Score (DDS): Quantifies the degree of separation between relevant and irrelevant features.
- Consistency-Magnitude-Index (CMI): A composite metric combining PES and DDS to streamline the identification of high-performing AMs [60].
- Output: A faithfulness evaluation of the XAI method that is robust to the choice of perturbation method.
This section details key computational tools and metrics essential for implementing the described protocols.
Table 3: Key Research Reagents and Computational Tools
| Tool/Resource | Type | Function in XAI Validation | Applicable Topologies/Modalities |
|---|---|---|---|
| Stochastic Masking Generator | Algorithm | Generates in-distribution masked samples for fine-tuning and evaluation in F-Fidelity. | General (Images, Time Series, Text) |
| Diverse Perturbation Methods (PMs) | Algorithm Library | Applies various input transformations (noise, mean, zero) to test explanation robustness. | Critical for Time Series, also Images, Text |
| Consistency-Magnitude-Index (CMI) | Evaluation Metric | Combines PES and DDS for a faithful assessment of feature importance attribution. | General |
| XSMILES [83] | Visualization Tool | Interactive visualization for explaining model predictions based on SMILES strings in drug discovery. | Molecular Graphs (Chemistry) |
| Graph Signal Processing [81] | Analysis Framework | Models MLPs as graphs; uses eigencentrality for fast, interpretable key driver identification. | Graph-based Networks, Water Systems |
| Quantus [82] | Software Toolkit | Provides a comprehensive suite of metrics for quantitatively evaluating XAI explanations. | General |
Ensuring high-fidelity and stable explanations in XAI requires moving beyond single-metric, single-perturbation evaluations. Frameworks like F-Fidelity offer a principled approach to mitigate distribution shift and information leakage [79]. Furthermore, employing a diverse set of perturbation methods and composite metrics like the Consistency-Magnitude-Index (CMI) is critical for a faithful assessment, especially when validating effects across different network topologies and data modalities [60]. The choice of protocol should be guided by the specific model architecture, data type, and the required balance between computational efficiency and evaluation rigor. For drug development professionals, leveraging domain-specific tools like XSMILES [83] can further enhance the interpretability and trust in AI-driven models.
Validation Frameworks and Comparative Analysis of Perturbation Techniques
In network biology, the ability to accurately predict the effects of perturbations—such as gene knockouts or drug treatments—is fundamental to understanding cellular processes and advancing therapeutic development. The core challenge lies in validating these predictions without complete knowledge of the system's kinetic parameters. Research indicates that network topology (the structure of interactions between biochemical entities) can provide 65-80% of the information needed to accurately predict perturbation effects, even in the absence of detailed dynamical data [9]. This insight has catalyzed the development of sophisticated validation frameworks that can reliably quantify the faithfulness of perturbation-based explanations across different network types.
As high-throughput technologies enable the systematic mapping of the human interactome, covering over 170,000 physical interactions between approximately 14,000 biochemical entities, the need for robust validation metrics has become increasingly pressing [9]. The field of explainable AI (XAI) has paralleled these developments, particularly for deep learning models used in high-stakes domains like medicine and drug discovery. In this context, feature attribution methods (AMs) have emerged as crucial tools for interpreting model predictions by identifying the most influential input features [60]. This comparison guide examines two innovative validation metrics—the Consistency-Magnitude-Index (CMI) and Perturbation Effect Size (PES)—that are transforming how researchers quantify and validate perturbation effects across diverse network topologies and analytical models.
Theoretical Foundations of Perturbation Analysis
Network Topology and Perturbation Spreading
Biological networks exhibit distinct structural properties that fundamentally influence how perturbations spread through the system. Key properties include sparsity (most genes affect only a few others), hierarchical organization, modularity, and degree distributions that often follow approximate power-law patterns [2] [9]. These properties create systems where perturbation effects are not uniform but follow topological pathways. The DYNAMO framework (DYNamics-Agnostic Network MOdels) demonstrates that simple distance-based topological models can achieve 65% accuracy in predicting perturbation patterns, while incorporating additional topological features like directionality and sign (activation/inhibition) can increase predictive performance to 80% [9].
Gene regulatory networks (GRNs) further exemplify how topology dictates perturbation response. Realistic GRN structures exhibit small-world properties and scale-free topologies with hierarchical organization that tend to dampen the effects of gene perturbations [2]. This structural buffering has crucial implications for experimental design in drug discovery, as it suggests network position may be more important than individual kinetic parameters when predicting perturbation outcomes.
Explainable AI and Feature Attribution Validation
In parallel with biological network research, the field of explainable AI has developed methods to validate how models interpret perturbations. Feature attribution methods explain model predictions by estimating the relevance of each input feature, with applications ranging from time-series classification to image recognition [60]. The fundamental challenge lies in validating whether these attributions faithfully reflect what was truly important to the model's decision—a property known as faithfulness or fidelity [60].
The most prevalent approach for estimating AM faithfulness is region perturbation, which systematically perturbs features based on their estimated importance and measures the impact on classifier performance [60]. However, traditional evaluation metrics like the Area Under the Perturbation Curve (AUPC) have been shown to provide misleading assessments, particularly for time-series data, necessitating more robust validation frameworks [60] [84].
Novel Validation Metrics: Comprehensive Analysis
Perturbation Effect Size (PES)
The Perturbation Effect Size addresses critical flaws in previous validation metrics that could lead to incorrect conclusions about attribution method performance [60] [84]. Traditional metrics like AUPC fail to adequately measure how consistently an attribution method distinguishes truly important features from unimportant ones. PES directly quantifies this consistency of separation by evaluating the reliability of importance rankings across different perturbation scenarios [60].
PES operates on the principle that a faithful attribution method should consistently identify the same set of important features regardless of the specific perturbation approach used for validation. This is particularly important for time-series classification models in high-stakes domains like medicine and finance, where understanding model decisions has significant consequences [60]. By focusing on consistency rather than just magnitude of effect, PES provides a more nuanced view of attribution method performance that aligns with practical deployment requirements.
Consistency-Magnitude-Index (CMI)
The Consistency-Magnitude-Index represents an integrated validation framework that combines the strengths of multiple assessment approaches [60]. CMI unifies two complementary metrics: the Perturbation Effect Size, which measures consistency, and the Decaying Degradation Score, which quantifies the degree of separation between relevant and irrelevant features [60]. This integration enables researchers to simultaneously evaluate both the reliability and discriminative power of attribution methods.
CMI operates on several key principles. First, it emphasizes the importance of evaluating attribution methods across multiple perturbation techniques rather than relying on a single approach [60]. Second, it acknowledges that the optimal perturbation method depends on both data characteristics and what the model has learned to rely on [60]. Third, it provides a standardized framework for comparing attribution method performance across different model architectures and dataset types, addressing a critical limitation of previous validation approaches.
Table 1: Comparative Analysis of Perturbation Validation Metrics
| Metric | Key Function | Advantages | Limitations | Optimal Use Cases |
|---|---|---|---|---|
| Perturbation Effect Size (PES) | Measures consistency of important/unimportant feature separation | Addresses flaws in AUPC metric; Works across perturbation methods | Does not quantify magnitude of separation | Time-series classification; High-stakes model validation |
| Consistency-Magnitude-Index (CMI) | Combines consistency and magnitude of feature separation | Integrated framework; Standardized comparison | More complex implementation | Comprehensive AM evaluation; Cross-domain comparisons |
| Area Under Perturbation Curve (AUPC) | Traditional metric for perturbation-based validation | Widely adopted; Simple interpretation | Can provide misleading results for time-series data [60] | Initial screening (with caution) |
| Decaying Degradation Score (DDS) | Quantifies degree of relevant/irrelevant feature separation | Complementary to consistency measures | Does not assess consistency alone | Combined with PES in CMI framework |
Experimental Protocols and Methodologies
Faithfulness Estimation for Attribution Methods
The validation of feature attribution methods requires a structured experimental protocol to ensure robust and reproducible assessments. The following workflow outlines the key steps for conducting a comprehensive faithfulness evaluation [60]:
Selection of Attribution Methods: Choose a diverse set of AMs representing different computational approaches (gradient-based, occlusion-based, surrogate models, etc.). Recent studies have evaluated up to 12 different AMs to ensure comprehensive comparison [60].
Perturbation Method Strategy: Employ multiple perturbation techniques rather than relying on a single approach. Research indicates that evaluations should include 23+ different perturbation methods, many specifically designed for time-series data, to account for model- and data-specific sensitivities [60].
Region Size Selection: Determine appropriate perturbation region sizes, recognizing that this parameter has comparatively lesser impact on faithfulness evaluation than perturbation method selection, though with differences in suitability across PMs [60].
Metric Calculation: Compute the Consistency-Magnitude-Index by first calculating both the Perturbation Effect Size and Decaying Degradation Score, then combining them according to the integrated framework [60].
Cross-Validation: Repeat evaluations across different model architectures (studies have investigated 5+ DL model architectures) and dataset types (binary imbalanced, binary balanced, and multiclass) to ensure robust conclusions [60].
Benchmarking Perturbative Maps
For large-scale perturbation datasets, such as those generated by CRISPR-based screens, researchers have developed standardized benchmarking pipelines. The EFAAR framework provides a structured approach for building and evaluating perturbative maps [85]:
Embedding: Reduce high-dimensional assay data (e.g., 20,000 gene expression values or million+ pixel images) to tractable numerical representations using dimensionality reduction techniques like PCA or neural network embeddings.
Filtering: Remove perturbation units that do not satisfy quality criteria, such as wells with abnormal pixel intensity or cells receiving multiple guide RNAs.
Aligning: Correct for batch effects using methods like Typical Variation Normalization, ComBat, or nearest neighbor matching to reduce technical variations.
Aggregating: Combine technical and biological replicates (e.g., multiple wells or cells with the same perturbation) using coordinate-wise mean, median, or robust methods like Tukey median.
Relating: Identify relationships between biological entities by computing distances or similarity measures between aggregated perturbation representations.
This pipeline enables two classes of benchmarks: perturbation signal benchmarks that assess consistency and magnitude of individual perturbation representations, and biological relationship benchmarks that evaluate the ability to recapitulate known biological relationships from annotated databases [85].
Comparative Performance Analysis
Quantitative Comparison of Validation Approaches
Recent comprehensive evaluations of attribution methods for neural time series classifiers provide critical insights into the performance of different validation strategies. These studies examined 12 attribution methods across 5 deep learning model architectures and 23 perturbation methods, offering one of the most complete comparisons to date [60].
Table 2: Performance Comparison of Perturbation-Based Evaluation Approaches
| Evaluation Aspect | Traditional Approaches | CMI/PES Framework | Performance Improvement |
|---|---|---|---|
| Metric Reliability | AUPC can provide misleading results [60] | Robust across data types and models | Addresses fundamental flaws in validation |
| Perturbation Method Selection | Often arbitrary choice of single PM [60] | Uses diverse set of PMs (23+) | Reduces sensitivity to PM selection |
| Model Architecture Coverage | Limited evaluation (2 architectures) | Extensive evaluation (5 architectures) | Broader applicability guarantees |
| Dataset Type Validation | Focus on single data type | Multiple types (binary, multiclass, imbalanced) | More reliable real-world performance |
| Consistency Assessment | Not specifically quantified | Explicitly measured via PES | Better alignment with faithfulness |
The results demonstrate that no single attribution method consistently outperforms all others across different model architectures and datasets [60]. Similarly, no universal optimal perturbation method exists for all scenarios. This underscores the importance of the CMI framework, which enables researchers to select the most faithful AM for their specific dataset and model combination based on systematic evaluation rather than arbitrary choices.
Domain-Specific Performance Considerations
The performance of perturbation validation metrics varies significantly across domains and data types. In time series classification, traditional metrics like AUPC have been shown to produce misleading conclusions, making PES and CMI particularly valuable for this domain [60] [84]. For biological network analysis, simple distance-based topological models achieve approximately 65% accuracy in predicting perturbation patterns, while more sophisticated approaches incorporating directionality and sign information can reach 80% accuracy [9].
In single-cell RNA sequencing studies, algorithms leveraging manifold learning and graph signal processing, such as the MELD algorithm, demonstrate 57% higher accuracy at identifying clusters of cells enriched or depleted in each condition compared to next-best-performing methods [15]. This performance advantage stems from the ability to quantify perturbation effects at single-cell resolution across continuous manifolds rather than being limited to discrete clusters.
Research Reagent Solutions and Computational Tools
Essential Research Reagents and Platforms
Table 3: Key Research Reagents and Platforms for Perturbation Studies
| Reagent/Platform | Function | Application Context |
|---|---|---|
| CRISPR-based Perturbation Libraries | Gene knockout/activation at scale | Genome-wide reverse genetics screens [85] [3] |
| Perturb-seq | Single-cell RNA-seq readout of genetic perturbations | High-resolution mapping of perturbation effects [2] [85] |
| Single-cell RNA Sequencing | Transcriptome profiling at cellular resolution | Measuring molecular responses to perturbations [15] |
| Cellular Imaging Platforms | High-content phenotypic screening | Morphological profiling of perturbation effects [85] |
| Graph Construction Algorithms | Build cellular manifolds from high-dimensional data | Represent transcriptomic state space for perturbation analysis [15] |
Computational Tools and Software Packages
The field of perturbation analysis has seen rapid development of specialized computational tools. For higher-order network analysis, the Q-analysis Python package enables identification of multi-node interactions beyond traditional pairwise analysis by constructing simplicial complexes from graphs and computing topological metrics [86]. For single-cell perturbation analysis, the MELD algorithm implements sample-associated relative likelihood estimation using graph signal processing to quantify perturbation effects across cellular manifolds [15].
The EFAAR benchmarking codebase (github.com/recursionpharma/EFAAR_benchmarking) provides a standardized framework for constructing and evaluating perturbative maps across different technologies and modalities [85]. For gene regulatory network analysis, tools implementing the DYNAMO framework enable perturbation effect prediction based on network topology alone, bypassing the need for expensive kinetic parameter measurement [9].
Implications for Drug Development and Network Medicine
The advancement of robust perturbation validation metrics has significant implications for drug discovery and development. The demonstrated ability to predict perturbation patterns with 65-80% accuracy using topological information alone suggests that network-based approaches can significantly reduce the experimental burden in target identification and validation [9]. Furthermore, the application of faithfulness metrics like CMI and PES to AI models used in drug discovery ensures that explanatory insights align with actual model reasoning rather than misleading artifacts.
In network medicine, understanding how perturbations spread through biological networks is crucial for identifying therapeutic targets and predicting side effects. The DYNAMO framework shows that network topology alone can predict with ~80% accuracy the directionality of gene expression and phenotype changes in knock-out and overproduction experiments [9]. This predictive capability enables more efficient prioritization of candidate targets before embarking on expensive experimental validation.
The integration of single-cell technologies with perturbation screening creates unprecedented opportunities for mapping the cellular effects of genetic and chemical perturbations. The MELD algorithm's ability to identify cell populations specifically affected by perturbations at the appropriate level of granularity enables more precise characterization of drug mechanisms and toxicities [15]. Similarly, the construction of unified perturbative maps facilitates the discovery of novel biological relationships that can inform drug repurposing and combination therapy strategies [85].
As the field progresses, the continued development and validation of robust metrics for assessing perturbation effects will be essential for translating network biology insights into clinical applications. The Consistency-Magnitude-Index and Perturbation Effect Size represent significant advances in this direction, providing researchers with more faithful tools for evaluating explanatory methods across diverse network topologies and biological contexts.
Comparative Analysis of Perturbation Techniques Across Network Types
In network biology, the systematic mapping of interactions between biochemical entities has fueled the development of powerful frameworks for understanding cellular processes and disease states. A fundamental challenge in this field involves predicting how perturbations—such as gene knockouts or drug treatments—spread through biological networks to influence cellular behavior. The core premise of perturbation analysis is that changes in the concentration or activity of biological species propagate along physical interactions and reactions, affecting various parts of the interactome. Understanding these propagation patterns is crucial for applications ranging from basic biological discovery to drug target identification in therapeutic development.
The development of high-throughput technologies has enabled researchers to generate perturbation data at unprecedented scales, creating opportunities to build comprehensive "perturbative maps" that capture system-wide cellular responses to interventions. However, a significant challenge persists: while network topology (the wiring diagram of interactions) is increasingly well-mapped, we often lack complete knowledge of the kinetic parameters governing the dynamics of these interactions. This limitation has prompted critical investigations into how much information about perturbation effects can be recovered from topology alone, and what experimental and computational approaches best enable accurate network inference and prediction of perturbation outcomes.
Theoretical Foundations of Network Comparison Methods
Categories of Network Comparison Approaches
The problem of comparing networks arises frequently when assessing the effects of perturbations or differences between biological states. Network comparison methods can be broadly classified based on whether they assume known correspondence between nodes in the networks being compared. Known Node-Correspondence (KNC) methods apply when two networks share the same node set (e.g., the same set of genes or proteins) with known pairwise correspondence. In contrast, Unknown Node-Correspondence (UNC) methods can compare any pair of graphs, even with different sizes and densities, by summarizing global structure into comparable statistics [87].
KNC methods include approaches like direct comparison of adjacency matrices using various norms (Euclidean, Manhattan, Canberra, or Jaccard distances) and the DeltaCon method, which compares networks by measuring the difference in node similarity matrices. DeltaCon calculates similarity matrices S = [I + ε²D - εA]⁻¹, where A is the adjacency matrix and D is the degree matrix, then computes distance using the Matusita distance between similarity matrices [87]. UNC methods encompass alignment-based approaches, graphlet-based methods, spectral methods, and recently proposed techniques like Portrait Divergence and NetLSD, which enable comparison of networks with different node sets by capturing their global structural properties [87].
Information Content in Network Topology
A critical question in perturbation analysis concerns how much dynamical information can be recovered from network topology alone. Research on DYNAmics-Agnostic Network MOdels (DYNAMO) has demonstrated that surprisingly accurate predictions of perturbation patterns can be achieved without detailed kinetic parameters. In studies of biological models with known kinetics, simple distance-based models achieved approximately 65% accuracy in recovering true perturbation patterns, while more sophisticated topological models incorporating directionality and sign (activation/inhibition) of interactions could increase predictive power to 80% [9].
This remarkable performance stems from the property of "sloppiness" in biological networks, where only a small subset of parameters significantly affects overall dynamics. The robustness of perturbation patterns to parameter changes suggests that topology plays a dominant role in determining system behavior. This insight has profound implications for drug discovery, as it suggests that the increasingly accurate topological models of human interactome can potentially bypass expensive kinetic constant measurement when predicting perturbation effects [9].
Quantitative Benchmarking of Perturbation Analysis Methods
Performance Evaluation of Network Inference Methods
Rigorous benchmarking is essential for evaluating the performance of different network inference methods applied to perturbation data. The CausalBench framework, developed for this purpose, employs both biology-driven and statistical evaluations. Key metrics include the mean Wasserstein distance, which measures whether predicted interactions correspond to strong causal effects, and the false omission rate (FOR), which quantifies the rate at which true causal interactions are missed by a model [88] [89].
Recent benchmarking studies have revealed important insights into the capabilities of different methodological approaches. A systematic evaluation of state-of-the-art causal inference methods using CausalBench highlighted how poor scalability of existing methods often limits performance. Contrary to theoretical expectations, methods using interventional information frequently do not outperform those using only observational data, particularly in real-world biological systems as opposed to synthetic benchmarks [88]. This surprising finding underscores the importance of rigorous benchmarking on biologically relevant datasets.
Table 1: Performance Comparison of Network Inference Methods on CausalBench
| Method Category | Representative Methods | Mean Performance (F1 Score) | Strengths | Limitations |
|---|---|---|---|---|
| Observational | PC, GES, NOTEARS | 0.15-0.25 | Broad applicability | Struggle with directionality |
| Interventional | GIES, DCDI variants | 0.18-0.28 | Leverages causal information | Poor scalability |
| Challenge Winners | Mean Difference, Guanlab | 0.30-0.35 | Better scalability | Limited evaluation history |
Benchmarking Foundation Models for Perturbation Prediction
The emergence of foundation models pre-trained on large-scale single-cell RNA sequencing data (e.g., scGPT and scFoundation) has introduced new possibilities for predicting post-perturbation gene expression profiles. However, recent benchmarking studies have yielded surprising results. When evaluated on Perturb-seq datasets, these foundation models were outperformed by simple baseline models that predict post-perturbation expression by averaging training examples [90].
Even more notably, standard machine learning models incorporating biologically meaningful features such as Gene Ontology vectors significantly outperformed foundation models. For instance, Random Forest regressors using GO features achieved Pearson correlation values in differential expression space of 0.739, 0.586, 0.480, and 0.648 across four benchmark datasets (Adamson, Norman, Replogle K562, and Replogle RPE1), compared to 0.641, 0.554, 0.327, and 0.596 for scGPT [90]. These results highlight both the limitations of current benchmarking approaches and the importance of incorporating biological prior knowledge.
Table 2: Performance Comparison of Perturbation Prediction Methods on Replogle Dataset
| Method | Pearson Delta (K562) | Pearson Delta (RPE1) | Computational Efficiency | Biological Interpretability |
|---|---|---|---|---|
| Train Mean | 0.373 | 0.628 | High | Low |
| scGPT | 0.327 | 0.596 | Medium | Medium |
| scFoundation | 0.269 | 0.471 | Medium | Medium |
| RF with GO features | 0.480 | 0.648 | Medium | High |
| RF with scGPT embeddings | 0.421 | 0.635 | Medium | Medium |
Experimental Protocols for Network Perturbation Studies
Dynamic Least-Squares Modular Response Analysis (DL-MRA)
Dynamic Least-squares Modular Response Analysis (DL-MRA) represents a significant advancement in network inference from perturbation time course data. This approach specifies sufficient experimental perturbation time course data to robustly infer arbitrary two and three-node networks, addressing several limitations of previous methods. DL-MRA can capture critical network properties including edge sign and directionality, cycles with feedback or feedforward loops, dynamic network behavior, edges external to the network, and maintains robust performance with experimental noise [10].
The experimental protocol for DL-MRA requires n perturbation time courses for an n-node system. Each node must be perturbed at least once, and the system response must be measured across multiple time points. The network dynamics are described using ordinary differential equations, with edge weights connected to system dynamics through the Jacobian matrix. The approach uses a least-squares estimation to determine Jacobian elements from perturbation time courses, enabling reconstruction of signed, directed network structures including self-regulation and external stimuli effects [10].
Figure 1: DL-MRA Experimental Workflow for Network Inference from Perturbation Time Courses
Parameter Estimation in Gene Regulatory Networks
Parameter estimation represents a fundamental challenge in building quantitative models of biological networks. Community-based efforts like the DREAM challenges have established standardized protocols for evaluating parameter estimation methods. In a typical parameter estimation challenge, participants are given the topology of a regulatory network and must determine parameter values from a limited "budget" of experimental data that can be purchased from a virtual catalog of available assays [91].
The experimental protocol involves an iterative loop of experiments and computation, where participants strategically select which data to acquire based on current parameter estimates. Successful strategies typically combine state-of-the-art parameter estimation with varied experimental methods, particularly fluorescence imaging data that provides dynamic protein information. Aggregating independent parameter predictions across multiple teams often produces better solutions than any single approach, highlighting the value of collaborative methods in tackling complex parameter estimation problems [91].
Research Reagent Solutions for Perturbation Studies
Essential Materials for Perturbation Experiments
Table 3: Key Research Reagents for Network Perturbation Studies
| Reagent/Category | Function | Example Applications |
|---|---|---|
| CRISPR-Cas9 Libraries | Gene knockout via targeted DNA cleavage | Genome-scale loss-of-function screens |
| CRISPRi/a Systems | Gene knockdown (i) or activation (a) | Transcriptional manipulation without DNA alteration |
| Perturb-seq Platforms | Combined CRISPR perturbation with single-cell RNA-seq | High-resolution mapping of transcriptional responses |
| Fluorescent Reporters | Live monitoring of protein abundance/localization | Time-course tracking of network dynamics |
| Small Molecule Inhibitors | Targeted protein inhibition | Acute perturbation of signaling networks |
| Antibody-based Detection | Protein quantification via immunoassays | Measuring phospho-signaling responses |
The computational toolkit for perturbation network analysis has expanded significantly, with several specialized resources now available. CausalBench provides an open-source benchmark suite for evaluating network inference methods on real-world interventional single-cell data [88] [89]. DYNAMO offers a collection of topology-based models for predicting perturbation propagation without kinetic parameters [9]. NetworkX serves as a fundamental Python library for network creation, manipulation, and analysis [92], while DL-MRA implementations enable network inference from perturbation time courses [10].
For constructing and benchmarking perturbative maps, the EFAIR pipeline (Embedding, Filtering, Aligning, Aggregating, Relating) provides a standardized framework for processing perturbation data across different modalities and experimental designs [85]. This systematic approach enables meaningful comparison of perturbation effects across diverse experimental conditions and measurement technologies.
Figure 2: EFAIR Pipeline for Constructing Perturbative Maps from High-Throughput Data
Implications for Drug Discovery and Development
The systematic comparison of perturbation techniques across network types has profound implications for drug discovery and development. Approaches that successfully predict perturbation patterns from network topology offer exciting opportunities to prioritize drug targets and understand mechanism of action without extensive kinetic parameter measurement. The demonstrated ability of topological models to achieve 65-80% accuracy in predicting true perturbation patterns suggests that increasingly complete maps of human interactome can significantly accelerate target validation and lead compound identification [9].
Furthermore, benchmarking frameworks like CausalBench enable more rigorous evaluation of computational methods for predicting drug effects, potentially reducing late-stage attrition in drug development. The finding that simpler models with biological prior knowledge sometimes outperform complex foundation models highlights the continued importance of incorporating domain expertise into computational approaches [90]. As perturbation technologies continue to scale and improve, the systematic comparison of perturbation analysis methods will play an increasingly vital role in translating network biology insights into therapeutic advances.
Network robustness represents a critical property of complex systems, defined as the ability of a network to maintain its structural integrity and core functions when subjected to failures or attacks [93]. In the context of biological and pharmacological research, this concept extends to understanding how perturbations—whether from genetic modifications, chemical treatments, or environmental changes—propagate through interconnected systems and ultimately affect cellular functions and disease outcomes. The systematic evaluation of robustness across different network topologies provides researchers with a powerful framework for predicting how biological systems respond to interventions, thereby accelerating therapeutic discovery and validation.
The fundamental challenge in robustness testing lies in the diverse nature of topological structures that underlie biological networks. From scale-free configurations prevalent in protein-protein interactions to small-world patterns in neural connectivity, each topology exhibits distinct robustness characteristics that determine how sensitive the system is to various perturbation types. Research has demonstrated that scale-free networks display remarkable resilience to random failures yet exhibit pronounced vulnerability to targeted attacks on highly connected hubs [94] [93]. Understanding these topological sensitivities is paramount for drug development professionals seeking to identify critical intervention points while anticipating potential side effects and compensatory mechanisms within biological systems.
Theoretical Foundations of Topological Robustness
Key Network Topologies in Biological Systems
Biological networks manifest in several distinct topological patterns, each with characteristic robustness profiles. The star topology features a central hub connected to multiple peripheral nodes, creating a structure highly vulnerable to hub failure but resilient to peripheral disruptions [95]. This configuration appears in various biological contexts where master regulators control subordinate elements. In contrast, tree topologies establish hierarchical relationships with parent-child node connections, offering scalable organization but presenting single points of failure at branching points [95]. Such structures frequently emerge in transcriptional regulatory networks and metabolic pathways.
Mesh topologies provide extensive redundancy through multiple interconnected paths, creating robust networks capable of maintaining functionality despite multiple node failures [95]. This architecture appears in protein interaction networks with abundant cross-talk and alternative signaling routes. Scale-free networks, characterized by a power-law degree distribution where few nodes possess many connections while most nodes have few, demonstrate exceptional resilience to random failures but critical vulnerability to targeted hub attacks [93]. This topology predominates in metabolic networks and food webs. Finally, small-world networks combine high clustering with short path lengths, facilitating rapid signal propagation while maintaining modular organization [93]. This structure underlies many neural and social interaction networks.
Quantitative Metrics for Robustness Assessment
Robustness evaluation employs diverse mathematical metrics that capture different aspects of network resilience. The effective graph resistance (RG) combines information from all paths in a network through the analogy of electrical circuits, where lower values indicate greater robustness [96]. This metric decreases when links are added and increases when links are removed, providing a sensitive measure of structural resilience. Flow capacity robustness assesses a network's ability to maintain throughput under attack by measuring maximum flow retention as nodes or edges are removed [93]. This approach is particularly relevant for biological systems where maintaining signal flux is essential.
Algebraic connectivity (the second smallest eigenvalue of the Laplacian matrix) quantifies how well-connected a network remains after damage, with higher values indicating stronger connectivity [97]. Percolation threshold identifies the critical fraction of nodes or edges whose removal disconnects the network, providing a clear breakpoint for system collapse [93]. The R*-value framework integrates multiple robustness metrics through principal component analysis (PCA), creating a unified robustness surface that enables visual assessment of network performance across different failure scenarios [97].
Table 1: Key Metrics for Network Robustness Evaluation
| Metric | Definition | Interpretation | Best Use Cases |
|---|---|---|---|
| Effective Graph Resistance (RG) | Based on electrical circuit analogy summing inverse eigenvalues of Laplacian matrix | Lower values indicate greater robustness; sensitive to edge additions/removals | General topological robustness assessment |
| Flow Capacity Robustness | Measures retention of maximum flow through network after attacks | Higher values indicate better maintenance of throughput | Signal transduction, metabolic flux networks |
| Algebraic Connectivity | Second smallest eigenvalue of the Laplacian matrix | Higher values indicate stronger connectivity; zero when network disconnected | Community structure, network cohesion |
| LCC Size | Size of largest connected component after perturbation | Larger values indicate better connectivity preservation | Targeted attack scenarios, fragmentation analysis |
| R*-Value | PCA-integrated multiple metrics normalized to initial robustness | Values <1 indicate performance degradation; enables cross-network comparison | Unified assessment across multiple failure scenarios |
Experimental Frameworks for Robustness Testing
Robustness Testing Methodologies
Robustness testing employs systematic methodologies to evaluate network responses to topological perturbations. The failure simulation approach subjects networks to progressive removal of nodes or edges according to specific strategies, monitoring performance degradation through selected metrics [97] [93]. Random failure simulations remove elements randomly, modeling accidental disruptions or non-specific interventions. Targeted attacks deliberately remove highest-impact elements—typically those with maximal degree, betweenness centrality, or other importance measures—simulating focused interventions or coordinated biological attacks [94]. Adaptive strategies recalculate node importance after each removal, mimicking intelligent adversaries or dynamic compensatory mechanisms.
The topological perturbation method quantifies how localized changes propagate through network structures, using distance-based models or linear response approximations to predict influence patterns [9]. This approach is particularly valuable in biological contexts where complete kinetic parameters are unavailable. The DYNAMO framework (DYNamics-Agnostic Network MOdels) implements this strategy through an "onion-peeling" approach that successively removes dynamical information while retaining topological features, enabling researchers to determine how much predictive accuracy derives from topology alone [9]. Experimental validation demonstrates that topological information alone captures 65-80% of perturbation patterns observed in full biochemical models.
Robustness surface generation creates comprehensive visualizations of network performance across multiple failure percentages and configurations [97]. This methodology applies principal component analysis to combine multiple robustness metrics, generating a unified surface that enables direct comparison of different networks under varying attack scenarios. The resulting surfaces reveal characteristic robustness signatures for different topological classes, facilitating rapid assessment of network vulnerability profiles.
Protocol: Robustness Testing for Biological Networks
Network Reconstruction: Compile network structure from protein-protein interaction databases (BioGRID, STRING), pathway databases (KEGG, Reactome), or gene co-expression networks. For drug perturbation studies, integrate drug-target interactions from DrugBank or ChEMBL.
Topological Characterization: Calculate basic network properties including degree distribution, average path length, clustering coefficient, and betweenness centrality. Classify network topology as scale-free, small-world, or random.
Metric Selection: Choose appropriate robustness metrics based on research objectives. For connectivity-focused studies, employ effective graph resistance and algebraic connectivity. For flow-based systems, utilize flow capacity robustness.
Perturbation Design: Define perturbation strategy including failure type (node/edge removal), attack strategy (random/targeted/adaptive), and perturbation scale (1-70% of elements).
Simulation Implementation: Execute robustness tests using network analysis tools (Cytoscape, NetworkX, igraph) or custom scripts. For each perturbation level, perform multiple iterations (100-500 runs) to account for stochastic variations.
Robustness Quantification: Compute selected metrics at each perturbation level. For R*-value approaches, perform PCA on metric combinations and compute robustness surfaces.
Validation: Compare topological predictions with experimental data where available. For biological networks, validate against gene expression changes from perturbation experiments or known drug effects.
Visualization of the robustness testing workflow for biological networks
Comparative Analysis of Topological Robustness
Performance Across Network Topologies
Empirical robustness testing reveals consistent performance patterns across different network topologies. Scale-free networks exhibit exceptional resilience to random failures, with connectivity maintained until approximately 80% of randomly selected nodes are removed [93]. However, these networks demonstrate critical vulnerability to targeted attacks, with complete disintegration occurring after removal of just 5-10% of highest-degree nodes. This asymmetric robustness profile has profound implications for drug targeting strategies in biological systems exhibiting scale-free architecture.
Small-world networks display moderate robustness to both random and targeted attacks due to their combination of local clustering and global connectivity [93]. The presence of shortcut edges between clusters provides alternative pathways when key nodes are compromised, creating a resilient architecture particularly well-suited for biological systems requiring stable yet adaptable functionality. Robustness in small-world networks increases with higher average degree, as additional connections further enhance pathway redundancy.
Random networks (Erdős-Rényi model) demonstrate consistent robustness across failure types, with gradual performance degradation as node removal increases [93]. Unlike scale-free networks, random topologies lack critical hubs whose removal triggers catastrophic failure. However, they require higher connection density to achieve robustness levels comparable to structured topologies, making them less efficient in biological contexts where connection establishment carries metabolic or spatial costs.
Mesh networks provide maximal robustness through extensive pathway redundancy, maintaining functionality even after multiple node failures [95]. This robustness advantage comes at the cost of implementation complexity, as the number of connections grows quadratically with network size. In biological systems, this architecture appears in critical functions where failure cannot be tolerated, such as core metabolic processes or essential signaling pathways.
Table 2: Comparative Robustness of Network Topologies
| Topology | Random Failure Resilience | Targeted Attack Resilience | Biological Examples | Robustness Optimization Strategies |
|---|---|---|---|---|
| Scale-Free | Very High (80% node removal) | Very Low (5-10% hub removal) | Protein interactions, Metabolic networks | Protect high-degree hubs, Add connections between low-degree nodes |
| Small-World | Moderate (40-60% removal) | Moderate (15-25% removal) | Neural networks, Social interactions | Increase average degree, Add strategic shortcuts between clusters |
| Random | Moderate (30-50% removal) | Moderate (20-30% removal) | Ecological networks, Genetic interactions | Increase connection density, Optimize degree distribution |
| Mesh | Very High (70-90% removal) | High (30-50% removal) | Signaling pathways, Backup systems | Enhance existing redundancy, Add cross-connections between modules |
| Star | Low (Hub failure critical) | Very Low (Single point failure) | Master regulator systems, Hub-and-spoke organizations | Add backup hubs, Create secondary coordination mechanisms |
Robustness Enhancement Strategies
Network robustness can be systematically improved through strategic topological interventions. Link addition strategies focus on identifying optimal connections whose establishment maximally decreases effective graph resistance [96]. Genetic algorithms efficiently identify these critical connections by exploring the combinatorial space of possible edges, with optimal additions typically creating shortcuts between previously distant network regions. Link protection approaches prioritize safeguarding existing connections whose removal would cause maximal disruption [96]. These strategies are particularly valuable in resource-constrained environments where comprehensive protection is infeasible.
Robustness surface analysis enables comparative assessment of enhancement strategies across multiple failure scenarios [97]. This multidimensional evaluation reveals that optimal robustness strategies vary significantly depending on the anticipated threat profile—random failures versus targeted attacks—highlighting the importance of context-specific robustness optimization. For biological networks, this translates to designing interventions tailored to specific vulnerability profiles, whether protecting against random mutations or targeted pathogen attacks.
Applications in Drug Discovery and Development
Predicting Drug Efficacy Through Topological Perturbation
Network robustness principles directly inform drug discovery by predicting how pharmaceutical interventions propagate through biological systems. The PathPertDrug framework quantifies functional antagonism between drug-induced and disease-associated pathway perturbations, systematically identifying drug candidates that topologically reverse disease signatures [98]. This approach integrates drug-induced gene expression profiles, disease transcriptomes, and pathway interaction networks to quantify activation/inhibition states, achieving superior predictive accuracy (AUROC 0.62 vs 0.42-0.53 for alternative methods) across multiple cancer types.
Perturbation pattern analysis demonstrates that network topology alone predicts 65-80% of biochemical perturbation outcomes, bypassing the need for expensive kinetic parameter measurement [9]. This topological predictability enables rapid in silico screening of compound libraries against disease networks, significantly accelerating target identification. Validation studies confirm that topological models accurately predict gene expression and phenotype changes in knockout and overproduction experiments with approximately 80% accuracy, establishing topology as a powerful predictor of biological outcomes.
PRnet, a perturbation-conditioned deep generative model, exemplifies the application of robustness principles to drug discovery by predicting transcriptional responses to novel chemical perturbations [99]. This approach encodes chemical structures as molecular fingerprints and maps their effects onto biological networks, enabling prediction of perturbation responses for compounds never experimentally tested. Experimental validation demonstrates accurate prediction of novel bioactive compounds against small cell lung cancer and colorectal cancer, with efficacy confirmed at appropriate concentration ranges.
Network Medicine and Drug Repurposing
Robustness testing enables systematic drug repurposing by identifying existing compounds that topologically reverse disease-associated perturbations. The multiscale topological differentiation (MTD) framework applies persistent Laplacians to identify structurally central genes within protein-protein interaction networks derived from differentially expressed genes [100]. This approach captures high-dimensional network architecture often overlooked by conventional connectivity analysis, yielding more reliable therapeutic targets for complex diseases like opioid addiction.
Functional reversal scoring quantifies the degree to which drug-induced pathway perturbations antagonize disease-associated dysregulation, creating a robust prioritization metric for repurposing candidates [98]. This method successfully identified 83% of literature-supported cancer drugs in validation studies, including fulvestrant for colorectal cancer, while predicting novel therapeutic associations such as rifabutin for lung cancer. The approach demonstrates particular value under class imbalance conditions, achieving 3-23% AUPR improvement over alternative methods.
Network robustness framework for drug repurposing
Essential Research Reagent Solutions
Table 3: Key Research Tools for Network Robustness Testing
| Research Tool | Function | Application Context | Key Features |
|---|---|---|---|
| Network Analysis Platforms (Cytoscape, NetworkX, igraph) | Network reconstruction, visualization, and metric calculation | General topological analysis | Plugin architectures, extensive metric libraries, scripting capabilities |
| Pathway Databases (KEGG, Reactome, WikiPathways) | Source of biologically validated network structures | Biological network construction | Curated pathways, molecular interactions, functional annotations |
| Interaction Databases (STRING, BioGRID, DrugBank) | Protein-protein, genetic, and drug-target interactions | Network edge definition | Confidence scores, experimental evidence, comprehensive coverage |
| Perturbation Data Resources (CMap, LINCS L1000) | Drug-induced gene expression profiles | Perturbation pattern analysis | Standardized protocols, multiple cell lines, dose-response data |
| Robustness Simulation Tools (Custom R/Python scripts) | Implement failure scenarios and calculate robustness metrics | Experimental robustness testing | Flexible attack simulation, metric customization, batch processing |
| Persistent Laplacian Algorithms | Multiscale topological analysis | Identification of structurally critical nodes | High-dimensional topology capture, scale-independent features |
Robustness testing provides a powerful methodological framework for evaluating sensitivity to topological variations across biological and pharmacological networks. The comparative analysis presented in this guide demonstrates that network topology fundamentally determines perturbation response patterns, with scale-free networks showing asymmetric robustness, small-world networks offering balanced resilience, and mesh topologies providing maximum redundancy at the cost of complexity. These topological principles directly inform drug discovery strategies, enabling prediction of intervention efficacy and identification of repurposing candidates through functional reversal scoring.
The experimental protocols and metrics detailed herein establish standardized approaches for robustness assessment across diverse network types. As network medicine continues to evolve, robustness testing will play an increasingly critical role in translating topological insights into therapeutic strategies, ultimately enabling more predictive, efficient, and effective drug development pipelines. The integration of deep learning approaches with topological perturbation models, as exemplified by PRnet and PathPertDrug, represents the cutting edge of this rapidly advancing field, offering unprecedented capability to anticipate biological responses to novel chemical perturbations.
In the domain of explainable artificial intelligence (XAI), feature attribution methods are essential tools that illuminate the decision-making processes of complex "black box" models, such as deep neural networks. These methods identify and highlight the input features—whether pixels in an image, words in text, or biological markers in data—that most significantly influence a model's prediction. Faithfulness estimation has emerged as the critical paradigm for evaluating whether these explanatory methods accurately reflect the true reasoning of the underlying model they seek to explain. The core principle of faithfulness is that altering or removing features identified as important should correspondingly produce a meaningful change in the model's output prediction [101].
The urgency for robust faithfulness estimation is particularly acute in scientific and medical domains, such as drug development, where model decisions carry significant consequences. Here, the objective extends beyond mere technical validation; it encompasses the broader framework of Verification, Validation, and Uncertainty Quantification (VVUQ). This framework is essential for building trust in computational tools, ensuring they are not only mathematically sound but also reliably applicable to real-world, risk-critical scenarios like clinical decision-making [102]. Furthermore, research into network topologies reveals that a system's structure—be it a biological gene regulatory network or an artificial neural network—fundamentally shapes its response to perturbations [71] [6]. Therefore, validating feature attribution methods requires a holistic approach that considers both the fidelity of the explanation to the model and the stability of that explanation within the context of the system's inherent architecture and uncertainties.
Core Metrics for Evaluating Faithfulness
Evaluating feature attribution methods poses significant challenges, primarily due to the absence of a definitive "ground truth" for what constitutes a correct explanation. To address this, researchers have developed several quantitative metrics centered on the concept of faithfulness, which assesses how faithfully an attribution map reflects the model's internal reasoning [101].
Foundational Principles: Soundness and Completeness
Moving beyond monolithic faithfulness scores, a more nuanced approach proposes evaluating attributions through two complementary perspectives: soundness and completeness [101].
- Soundness measures the precision of an attribution method. It answers the question: "Are the features highlighted by the attribution method truly predictive for the model?" A method with high soundness will avoid highlighting irrelevant features, thereby minimizing false positive explanations. It can be evaluated by testing model performance when only the attributed features are used.
- Completeness measures the recall of an attribution method. It answers the question: "Does the attribution method capture all the features that are important to the model's prediction?" A method with high completeness ensures that no critical feature is omitted, which is vital in high-stakes fields like healthcare where missing a key biomarker could have dire consequences [101].
This dual-lens framework provides a more holistic and reliable assessment than a single faithfulness metric, helping practitioners select the most suitable explanation method for their specific application, whether it prioritizes avoiding false positives (soundness) or false negatives (completeness).
Robust Faithfulness and Stability Metrics
In real-world environments, models and their explanations face noise and potential adversarial attacks. Consequently, evaluating the stability of attributions is as crucial as assessing their initial faithfulness. The MeTFA (Median Test for Feature Attribution) framework has been proposed to quantify this uncertainty and robustness [103].
MeTFA provides two key functions:
- Significance Testing: It examines whether a feature is statistically important or unimportant, generating a "MeTFA-significant map" that filters out spurious attributions.
- Confidence Intervals: It computes confidence intervals for attribution scores, producing a "MeTFA-smoothed map" that increases the stability and reliability of the explanation [103].
These robust faithfulness metrics ensure that explanations remain consistent and trustworthy even when the input data is subject to natural variation or malicious manipulation.
Table 1: Summary of Core Faithfulness Metrics
| Metric | Primary Question | Evaluation Method | Importance in High-Stakes Fields |
|---|---|---|---|
| Soundness | Are the attributed features truly predictive? | Measure model performance degradation when only attributed features are used. | Prevents false confidence based on irrelevant features. |
| Completeness | Are all predictive features included? | Measure model performance when attributed features are removed/perturbed. | Ensures no critical factors are overlooked in a diagnosis or treatment plan. |
| Robustness (via MeTFA) | Is the explanation stable under noise? | Compute confidence intervals and statistical significance for attribution scores. | Builds trust that explanations will not change drastically due to small, insignificant input variations. |
Benchmarking Methodologies and Experimental Protocols
Establishing rigorous, standardized benchmarks is fundamental for the objective comparison of feature attribution methods. A well-designed benchmark allows researchers to impartially assess the performance of different algorithms against a common standard.
The BAM Framework
The BAM (Benchmarking Attribution Methods) framework addresses the ground truth challenge by employing a synthetic dataset where the "relative feature importance" is known a priori [104]. In this controlled setup, models are trained on data where the importance of specific features is predefined by the experimenters. This knowledge allows for the quantitative evaluation of attribution methods by comparing their output against this established baseline. The BAM framework utilizes three complementary metrics to perform this comparison across different models and inputs, helping to identify methods that are more likely to produce false positive explanations—those that incorrectly identify features as important [104].
Experimental Protocol for Evaluating Soundness and Completeness
For a hands-on evaluation, the following protocol, derived from research on soundness and completeness, can be implemented [101]:
- Model and Data Setup: Train a model on a dataset where some control over feature importance is possible. Synthetic datasets are ideal, but carefully designed real-world datasets can also be used.
- Generate Attributions: Apply the feature attribution method(s) under evaluation to the model's predictions on a test set.
- Soundness Evaluation:
- For a given input and its attribution map, create a new version of the input that retains only the features highlighted by the attribution method.
- Feed this modified input into the model and observe the change in the output prediction.
- A sharp drop in prediction confidence for the target class indicates low soundness, as the features deemed important were not, in fact, sustaining the prediction.
- Completeness Evaluation:
- Conversely, create a modified input where the features highlighted in the attribution map are removed or sufficiently perturbed.
- If the model's prediction remains largely unchanged, this indicates low completeness, suggesting that the attribution method missed features that the model actually relies on.
- Quantification: Repeat steps 3 and 4 across a large dataset and aggregate the results to compute quantitative scores for soundness and completeness.
Comparative Analysis of Feature Attribution Methods
A wide array of feature attribution methods exists, each with distinct underlying mechanics, strengths, and weaknesses. The following section provides a comparative guide, categorizing major families of algorithms and summarizing their performance characteristics relevant to faithfulness estimation.
Gradient-Based Methods: These techniques leverage the model's gradients to determine feature importance.
- Saliency Maps: Compute the gradient of the output with respect to the input. While simple and efficient, they are often noisy and suffer from gradient saturation [105].
- Integrated Gradients (IG): Address saturation by integrating gradients along a path from a baseline to the input. This method provides axiomatic guarantees like completeness but is computationally more intensive [105].
- Gradient SHAP: A gradient-based approximation of Shapley values from game theory. It is theoretically grounded but can be computationally expensive and may assume feature independence [105].
Activation-Based Methods: These methods analyze the internal activations of the model.
- Grad-CAM: Uses gradients from the final convolutional layer to produce a coarse localization heatmap. It is less noisy than input gradients but can miss fine-grained details [105].
- Layer-wise Relevance Propagation (LRP): Propagates relevance scores from the output back to the input in a backward pass. It can provide fine-grained explanations but is complex and its results depend heavily on the chosen propagation rules [105].
Attention-Based Methods: For models equipped with attention mechanisms, the attention weights themselves can be used as a form of explanation.
- Self-Attention Visualization: Visualizes the attention weights in Transformer models to show which tokens (e.g., words or image patches) the model attends to. While highly intuitive, research indicates that attention weights are not always faithful to the model's true reasoning process [105].
Faithfulness Performance Comparison
When evaluated under the soundness and completeness framework, different attribution methods reveal distinct performance profiles. No single method universally outperforms all others in both dimensions; instead, each demonstrates a characteristic trade-off [101].
Table 2: Comparative Analysis of Major Feature Attribution Methods
| Method | Category | Key Principle | Theoretical Guarantees | Strengths | Weaknesses |
|---|---|---|---|---|---|
| Saliency Maps [105] | Gradient | Gradient of output w.r.t. input. | None | Simple, efficient, model-agnostic. | Noisy; prone to gradient saturation. |
| Integrated Gradients [105] | Gradient | Path-integrated gradients from baseline. | Completeness, Sensitivity. | Avoids saturation; theoretically robust. | Computationally expensive; baseline choice sensitive. |
| Grad-CAM [105] | Activation | Weighted combination of activation maps. | None | Less noisy; intuitive visualizations. | Lower resolution; model-specific (CNNs). |
| Layer-wise Relevance Propagation (LRP) [105] | Activation | Backward propagation of relevance scores. | Conservation of Relevance. | Fine-grained; no gradient computation. | Complex; rule-dependent results. |
| Gradient SHAP [105] | Gradient / Game Theory | Approximates Shapley values via gradients. | Shapley axioms (approximated). | Theoretically fair; model-agnostic. | Very computationally intensive. |
| Attention Visualization [105] | Attention | Uses model's internal attention weights. | None | Very efficient and intuitive. | Potentially unfaithful to model decision. |
For researchers and professionals in drug development and computational biology aiming to implement these validation protocols, the following table outlines key conceptual "reagents" and resources essential for conducting rigorous faithfulness estimation.
Table 3: Essential Research Reagents for Faithfulness Experimentation
| Tool / Resource | Type | Primary Function | Relevance to Faithfulness Estimation |
|---|---|---|---|
| Synthetic Datasets (e.g., BAM) [104] | Data | Provides ground truth for feature importance. | Enables controlled benchmarking by allowing comparison against known important features. |
| Soundness & Completeness Metrics [101] | Metric | Quantifies two key aspects of faithfulness. | Provides a dual-perspective framework for a more nuanced evaluation than a single score. |
| MeTFA Framework [103] | Software/Metric | Quantifies uncertainty and robustness of attributions. | Evaluates explanation stability under noise and generates statistically significant attribution maps. |
| Benchmarked Model Zoo | Software/Model | A collection of pre-trained models with standard architectures. | Allows for standardized testing and comparison of attribution methods across different model topologies. |
| Perturbation Engine | Software/Method | A tool for systematically perturbing input features. | Core to the experimental protocol for measuring soundness and completeness via feature removal/retention. |
The rigorous estimation of faithfulness is a cornerstone for the responsible deployment of AI in scientific and clinical settings. As this guide has outlined, moving beyond single-metric evaluations to a multi-faceted approach—encompassing soundness, completeness, and robustness—is critical for obtaining a true measure of an explanation's reliability. The interplay between network topology and perturbation response, a theme in systems biology [6] and power grid research [71], underscores that future validation frameworks must be context-aware, accounting for the specific architecture and dynamics of the model being explained.
The future of faithfulness estimation will likely involve greater standardization of benchmarks like BAM [104] and the integration of rigorous VVUQ processes [102] from the digital twin paradigm into the XAI lifecycle. This is particularly vital for precision medicine, where digital twins of patient physiology could leverage faithful explanations to simulate interventions and optimize therapeutic strategies. By adopting the comprehensive validation methodologies described herein, researchers and drug development professionals can build more transparent, trustworthy, and ultimately, more effective AI systems for advancing human health.
Benchmarking Performance Against Biological Ground Truths
The fundamental challenge in gene regulatory network (GRN) inference is the absence of a perfectly known "ground truth" against which to validate computational predictions. In biological systems, the true causal architecture of molecular interactions is never fully known, creating significant obstacles for evaluating the performance of network reconstruction algorithms. This challenge has become increasingly pressing with the advent of large-scale perturbation technologies like single-cell CRISPR screens, which generate unprecedented volumes of data on how genetic perturbations affect gene expression patterns across thousands of genes and cell types. Benchmarking in this domain requires sophisticated frameworks that can approximate biological reality while accounting for the complex topology, dynamics, and context-specificity of genuine cellular networks.
Traditional evaluations relying on synthetic networks with randomly generated structures often fail to predict real-world performance, as they cannot capture the intricate organizational principles of biological systems. Recent research has revealed a troubling disparity: methods that perform excellently on synthetic benchmarks frequently show poor generalization to experimental biological data. This discrepancy underscores the critical need for benchmarking frameworks that incorporate realistic network properties and utilize empirical perturbation data to establish more meaningful performance standards. The development of such frameworks represents an essential step toward reliable computational models that can genuinely advance drug discovery and our understanding of disease mechanisms.
Establishing Biological Ground Truth
The Challenge of Biological Validation
Unlike many computational domains where ground truth can be definitively established, biological networks present unique validation challenges due to their incomplete characterization, context-dependent behavior, and technical limitations of experimental measurements. Even gold-standard experimental approaches like chromatin immunoprecipitation (ChIP) assays or perturbation studies provide only partial insights into network topology, capturing specific interactions under particular conditions rather than comprehensive architectures. This fundamental limitation has necessitated the development of creative benchmarking strategies that leverage consensus knowledge, silver standards, and functional validation to approximate ground truth for evaluation purposes.
The field has gradually shifted from purely synthetic benchmarks toward frameworks that incorporate curated biological networks and large-scale perturbation data. These approaches recognize that biological networks exhibit distinctive structural properties—including sparsity, hierarchical organization, modularity, and specific degree distributions—that significantly impact inference performance. By embedding these properties into evaluation frameworks, researchers can create more meaningful tests that better predict real-world applicability. The most advanced benchmarks now utilize massive perturbation datasets that provide direct causal evidence for regulatory relationships, offering a substantial improvement over earlier approaches that relied solely on observational data or synthetic networks.
Structural Properties of Biological Networks
Gene regulatory networks exhibit consistent topological properties that inform benchmarking design. Key properties include:
- Sparsity: Most genes are regulated by a small number of transcription factors, with only 41% of transcript-targeting perturbations showing significant effects on other genes [2].
- Directionality and Feedback: Regulatory relationships are inherently directional, with feedback loops being common (2.4% of interacting gene pairs show bidirectional effects) [2].
- Hierarchical Organization: Networks display clear hierarchical structures with master regulators and downstream targets.
- Modularity: Functionally related genes often cluster into modules with dense internal connections.
- Degree Distribution: Following approximate power-law distributions where few genes regulate many targets while most genes regulate few [2].
These properties are not merely structural features but actively shape how perturbations propagate through networks. Benchmarking frameworks must therefore incorporate these characteristics to generate meaningful evaluations of method performance.
Benchmarking Frameworks and Metrics
The CausalBench Framework
CausalBench represents a significant advancement in benchmarking for network inference, specifically designed to address the limitations of synthetic evaluations. This framework utilizes two large-scale perturbation datasets from human cell lines (K562 and RPE1) containing over 200,000 interventional data points from CRISPRi perturbations [106]. Unlike synthetic benchmarks, CausalBench employs biologically-motivated evaluation strategies that do not assume perfect knowledge of the true network, instead using statistical measures and functional consistency to assess performance.
The framework incorporates two complementary evaluation approaches:
- Biology-driven approximation: Uses curated biological knowledge to establish partial ground truth for evaluation.
- Quantitative statistical evaluation: Employs causal effect estimation between control and treated cells to assess prediction quality.
CausalBench implements several key metrics designed to capture different aspects of inference performance:
- Mean Wasserstein Distance: Measures how well predicted interactions correspond to strong causal effects.
- False Omission Rate (FOR): Quantifies the rate at which true causal interactions are missed by the model.
- Biological F1 Score: Assesses agreement with biologically validated interactions.
These metrics reflect the inherent trade-off between precision and recall in network inference, where methods must balance comprehensive coverage against accurate prediction.
Network Comparison Methodologies
Quantifying similarity between predicted and reference networks requires specialized methodologies that account for both local and global topological properties. Multiple approaches have been developed for this purpose, falling into two broad categories:
Known Node-Correspondence (KNC) Methods assume the same nodes exist in both networks and focus on edge similarity. These include:
- DeltaCon: Compares node similarity matrices derived from the networks, considering all paths between nodes rather than just direct edges [87].
- Adjacency Matrix Differences: Simple direct comparison of adjacency matrices using norms like Euclidean, Manhattan, or Canberra distances [87].
Unknown Node-Correspondence (UNC) Methods compare global structural properties without assuming node identity alignment. These include:
- Portrait Divergence: Compares network feature distributions.
- NetLSD: Creates spectral signatures that capture network-scale features.
- Graphlet-based Methods: Compare small subgraph distributions.
For biological network benchmarking, KNC methods are typically more relevant since gene identities are preserved between predicted and reference networks. However, each method offers different insights into the nature of the similarity between networks.
Performance Comparison of Network Inference Methods
Experimental Protocol
The performance data presented in this section derives from a comprehensive evaluation using the CausalBench framework [106]. The benchmarking protocol involved:
Datasets:
- K562 cell line: 5,530 gene transcripts measured in 1,989,578 cells with 11,258 CRISPR-based perturbations targeting 9,866 unique genes.
- RPE1 cell line: Comparable scale perturbation dataset.
Evaluation Methodology:
- All methods trained on full datasets with five different random seeds.
- Performance assessed using both statistical metrics (Mean Wasserstein Distance, FOR) and biological evaluation (F1 score against biological ground truth).
- Methods categorized as observational (using only unperturbed data) or interventional (using perturbation data).
Implementation Details:
- Standardized preprocessing and gene selection across all methods.
- Computational resources allocated equally across methods.
- Evaluation metrics computed using consistent implementations.
This rigorous protocol ensures fair comparison across diverse methodological approaches and provides insights into real-world performance characteristics.
Table 1: Performance Comparison of Network Inference Methods on Statistical Metrics
| Method | Type | Mean Wasserstein Distance | False Omission Rate | Performance Ranking |
|---|---|---|---|---|
| Mean Difference | Interventional | High | Low | 1 |
| Guanlab | Interventional | High | Medium | 2 |
| SparseRC | Interventional | High | Medium | 3 |
| Betterboost | Interventional | Medium | Medium | 4 |
| GRNBoost | Observational | Low | High | 5 |
| NOTEARS variants | Observational | Low | High | 6 |
| PC | Observational | Low | High | 7 |
| GES/GIES | Observational/Interventional | Low | High | 8 |
| DCDI variants | Interventional | Low | High | 9 |
Table 2: Biological Evaluation Performance (F1 Scores)
| Method | K562 Dataset | RPE1 Dataset | Overall Ranking |
|---|---|---|---|
| Guanlab | 0.42 | 0.39 | 1 |
| Mean Difference | 0.38 | 0.37 | 2 |
| GRNBoost | 0.35 | 0.33 | 3 |
| Betterboost | 0.31 | 0.29 | 4 |
| SparseRC | 0.28 | 0.27 | 5 |
| NOTEARS | 0.21 | 0.19 | 6 |
| GES/GIES | 0.18 | 0.17 | 7 |
| PC | 0.15 | 0.14 | 8 |
| DCDI | 0.12 | 0.11 | 9 |
The performance comparison reveals several key insights. First, methods specifically designed for interventional data generally outperform those adapted from observational frameworks, with Mean Difference and Guanlab showing consistently strong performance across both statistical and biological evaluations. Second, the trade-off between precision and recall is evident across all methods, with some approaches (like GRNBoost) achieving higher recall but lower precision, while others show the opposite pattern.
Surprisingly, some interventional methods (particularly GIES and DCDI variants) failed to outperform their observational counterparts, contrary to theoretical expectations. This suggests that effectively leveraging perturbation data requires specialized algorithmic approaches beyond simple adaptation of existing methods. The best-performing methods shared characteristics including computational scalability, effective use of interventional information, and incorporation of biological priors.
Experimental Workflows and Protocols
Benchmarking Workflow
The following diagram illustrates the comprehensive benchmarking workflow used in contemporary network inference evaluation:
Diagram 1: Comprehensive Benchmarking Workflow for Network Inference Methods
This workflow ensures systematic evaluation across multiple methodological approaches and performance dimensions. The incorporation of both statistical and biological evaluation provides a more complete picture of real-world applicability than single-metric approaches.
Network Inference Process
The core process of network inference from perturbation data involves multiple transformation steps from raw data to biological insights:
Diagram 2: Network Inference Process from Perturbation Data
This process highlights the transformation of raw experimental data into biological knowledge through computational inference. Each stage introduces specific assumptions and limitations that ultimately affect benchmarking outcomes.
The Impact of Network Topology on Inference Performance
Topological Properties and Benchmarking Accuracy
Network topology significantly influences the performance of inference methods, with certain structural properties either facilitating or impeding accurate reconstruction. Research has demonstrated that simple distance-based models using only topological information can achieve approximately 65% accuracy in predicting perturbation patterns, increasing to 80% when key network properties are properly leveraged [9]. This remarkable performance highlights the fundamental importance of topology in determining network behavior.
The hierarchy inherent in biological networks creates asymmetries in inferability, with upstream regulators generally more difficult to identify than downstream targets. This occurs because perturbations propagate preferentially in the direction of hierarchical flow, creating stronger statistical signatures for downstream relationships. Additionally, network motifs such as feed-forward loops create distinctive perturbation signatures that can be exploited by specialized algorithms but may challenge general-purpose methods. Dense interconnectivity within modules improves internal inferability while potentially obscuring connections between modules due to complex interaction patterns.
Topology-Based Perturbation Prediction
The relationship between network topology and perturbation effects can be visualized as a process of influence propagation:
Diagram 3: Topology-Based Prediction of Perturbation Patterns
This diagram illustrates how perturbation effects propagate through network topology, with intensity generally decreasing with distance from the perturbation source while being modulated by specific topological features. This relationship forms the basis for topology-based prediction approaches that can achieve substantial accuracy without detailed kinetic parameters.
Essential Research Reagents and Computational Tools
Table 3: Essential Research Resources for Network Inference Benchmarking
| Resource Category | Specific Examples | Function in Benchmarking |
|---|---|---|
| Perturbation Datasets | K562 CRISPRi dataset, RPE1 dataset [106] | Provide experimental data with ground-truth perturbation effects |
| Reference Networks | Curated biological pathways, Prior knowledge networks | Establish partial ground truth for biological evaluation |
| Benchmarking Frameworks | CausalBench [106] | Standardized evaluation pipelines and metrics |
| Network Inference Methods | Mean Difference, Guanlab, GRNBoost, NOTEARS [106] | Algorithms for comparative performance assessment |
| Evaluation Metrics | Wasserstein distance, FOR, Biological F1 score [106] | Quantify different aspects of inference performance |
| Network Analysis Tools | DeltaCon, Portrait Divergence [87] [107] | Compare network topologies and assess statistical significance |
| Visualization Platforms | Cytoscape, Graph visualization tools | Interpret and communicate network inference results |
These resources collectively enable comprehensive benchmarking that spans from data processing through method evaluation to biological interpretation. The availability of standardized frameworks like CausalBench has significantly improved the rigor and reproducibility of performance comparisons in the field.
Benchmarking network inference methods against biological ground truths remains challenging but essential for advancing computational biology and drug discovery. The development of frameworks like CausalBench that utilize large-scale perturbation data represents significant progress toward more meaningful evaluation standards. Current evidence indicates that methods specifically designed for interventional data—particularly those with strong scalability and effective use of perturbation information—generally outperform approaches adapted from observational frameworks.
The surprising performance of topology-based prediction models, achieving 65-80% accuracy without kinetic parameters, suggests that network architecture itself encodes substantial information about perturbation effects. This insight highlights the importance of incorporating realistic topological properties into benchmarking frameworks and method development. As the field advances, future benchmarking efforts will need to address emerging challenges including multi-modal data integration, temporal network dynamics, and context-specific regulatory relationships.
For researchers and drug development professionals, selecting network inference methods should consider both benchmarking performance and specific application requirements. Methods like Mean Difference and Guanlab currently show strong overall performance, but optimal choice may depend on specific factors including dataset size, biological context, and analysis goals. As benchmarking frameworks continue to evolve, they will provide increasingly reliable guidance for method selection and development, ultimately accelerating the translation of network models into biological insights and therapeutic advances.
Conclusion
The validation of perturbation effects across network topologies represents a paradigm shift in biomedical research, integrating computational rigor with biological insight. By establishing robust mathematical frameworks, adaptable methodologies, troubleshooting protocols, and comprehensive validation standards, researchers can more reliably predict therapeutic outcomes and identify novel treatment strategies. Future directions should focus on developing standardized perturbation validation pipelines, integrating multi-omics data into unified network models, and creating clinical translation frameworks that bridge computational predictions with patient outcomes. As network medicine evolves, these validated perturbation approaches will become increasingly crucial for personalized medicine, drug repurposing, and understanding complex disease mechanisms at a systems level.
References
- 1. Perturbation Biology: Inferring Signaling Networks in Cellular ... [https://journals.plos.org/ploscompbiol/article?id=10.1371/journal.pcbi.1003290]
- 2. Gene regulatory network structure informs the distribution of ... [https://journals.plos.org/ploscompbiol/article?id=10.1371/journal.pcbi.1013387]
- 3. Deep-learning-based gene perturbation effect prediction ... [https://www.nature.com/articles/s41592-025-02772-6]
- 4. Combinatorial prediction of therapeutic perturbations using ... [https://www.nature.com/articles/s41551-025-01481-x]
- 5. [2410.03380] Identifying biological targets through... perturbation [https://arxiv.org/abs/2410.03380]
- 6. A computational approach for perturbation-induced EMT ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12615684/]
- 7. Towards perturbation prediction of biological using deep... networks [https://www.nature.com/articles/s41598-019-48391-y?error=cookies_not_supported&code=e32d6ad9-7b9b-465c-98e3-f35d20c76ce9]
- 8. Mapping the perturbome network of cellular perturbations - PMC [https://pmc.ncbi.nlm.nih.gov/articles/PMC6853941/]
- 9. Predicting perturbation patterns from the topology of biological ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC6142275/]
- 10. Network inference from perturbation time course data [https://www.nature.com/articles/s41540-022-00253-6]
- 11. The topology of synergy - Research journals - PLOS [https://journals.plos.org/ploscompbiol/article?id=10.1371/journal.pcbi.1013649]
- 12. Causal identification of single-cell experimental ... [https://www.nature.com/articles/s41592-023-02040-5]
- 13. Deep learning framework for predicting drug combination ... [https://www.sciencedirect.com/science/article/abs/pii/S1476927125003974]
- 14. Network topology and interaction logic determine states it ... [https://www.nature.com/articles/s41540-024-00423-8]
- 15. Quantifying the effect of experimental perturbations at single ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC8122059/]
- 16. Mapping the perturbome network of cellular perturbations [https://www.nature.com/articles/s41467-019-13058-9]
- 17. Benchmarking and optimizing Perturb-seq in differentiating ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC11785042/]
- 18. Gene interaction perturbation network deciphers a high ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC9643007/]
- 19. Centrality in modular networks | EPJ Data Science | Full Text [https://epjdatascience.springeropen.com/articles/10.1140/epjds/s13688-019-0195-7]
- 20. Network topological reorganization mechanisms of primary ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12540415/]
- 21. Network topological reorganization mechanisms of primary ... [https://www.frontiersin.org/journals/neuroscience/articles/10.3389/fnins.2025.1678035/full]
- 22. Topological Determinants of Perturbation Spreading in ... [https://arxiv.org/html/2403.05797v1]
- 23. Network-based in silico drug efficacy screening | Nature Communications [https://www.nature.com/articles/ncomms10331]
- 24. Targets of drugs are generally, and targets of drugs having side effects are specifically good spreaders of human interactome perturbations - PMC [https://pmc.ncbi.nlm.nih.gov/articles/PMC4426692/]
- 25. Identification of disease treatment mechanisms through the multiscale interactome - PMC [https://pmc.ncbi.nlm.nih.gov/articles/PMC7979814/]
- 26. Automated model refinement using perturbation- ... [https://www.nature.com/articles/s41540-025-00532-y]
- 27. Multiscale interactome analysis coupled with off-target drug predictions reveals drug repurposing candidates for human coronavirus disease - PMC [https://pmc.ncbi.nlm.nih.gov/articles/PMC8640055/]
- 28. Perturbation response scanning of drug-target networks [https://www.sciencedirect.com/science/article/pii/S2095177925001121]
- 29. Perturbation response scanning of drug-target networks [https://pubmed.ncbi.nlm.nih.gov/40678478/]
- 30. CAGI7 PRS [https://genomeinterpretation.org/cagi7-prs.html]
- 31. Single-cell polygenic risk scores dissect cellular and ... [https://www.nature.com/articles/s41587-025-02725-6]
- 32. Polygenic Risk Scores Developed by Allelica [https://www.allelica.com/prs/]
- 33. Gene regulatory network inference during cell fate ... [https://www.nature.com/articles/s41540-025-00504-2]
- 34. Comparing the intrinsic dynamics of multiple protein ... [https://www.sciencedirect.com/science/article/pii/S0304416514003237]
- 35. BioSpring: An elastic network framework for interactive ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12006919/]
- 36. Elastic network models capture the motions apparent within ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC4024634/]
- 37. Elastic network modeling of cellular networks unveils sensor ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC9216591/]
- 38. Systematic Multiscale Parameterization of Heterogeneous ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC2567941/]
- 39. Identification of disease comorbidity through hidden ... [https://www.nature.com/articles/srep39433]
- 40. Random walk with restart on multilayer networks: from node ... [https://bmcbioinformatics.biomedcentral.com/articles/10.1186/s12859-024-05683-z]
- 41. Perturbation response scanning of drug-target networks [https://pmc.ncbi.nlm.nih.gov/articles/PMC12268079/]
- 42. A Random Walk with Restart Model Based on Common ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC8674059/]
- 43. Systematic discovery of signaling pathways linking immune ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC8551081/]
- 44. LeMeDISCO is a computational method for large-scale ... [https://www.nature.com/articles/s42003-022-03816-9]
- 45. Mining comorbidities of opioid use disorder from FDA adverse ... [https://bmcmedinformdecismak.biomedcentral.com/articles/10.1186/s12911-022-01869-8]
- 46. Integrative multi-omic profiling in blood reveals distinct ... [https://www.frontiersin.org/journals/immunology/articles/10.3389/fimmu.2025.1667662/full]
- 47. - Feature for Graph Neural... :: SSRN Topology Cascade Perturbation [https://papers.ssrn.com/sol3/papers.cfm?abstract_id=5017384]
- 48. [2209.07754] On the Robustness of Graph Neural Diffusion to... [https://arxiv.org/abs/2209.07754]
- 49. GTAT-GRN: a graph topology-aware attention method with ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12540167/]
- 50. Minimizing Edge Changes in Graph Neural Networks - Simple Science [https://scisimple.com/en/articles/2025-09-01-minimizing-edge-changes-in-graph-neural-networks--aky64v0]
- 51. Unifying topological structure and self-attention mechanism ... [https://www.nature.com/articles/s41598-024-84816-z]
- 52. On the Topology Awareness and Generalization ... [https://arxiv.org/abs/2403.04482]
- 53. Are GNNs doomed by the topology of their input graph? [https://arxiv.org/html/2502.17739v1]
- 54. Drug Repurposing Using Biological Networks [https://www.mdpi.com/2227-9717/9/6/1057]
- 55. System and network biology-based computational ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC9300680/]
- 56. Drug Repurposing and Artificial Intelligence in Multiple ... [https://www.mdpi.com/2813-3064/3/3/28]
- 57. Network-based approach to prediction and population-based ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC6043492/]
- 58. Next-generation drug repurposing using human genetics ... [https://www.sciencedirect.com/science/article/pii/S1471489219301237]
- 59. Perturbation response scanning of drug-target networks [https://doaj.org/article/9ef246626fbc4f82b6d11a4062f16b88]
- 60. A comprehensive analysis of perturbation methods in ... [https://www.nature.com/articles/s41598-025-09538-2]
- 61. Topological perturbations on resilience of the world trade ... [https://www.nature.com/articles/s41599-024-03045-x]
- 62. Perturbation Theory: Techniques and Limitations [https://link.springer.com/chapter/10.1007/978-1-4899-1085-1_2]
- 63. Comparison of nonlinear dynamic methods and perturbation ... [https://pubmed.ncbi.nlm.nih.gov/16266175/]
- 64. Gene regulatory network structure informs the distribution of ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12419648/]
- 65. In silico biological discovery with large perturbation models [https://www.nature.com/articles/s43588-025-00870-1]
- 66. MORPH Predicts the Single-Cell Outcome of Genetic ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12236822/]
- 67. BioBO: Biology-informed Bayesian Optimization for ... [https://arxiv.org/html/2509.19988v1]
- 68. Towards a New Method for Perturbation Analysis ... [https://www.scitepress.org/PublishedPapers/2025/133842/]
- 69. Model: Bayesian Optimisation for Biology | Imperial - iGEM 2025 [https://2025.igem.wiki/imperial/Model]
- 70. TopoReformer: Mitigating Adversarial Attacks Using ... [https://arxiv.org/html/2511.15807v1]
- 71. How Network Topology Affects the Strength of Dangerous ... [https://arxiv.org/abs/2401.00552]
- 72. Topology-Aware Conformal Prediction for Stream Networks [https://arxiv.org/html/2503.04981v2]
- 73. Regression and alignment for functional data and network ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC11822954/]
- 74. Optimizing hybrid network topologies in ... [https://www.nature.com/articles/s41598-025-05631-8]
- 75. First-Passage Approach to Optimizing Perturbations for ... [https://arxiv.org/abs/2502.04121]
- 76. First-Passage Approach to Optimizing Perturbations for Improved ... [https://arxiv.org/html/2502.04121v3]
- 77. Towards perturbation prediction of biological networks ... [https://www.nature.com/articles/s41598-019-48391-y]
- 78. Bayesian Lookahead Perturbation Policy for Inference of ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC11474162/]
- 79. F-Fidelity: A Robust Framework for Faithfulness Evaluation ... [https://arxiv.org/html/2410.02970v2]
- 80. A Comprehensive Review of Explainable Artificial Intelligence ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12252469/]
- 81. Enhancing explainable AI with graph signal processing [https://www.sciencedirect.com/science/article/pii/S0043135425009303]
- 82. Explainable AI Methods - A Brief Overview [https://link.springer.com/chapter/10.1007/978-3-031-04083-2_2]
- 83. XSMILES: interactive visualization for molecules, SMILES and ... [https://jcheminf.biomedcentral.com/articles/10.1186/s13321-022-00673-w]
- 84. A comprehensive analysis of perturbation methods in ... [https://www.semanticscholar.org/paper/A-comprehensive-analysis-of-perturbation-methods-in-Simic-Veas/962b4f5343fa76ff5df51edc9aef9c4ebf1bccd2]
- 85. Building, benchmarking, and exploring perturbative maps ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC11469686/]
- 86. Frontiers | A Q-analysis package for higher-order interactions analysis... [https://www.frontiersin.org/journals/network-physiology/articles/10.3389/fnetp.2025.1691159/full]
- 87. Comparing methods for comparing networks [https://www.nature.com/articles/s41598-019-53708-y]
- 88. A large-scale benchmark for network inference from single- ... [https://www.nature.com/articles/s42003-025-07764-y]
- 89. [2210.17283] CausalBench: A Large-scale Benchmark for ... [https://arxiv.org/abs/2210.17283]
- 90. Benchmarking foundation cell models for post-perturbation ... [https://bmcgenomics.biomedcentral.com/articles/10.1186/s12864-025-11600-2]
- 91. Network topology and parameter estimation [https://bmcsystbiol.biomedcentral.com/articles/10.1186/1752-0509-8-13]
- 92. Tutorial — NetworkX 3.6 documentation [https://networkx.org/documentation/stable/tutorial.html]
- 93. Network Robustness Analysis Based on Maximum Flow [https://www.frontiersin.org/journals/physics/articles/10.3389/fphy.2021.792410/full]
- 94. Graph Metrics for Network Robustness—A Survey [https://www.mdpi.com/2227-7390/9/8/895]
- 95. Types of Network Topologies: Definitions and Use Cases [https://www.netally.com/general/types-of-network-topology/]
- 96. Comparative evaluation of strategies for improving the ... [https://appliednetsci.springeropen.com/articles/10.1007/s41109-023-00569-0]
- 97. Robustness surfaces of complex networks | Scientific Reports [https://www.nature.com/articles/srep06133]
- 98. Drug repurposing through pathway perturbation dynamics [https://www.sciencedirect.com/science/article/pii/S0169260725005929?dgcid=rss_sd_all]
- 99. Predicting transcriptional responses to novel chemical ... [https://www.nature.com/articles/s41467-024-53457-1]
- 100. Meta-analysis and Topological Perturbation in Interactomic ... [https://arxiv.org/html/2509.19410v1]
- 101. Improving Feature Methods in AI - Simple Science Attribution [https://scisimple.com/en/articles/2025-10-07-improving-feature-attribution-methods-in-ai--a3o0zyz]
- 102. Survey and perspective on verification, validation, and ... [https://www.nature.com/articles/s41746-025-01447-y]
- 103. A Robustness Evaluation Framework for Feature Attribution [https://arxiv.org/abs/2209.01782]
- 104. Benchmarking Attribution Methods with Relative Feature ... [https://arxiv.org/abs/1907.09701]
- 105. Advanced Feature Techniques for Deep Learning Models Attribution [https://www.auroria.io/advanced-feature-attribution-techniques-for-deep-learning-models/]
- 106. A large-scale benchmark for network inference from single-cell... [https://www.nature.com/articles/s42003-025-07764-y?error=cookies_not_supported]
- 107. Assessing the statistical significance of network topologies [https://journals.plos.org/plosone/article?id=10.1371/journal.pone.0309005]