Strategic Approaches for Handling Infeasible Solutions in Constrained Evolutionary Optimization
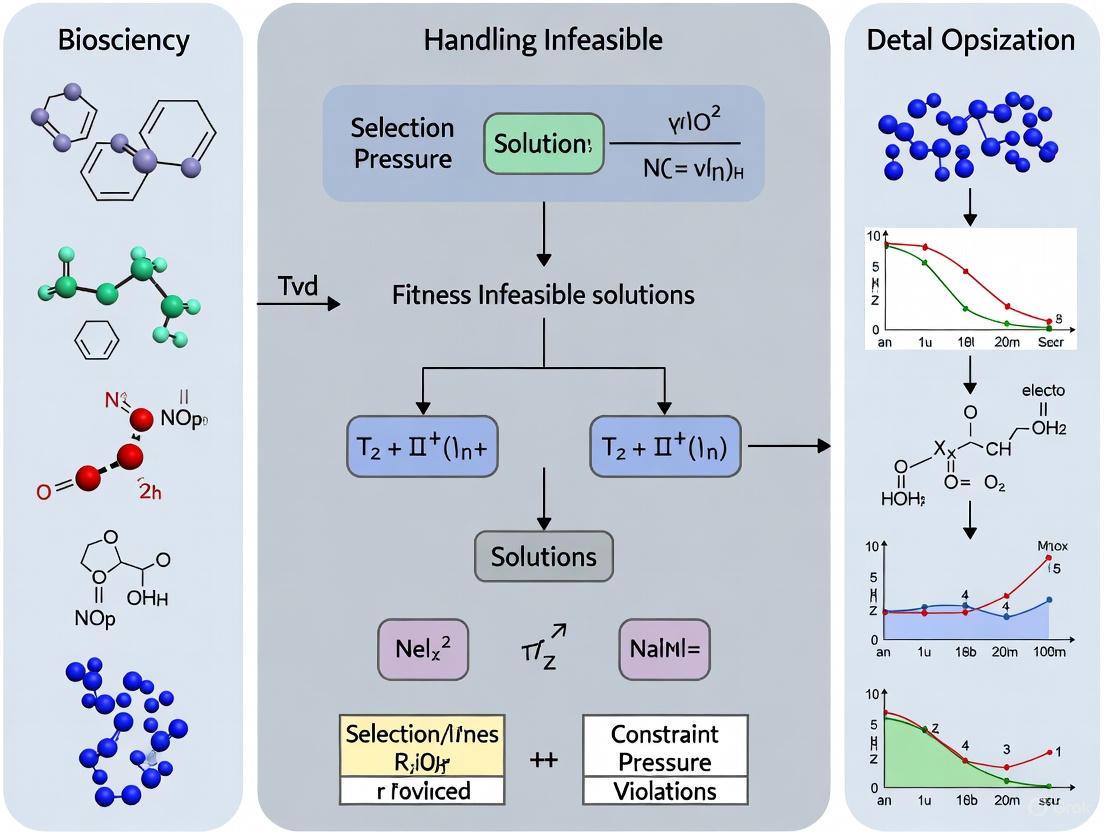
This article provides a comprehensive analysis of advanced methodologies for strategically leveraging infeasible solutions in constrained evolutionary optimization.
Strategic Approaches for Handling Infeasible Solutions in Constrained Evolutionary Optimization
Abstract
This article provides a comprehensive analysis of advanced methodologies for strategically leveraging infeasible solutions in constrained evolutionary optimization. Targeting researchers and drug development professionals, we explore the paradigm shift from discarding to strategically utilizing infeasible solutions through four key dimensions: fundamental principles of constraint violation metrics and feasibility rules; methodological implementations including multi-stage frameworks and adaptive penalty functions; optimization strategies for premature convergence and complex feasible regions; and rigorous validation using benchmark problems and industrial case studies. The synthesis of these approaches demonstrates significant potential for enhancing global search capability and solution quality in complex optimization scenarios prevalent in biomedical research and drug development.
Understanding Infeasible Solutions: Concepts and Significance in Constrained Optimization
Defining Constrained Optimization Problems and Constraint Violation Metrics
Frequently Asked Questions (FAQs)
1. What does it mean when my constrained optimization model is infeasible? An infeasible model is one where no solution exists that can satisfy all constraints simultaneously. This means the search space defined by the constraints has no overlapping region where all conditions are met. This can occur due to errors in the model formulation or because the real-world scenario described by the input data genuinely has no solution that meets all the requirements [1] [2].
2. What is a constraint violation metric? A constraint violation metric quantifies how severely an solution fails to meet the problem's constraints. A common formulation for the degree of constraint violation (G(x)) is the sum of violations for all constraints [3]: G(x) = Σ max( gᵢ(x), 0 ) + Σ max( |hⱼ(x)| - δ, 0 ) Here, gᵢ(x) are inequality constraints, hⱼ(x) are equality constraints, and δ is a small tolerance for converting equalities to inequalities [3]. This metric is crucial for algorithms that handle infeasible solutions.
3. What is an Irreducible Inconsistent Subsystem (IIS)? An IIS is a minimal set of constraints and variable bounds that is itself infeasible. If any single constraint or bound is removed from this set, the subsystem becomes feasible [1] [4]. Identifying an IIS helps you pinpoint the core conflicting rules in your model. Solvers like Gurobi, XPRESS, and CPLEX offer features to compute IISs [1] [5].
4. How can I resolve an infeasible model? Two primary approaches are analyzing the model and relaxing constraints.
- Diagnosis: Use tools like the IIS to identify the root cause of the conflict [1] [5].
- Relaxation: Transform "hard" constraints into "soft" constraints by introducing slack variables that are penalized in the objective function. This allows the solver to find a solution that minimally violates the constraints [1] [3]. This can be done manually or by using the built-in feasibility relaxation utilities in solvers like Gurobi and FICO Xpress [4] [5].
5. What is the difference between relaxable and unrelaxable constraints? This classification is vital for handling infeasibility [6]:
- Relaxable Constraints: These do not need to be strictly satisfied to obtain a meaningful output from the simulation or model. Slight violations are acceptable. An example could be a desired target output power.
- Unrelaxable Constraints: These must be satisfied for the solution to be physically or logically meaningful. An example is a constraint ensuring a positive pinch-point temperature difference in a heat exchanger, without which the process is thermodynamically impossible [6]. These are often handled with an extreme barrier approach, assigning an extremely high cost to any violation [6].
Troubleshooting Guide: My Model is Infeasible
Follow this logical workflow to diagnose and remedy an infeasible constrained optimization problem.
Step 1: Verify Input Data and Model Formulation
Before complex diagnosis, perform basic checks.
- Data Accuracy: Perform thorough sanity checks on your input data. Overpromising beyond capacity (e.g., production or resource limits) is a common cause of infeasibility [1].
- Model Accuracy: Check for simple coding errors: incorrect variable types, indexing mistakes, wrong bounds, or misusing equality instead of inequality [1].
- Best Practice: Always start with an algebraic formulation of your model before coding. This simplifies verification and sharing with colleagues [1].
Step 2: Compute an IIS
Use your solver's functionality to find an Irreducible Inconsistent Subsystem (IIS). This tool will return a minimal set of conflicting constraints [1] [5].
- In Python with Gurobi: Use the
Model.computeIIS()method [5]. - In Mosel with FICO Xpress: Use the
conflict_refinerfunctionality [4]. - Note: For large Mixed-Integer Programming (MIP) models, computing an IIS can be computationally expensive. For such cases, a feasibility relaxation (next step) may be a faster alternative [5].
Step 3: Analyze the IIS Output
Examine the constraints and bounds in the IIS. This is the core of your problem. Ask yourself:
- Are the constraints in the IIS logically contradictory (e.g., x ≥ y+1 and y ≥ x+1) [2]?
- Do they reflect a real-world impossibility given the current data (e.g., total demand exceeding total capacity) [2]?
Step 4: Choose a Resolution Strategy
Based on your analysis, choose a path forward.
Path A: Correct the Model or Data: If the IIS reveals a formulation error or incorrect data, correct it directly. This is the preferred solution during model development [1].
Path B: Relax Constraints: If the infeasibility is genuine (e.g., in production data), you need to relax constraints. This can be done manually or automatically.
- Using Slack Variables: Add slack variables to constraints and penalize their use in the objective function. This transforms hard constraints into soft ones [1].
- Using Built-in Relaxation: Solvers like Gurobi offer
Model.feasRelaxS()to automatically find the minimal relaxation needed for feasibility [5].
Step 5: Implement and Re-solve
Apply your chosen correction and solve the model again. If using constraint relaxation, the solution will indicate which constraints were violated and by how much, providing valuable business or research insights [2].
The Scientist's Toolkit: Key Reagents for Constrained Optimization
The table below outlines essential "research reagents"—methods and solver functions—for diagnosing and handling infeasibility.
Table 1: Essential Reagents for Handling Infeasibility
| Research Reagent | Function | Application Context |
|---|---|---|
| IIS Finder | Identifies a minimal set of conflicting constraints and bounds [1] [5]. | Primary diagnosis for linear and mixed-integer models to understand the root cause of infeasibility. |
| Slack Variables | Auxiliary variables added to constraints to absorb violations, transforming hard constraints into soft ones [1]. | Manual implementation of constraint relaxation; penalized in the objective function to find minimally violating solutions. |
| Feasibility Relaxation | A solver utility that automatically relaxes constraints and bounds to find a solution with minimal violation according to a specified metric [4] [5]. | An alternative to IIS for large models (especially MIP) or for directly obtaining a relaxed solution. |
| Constraint Violation Metric (G(x)) | A scalar measure quantifying the total infeasibility of a solution [3]. | Used in evolutionary algorithms to compare and steer infeasible solutions toward feasibility, e.g., in feasibility rules or ɛ-constraint methods [3]. |
| Extreme Barrier Function | Assigns an extremely poor (or infinite) objective value to any infeasible solution [6]. | Handling unrelaxable constraints that must be satisfied for a solution to be physically meaningful [6]. |
Experimental Protocols
Protocol 1: Implementing an IIS Analysis in Gurobi (Python)
This protocol details the steps to identify the cause of infeasibility using Gurobi's IIS functionality.
Methodology:
- Model Definition: Formulate and build the optimization model as usual.
- Solve and Check Status: After calling
model.optimize(), check if the model status isGRB.INFEASIBLE. - Compute IIS: Call
model.computeIIS()to instruct the solver to find the irreducible inconsistent subsystem. - Output Results: Write the IIS to a file for analysis using
model.write("model.ilp"). The.ilpfile will contain the minimal set of infeasible constraints.
Protocol 2: Implementing a Simple Feasibility Relaxation
This protocol describes how to use slack variables to handle infeasibility, a method applicable across various solvers and research codes.
Methodology:
- Define Slack Variables: For each constraint that can be relaxed, create a non-negative slack variable.
- Modify Constraints: Incorporate the slack variable to relax the constraint.
- For a constraint
f(x) ≤ b, it becomesf(x) - s ≤ b, withs ≥ 0. - For a constraint
f(x) ≥ b, it becomesf(x) + s ≥ b, withs ≥ 0.
- For a constraint
- Penalize in Objective: Add a penalty term to the objective function to discourage the use of slack. The new objective becomes
Minimize: Original_Cost + P * Σ s, wherePis a sufficiently large penalty weight.
Table 2: Comparison of Infeasibility Resolution Methods
| Method | Key Advantage | Key Disadvantage | Best Used When |
|---|---|---|---|
| IIS Analysis | Pinpoints the exact source of conflict for precise debugging [5]. | Can be computationally expensive for large MIP models [5]. | The root cause is unknown and the model is an LP or a manageable MIP. |
| Built-in Relaxation (e.g., feasRelaxS) | Fast, automated, and minimizes the relaxation according to a defined metric [5]. | Provides a "black-box" solution with less insight into the core conflict. | Speed is critical or the goal is simply to find a "close-to-feasible" solution. |
| Manual Slack Variables | Offers full control over which constraints are relaxed and the penalty structure [1]. | Requires manual setup and careful tuning of penalty weights to avoid numerical issues [1]. | Specific constraints are known to be soft, or full integration into a custom algorithm is needed. |
FAQs: Leveraging Infeasible Solutions in Constrained Optimization
Q1: Why should I keep infeasible solutions in my population? Won't they slow down convergence to a feasible optimum?
A1: Traditionally, infeasible solutions were often discarded. However, modern research shows that strategically maintaining infeasible solutions can be highly beneficial. They provide valuable information about the problem's landscape, help navigate around infeasible regions, and maintain population diversity. Crucially, infeasible solutions close to the feasible region boundary can be genetically closer to optimal feasible solutions than distant feasible ones, providing better genetic material for evolutionary operators [7]. The key is not to discard them, but to manage them intelligently.
Q2: What are the primary strategies for handling and utilizing infeasible solutions?
A2: The main strategies identified in current literature include:
- Feasibility Rules and Stochastic Ranking: Prefer feasible over infeasible solutions, but allow some high-quality infeasible solutions to remain based on a probability [8].
- Multi-Objective Transformation: Treat constraint satisfaction as separate objectives to be optimized alongside your primary objective. This allows you to work with a population that has varying degrees of feasibility and objective quality [9] [8].
- ε-Constrained Methods: Relax the constraints to allow solutions with a small, acceptable violation (ε) to be treated as feasible. This helps the population cross narrow infeasible regions [8].
- Dual-Population Approaches: Use one population to explore the feasible region and another to explore promising infeasible regions, allowing for information exchange between them [9].
- Preference-Based Optimization: Use a framework that prioritizes feasible solutions but also prefers infeasible solutions with lower constraint violations over those with higher violations, eliminating the need for careful penalty parameter tuning [10].
Q3: My algorithm gets stuck in a local feasible region. How can infeasible solutions help me escape it?
A3: This is a classic problem in constrained optimization, especially when feasible regions are disconnected. Allowing the population to traverse through promising infeasible regions can bridge isolated feasible zones. Techniques like the Feasible Search Boundary (CHT-FSB) dynamically define a boundary around feasible solutions, allowing infeasible solutions within this boundary to be considered potential candidates. This enables the algorithm to "cross" an infeasible valley to reach a separate, and potentially better, feasible region [9].
Q4: In a multi-objective setting, how can feasible solutions guide the search?
A4: In Constrained Multi-Objective Optimization Problems (CMOPs), feasible non-dominated solutions can be used to identify potential regions of the Constrained Pareto Front (CPF). A technique like the Feasible non-dominated reference set based Dominance Principle (FDP) uses these solutions to guide the search towards areas where the CPF is likely to exist, promoting a uniform and thorough exploration of the objective space [9].
Q5: Are there specific evolutionary algorithms where the handling of infeasible solutions is particularly critical?
A5: Yes. The handling method is a critical component that significantly impacts performance and reproducibility. For instance, in Differential Evolution (DE), the specific strategy for dealing with solutions generated outside the domain (even for simple box constraints) induces notably different behaviors in performance, disruptiveness, and population diversity. This effect grows with problem dimensionality. It is recommended to formally specify this strategy in any algorithmic description to ensure reproducibility [11].
Troubleshooting Guides
Problem 1: Population Stagnation in a Local Feasible Region
Symptoms: Convergence to a suboptimal feasible solution; rapid loss of population diversity; inability to find better solutions across disconnected feasible regions.
Solution Protocol:
- Diagnosis: Confirm that the problem has a complex constraint landscape (e.g., disconnected or narrow feasible regions). Check the population's feasibility history—a rapid, early jump to 100% feasibility often indicates over-preference for feasibility at the cost of exploration.
- Implementation: Integrate a dual-population mechanism.
- Implement an exploration-guided population (
P1) tasked with searching across both feasible and infeasible regions. Equip it with a constraint-handling technique like CHT-FSB that dynamically adjusts a search boundary to preserve promising infeasible solutions [9]. - Maintain an exploitation-guided population (
P2) that focuses on converging within the feasible regions identified. - Enable periodic information exchange between
P1andP2to allow the entire search process to benefit from both exploration and exploitation.
- Implement an exploration-guided population (
- Verification: Monitor the evolution of both populations. You should observe
P1gradually discovering new feasible regions, whileP2's solutions should show improvement in quality as it receives new genetic material.
Problem 2: Poor Balance Between Feasibility and Optimality
Symptoms: The algorithm finds feasible solutions easily, but they are of low quality; or, it finds high-quality solutions that are, however, infeasible.
Solution Protocol:
- Diagnosis: Evaluate your constraint-handling technique. Classic penalty function methods with fixed parameters are a common culprit.
- Implementation: Adopt a hybrid or advanced constraint-handling technique.
- Option A (Multi-Objective): Reformulate your single-objective constrained problem as a bi-objective problem where you simultaneously optimize the original objective
f(x)and the total constraint violationG(x). This allows you to find a trade-off front between performance and feasibility [8]. - Option B (Preference-Based): Implement a preference-based optimization framework like UCPO. This method uses a universal constrained preference loss function that inherently prioritizes feasibility and lower constraint violations without needing to tune sensitive penalty parameters [10].
- Option A (Multi-Objective): Reformulate your single-objective constrained problem as a bi-objective problem where you simultaneously optimize the original objective
- Verification: The output should be a set of solutions that represent a better trade-off. In the multi-objective case, you will get a Pareto front showing the relationship between objective value and constraint violation.
Problem 3: Algorithm is Overly Sensitive to Hyperparameters
Symptoms: Small changes in parameters (especially penalty factors) lead to drastically different results; requires extensive and problem-specific tuning.
Solution Protocol:
- Diagnosis: This is a known weakness of Lagrangian-based methods and penalty functions, where the Lagrange multipliers or penalty factors are notoriously sensitive to calibration [10].
- Implementation: Shift to a method that reduces or eliminates the need for such parameters.
- Verification: The algorithm's performance should become more robust and consistent across different runs and problem instances, with a significant reduction in time spent on parameter tuning.
Experimental Protocols & Data
Protocol 1: Implementing a Dual-Population Approach (UICMO)
Methodology: This protocol is based on the UICMO framework for constrained multi-objective optimization [9].
- Initialization: Randomly generate an initial population and split it into two sub-populations:
P1(exploration-guided) andP2(exploitation-guided). - Constraint Handling Assignment:
- For
P1, implement the Constraint Handling Technique based on Feasible Search Boundary (CHT-FSB). Calculate a dynamic boundary factorβ. An infeasible solution is considered "promising" and retained if a feasible solution exists within a Euclidean distanceβfrom it. - For
P2, implement the Feasible non-dominated reference set based Dominance Principle (FDP). Maintain an archive of feasible non-dominated solutions. Use this set to guide the selection pressure towards unexplored regions of the potential constrained Pareto front.
- For
- Evolution and Collaboration: Evolve
P1andP2for a defined number of generations using your chosen evolutionary algorithm (e.g., DE, GA). After everyKgenerations, allow a percentage of individuals to migrate betweenP1andP2to share information. - Termination: Combine the final
P1andP2and output the non-dominated feasible solutions as your approximation of the Pareto front.
Logical Workflow:
Protocol 2: Preference Optimization for Hard Constraints (UCPO)
Methodology: This protocol uses the UCPO framework to fine-tune a pre-trained neural solver for combinatorial problems with hard constraints [10].
- Warm-Start: Obtain a pre-trained model checkpoint for your target combinatorial problem (e.g., a model trained on TSP). This serves as a high-quality initializer.
- Fine-Tuning with Preference Loss:
- For a set of problem instances, sample solution pairs
(x, x'). - Compute the UCPO loss, which comprises:
- Feasibility Margin Loss: Ensures a margin between the scores of feasible and infeasible solutions.
- Primal Refinement Loss: Encourages improvement in the objective value.
- Dual Exploration Loss: Promotes exploration by increasing the score of infeasible solutions with low constraint violation.
- Perform gradient-based updates on the model parameters using this aggregated loss.
- For a set of problem instances, sample solution pairs
- Inference: Use the fine-tuned model to generate solutions for new, constrained problem instances (e.g., TSP with Time Windows).
Quantitative Comparison of Multi-Objective Optimization Algorithms: Table: Performance of MOO Algorithms on a Pharmaceutical Formulation Problem [12]
| Algorithm | Hypervolume | Generational Distance | Inverted Generational Distance | Spacing | Weighted Sum Method Score |
|---|---|---|---|---|---|
| NSGA-III | Highest | Smallest | Smallest | Most Uniform | 82.08 |
| MOEAD | High | Small | Small | Uniform | 80.89 |
| RVEA | Competitive | Competitive | Competitive | Competitive | Slightly Lower |
| C-TAEA | Competitive | Competitive | Competitive | Competitive | Slightly Lower |
| AGE-MOEA | Competitive | Competitive | Competitive | Competitive | Slightly Lower |
The Scientist's Toolkit: Key Research Reagents
Table: Essential Computational "Reagents" for Constrained Evolutionary Optimization
| Research Reagent | Function / Role in the Experiment |
|---|---|
| Differential Evolution (DE) | A versatile evolutionary algorithm framework that operates on real-valued vectors. Its mutation and crossover operators are highly effective for continuous optimization problems [13] [8]. |
| Reference Point Set (e.g., for NSGA-III) | A set of predefined points in objective space that guide the population towards a well-distributed set of Pareto-optimal solutions, crucial for many-objective problems [12]. |
Constraint Violation Metric G(x) |
A single, aggregate measure of the total violation of all constraints by a solution x. This is the fundamental quantity for any constraint-handling technique [9] [8]. |
| Feasible Non-Dominated Archive | A dynamic memory that stores the best feasible, non-dominated solutions found so far during the search. Used in techniques like FDP to guide the exploitation population [9]. |
| Preference Optimization Loss Function | A composite loss function (e.g., from UCPO) that allows fine-tuning neural solvers to handle hard constraints without manual penalty tuning or complex masking logic [10]. |
Taxonomy of Constraint Handling Techniques in Evolutionary Algorithms
Frequently Asked Questions (FAQs)
Q1: What is the core challenge when handling constraints in Evolutionary Algorithms (EAs)? The primary challenge is effectively balancing the search for optimal solutions with the need to satisfy all problem constraints. This involves making decisions about how to guide the population towards the feasible region while not prematurely converging or losing valuable genetic information from infeasible solutions that may be close to the global optimum, which often lies on constraint boundaries [14].
Q2: My algorithm is converging to a suboptimal feasible region. How can I improve its exploration capability? This is a common issue when the algorithm over-penalizes infeasible solutions too early. Consider implementing a two-stage approach. In the first stage, relax the constraints or use an exploratory population that ignores constraints to explore the entire search space and approximate the unconstrained Pareto Front. In the second stage, strictly enforce constraints or use a feasibility-driven population to exploit the feasible regions and refine the solutions [15] [16]. This balances exploration and exploitation.
Q3: How should I handle equality constraints?
Equality constraints are typically converted into inequality constraints using a tolerance value δ. The constraint violation for an equality constraint h_j(x) is calculated as max(0, |h_j(x)| - δ), where δ is a small positive tolerance (e.g., 10^-6) [8] [16]. This transformation allows the algorithm to treat near-feasible solutions as feasible, making the search process more manageable.
Q4: What should I do when my population contains very few or no feasible solutions? When feasible solutions are rare, pure feasibility-based rules can fail. Instead, use techniques that leverage information from infeasible solutions. Methods like the Infeasibility Driven Evolutionary Algorithm (IDEA) explicitly maintain a small percentage of "good" infeasible solutions close to the constraint boundaries [14]. Alternatively, ranking-based methods like E-BRM create separate ranking lists for feasible and infeasible solutions, then merge them, giving higher priority to feasible solutions but also valuing infeasible ones with low constraint violation [17].
Q5: Are there strategies to automatically select the best constraint handling technique during a run? Yes, ensemble and adaptive strategies address this. For instance, one can use a Multi-Armed Bandit (MAB)-based decision-making strategy. This approach runs multiple populations, each with a different Constraint Handling Technique (CHT), and adaptively selects the most suitable parent population for offspring generation based on real-time performance feedback [15]. This is particularly useful without prior knowledge of the problem's constraint characteristics.
Troubleshooting Guides
Problem 1: Premature Convergence to a Local Feasible Optimum
Symptoms: The population becomes feasible quickly but the objective function value stagnates at a non-optimal value. Diversity is lost early in the run.
Possible Causes and Solutions:
- Cause: Overly greedy feasibility preference.
- Solution: Integrate an infeasibility-driven mechanism. Modify your selection process to rank some marginally infeasible solutions higher than feasible ones if they have better objective values, forcing the population to explore near constraint boundaries [14].
- Cause: Single-population approach with a fixed CHT.
- Cause: Ineffective balance between exploration and exploitation.
- Solution: Implement a dynamic two-stage strategy. Let the first stage focus primarily on exploration (e.g., by ignoring constraints or using a multi-objective technique to find the unconstrained Pareto Front). Then, switch to a second stage that focuses on exploiting the feasible regions identified [15].
Problem 2: Inability to Find Any Feasible Solutions
Symptoms: The algorithm completes its run without discovering a single feasible solution, or finds feasible solutions only very late in the process.
Possible Causes and Solutions:
- Cause: The feasible region is extremely small or disconnected.
- Solution: Use a constraint relaxation mechanism. For example, in a two-stage archive-based algorithm (CMOEA-TA), constraints can be relaxed in the first stage based on the proportion of feasible solutions and the degree of constraint violation, encouraging the population to approach the feasible region gradually [16].
- Cause: Penalty coefficients are too high or too low.
- Cause: Population is not directed towards feasibility.
- Solution: For large-scale problems, hybridize the EA with a local constraint-handling method. One approach is to use the Constraint Consensus (DBmax) method, which can be applied to infeasible solutions within a cooperative coevolution framework to actively improve their feasibility [19].
Problem 3: Poor Performance on Large-Scale Constrained Problems
Symptoms: The algorithm's performance degrades significantly as the number of decision variables and constraints increases. Computation time becomes prohibitive.
Possible Causes and Solutions:
- Cause: The "curse of dimensionality" exacerbates the search complexity.
- Solution: Implement a cooperative coevolution (CC) framework. Decompose the large-scale problem into smaller, more manageable subproblems using techniques like Recursive Differential Grouping. Then, evolve these subproblems separately [19].
- Cause: Inefficient handling of many constraints.
- Solution: Use a classification-collaboration constraint handling technique. Randomly classify the constraints into
Kgroups, decompose the original problem intoKsubproblems, and assign each to a subpopulation. These subpopulations can then interact through learning strategies to generate better solutions for the original problem [8].
- Solution: Use a classification-collaboration constraint handling technique. Randomly classify the constraints into
Experimental Protocols & Methodologies
Protocol 1: Implementing a Two-Stage Ensemble Algorithm (CMOEA-TENS)
This protocol is effective for constrained multi-objective problems where the balance between convergence and diversity in the feasible region is critical [15].
- Initialization: Initialize an ensemble of multiple populations (e.g., four). Each population is assigned a different CHT, focusing on aspects like feasibility, diversity, or convergence.
- Stage 1 - Exploration:
- Designate one population as the "exploratory" population, which ignores all constraints.
- The goal of this stage is for the exploratory population to drive the evolution and converge towards the Unconstrained Pareto Front (UPF).
- The other populations in the ensemble co-evolve, leveraging the solutions found by the exploratory population.
- Stage 2 - Exploitation:
- Switch the driving force of the evolution to the ensemble of CHT-based populations.
- The goal is to refine the search and converge to the Constrained Pareto Front (CPF).
- Offspring Generation & Selection:
- Implement a Multi-Armed Bandit (MAB) strategy. The MAB dynamically selects the most suitable parent population from the ensemble for generating offspring in each generation, based on real-time performance feedback.
- Select parents from the chosen population and generate offspring using evolutionary operators (e.g., crossover, mutation).
- Environmental Selection: Combine parents and offspring, and select the next generation based on the specific CHT assigned to each population and Pareto dominance principles.
Protocol 2: Implementing the Infeasibility Driven Evolutionary Algorithm (IDEA)
This protocol is designed to improve performance on problems where the optimal solution lies on a constraint boundary by explicitly maintaining useful infeasible solutions [14].
- Initialization: Generate a random initial population.
- Evaluation and Classification: Evaluate each individual for objective function value and constraint violation. Classify the population into feasible and infeasible solutions.
- Ranking:
- Rank the infeasible solutions based on a combination of their objective function value and constraint violation. The key is to rank some "good" infeasible solutions (those with low objective value and low violation) higher than feasible solutions.
- Rank the feasible solutions based primarily on their objective function value.
- Selection and Reproduction: Use a selection operator (e.g., tournament selection) that considers this special ranking, ensuring that the best infeasible solutions are preserved and can participate in creating offspring.
- Replacement: Form the new population by selecting top-ranked individuals from the combined list of feasible and infeasible solutions, guaranteeing that a small percentage of the best infeasible solutions are retained.
Research Reagent Solutions
Table 1: Essential Computational Tools and Techniques for Constrained Evolutionary Optimization.
| Research Reagent | Function & Purpose |
|---|---|
| Feasibility Rules (e.g., CDP) | A simple, popular method that strictly prefers any feasible solution over any infeasible one. Serves as a baseline and is effective when feasible regions are easy to find [15]. |
| Stochastic Ranking (SR) | Balances the influence of objective and constraint functions by using a probability P to compare individuals based on objective function, even when infeasible. Helps prevent domination by either the objective or constraints [8]. |
| ε-Constraint Method | Relaxes constraints by allowing solutions with violation below a threshold ε to be treated as feasible. The parameter ε can be adaptively decreased during the run, providing a smooth transition from exploration to exploitation [8] [15]. |
| Penalty Function | Degrades the fitness of infeasible solutions by adding a penalty term proportional to their constraint violation. Adaptive versions self-tune the penalty coefficient, reducing parameter sensitivity [8] [17] [18]. |
| Multi-Objective CHT | Transforms the constrained problem into an unconstrained multi-objective one by treating constraint violations as additional objectives to minimize. Allows the use of well-established MOEAs [8]. |
| Test Suites (CEC2006, CEC2010, CEC2017) | Standard sets of benchmark constrained optimization problems. Used for rigorous validation, performance comparison, and ablation studies of new algorithms [8] [17]. |
| Performance Indicators (IGD, HV) | Quantitative metrics like Inverted Generational Distance (IGD) and Hypervolume (HV) used to assess the convergence and diversity of the obtained solution set against the true Pareto front [16]. |
Visualization of Key Concepts
Diagram 1: Two-Stage Evolutionary Workflow for Constrained Optimization
Diagram 2: High-Level Taxonomy of Constraint Handling Techniques
Feasibility Rules and Stochastic Ranking Approaches
Troubleshooting Guide: Common Issues with Constrained Evolutionary Optimization
Problem 1: Algorithm Converges on Infeasible Solutions
- Description: The evolutionary algorithm consistently produces solutions that violate problem constraints, failing to find the feasible region.
- Possible Causes & Solutions:
- Cause: Poor balance between objective function and constraint minimization. The search is overly biased toward better objective values, even in infeasible space [20].
- Solution: Implement a dynamic knowledge transfer mechanism. Classify your problem's objective as "simple" (clear minimizing direction) or "complex" (highly nonlinear). For simple objectives, use an objective-oriented constraint handling technique (CHT) that transfers knowledge from the objective to help satisfy constraints. For complex objectives, use a constraint-oriented CHT that first drives the population toward feasibility before considering the objective [20].
- Cause: Inadequate diversity maintenance near feasible region boundaries.
- Solution: Deliberately maintain and utilize "useful infeasible solutions" close to the feasible region. These solutions can, through genetic operators, help generate new solutions inside the feasible region and enable better sampling near its boundaries [7].
Problem 2: Algorithm is Trapped in Local Feasible Regions
- Description: The algorithm finds a small, suboptimal feasible region but cannot escape to discover better, potentially larger feasible areas.
- Possible Causes & Solutions:
- Cause: Infeasible barriers between disjoint feasible regions are too difficult for the algorithm to cross.
- Solution: Temporarily relax constraints using an
ɛ-constraint method or a stochastic ranking technique. This allows the population to traverse infeasible regions to reach other, more promising feasible areas [20]. - Cause: Loss of diversity in the population after discovering a feasible solution.
- Solution: Introduce a diversity mechanism into your evolution strategy. This can involve specific mutation operators or a niching technique to maintain a diverse population and continue exploring the search space [7].
Problem 3: Infeasibility in Complex Mathematical Optimization Models
- Description: When solving complex models (e.g., MIPs), the solver reports the model as infeasible.
- Possible Causes & Solutions:
- Cause: A small subset of conflicting constraints is making the entire model infeasible.
- Solution: Use an Irrreducible Infeasible Set (IIS) finder. Many modern solvers (like CPLEX) can identify an IIS—a minimal set of constraints and variable bounds that are mutually contradictory—which helps you pinpoint the exact source of infeasibility [21].
- Cause: Model formulation errors or incorrect data inputs.
- Solution: Systematically test your model. Build the model one constraint at a time, testing feasibility frequently. Fix variables to a known feasible solution (if one exists) to verify each new constraint's correctness [21].
Problem 4: Slow Convergence and High Computational Cost
- Description: The algorithm finds feasible solutions but is computationally expensive and takes too long to converge to a high-quality result.
- Possible Causes & Solutions:
- Cause: Evaluating the fitness of a large population over many generations is inherently computationally intensive [22].
- Solution: Analyze the problem landscape. If the objective function and constraints are correlated, use methods that leverage this relationship (like the KTR indicator) to guide the search more efficiently. For problems with complex objectives, avoid premature use of objective information that can lead the population to local optima [20].
- Cause: Inefficient handling of constraints for every individual in every generation.
- Solution: Consider using penalty functions that add a penalty for constraint violations to the objective function. To avoid numerical issues, use a reasonable penalty weight instead of an extremely large one. Alternatively, use a feasibility rule that prioritizes feasible solutions over infeasible ones, and between infeasible solutions, prioritizes those with a lower total constraint violation [20] [21].
Frequently Asked Questions (FAQs)
Q1: What are the main categories of Constraint Handling Techniques (CHTs)? The popular CHTs can be briefly divided into six categories [20]:
- Penalty Functions: Add a penalty for constraint violation to the objective value.
- Feasibility Rules: Prioritize solutions based on feasibility and degree of constraint violation.
- Stochastic Ranking: Rank solutions with a probability of switching between objective and constraint violation as the ranking criteria.
ɛ-Constraint: Allow a controllable level of constraint violation.- Multiobjective Optimization: Treat constraints as separate objectives to be minimized.
- Hybrid Methods: Combine two or more of the above techniques.
Q2: How can "useful infeasible solutions" improve my optimization? Maintaining infeasible solutions that are very close to the feasible region, especially those located in promising areas, can be highly beneficial. Using genetic operators (crossover and mutation), these solutions can help generate new offspring inside the feasible region. They also ensure the feasible region boundaries are well-sampled, which can lead to discovering better feasible solutions than if only feasible solutions were maintained [7].
Q3: My model is infeasible. How can I quickly diagnose the cause? Beyond using an IIS, you can [21]:
- Add slack variables: Convert hard constraints into soft ones by adding slack variables with a high penalty in the objective function. Solving this penalized model will show you which constraints are being violated (and by how much), helping to locate the source of infeasibility.
- Build and test incrementally: Add constraints to your model one by one, solving the model after each new addition. The point at which the model becomes infeasible immediately identifies the problematic constraint or the interaction causing the issue.
Q4: What is the core process of an Evolutionary Algorithm (EA)? EAs generally follow an iterative process with these key steps [22]:
- Initialization: Generate an initial population of random potential solutions.
- Fitness Evaluation: Assess each solution using a fitness function that measures how well it solves the problem.
- Selection: Select the fittest solutions to be parents for reproduction.
- Reproduction (Crossover/Mutation): Create new offspring by combining parts of parent solutions (crossover) and introducing small random changes (mutation).
- Replacement: Form a new population from the offspring and, optionally, some parents.
- Termination: Repeat from step 2 until a stopping condition (e.g., max iterations, fitness threshold) is met.
Experimental Protocol: Benchmarking CHT Performance
To rigorously compare the performance of different Constraint Handling Techniques within an Evolutionary Algorithm framework, follow this structured experimental methodology, adapted from recent literature [23] [20].
1. Benchmark Problems: Utilize established test suites to ensure a comprehensive evaluation.
- Recommended Suites: IEEE CEC2006, CEC2010, and CEC2017 for constrained optimization [20].
- Rationale: These suites provide a variety of problem landscapes with different challenges, such as disjoint feasible regions and nonlinear constraints.
2. Performance Measures: Use multiple metrics for a fair comparison. The expected run-time (fixed-target perspective) is a robust metric [23].
- Primary Metric: Function Evaluations (FE): Record the number of times the objective function is evaluated until the algorithm finds a solution with an objective value at or below a predefined target (e.g., the known global optimum or a best-known value). This is preferred over CPU time, which can be influenced by the computing environment [23].
- Secondary Metric: Best Achievable Solution Quality (Fixed-Budget): For a fixed budget of FEs, record the best solution quality achieved. This measures how close the solution is to the global optimum given limited resources [23].
3. Statistical Comparison Protocol: Due to the stochastic nature of EAs, perform multiple independent runs and use robust statistical analysis.
- Runs: Execute each algorithm-CHT combination on each problem for a minimum of 20-30 independent runs [23].
- Analysis: Use a bootstrapping-based hypothesis testing procedure that incorporates the principles of severity. This approach goes beyond simple
p-values by considering the magnitude of performance differences and their practical relevance [23]. - Ranking: A novel ranking scheme analogous to a football league can be employed. Algorithms get points for wins/draws against others on each problem, and the magnitude of performance difference ("goal difference") serves as a tie-breaker and quantitative performance measure [23].
| Technique | Core Principle | Key Advantages | Potential Drawbacks |
|---|---|---|---|
| Penalty Functions | Adds a penalty for constraint violation to the objective function. | Simple to implement; widely applicable. | Performance highly sensitive to the choice of penalty weights; can cause numerical issues [21]. |
| Feasibility Rules (FR) | Gives strict precedence to feasible solutions; compares infeasibles by their violation. | No parameters to tune; strong push towards feasibility. | May reject promising infeasible solutions that are close to the global optimum. |
| Stochastic Ranking | Ranks solutions with a probability of using objective or violation. | Balances objective and constraints without hard rules. | Performance depends on the chosen ranking probability. |
ɛ-Constraint |
Allows a dynamically controlled level of constraint violation. | Can bridge infeasible regions between feasible areas. | Requires a strategy for adaptively managing ɛ. |
| Multiobjective | Treats constraints as separate objectives. | Leverages powerful multi-objective algorithms. | Increases problem complexity; can be computationally expensive. |
| Knowledge Transfer (CLBKR) | Classifies objective as simple/complex and applies tailored CHT [20]. | Dynamically adapts to problem characteristics. | Requires a problem classification step. |
The Scientist's Toolkit: Research Reagents & Materials
This table lists key algorithmic components and their functions for implementing and experimenting with feasibility rules and stochastic ranking.
| Item | Function in the Experiment |
|---|---|
| Evolutionary Algorithm Engine | The core optimizer (e.g., Differential Evolution, Evolution Strategy) that handles population management, selection, and genetic operators [20]. |
| Constraint Violation Calculator | A function that calculates the degree of violation for all constraints for a given solution, often summed into a single scalar value G(x) [20]. |
| Feasibility Rule (FR) Comparator | A procedure for comparing two solutions that prioritizes: 1) feasible over infeasible, 2) if both infeasible, the one with lower total constraint violation [20]. |
| Stochastic Ranking Procedure | A ranking algorithm that probabilistically switches between comparing solutions based on their objective value and their constraint violation [20]. |
| IIS (Irrreducible Infeasible Set) Finder | A solver tool (e.g., in CPLEX) that identifies the minimal set of conflicting constraints in an infeasible model, crucial for debugging [21]. |
| Benchmark Test Suites (CEC2006, etc.) | Standardized sets of constrained optimization problems used to ensure fair and comprehensive performance testing of new algorithms [20]. |
| Performance Analysis Toolkit | Software for statistical comparison of results (e.g., using severity-based testing) and visualization (e.g., IOHanalyzer) [23]. |
Workflow for Selecting a Constraint Handling Strategy
This diagram illustrates a logical decision pathway for selecting an appropriate constraint handling approach, based on problem characteristics.
The Role of Infeasible Solutions in an EA Cycle
This diagram integrates the strategic use of infeasible solutions into the standard evolutionary algorithm workflow.
The Role of Infeasible Solutions in Maintaining Population Diversity
Frequently Asked Questions
1. What is an infeasible solution, and why is it important in constrained optimization? An infeasible solution is a candidate answer generated during the evolutionary process that violates one or more constraints of the problem. Unlike in traditional approaches where they are immediately discarded, modern research shows that selectively retaining certain infeasible solutions is crucial. They help maintain population diversity, enable the algorithm to cross infeasible "valleys" to reach separate feasible regions, and prevent the population from getting trapped in local optima, especially in problems with complex, narrow, or disjoint feasible spaces [11] [24] [25].
2. My algorithm is converging prematurely. Could my handling of infeasible solutions be the cause? Yes, this is a common issue. Overly strict constraint-handling, which eliminates all infeasible solutions, can drastically reduce population diversity and lead to premature convergence. This is particularly problematic when the feasible region is small or complex. To mitigate this, consider implementing strategies that preserve some well-distributed infeasible solutions. Algorithms like EGDCMO and DP-NSGA-III explicitly maintain an archive of infeasible solutions with good objective values or distribution to guide the population and improve exploration [24] [25] [26].
3. How do I choose which infeasible solutions to keep? Not all infeasible solutions are equally valuable. The key is to prioritize those that contribute to population diversity or have promising objective values. Effective strategies include:
- Global Diversity: Using weight vectors to partition the objective space and selecting infeasible solutions that are well-distributed across these subregions [24].
- Balanced Fitness: Evaluating infeasible solutions with a fitness function that balances their constraint violation degree with their objective function quality [24] [26].
- ε-Constraint Method: Allowing solutions with a constraint violation below a dynamically decreasing threshold (ε) to participate in the evolution, effectively treating them as "quasi-feasible" [25].
4. Are there strategies for leveraging infeasible solutions in drug discovery and molecule optimization? Absolutely. In drug discovery, the chemical space is vast and complex. Methods like the Swarm Intelligence-Based Method for Single-Objective Molecular Optimization (SIB-SOMO) use operations like "Random Jump" on particles (molecules) that are not improving. This introduces random changes, effectively creating novel infeasible structures that can help the swarm escape local optima and explore a wider area of the molecular space to find better, feasible candidates [27].
Troubleshooting Guides
Problem: Population Lacks Diversity in Problems with Disjoint Feasible Regions
- Symptoms: The population converges to a single, small feasible area, missing other potentially better regions. The algorithm performs poorly on problems where the feasible Pareto front is composed of multiple disconnected parts.
- Solution: Implement a Dual-Population or Multi-Archive Approach.
- Description: Maintain two co-evolving populations. The main population focuses on solving the constrained problem. An auxiliary population ignores constraints to explore the unconstrained Pareto front, providing genetic material to help the main population cross infeasible barriers.
- Protocol: The DP-NSGA-III algorithm is a prime example [25].
- Initialize two populations: Pop1 (main) and Pop2 (auxiliary).
- Evolve Pop1 using a constrained handling method (e.g., ε-constraint).
- Evolve Pop2 without considering any constraints, focusing solely on objective optimization.
- Exchange Offspring between the two populations every generation.
- Output the feasible solutions from Pop1 as the final result.
- Expected Outcome: The main population receives high-quality genetic information from the unconstrained search, enabling it to discover all disjoint segments of the feasible Pareto front and significantly improving convergence and diversity [25].
Problem: Algorithm Struggles with Balancing Objectives and Constraints
- Symptoms: The search is either dominated by constraint satisfaction, leading to poorly optimized objectives, or by objective optimization, leading to a high proportion of infeasible solutions.
- Solution: Adopt an Adaptive Penalty or Fitness Function.
- Description: Instead of treating all constraints equally, assign them different weights based on their violation severity or significance to guide the search more intelligently.
- Protocol: As implemented in the CdEA-SCPD algorithm [26]:
- Investigate Stage: During evolution, automatically calculate the significance (
Sig_j) for each constraintjbased on the population's current violation severity. - Adaptive Penalty: Calculate the total constraint violation for a solution
xasTotal_CV(x) = Σ (Sig_j * CV_j(x)), whereCV_j(x)is the violation of the j-th constraint. - Fitness Evaluation: Combine the objective value
f(x)andTotal_CV(x)into a single fitness function to rank solutions.
- Investigate Stage: During evolution, automatically calculate the significance (
- Expected Outcome: The algorithm gains "interpretability" by understanding which constraints are most critical, leading to faster and more stable convergence toward the true constrained optimum [26].
Problem: Premature Convergence in Molecular Optimization
- Symptoms: In molecule generation tasks, the algorithm repeatedly produces similar molecular structures and fails to discover novel candidates with improved properties.
- Solution: Integrate Exploration-Enhancing Operations.
- Description: Incorporate specific operations that actively disrupt convergence to push the search into new areas of the chemical space.
- Protocol: Following the SIB-SOMO framework for molecule optimization [27]:
- MIX Operation: Combine a current molecule (particle) with its local best and the global best molecule to create new candidates.
- MOVE Operation: Select the best candidate from the original and mixed molecules.
- Random Jump/Vary Operation: If the original particle remains the best after MIX, apply a "Random Jump" that randomly alters a portion of its structure (e.g., atoms or bonds). This introduces infeasible or novel intermediates that help escape local optima.
- Expected Outcome: Enhanced exploration of the vast molecular space, leading to the discovery of more diverse and novel molecular structures with desired properties in a shorter time [27].
Experimental Protocols for Key Studies
Protocol 1: Utilizing a Global Diversity Strategy for CMOPs (EGDCMO) This protocol is based on the EGDCMO algorithm designed for constrained multi-objective problems with small feasible regions [24].
- Initialization: Generate an initial population
Pand a set of weight vectors to partition the objective space into subregions. - Loop for a maximum number of generations:
- Reproduction: Create offspring
QfromPusing genetic operators. - Combination: Let
R = P ∪ Q. - Feasible Selection: Select all feasible solutions from
Rto formF. - Infeasible Selection (Global Diversity): From the remaining infeasible solutions, select a set
Ithat is well-distributed across the subregions defined by the weight vectors. Use a new fitness function that balances constraint violation and objective value for selection. - New Population: Form the next generation
Pby combiningFandI.
- Reproduction: Create offspring
- Output: The final feasible, non-dominated solutions.
Protocol 2: A Dual-Population Approach for Many-Objective Problems (DP-NSGA-III) This protocol is for challenging constrained many-objective problems (CMaOPs) and is derived from the DP-NSGA-III algorithm [25].
- Initialization: Create two populations: Pop1 (main) and Pop2 (auxiliary). Initialize an ε value using the provided formula based on initial constraint violation.
- Loop for a maximum number of generations:
- Evolve Pop1: Use NSGA-III with an ε-constraint method. Solutions with violation < ε are treated as feasible during environmental selection.
- Evolve Pop2: Use NSGA-III but completely ignore all constraints during environmental selection.
- Offspring Sharing: Combine the offspring from both populations. Each population uses the combined offspring pool for its next evolution step.
- Update ε: Decrease the ε value according to the monotonically decreasing function.
- Output: The final Pop1 population.
Research Reagent Solutions
The table below lists key algorithmic components and their functions in research on infeasible solutions.
| Component/Strategy | Primary Function in Research |
|---|---|
| ε-Constraint Method [25] | Dynamically relaxes constraints during early evolution, allowing beneficial infeasible solutions to participate and guide the search. |
| Dual-Population Coevolution [25] | Enables one population to explore the unconstrained objective space, providing genetic information to help a second population satisfy complex constraints. |
| Global Diversity Archive [24] | Actively maintains a diverse set of infeasible solutions across the objective space to prevent premature convergence and aid in exploring disjoint regions. |
| Adaptive Penalty Function [26] | Automatically assigns different weights to constraints based on their violation severity, improving interpretability and convergence. |
| Random Jump Operation [27] | In molecular optimization, it randomly modifies a solution to escape local optima and explore new areas of the chemical space. |
Optimization Strategy Workflow
The following diagram illustrates the logical relationships and workflow of a dual-population approach that leverages infeasible solutions, synthesizing concepts from the cited research.
Frequently Asked Questions: KKT Conditions and Constraints
What do the KKT conditions represent in a constrained optimization problem? The Karush-Kuhn-Tucker (KKT) conditions are first-order necessary conditions for a solution in nonlinear programming to be optimal, provided that some regularity conditions are satisfied. They generalize the method of Lagrange multipliers to allow for inequality constraints. A key interpretation is that at the optimum, the gradient of the objective function can be expressed as a linear combination of the gradients of the active constraints, effectively balancing the "forces" that keep the solution within the feasible region [28].
What does the *Stationarity condition mean?* The stationarity condition requires that at the optimal point ( x^* ), the gradient of the Lagrangian function ( L ) with respect to ( x ) is zero. For a minimization problem, this is expressed as ( \partial f(x^) + \sum_{j=1}^{\ell} \lambda_j \partial h_j(x^) + \sum{i=1}^{m} \mui \partial g_i(x^*) \ni \mathbf{0} ). This means the objective function's gradient is balanced by the gradients of the constraints [28].
Why is *Dual Feasibility ( \mu_i \geq 0 ) required for inequality constraints?* The dual feasibility condition ensures that the Lagrange multipliers ( \mu_i ) for inequality constraints are non-negative. This is crucial because it guarantees that the influence of an active inequality constraint opposes the decrease of the objective function, ensuring optimality. A negative multiplier would imply that the objective could be improved by moving further into the infeasible region, which is illogical [28] [29].
What is the practical interpretation of *Complementary Slackness?* Complementary Slackness ( \mui gi(x^) = 0 ) means that for each inequality constraint, either the constraint is active ( g_i(x^) = 0 ), or its corresponding Lagrange multiplier is zero ( \mui = 0 ), or both. If a constraint is not active ( gi(x^*) < 0 ), it has no direct influence on the solution (its multiplier is zero). Conversely, a non-zero multiplier ( \mu_i > 0 ) indicates that the constraint is active at the optimum [28] [29].
A solution satisfies the KKT conditions but is clearly not the global minimum. What might be wrong? The KKT conditions are necessary for optimality under certain regularity conditions (like constraint qualifications). If a solution meets the KKT conditions but is not the global minimum, the problem might be non-convex. For convex problems (convex objective and feasible region), the KKT conditions are sufficient, and any point satisfying them is a global minimizer. For non-convex problems, a KKT point could be a local minimum or a saddle point [28] [30].
How do I handle a case where my optimization algorithm converges to an infeasible solution? Convergence to an infeasible solution often indicates issues with the constraint handling method. In evolutionary algorithms, one advanced approach is to use adaptive penalty functions that assign different weights to constraints based on their violation severity. This helps guide the search back towards the feasible region by treating more severely violated constraints as more significant. Additionally, maintaining an archive of infeasible solutions with good objective values can provide directional information to help cross narrow feasible regions [26].
What does it mean if most of my Lagrange multipliers are zero at the solution? This is a common occurrence explained by complementary slackness. It means that the corresponding inequality constraints are not active at the solution ( g_i(x^*) < 0 ) and thus do not directly influence the optimal point. In practical terms, you could potentially remove these constraints from your model without changing the optimal solution, simplifying the problem [28] [29].
In the context of evolutionary constrained optimization, why is it ineffective to treat all constraints equally? In real-world problems, constraints have varying levels of "significance." Treating them equally fails to exploit their individual characteristics. Research shows that assigning different weights to constraints based on their violation severity enhances an algorithm's interpretability and helps it converge more rapidly toward the global optimum. The significance of each constraint can even be investigated spontaneously during the evolution process [26].
Troubleshooting Common KKT Issues
| Problem Symptom | Potential Cause | Diagnostic Steps | Solution & Recommendations |
|---|---|---|---|
| Infeasible KKT System: The KKT equations and complementarity conditions yield no solution. | Incorrect assumption about which constraints are active. | 1. Verify primal feasibility of the candidate point.2. Check all combinations of active/inactive constraints (e.g., for 3 constraints, check all 8 cases) [30]. | Re-solve the problem by systematically enumerating all active-set combinations. For convex problems, a graphical analysis can identify the active constraints [30]. |
| Violated Regularity: KKT conditions do not hold at a point that appears optimal. | Failure of constraint qualifications (e.g., the LICQ). | Check if the gradients of the active constraints at the point are linearly independent. | Reformulate the constraints to ensure linear independence or use numerical methods less sensitive to CQ failures, such as primal-dual interior point methods [28] [31]. |
| Numerical Instability: Difficulty solving the stationarity conditions due to ill-conditioning. | The problem may be poorly scaled, or the solution may lie very close to the constraint boundary. | Evaluate the condition number of the Hessian of the Lagrangian. | Implement a primal-dual interior point method that follows the "central path," keeping iterates in the interior and improving numerical stability [31]. |
| Trivial Multipliers: All Lagrange multipliers (μ) for inequality constraints are zero at the suspected solution. | No inequality constraints are active, meaning the solution is an unconstrained minimum inside the feasible region. | Check the values of ( g_i(x^*) ). If all are strictly negative, constraints are inactive. | Verify the unconstrained optimum. If it is feasible, the constraints are redundant and can be disregarded for determining the solution [28] [29]. |
Experimental Protocol: Identifying Active Constraints via KKT Analysis
This protocol provides a systematic methodology for empirically verifying the Karush-Kuhn-Tucker conditions in a numerical optimization experiment, a common task in evolutionary constrained optimization research.
1. Objective To verify whether a candidate solution ( x^* ) obtained from a constrained optimization algorithm satisfies the KKT conditions and to correctly identify the set of active constraints.
2. Materials and Computational Environment
- Software: A numerical computing environment (e.g., MATLAB, Python with NumPy/SciPy).
- Algorithm: A constrained optimization solver (e.g., an Evolutionary Algorithm with constraint-handling technique, fmincon in MATLAB, or scipy.optimize.minimize).
- Problem Definition: The objective function ( f(x) ) and constraint functions ( gi(x) ) and ( hj(x) ) must be explicitly defined and differentiable.
3. Procedure 1. Obtain a Candidate Solution: Run your chosen optimization algorithm on the problem to obtain a proposed solution ( x^* ). 2. Verify Primal Feasibility: * Calculate the values of all constraints at ( x^* ). * For inequality constraints: Confirm ( gi(x^*) \leq 0 ) for all ( i ). * For equality constraints: Confirm ( hj(x^) = 0 ) for all ( j ). * *If primal feasibility is violated, the point is not a candidate optimum. 3. Identify Active Inequality Constraints: * The set of active inequality constraints ( A ) is defined as ( A = { i \mid gi(x^*) = 0 } ). * All equality constraints are considered active by definition. 4. Check Linear Independence of Active Constraints: * Compute the gradients ( \nabla gi(x^) ) for all ( i \in A ) and ( \nabla h_j(x^) ) for all ( j ). * Verify that this set of gradient vectors is linearly independent. This is a common Constraint Qualification (CQ). If this fails, the KKT conditions may not be necessary at ( x^* ). 5. Form and Solve the KKT System: * Construct the Lagrangian: ( L(x, \mu, \lambda) = f(x) + \sumi \mui gi(x) + \sumj \lambdaj hj(x) ). * Write the stationarity condition: ( \nablax L(x^*, \mu, \lambda) = \nabla f(x^*) + \sumi \mui \nabla gi(x^) + \sum_j \lambda_j \nabla h_j(x^) = 0 ). This is a system of linear equations with variables ( \mu ) and ( \lambda ). * Solve this system for the Lagrange multipliers. 6. Verify Dual Feasibility and Complementary Slackness: * Dual Feasibility: Check that ( \mui \geq 0 ) for all inequality constraints. * Complementary Slackness: Confirm that ( \mui g_i(x^*) = 0 ) holds for all inequality constraints. This is automatically satisfied if multipliers for inactive constraints are zero.
4. Expected Results If all steps are completed successfully—primal and dual feasibility are satisfied, the stationarity condition holds, and complementary slackness is met—then the candidate solution ( x^* ) is a KKT point and a strong candidate for a local (or global, for convex problems) optimum.
5. Visualization of KKT Verification Logic The workflow for the experimental protocol described above can be logically represented by the following decision tree:
Research Reagent Solutions: Key Components for KKT Experiments
| Item Name | Function / Role in Experiment | Technical Specifications |
|---|---|---|
| Analytical Gradient Function | Provides exact first-derivative information for the objective and constraints, essential for forming the stationarity condition. | Must output ( \nabla f(x) ), ( \nabla gi(x) ), and ( \nabla hj(x) ) as vectors/matrices. Symbolic differentiation tools are ideal. |
| Lagrangian Formulation | The core function that combines the objective and constraints into a single unconstrained-looking function, incorporating the Lagrange multipliers. | ( L(x, \mu, \lambda) = f(x) + \sumi \mui gi(x) + \sumj \lambdaj hj(x) ) [28]. |
| Linear System Solver | A numerical routine to solve the system of equations arising from the stationarity condition ( \nabla_x L = 0 ) for the multiplier values. | Should be robust to ill-conditioning (e.g., LU decomposition, QR factorization). |
| Constraint Qualification Check | A procedure to verify that the gradients of active constraints are linearly independent, ensuring the necessity of the KKT conditions. | Algorithm to compute the rank of the matrix formed by ( \nabla gi(x^*) ) and ( \nabla hj(x^*) ). |
| Primal-Dual Interior Point Solver | An optimization algorithm that naturally generates sequences of primal variables and Lagrange multipliers, useful for benchmarking and validation. | Configured to follow the central path, providing both the solution and valid multipliers [31]. |
Advanced Methodologies for Leveraging Infeasible Solutions in Evolutionary Algorithms
Multi-Stage and Multi-Population Evolutionary Frameworks
Frequently Asked Questions (FAQs)
1. What does "infeasible solution" mean in the context of evolutionary optimization? An infeasible solution is a candidate solution proposed by the evolutionary algorithm that violates one or more of the problem's constraints. In a constrained optimization problem, the goal is to find a solution that not only optimizes an objective function (e.g., minimizes cost or maximizes efficacy) but also satisfies all given limitations, such as budgetary caps, resource capacity, or physical laws. When an algorithm produces an infeasible solution, it is not a valid answer to the problem as posed [1] [2].
2. What are the first steps I should take when my model is consistently infeasible? The first steps involve verifying the correctness of your model and data [1].
- Check Input Data: Perform thorough sanity checks on your input data. Inaccuracies, such as overpromising client commitments beyond your actual production capacity, are a common source of infeasibility [1].
- Review Model Formulation: Check for simple coding errors, including incorrect variable types, indexing mistakes, erroneous bounds, or using an equality constraint where an inequality would be more appropriate. It is highly recommended to start with an algebraic formulation of your model before coding to simplify verification [1].
3. What is an IIS and how can it help me? An IIS (Irreducible Inconsistent Subsystem or Irreducible Infeasible Set) is a powerful tool provided by solvers like Gurobi, CPLEX, and XPRESS. An IIS is a minimal subset of your model's constraints and variable bounds that is itself infeasible. If any single constraint or bound is removed from this subset, the subsystem becomes feasible. Analyzing the IIS helps you pinpoint the specific set of conflicting rules causing the infeasibility, saving considerable time in debugging large models [1] [2].
4. What are slack variables and the penalty method? This is a widely used strategy to manage infeasibility by softening hard constraints [1] [2].
- Slack Variables: A slack variable is added to a constraint, effectively allowing it to be "violated" by a certain amount.
- Penalty Method: The violation of the slack variable is then penalized in the objective function. The optimizer must then balance the original goal (e.g., minimizing cost) with the new goal of minimizing constraint violations. This approach often reflects real-world scenarios where some constraints can be bent at a cost (e.g., hiring temporary workers to overcome a labor shortage) [1].
5. How does the Boundary Update (BU) method work? The Boundary Update method is an implicit constraint handling technique that dynamically adjusts the lower and upper bounds of decision variables during the optimization process. It uses the problem's constraints to iteratively cut away portions of the infeasible search space, thereby guiding the algorithm toward the feasible region more quickly. However, this twisting of the search space can make the optimization problem more challenging. To counter this, switching mechanisms can be implemented to revert to the original problem landscape once the feasible region is found [32].
6. What is a Random Key Genetic Algorithm and how does it handle constraints? A Random Key Genetic Algorithm (RKGA) is a variant that ensures feasibility through a specialized decoding function. In an RKGA, chromosomes are encoded as vectors of real numbers (random keys). A decoding function is then designed to map any given chromosome to a feasible solution to the original problem. Because the decoder guarantees feasibility, the evolutionary algorithm operates without ever evaluating an infeasible solution. Designing this decoder is problem-specific but is often superior to penalty-based methods when achievable [33].
Troubleshooting Guides
Guide 1: Diagnosing and Resolving Infeasibility in Optimization Models
This guide outlines a systematic workflow for handling infeasible models. The process begins when a solver returns an infeasible status.
Diagram 1: A systematic workflow for diagnosing and resolving model infeasibility.
Step 1: Initial Verification Before deep diving, confirm the basics. Manually check your input data for accuracy and review your model's code for simple errors. A known feasible solution can be input into the model to see if it is correctly recognized as feasible [1].
Step 2: Identify the Core Conflict Use your solver's built-in tool to compute the Irreducible Inconsistent Subsystem (IIS). This report is the most direct way to identify the minimal set of constraints that are mutually exclusive [1] [2].
Step 3: Apply a Resolution Strategy Based on the IIS analysis, choose a resolution path:
- Model Reformulation: If the IIS reveals a modeling error (e.g., an incorrect sign or an overly restrictive bound), correct the formulation directly [1] [2].
- Slack Variables and Penalization: If the constraints are correct but too rigid, introduce slack variables. This transforms hard constraints into soft constraints, making the model feasible by construction and guiding the solver toward a solution that minimizes both the original objective and the constraint violations [1] [2].
- Constraint Prioritization: For complex models, assign priority levels to different constraints. During the resolution process, the solver can then relax lower-priority constraints first. This can be implemented by setting different penalty weights for the slack variables of different constraints [2].
Guide 2: Implementing a Hybrid Boundary Update Framework
This guide provides a methodology for implementing a multi-stage framework that uses the Boundary Update method to quickly find feasibility, then switches to a standard optimization process.
Experimental Protocol
- Objective: To enhance the convergence speed of evolutionary algorithms on constrained problems by rapidly locating the feasible region.
- Algorithms: This framework can be coupled with any evolutionary algorithm (e.g., Genetic Algorithm, Particle Swarm Optimization) for both single and multi-objective problems [32].
- Core Mechanism: The BU method is an implicit constraint handling technique that iteratively updates the bounds of decision variables to cut off infeasible regions of the search space [32].
- Key Innovation (Switching Mechanism): Since continuous BU can distort the search space, two switching thresholds are proposed to transition the optimization process back to the original problem landscape [32].
Diagram 2: A two-stage optimization framework using the Boundary Update method.
Detailed Methodology:
- Initialization: Start with a population of randomly generated individuals within the original variable bounds [34] [35].
- Stage 1 (BU Phase):
- Evaluation: Calculate the fitness and constraint violation for each individual [32].
- Boundary Update: Use the constraints to calculate new, tighter bounds for the decision variables. This reduces the available search space, cutting away infeasible regions [32].
- Evolution: Apply standard evolutionary operators (selection, crossover, mutation) within the updated bounds to create a new generation [36] [35].
- Switching Condition Check: After each generation, evaluate one of two conditions [32]:
- Hybrid-cvtol: Switch when the total constraint violation across the entire population reaches zero.
- Hybrid-ftol: Switch when the improvement in the objective function value stalls for a predefined number of generations.
- Stage 2 (Standard EA Phase): Once the switching condition is met, disable the BU method. Continue the evolutionary optimization using the original, untransformed search space and a standard constraint handling technique (e.g., feasibility rules) until the termination condition is met [32].
Research Reagent Solutions
The following table details key algorithmic components and their functions in implementing advanced constrained evolutionary frameworks.
| Research Reagent | Function in the Experimental Framework |
|---|---|
| Boundary Update (BU) Method | An implicit constraint handling technique that dynamically tightens variable bounds to steer the population toward the feasible region [32]. |
| Switching Mechanism (Hybrid-cvtol/ftol) | A critical control that transitions the algorithm from the distorted BU landscape back to the original problem space to facilitate better convergence [32]. |
| Slack Variables with Penalty Weights | A explicit method to soften hard constraints, allowing controlled violations that are penalized in the objective function, thus ensuring feasibility [1] [2]. |
| IIS (Irreducible Inconsistent Subsystem) Analyzer | A diagnostic tool within mathematical solvers that identifies the minimal set of conflicting constraints, invaluable for model debugging [1] [2]. |
| Feasibility Rules | A explicit constraint handling method often used in tandem with BU; it prioritizes selection of feasible solutions over infeasible ones [32]. |
The following table summarizes performance comparisons of constraint handling methods as reported in the literature.
| Method / Algorithm | Key Performance Findings | Comparative Basis |
|---|---|---|
| Improved PSO with Sparse Penalty [37] | Average value increased by at least 15x on single-peak test functions; always found global optimum on multi-peak functions. | Compared to 3 other PSO algorithms on 6 test functions. |
| Hybrid BU-Switching Method [32] | Significantly boosted convergence speed and found better solutions for constrained problems. | Benchmarked against EA with and without BU over the entire search process. |
| Improved PSO for Image Enhancement [37] | Performance indicators saw at least a 5% increase; algorithm running time increased by a minimum of 15%. | Compared to other evolutionary algorithms for contrast enhancement on multiple datasets. |
Adaptive Penalty Functions with Constraint-Specific Weighting
This technical support resource provides troubleshooting guides and detailed methodologies for researchers implementing adaptive penalty functions in constrained evolutionary optimization.
Troubleshooting Guide: Frequently Asked Questions
FAQ 1: My optimization converges to an infeasible solution even with an adaptive penalty. What could be wrong? This often occurs when the penalty method fails to effectively balance the objective function and constraints. The adaptive penalty method (APM) is designed to behave like a primal-dual active set method as the solution residual decreases, ensuring exact imposition of constraints at the limit [38]. Check if your penalty parameter is adapting correctly using the auxiliary problem at each iteration. Also, verify that your method transitions properly from exploring infeasible regions to exactly enforcing constraints as the solution converges.
FAQ 2: How do I determine appropriate initial weights for constraint-specific weighting?
There's no universal value, as appropriate weights are problem-dependent. A recommended approach is to implement a standardization procedure similar to that used in the ECO-HCT algorithm: calculate the maximum constraint violation for each constraint in the initial population (G_max,j = max_i=1,…,NP(G_j(x→))), then use these values to normalize all constraints so they contribute equally to the total penalty [39]. This prevents any single constraint from dominating due to scale differences.
FAQ 3: When should I use a hybrid constraint-handling technique versus a pure penalty method? Consider a hybrid approach when dealing with complex problems where the population may encounter different situations during evolution. Research shows that classifying the population state into three categories—infeasible (far from feasible region), semi-feasible (near boundary), and feasible (inside region)—then applying different constraint-handling techniques for each situation can significantly improve performance [39]. Pure penalty methods may struggle with this diversity of scenarios.
FAQ 4: How can I prevent my algorithm from getting stuck in local optima in the infeasible region? Implement a criterion for detecting local optima stagnation and a restart mechanism. The ECO-HCT method proposes specifically this approach: when the population is judged to be stuck in a local optimum in the infeasible region, a simple restart mechanism helps the population escape and improves the ability to solve complex constrained optimization problems [39].
FAQ 5: What is the most efficient way to handle box constraints with adaptive penalties? Never assume this is trivial. Research emphasizes that dealing with solutions generated outside the domain, even for simple box constraints, significantly impacts algorithm performance, disruptiveness, and population diversity [11]. Always fully specify and document your boundary-handling strategy to ensure reproducible results. The importance of this choice grows with problem dimensionality.
Experimental Protocols & Implementation
Standardized Constraint Violation Calculation
For meaningful constraint-specific weighting, consistently calculate constraint violations using this established methodology [39]:
Inequality constraints: G_j(x→) = max(0, g_j(x→)) for j = 1,…,q
Equality constraints: G_j(x→) = max(0, |h_j(x→)| - δ) for j = q+1,…,m
where δ is a small positive tolerance value (typically 0.0001) to relax equality constraints.
Total violation: G(x→) = ∑_{j=1}^m G_j(x→)
Standardized violation (recommended): G(x→) = 1/m ∑_{j=1}^m G_j(x→)/G_max,j where G_max,j = max_i=1,…,NP(G_j(x→))
Implementing the Adaptive Penalty Method (APM)
The APM can be considered a quasi-Newton method where the Jacobian is approximated using a penalty parameter [38]. Follow this implementation protocol:
Step 1: Initialize - Choose initial penalty parameters λ_i^0 for each constraint, typically starting with small positive values. Initialize the solution estimate x^0.
Step 2: Solve the penalized problem - At iteration k, minimize f(x) + ∑ λ_i^k * G_i(x) where G_i(x) represents the violation of the i-th constraint.
Step 3: Update penalties adaptively - Solve an auxiliary problem to determine new penalty parameters λ_i^{k+1} that approximate the active set method behavior.
Step 4: Check convergence - Stop when constraint violations are below tolerance AND solution changes are minimal. Otherwise, return to Step 2.
The key innovation of APM is that the penalty parameter varies spatially and is updated at each iteration based on the auxiliary problem, enabling it to transition to exact constraint enforcement [38].
Hybrid Constraint-Handling Technique (HCT) Protocol
The HCT approach classifies population status and applies situation-specific methods [39]:
Step 1: Population assessment - Each generation, calculate the proportion of feasible solutions in the population.
Step 2: Situation classification:
- Infeasible situation: Population far from feasible region (very few or no feasible solutions)
- Semi-feasible situation: Population near feasibility boundary (moderate feasible solutions)
- Feasible situation: Population mainly inside feasible region (many feasible solutions)
Step 3: Method application:
- Infeasible situation: Use elite replacement strategy to accumulate experience
- Semi-feasible situation: Balance objective and constraints using feasibility rules
- Feasible situation: Focus on objective optimization while maintaining feasibility
Step 4: Restart if needed - If population is stuck in local optimum in infeasible region, trigger restart mechanism
Comparative Performance Data
Table 1: Constraint-Handling Method Performance Comparison
| Method | Key Mechanism | Best For | Implementation Complexity | Notable Advantages |
|---|---|---|---|---|
| Adaptive Penalty Method (APM) [38] | Spatially varying penalty updated via auxiliary problem | Problems needing exact constraint enforcement | Medium | Transitions to active set method; combines ease of implementation with exact constraint imposition |
| Hybrid Constraint Technique (HCT) [39] | Population situation detection with different methods for each | Complex problems with varying feasibility characteristics | High | Adapts to population state; uses evolution information effectively |
| Boundary Update (BU) Method [40] | Iteratively updates variable bounds to cut infeasible space | Problems where finding feasible region is challenging | Medium | Finds feasible region faster; can be combined with switching mechanisms |
| Feasibility Rules [39] | Prefers feasible over infeasible solutions | Problems with moderate constraint complexity | Low | Simple to implement; no parameter tuning needed |
| Switching Method | Trigger Condition | Performance Benefit | Potential Limitations |
|---|---|---|---|
| Hybrid-cvtol | Constraint violations reach zero | Maintains feasibility after switching | May switch too early if feasibility is fragile |
| Hybrid-ftol | Objective space unchanged for specified generations | Continues refinement after BU phase | May delay switching if objective stagnates for other reasons |
Research Reagent Solutions
Table 3: Essential Computational Tools for Constrained Optimization Research
| Tool/Component | Function | Implementation Notes |
|---|---|---|
| Standardized Constraint Violation Metric | Enables fair constraint comparison and weighting | Essential for constraint-specific weighting; use normalization [39] |
| Population Feasibility Assessor | Classifies population situation (infeasible/semi-feasible/feasible) | Critical for hybrid methods; determines which constraint-handling technique to apply [39] |
| Penalty Parameter Update Algorithm | Adapts penalty weights based on current solution state | Core of APM; uses auxiliary problem to determine optimal parameters [38] |
| Boundary Update Mechanism | Dynamically adjusts variable bounds to exclude infeasible regions | BU method cuts infeasible search space over iterations [40] |
| Restart Trigger Criterion | Detects population stagnation in local optima | Helps escape infeasible region local optima; improves complex problem solving [39] |
Workflow Visualization
Multi-Task Optimization with Constrained and Unconstrained Tasks
This technical support center is designed for researchers and professionals working with Multi-Task Optimization (MTO) frameworks that combine constrained and unconstrained tasks. These advanced optimization architectures are particularly valuable for solving Complex Constrained Optimization Problems (COPs) and Constrained Multi-Objective Optimization Problems (CMOPs) prevalent in engineering design, resource allocation, and drug development. The core challenge in these systems involves strategically handling infeasible solutions to maintain population diversity while driving convergence toward optimal, feasible regions. This guide addresses frequent experimental difficulties through targeted troubleshooting methodologies and evidence-based solutions drawn from current evolutionary computation research.
Frequently Asked Questions & Troubleshooting Guides
FAQ 1: How can I prevent negative transfer between constrained and unconstrained tasks in multi-task optimization frameworks?
Problem Description: Negative transfer occurs when knowledge sharing between optimization tasks detrimentally impacts performance, often causing population convergence to suboptimal regions or reduced constraint satisfaction rates.
Diagnosis Methodology:
- Monitor task interference by tracking population fitness segregation weekly
- Calculate Negative Transfer Index (NTI):
NTI = (Perf_isolated - Perf_shared)/Perf_isolated - Analyze cross-task solution migration patterns using similarity measures in decision space
Resolution Protocols:
Table 1: Solutions for Mitigating Negative Transfer
| Approach | Mechanism | Implementation Example | Expected Outcome |
|---|---|---|---|
| Weak Cooperation Model | Limited offspring sharing between populations | Share only generated offspring in initial stages [41] | Reduces harmful interaction while maintaining beneficial transfer |
| Stage-Specific Collaboration | Different cooperation strategies per evolutionary stage | Stage 1: Weak cooperation; Stage 2: Strong collaboration [41] | Aligns information exchange with evolutionary needs |
| Adaptive Resource Allocation | Dynamic allocation of computational resources based on task performance | Balance function evaluations between main and auxiliary populations [41] | Prevents dominant tasks from starving others |
FAQ 2: What strategies effectively balance constraint handling with objective optimization across tasks?
Problem Description: Improper balancing leads to premature convergence to feasible but suboptimal solutions or populations trapped in infeasible regions with excellent objective values.
Diagnosis Methodology:
- Compute feasible-to-infeasible ratio weekly:
Feasible Ratio = N_feasible/N_total - Track population progression toward Constrained Pareto Front (CPF) using generational distance metrics
- Monitor diversity loss using spread indicator or similar diversity metrics
Resolution Protocols:
Table 2: Constraint-Objective Balancing Techniques
| Technique | Key Principle | Parameterization | Application Context |
|---|---|---|---|
| Multi-Stage Optimization | Separate exploration and exploitation phases [41] [42] | Stage 1: Explore UPF; Stage 2: Approach CPF | CMOPs with complex feasible regions |
| Adaptive Penalty Functions | Dynamic constraint weighting based on violation severity [26] | Weights updated per generation based on constraint significance | Single-objective COPs and CMOPs |
| Constraint Relaxation | Progressive tightening of constraints [42] [16] | Epsilon method gradually reducing tolerance | Problems with disconnected feasible regions |
| Dual-Population Strategy | Simultaneous exploration of feasible/infeasible regions [24] | Main population (feasibility), Auxiliary (infeasible diversity) | CMOPs with small feasible regions |
FAQ 3: How can I maintain population diversity when handling complex constraints?
Problem Description: Complex constraints (especially nonlinear and discontinuous) often cause diversity loss, limiting exploration of potential feasible regions and resulting in incomplete Pareto front approximation.
Diagnosis Methodology:
- Calculate population spread metric every 5 generations
- Monitor niche counts and solution distribution across objective space
- Track recurrence of identical solutions in consecutive generations
Resolution Protocols:
Table 3: Diversity Maintenance Strategies for Constrained Optimization
| Strategy | Implementation | Key Parameters | Effectiveness Metric |
|---|---|---|---|
| Global Diversity Maintenance | Preserve well-distributed infeasible solutions [24] | Number of weight vectors, selection ratio | Spread indicator, Feasible region coverage |
| Dynamic Archiving | Adaptive preservation of infeasible solutions based on population diversity [26] | Archive size threshold, Diversity fluctuation tolerance | Archive quality index |
| Angle-Based Selection | Diversity-first selection based on angular distribution [16] | Niche radius, Angle threshold | Distribution uniformity metric |
| Dual-Arcive Mechanisms | Separate archives for feasible and infeasible solutions [42] [16] | Archive exchange frequency, Cooperation strategy | IGD metric, HV metric |
Experimental Protocol:
- Initialize population with Latin Hypercube Sampling for even distribution
- For each generation:
- Apply variation operators (crossover, mutation)
- Evaluate objectives and constraints
- Calculate constraint violations using:
CV(x) = Σmax(0, g_i(x)) + Σ|h_j(x) - δ|[41] [24] - Apply diversity-preserving selection:
- Partition objective space using weight vectors [24]
- Select best infeasible solutions from each subregion
- Combine with feasible solutions using balanced ratio
- Update dynamic archive based on diversity fluctuations [26]
- Terminate after 100,000 function evaluations or convergence stabilization
FAQ 4: What are efficient methods for reducing computational overhead in complex constrained optimization?
Problem Description: Hydraulic simulations, finite element analysis, or molecular dynamics evaluations in optimization loops create prohibitive computational costs, limiting algorithm application to real-world problems.
Diagnosis Methodology:
- Profile computational time by function component
- Track feasibility classification accuracy vs. computational cost
- Monitor resource allocation efficiency
Resolution Protocols:
Table 4: Computational Efficiency Improvement Methods
| Method | Approach | Accuracy Trade-off | Implementation Complexity |
|---|---|---|---|
| Feasibility Predictor Models (FPM) | ML classifiers to pre-filter solutions [43] | Medium (85-95% accuracy) | Medium (requires training data) |
| Boundary Update (BU) Methods | Implicit constraint handling reducing search space [40] | Low (minimal impact) | Low (direct implementation) |
| Switching BU Mechanisms | Transition to standard optimization after feasible region located [40] | Low (preserves accuracy) | Medium (threshold tuning required) |
| Surrogate-Assisted Evolution | Replacement of expensive simulations with metamodels [43] | High (accuracy varies) | High (model training & management) |
Experimental Protocol for FPM Integration:
- Initial Phase (Offline Training):
- Generate diverse solutions using space-filling design
- Run full simulation/evaluation to label solutions as feasible/infeasible
- Train classifier (XGBoost, Random Forest) on feasibility prediction
- Validate classifier accuracy with cross-validation
Optimization Phase (Online Application):
- For each candidate solution:
- First, evaluate using trained FPM
- If predicted infeasible with high confidence (>95%), discard without simulation
- If predicted feasible or uncertain, proceed with full simulation
- Retrain FPM periodically with new data (every 1000 evaluations)
- For each candidate solution:
Performance Validation:
- Compare results with full simulation approach
- Verify no significant degradation in solution quality
- Calculate computational savings:
Savings = (N_filtered/N_total) * 100
The Scientist's Toolkit: Essential Research Reagents
Table 5: Key Algorithmic Components for Multi-Task Constrained Optimization
| Component | Function | Implementation Notes | Validation Metrics |
|---|---|---|---|
| Constrained Dominance Principle (CDP) | Primary constraint handling mechanism [41] [24] | Feasible solutions dominate infeasible; equal feasibility uses Pareto dominance | Feasibility rate, Convergence speed |
| Epsilon Constraint Method | Controlled constraint relaxation [41] | Gradually decrease ε from high value to zero across generations | Transition smoothness, Feasible region discovery |
| Multi-Task Framework | Coordinated optimization across related problems [41] | Main population + auxiliary populations with different CHTs | Cross-task knowledge transfer efficiency |
| Adaptive Penalty Function | Dynamic constraint weighting [26] | Weights based on constraint violation severity and significance | Balance between objectives and constraints |
| Feasibility Predictor Model | Computational expense reduction [43] | Machine learning classifier to pre-filter solutions | Prediction accuracy, Computational savings |
| Diversity Maintenance Mechanism | Preservation of exploration capability [24] | Weight vector-based selection from subregions | Spread indicator, Feasible region coverage |
| Boundary Update Method | Implicit constraint handling [40] | Dynamic variable bound adjustment using constraints | Feasible region localization speed |
Advanced Methodologies for Complex Cases
Integrated Multi-Stage Multi-Task Framework
For particularly challenging CMOPs with discontinuous feasible regions or strong objective-constraint conflicts, consider implementing a comprehensive multi-stage multi-task framework:
Stage 1 Protocol:
- Task Combination: Main population (CDP) + Auxiliary population (unconstrained)
- Collaboration: Weak cooperation with only offspring sharing
- Objective: Explore Unconstrained Pareto Front (UPF) and discover feasible regions
- Termination Condition: 40% of function evaluations or feasible ratio >50%
Stage 2 Protocol:
- Task Combination: Main population (CDP) + Auxiliary population (epsilon constraint)
- Collaboration: Strong collaboration with full solution exchange
- Objective: Approach CPF from both feasible and infeasible directions
- Termination Condition: Remaining function evaluations
Validation Metrics:
- Inverted Generational Distance (IGD) - Comprehensive performance assessment
- Hypervolume (HV) - Convergence and diversity combination
- Feasible Ratio - Constraint satisfaction effectiveness
- Spread - Diversity maintenance capability
This technical support center provides methodologies grounded in current constrained optimization research. Implement these protocols systematically, validate against appropriate benchmarks, and adapt parameters to your specific problem characteristics for optimal results in handling infeasible solutions within multi-task optimization frameworks.
Dynamic Archiving Strategies for Maintaining Promising Infeasible Solutions
Constrained optimization problems are ubiquitous in real-world research and industry, from drug development to logistics. A significant challenge arises when an optimization algorithm encounters infeasible solutions—those that violate one or more problem constraints. Historically, these solutions were discarded. However, advanced research has demonstrated that promising infeasible solutions contain valuable information about the problem landscape. When maintained through dynamic archiving strategies, they can guide the search process through infeasible regions toward optimal feasible areas, ultimately improving convergence and diversity [44] [45].
This technical support center addresses the practical implementation of these strategies, providing researchers with troubleshooting guides and FAQs to navigate common experimental challenges. The content is framed within a broader thesis that argues for the strategic preservation and utilization of infeasible solutions as a critical component of modern constrained evolutionary optimization.
Core Concepts: FAQs on Infeasible Solutions and Archiving
FAQ 1: What constitutes a "promising" infeasible solution?
A promising infeasible solution is one that, despite violating some constraints, exhibits excellent objective function values. Its promise is typically quantified by its constraint violation (CV) and its proximity to the feasible region boundary. In many algorithms, a solution is considered promising if its CV is below a certain dynamic threshold, ε, allowing it to provide evolutionary directions toward potential feasible regions [45].
FAQ 2: Why do traditional algorithms struggle with infeasible solutions? Algorithms based solely on the Constrained Dominance Principle (CDP), like standard NSGA-II, prioritize feasibility above all else. They prefer any feasible solution over any infeasible solution. When confronting problems with disconnected or narrow feasible regions blocked by large infeasible areas, this approach can cause the population to converge prematurely to the first feasible region it finds, often missing the globally optimal solution [45].
FAQ 3: What is the fundamental principle behind dynamic archiving? Dynamic archiving strategically maintains a separate population (an archive) of promising infeasible solutions. This archive is not static; it evolves based on the algorithm's current state. The key principle is to use these archived solutions to provide supplementary evolutionary directions, helping the main population navigate around infeasible barriers and discover hidden or distant feasible regions that would otherwise be inaccessible [45].
Troubleshooting Common Experimental Issues
Issue 1: Algorithm Converging to Local Feasible Optima
- Problem Description: The optimization run consistently gets stuck in a local feasible region, failing to reach the true Constrained Pareto Front (CPF), especially in Type-III and Type-IV problems where the CPF is separated from the Unconstrained Pareto Front (UPF) [45].
- Diagnosis: This is a classic sign of over-emphasizing constraint satisfaction too early in the evolutionary process. The main population lacks the diversity or directional information to cross large infeasible regions.
- Solution:
- Implement a Dual-Population Approach: Maintain two co-evolving populations: a main population seeking the CPF and an auxiliary population that dynamically archives promising infeasible solutions near the constraint boundaries [45].
- Dynamic Constraint Boundary: Instead of a fixed CV threshold, use a dynamically changing
εvalue for the auxiliary archive. Start with a more relaxed (higher)εto allow exploration and gradually tighten it to guide the population toward the true feasible region [45]. - Knowledge Transfer: Allow periodic information exchange (e.g., through crossover) between the main population and the auxiliary archive. The infeasible solutions in the archive can provide genetic material to help the main population "jump" across infeasible gaps.
The following workflow illustrates how a dual-population algorithm with dynamic archiving interacts to solve a constrained problem.
Issue 2: Numerical Infeasibilities in Computationally Expensive Models
- Problem Description: The solver (e.g., CPLEX, Gurobi) reports a model as "infeasible" even when a feasible solution is known to exist, or it finds solutions but with poor quality metrics indicating numerical instability [46] [47].
- Diagnosis: This is often a numerical precision issue, not a true model infeasibility. It can be caused by extremely large or small coefficients in the objective function or constraints, overwhelming the solver's default feasibility tolerance (often around 1e-6) [46] [47].
- Solution:
- Scale Your Model: Revise and clean up the model coefficients to bring them within a consistent order of magnitude. The matrix coefficient range should not span too many orders of magnitude (e.g., from 1e-07 to 1e+08) [46] [47].
- Adjust Solver Parameters: Increase the
NumericFocusparameter to instruct the solver to pay more attention to numerical issues. For Gurobi, values of 1, 2, or 3 offer increasing levels of numerical caution [47]. - Tighten Tolerances Cautiously: You can try decreasing the
FeasibilityTolparameter, but this should be a last resort after scaling, as it increases computational cost and may not resolve the root cause [47]. - Use the Conflict Refiner: If the model is truly infeasible, use the solver's built-in conflict refiner to identify the minimal set of constraints causing the infeasibility, helping you debug the model logic [46].
Table 1: Troubleshooting Numerical Instabilities in Optimization Solvers
| Symptom | Potential Cause | Corrective Action | Solver Parameter (e.g., Gurobi) |
|---|---|---|---|
| "Infeasible" result for a known feasible problem. | Extreme coefficient ranges; low precision. | Scale model coefficients; increase numerical emphasis. | Method=2 (Barrier), NumericFocus=2 |
| Large objective residuals or constraint violations in solution. | Numerical difficulties during iterations. | Enable extreme numerical caution; check scaling. | BarrierConvTol, FeasibilityTol |
| Solver performance deteriorates with small model changes. | Ill-conditioned basis matrices. | Use a different algorithm; focus on model reformulation. | Crossover, Method=1 (Simplex) |
| "Unstable" or "suspicious" basis status in log. | Rounding errors in linear algebra. | Prioritize stable bases with higher numeric focus. | NumericFocus=3 |
The Scientist's Toolkit: Essential Reagents and Methods
This section details the key components for constructing and experimenting with dynamic archiving strategies.
Table 2: Research Reagent Solutions for Dynamic Archiving Experiments
| Reagent / Component | Function & Purpose | Implementation Example |
|---|---|---|
| Differential Evolution (DE) Algorithm | Serves as the core search engine for the population. Its mutation and crossover strategies are effective for exploring complex landscapes. | A multi-operator DE can be used, employing strategies like DE/rand/1 and DE/current-to-best to balance exploration and exploitation [44]. |
| Constraint Handling Technique (CHT) | Manages the trade-off between objective fitness and constraint violation. | Dynamic Constraint Boundary Method: The threshold ε for accepting promising infeasible solutions is adjusted based on the current generation or population feasibility ratio [45]. |
| Auxiliary Archive Population | The dynamic archive that stores and maintains promising infeasible solutions throughout the evolutionary process. | A separate population that is updated based on a relaxed ε-level dominance, ensuring it holds solutions that are near the feasible boundary [45]. |
| Knowledge Transfer Mechanism | Facilitates the exchange of information between the main and auxiliary populations. | Selects individuals from the auxiliary archive to periodically participate in the reproduction process of the main population, injecting useful genetic material [44]. |
| Performance Metrics | Quantifies the success of the algorithm for comparative analysis. | Mean Ideal Distance (MID): Measures convergence. Hypervolume (HV): Measures both convergence and diversity. Feasibility Ratio (FR): Tracks the proportion of feasible solutions over time [44]. |
Experimental Protocol: Implementing a Dynamic Constrained Boundary Method (CDCBM)
The following is a detailed methodology for implementing a CDCBM, a state-of-the-art approach that leverages dynamic archiving [45].
Objective: To solve a Dynamic Constrained Optimization Problem (DCOP) where the feasible region may be disconnected or separated from the UPF by utilizing an auxiliary population to maintain promising infeasible solutions.
Workflow:
- Initialization:
- Initialize two populations: the Main Population (Popm) and the Auxiliary Archive (Popa).
- Set the initial dynamic constraint boundary
εto a relatively high value (e.g.,ε = 1.0). - Define the maximum number of generations (
max_gen).
Evaluation and Classification:
- For each individual in both
Pop_mandPop_a, evaluate the objective functions and calculate the total constraint violation (CV) using the formula: 'CV(x) = Σ(max(0, gj(x))) + Σ(max(0, |hj(x)| - δ))' whereδis a small tolerance for equality constraints (e.g., 1e-6) [45]. - Classify solutions in
Pop_aas "promising infeasible" ifCV < ε.
- For each individual in both
Auxiliary Population State Detection (Dynamic Update of ε):
- Every
Kgenerations, assess the state ofPop_a. - If
Pop_ais successfully providing diverse solutions that helpPop_mimprove, maintain or slowly decreaseε. - If
Pop_mis stagnating (no improvement in fitness over several generations), increaseεslightly to allowPop_ato explore a wider infeasible region and provide new evolutionary directions.
- Every
Population Evolution:
- Evolve Pop_m: Use standard constrained selection (e.g., modified CDP) that incorporates information from
Pop_a. The goal is to converge toward the CPF. - Evolve Pop_a: Select parents from the current
Pop_aand generate offspring. UpdatePop_abased on a relaxed dominance criterion that favors low CV and good objective values, using the currentεthreshold.
- Evolve Pop_m: Use standard constrained selection (e.g., modified CDP) that incorporates information from
Knowledge Transfer:
- At regular intervals (e.g., every 10 generations), select the best individuals from
Pop_a(lowest CV and best objectives) and allow them to compete for entry intoPop_mduring its environmental selection.
- At regular intervals (e.g., every 10 generations), select the best individuals from
Termination:
- Repeat steps 2-5 until the
max_genis reached or another termination criterion (e.g., stability of the hypervolume metric) is met.
- Repeat steps 2-5 until the
The logical relationship between the main components of the CDCBM algorithm and their co-evolution is summarized below.
Advanced FAQ: Navigating Complex Constrained Landscapes
FAQ 4: How do you set the initial value and adjustment rate for the dynamic constraint boundary (ε)?
The initial ε should be set to a value that allows the auxiliary archive to capture a meaningful number of infeasible solutions—often a fraction of the maximum CV observed in a random initial population. The adjustment rate is typically problem-dependent. A common strategy is to link it to the feasibility ratio of the main population: if the ratio remains low for a prolonged period, ε can be increased to encourage more exploration; if the ratio is high and the population is converging, ε can be decreased to refine the search [45].
FAQ 5: Can these strategies be applied to real-world, black-box optimization problems in drug development? Yes. In drug development, constraints can represent toxicity limits, solubility, or synthetic feasibility, while the objective is efficacy. The functions are often computational black-box simulators. Dynamic archiving is highly suitable here because it doesn't require gradient information. By maintaining a diverse archive of promising (even if initially infeasible) molecular designs, researchers can explore a wider chemical space and potentially discover novel compounds that can be slightly modified to meet all constraints and become viable drug candidates [44].
Co-Evolutionary Approaches for Feasible and Infeasible Region Exploration
Frequently Asked Questions (FAQs)
Q1: Why does my constrained optimization algorithm converge to a local optimum, missing better solutions in disconnected feasible regions?
A1: This common issue, known as premature convergence, often occurs because the algorithm lacks mechanisms to maintain population diversity and navigate complex constraint landscapes. In problems where the constrained Pareto front (CPF) is fragmented into multiple discrete segments, populations can become trapped in a single feasible region [48]. To address this, implement a dual-population co-evolutionary strategy [49] [48]. Maintain a main population that explores the feasible region (CPF) and an auxiliary population that explores the unconstrained Pareto front (UPF). When the main population stagnates, initiate a regional mating mechanism between the two populations. This injects diversity and helps the main population escape local optima by leveraging genetic material from the auxiliary population, effectively crossing infeasible barriers to discover other feasible regions [48].
Q2: How can I reduce the computational cost of evaluating objectives and constraints in expensive, high-fidelity simulations?
A2: For computationally expensive problems, such as those involving finite element analysis, surrogate-assisted evolution is the recommended approach [49]. Instead of directly using the simulation, construct cheap-to-evaluate surrogate models (e.g., Radial Basis Functions (RBF) or Kriging) to approximate each objective and constraint function. Within a co-evolutionary framework, these surrogates are dynamically updated. A promising strategy is to use one population to explore the entire search space (ignoring constraints via the surrogates) and another to focus on feasible regions. Their offspring are shared, and an adaptive selection strategy chooses the most promising samples for expensive, high-fidelity re-evaluation, dramatically reducing the number of function evaluations [49].
Q3: What is the benefit of explicitly maintaining infeasible solutions in my population?
A3: While it seems counter-intuitive, preserving "good" infeasible solutions is crucial for solving problems with narrow feasible regions or where the global optimum lies on a constraint boundary [14] [50]. Infeasible solutions close to the boundary contain valuable information about the direction toward feasibility and often have excellent objective values. A method known as Infeasibility Driven Evolutionary Algorithm (IDEA) explicitly ranks some marginally infeasible solutions higher than feasible ones, driving the population toward the constraint boundary from both feasible and infeasible sides [14]. Modern algorithms formalize this with a weak constraint–Pareto dominance relation, which prevents the premature elimination of infeasible solutions that have strong convergence or diversity potential [50].
Q4: My algorithm struggles with problems involving multiple, interacting constraints. How can I manage this complexity?
A4: Complex constraints can be decoupled using a co-evolutionary framework based on constraints decomposition [51]. This method decomposes the original problem into several simpler subproblems, each handled by a dedicated subpopulation. Specifically, a constrained multi-objective optimization problem (CMOP) with q constraints is broken down into q single-constraint multi-objective problems. These auxiliary subpopulations explore feasible regions from different angles, effectively mapping the constraint landscape. A main population then collects this valuable information to solve the original problem. A two-stage strategy and an evolutionary state detection mechanism can further optimize this process to avoid wasting resources on stagnant subpopulations [51].
Troubleshooting Guides
Problem: Population Diversity Collapse in Complex Feasible Regions
Symptoms: The population converges to a small, clustered area of the Pareto front, failing to cover all discrete segments. The rate of improvement in performance metrics stalls.
Diagnosis and Solution: This indicates insufficient population diversity when facing disconnected feasible regions. Implement a region-based diversity enhancement strategy [48].
- Step 1: Dynamic Operator Adjustment. Continuously monitor population convergence and diversity metrics. Dynamically adjust genetic operators (e.g., mutation rate) based on the real-time state of the population. Increase exploration when diversity drops.
- Step 2: Regional Mating. If the main population stagnates, activate a mating mechanism between the main and auxiliary populations. This produces offspring with a more uniform distribution, helping to bridge gaps between feasible regions.
- Step 3: Diversity-First Selection. For the auxiliary population, use a regional distribution index to assess individual diversity. During selection, prioritize individuals that improve the population's spread, even if their convergence is slightly worse.
Problem: Infeasible Solutions Overwhelm the Population
Symptoms: The algorithm fails to find a sufficient number of feasible solutions, or converges to an infeasible region with good objective values but high constraint violation.
Diagnosis and Solution: The balance between objective optimization and constraint satisfaction is lost. Implement a structured constraint handling technique (CHT) within your co-evolutionary framework.
- Step 1: Problem Classification. First, classify your problem. Analyze the objective function's characteristics. If it has a clear minimizing direction and correlates with constraints, it's a "simple objective" problem; otherwise, it's "complex" [20].
- Step 2: Apply Tailored CHT.
- For simple objectives: Use an objective-oriented CHT. Calculate a Knowledge Transfer Rate (KTR) indicator that quantifies the similarity between the objective and constraint violation. Use KTR to control how much the objective function guides the search toward feasibility [20].
- For complex objectives: Use a constraint-oriented CHT. This is a two-stage method:
- Stage A (Constraint-Driven): Focus solely on minimizing constraint violation to bring the population near feasible regions.
- Stage B (Hybrid-Driven): Once near feasibility, leverage both objective and constraint information to find the optimal feasible solution [20].
- Step 3: Archive Management. Maintain separate archives [50]. One archive performs unconstrained optimization, another enforces strict feasibility, and a third uses a weak constraint–Pareto dominance rule to preserve promising infeasible solutions. This ensures a balanced approach.
Problem: Prohibitive Computational Cost in Expensive Evaluations
Symptoms: The optimization process is unacceptably slow, as each evaluation of a candidate solution's objectives and constraints takes minutes or hours.
Diagnosis and Solution: The algorithm is performing too many direct, high-fidelity evaluations. Integrate data-driven surrogate models into the co-evolutionary process [49].
- Step 1: Surrogate Model Selection. Choose appropriate surrogate models. Radial Basis Functions (RBF) are often preferred for their accuracy and fast modeling speed. Build a separate surrogate for each objective and constraint function.
- Step 2: Co-Evolutionary Exploration Framework. Establish a framework where two populations co-evolve:
- Population A: Operates on the surrogate models without considering constraints, performing global exploration.
- Population B: Operates on the surrogates while focusing on feasible regions.
- Both populations share their offspring, creating a shared pool of candidate solutions.
- Step 3: Adaptive Infill Strategy. From the shared pool, select the most "promising" samples for actual high-fidelity evaluation. This selection should balance convergence (good objective values) and diversity (exploring new regions). The new data from these evaluations is then used to update the surrogate models, increasing their accuracy for the next iteration [49].
Experimental Protocols & Methodologies
This section provides detailed protocols for key experiments cited in the FAQs.
Protocol: Implementing a Dual-Population Co-Evolutionary Algorithm
Objective: To solve CMOPs with complex feasible regions by maintaining and coordinating two populations [48].
Methodology:
Initialization:
- Generate two populations: Main Population (PopM) and Auxiliary Population (PopA).
- Pop_M is initialized with a focus on feasibility.
- Pop_A is initialized without considering constraints.
- Set shared reference vectors to divide the objective space.
Co-Evolutionary Loop (Repeat for a maximum number of generations):
- Step A: Independent Evolution.
- Evolve PopM using a genetic algorithm (e.g., DE, GA) with a feasibility-based ranking method (e.g., CDP).
- Evolve PopA using a multi-objective algorithm (e.g., NSGA-II, RVEA) without considering constraints.
- Step B: State Detection & Coordination.
- Monitor the convergence and diversity of both populations.
- If PopM is stagnating, perform regional mating between PopM and PopA to create diversified offspring for PopM.
- If Pop_A is stagnating, apply a diversity-first selection strategy based on a regional distribution index.
- Step C: Environmental Selection.
- Select the next generation for each population from their combined parent and offspring pools, respecting their respective goals (feasibility for PopM, performance for PopA).
- Step A: Independent Evolution.
Termination:
- The final output is the set of non-dominated feasible solutions from Pop_M.
Protocol: Data-Driven Surrogate-Assisted Co-Evolution (DDCEE)
Objective: To solve computationally expensive CMOPs by reducing the number of true function evaluations via surrogate models [49].
Methodology:
Initial Design of Experiments (DoE):
- Use Latin Hypercube Sampling (LHS) to generate an initial set of decision vectors.
- Perform the expensive simulation to evaluate all objectives and constraints for these initial samples.
Surrogate Model Construction:
- Using all current data, construct one RBF surrogate model for each objective function and each constraint function.
Co-Evolutionary Exploration:
- Population C1: Optimizes the surrogate models of the objectives without considering constraints.
- Population C2: Optimizes the surrogate models with a focus on feasible regions (e.g., using CDP on the constraint surrogates).
- Both populations generate offspring, which are merged into a candidate pool.
Adaptive Selection of Promising Samples:
- From the candidate pool, select a pre-defined number of samples for expensive re-evaluation. The selection uses an infill criterion that considers both:
- Convergence: Predicted objective values from the surrogates.
- Diversity: Spatial distribution of the candidates in the objective space.
- Evaluate the selected samples using the true, expensive simulation.
- From the candidate pool, select a pre-defined number of samples for expensive re-evaluation. The selection uses an infill criterion that considers both:
Model Update and Iteration:
- Add the newly evaluated data to the training dataset.
- Update the RBF surrogate models with the enriched dataset.
- Repeat from Step 3 until the evaluation budget is exhausted.
Key Research Reagent Solutions
The following table details essential algorithmic "reagents" for constructing effective co-evolutionary experiments.
| Research Reagent | Function / Purpose | Key Considerations |
|---|---|---|
| Radial Basis Function (RBF) Networks [49] | Serves as a surrogate model to approximate expensive objective and constraint functions, drastically reducing computational cost. | Chosen for good accuracy and fast modeling speed. Requires a strategy for dynamic updates. |
| Dual-Population Framework [48] [51] | Provides the architectural backbone for separating concerns: one population for feasibility, one for objective performance. | Critical to define coordination mechanisms (e.g., mating, information sharing) between populations. |
| Weak Constraint–Pareto Dominance [50] | A selection rule that integrates feasibility and objective performance, preventing premature loss of valuable infeasible solutions. | Helps balance exploration (via infeasible solutions) and exploitation (via feasible ones). |
| Reference Vectors [49] [50] | Used to divide the objective space into subregions, aiding in the selection of diverse solutions and maintaining a uniform spread. | Essential for many-objective problems. Requires a method for generating uniform vectors. |
| Knowledge Transfer Rate (KTR) [20] | An indicator that quantifies the relationship between objective and constraints, guiding the transfer of knowledge between them. | Used in problems where the objective function can guide the search toward feasibility. |
| Regional Distribution Index [48] | A metric to assess individual diversity based on their location in the objective space, used for diversity-first selection. | Prevents diversity collapse and helps the population explore disconnected feasible regions. |
The table below summarizes key performance metrics reported for the co-evolutionary algorithms discussed in this guide, based on benchmark testing.
| Algorithm | Key Mechanism | Reported Performance (vs. State-of-the-Art) | Computational Efficiency |
|---|---|---|---|
| DDCEE [49] | Data-driven co-evolution with RBF surrogates | "More stable and impressive performance" on benchmark CMOPs and a structural engineering problem. | Significantly reduces expensive function evaluations. |
| DESCA [48] | Dual-population with regional mating and diversity enhancement | "Strong competitiveness" on 33 benchmark and 6 real-world problems. | Not explicitly quantified, but designed to avoid stagnation. |
| CCMOEA [51] | Co-evolution based on decomposition of multiple constraints | "Competitive" convergence and diversity vs. 8 other algorithms on complex benchmark problems. | Uses evolutionary state detection to avoid wasted iterations. |
| CLBKR [20] | Dynamic knowledge transfer based on problem classification | "Superior or at least competitive performance" on CEC2006, CEC2010, and CEC2017 benchmark suites. | Adapts strategy to problem type, improving search efficiency. |
| CMOEA-WA [50] | Weak constraint–Pareto dominance and angle-based diversity | "Consistently outperforms" state-of-the-art CMOEAs on MW, LIRCMOP, and real-world problems. | Improved balance among feasibility, convergence, and diversity. |
Constraint Relaxation and ε-Constraint Handling Methods
Frequently Asked Questions & Troubleshooting Guides
FAQ 1: What is the fundamental difference between constraint relaxation methods and the ε-constraint handling technique?
Constraint relaxation methods and the ε-constraint technique are both strategic approaches for handling infeasible solutions, but they operate on different principles. Constraint relaxation methods, such as those used in ACREA (Adaptive Constraint Relaxation-based Evolutionary Algorithm), work by adaptively relaxing the constraints according to the iteration information of the population. The purpose is to induce infeasible solutions to transform into feasible ones and thus improve the ability to explore unknown regions [52]. This approach recognizes that completely ignoring constraints can cause the population to waste significant resources searching for infeasible solutions, while excessively satisfying constraints can trap the population in local optima [52].
In contrast, the ε-constraint handling technique implements a specific, often adaptive, threshold that defines an acceptable level of constraint violation. Solutions with constraint violations below this ε threshold are treated as feasible during selection. Takahama et al. proposed the foundational concept of ε constraint relaxation, where the ε constraint values change adaptively based on their own specified rules [52]. Fan et al. further developed this by dynamically adjusting the ε level based on changes in the population's feasibility ratio [52].
Troubleshooting Tip: If your algorithm is converging too quickly to local feasible regions, consider implementing adaptive constraint relaxation. If you're struggling with balancing feasible and infeasible solution information, the ε-constraint method with population-based adaptation may be more suitable.
FAQ 2: Why does my algorithm become trapped in local optima when solving CMOPs with narrow feasible regions?
This common issue typically occurs when the algorithm lacks mechanisms to effectively utilize information from infeasible solutions. When facing discontinuous and narrow feasible regions, algorithms highly likely become trapped in local optima because they cannot traverse infeasible regions to obtain a complete Constrained Pareto Front (CPF) [42]. The presence of very constricted feasible regions, multiple disconnected regions, and feasible regions with significant bias make it difficult for search methods to navigate [53].
Solution: Implement a dual-stage or dual-population approach. For example, the CMOEA-FTR (Feedback Tracking Constraint Relaxation) algorithm divides the entire search process into two stages. In the first stage, constraint boundaries are adaptively adjusted based on feedback information from the population solutions, guiding the boundary solutions toward neighboring solutions and tracking high-quality solutions. This promotes the population to approach the Unconstrained Pareto Front (UPF). In the second stage, the scaling of constraint boundaries is stopped to achieve the complete CPF [42].
FAQ 3: How can I identify which infeasible solutions are valuable for maintaining population diversity and convergence?
Traditional methods often consider only infeasible solutions that violate constraints lightly as valuable, but this may lead to the loss of valuable infeasible solutions in some cases, especially when the population is trapped in complex infeasible regions where individual constraint violations do not monotonously decrease with the decrease of the distance to feasible regions [54].
Advanced Approach: Use a multi-criterion evaluation that assesses the potential quality of each infeasible solution from different aspects, including not only the performances in violating the constraints and optimizing the objectives without considering feasibility, but also the distance to feasible solutions and the ability to pull population out of the infeasible regions below the constrained PFs [54]. The CCEA algorithm exemplifies this approach by regarding infeasible solutions that are shown to be the best in any aspect as valuable [54].
FAQ 4: What metrics should I use to evaluate the performance of my constraint handling method?
Comprehensive evaluation requires multiple metrics to assess different aspects of performance. The experimental results in recent studies show that the proposed ACREA algorithm achieved the best Inverse Generation Distance (IGD) value in 54.6% of the 44 benchmark test problems and the best Hypervolume (HV) value in 50% of them [52]. Similarly, CMOEA-FTR demonstrated superior performance in statistical IGD and HV metrics compared to seven other CMOEAs on 44 benchmark test problems and 16 real-world application cases [42].
Implementation Guidance: Use both IGD and HV metrics for comprehensive evaluation. IGD measures convergence and diversity by calculating the distance between the obtained solution set and the true Pareto front, while HV measures the volume of the objective space dominated by the obtained solutions.
Performance Comparison of Constraint Handling Methods
Table 1: Comparative Performance of Recent Constraint Handling Algorithms on Benchmark Problems
| Algorithm | Key Mechanism | Test Problems | IGD Performance | HV Performance | Key Strengths |
|---|---|---|---|---|---|
| ACREA [52] | Adaptive constraint relaxation based on population iteration information | 44 benchmark problems | Best in 54.6% of problems | Best in 50% of problems | Effective balance between objectives and constraints |
| CMOEA-FTR [42] | Feedback tracking with two-stage approach | 44 benchmark problems, 16 real-world cases | Superior to 7 other CMOEAs | Superior to 7 other CMOEAs | Handles narrow feasible regions effectively |
| CCEA [54] | Multi-criterion identification of valuable infeasible solutions | Multiple benchmarks & engineering problems | Better performance in different CMOPs | Competitive results | Effectively pulls population from infeasible regions |
| ECO-HCT [39] | Hybrid technique based on population situation | 52 test functions, 3 engineering problems | Competitive performance | Competitive performance | Adapts to different population situations |
| PSCMOEA [53] | Probabilistic selection with surrogate models | Challenging constrained problems | Competitive and consistent | Competitive and consistent | Efficient for expensive optimization problems |
Table 2: Classification of Constraint Handling Techniques in Evolutionary Optimization
| Technique Category | Key Principles | Representative Methods | Best Suited Problem Types |
|---|---|---|---|
| Penalty Function-Based [52] [55] | Uses penalty factors to control balance between objectives and constraints | Static penalty, Dynamic penalty, Self-adaptive penalty | Problems with moderate constraint complexity |
| Feasibility-Rule-Based [52] [55] | Gives priority to feasible solutions over infeasible ones | Constraint Dominance Principle (CDP), Stochastic Ranking | Problems with large feasible regions |
| Multi-Objective Transformation [55] | Converts constraints to additional objectives | Pareto ranking, Non-dominated sorting | Problems where constraint information informs search direction |
| Multi-Population/Multi-Stage [52] [42] | Uses multiple populations or stages with different constraint handling | Dual-population, Two-stage archives, Push-pull search | Complex problems with disconnected feasible regions |
| Surrogate-Assisted [53] | Uses approximation models for expensive constraints | Kriging, RBF, SVR models with uncertainty quantification | Problems with computationally expensive constraints |
| Archive-Based [52] [54] | Maintains archives of promising solutions | Elite archives, Diversity archives | Problems requiring balance of feasibility and diversity |
Experimental Protocols & Methodologies
Protocol 1: Implementing Adaptive Constraint Relaxation (ACREA Method)
Objective: To balance constraints and objectives by adaptively relaxing constraints based on population iteration information.
Step-by-Step Procedure:
- Initialize population with random solutions within search boundaries.
- Calculate constraint violation for each solution using the formula:
CV(x) = Σ[max(0, g_j(x))] + Σ[max(0, |h_j(x)| - δ)]where δ is a small positive tolerance parameter (typically 10⁻⁶) [52]. - Adaptively relax constraints according to iteration information of population. The relaxation parameter is adjusted based on the proportion of feasible solutions in the current population.
- Establish an archive for storage and update of solutions using diversity-based ranking to improve convergence speed.
- In the selection process of the mating pool, incorporate common density selection metrics.
- Repeat steps 2-5 until termination criteria are met.
Key Parameters:
- δ (equality constraint tolerance): 10⁻⁶
- Population size: Problem-dependent (typically 100-300)
- Relaxation adjustment rate: Adaptive based on feasible solution proportion
Protocol 2: Two-Stage Feedback Tracking Constraint Relaxation (CMOEA-FTR Method)
Objective: To address CMOPs with different characteristics through a structured two-stage approach.
Step-by-Step Procedure:
- Stage One - Exploration Phase:
- Adaptively adjust constraint boundaries based on feedback information from population solutions.
- Guide boundary solutions toward neighboring solutions.
- Track high-quality solutions to obtain the complete feasible region.
- Store obtained feasible solutions in an archive, continuously updated to promote diversity and convergence.
Stage Two - Exploitation Phase:
- Stop the scaling of constraint boundaries.
- Establish a new dominance criterion to obtain high-quality parents.
- Achieve the complete Constrained Pareto Front (CPF).
Implement elite mating pool selection, archive updating strategy, and elite environmental selection truncation mechanism to maintain balance between diversity and convergence.
Transition Condition: The switch from Stage One to Stage Two typically occurs when the population has achieved sufficient diversity and approached the Unconstrained Pareto Front (UPF).
Research Reagent Solutions
Table 3: Essential Algorithmic Components for Constrained Evolutionary Optimization
| Component | Function | Implementation Examples |
|---|---|---|
| Constraint Violation Calculator | Quantifies solution feasibility | CV(x) = Σ[max(0, g_j(x))] + Σ[max(0, |h_j(x)| - δ)] [52] |
| Adaptive ε Parameter | Controls acceptable constraint violation level | Population feasibility ratio-based adjustment [52] |
| Archive Mechanism | Stores and updates high-quality solutions | Diversity-based ranking update [52] |
| Dual-Population Framework | Separates feasibility and diversity concerns | CA/DA archives in C-TAEA [54] |
| Surrogate Models | Approximates expensive objective/constraint functions | Kriging, RBF, SVR with uncertainty quantification [53] |
| Performance Metrics | Evaluates algorithm effectiveness | IGD, HV, Feasibility Ratio [52] [42] |
Methodological Workflows
Two-Stage Constraint Handling Workflow
Valuable Infeasible Solution Identification Process
The tension/compression spring design problem (TCSDP) is a classical optimization task in engineering that aims to design a spring with minimal weight (or mass) that can carry a given axial load without material failure while satisfying various constraints on shear stress, surge frequency, and geometric limits [56]. This problem has become a canonical benchmark in the field of constrained evolutionary optimization due to its non-linear objective function and multiple constraints, making it an ideal test case for evaluating constraint-handling techniques (CHTs) [56] [57].
Within the broader context of a thesis on handling infeasible solutions in constrained evolutionary optimization research, this case study explores how the TCSDP serves as a standard for evaluating algorithms that must navigate complex, constrained search spaces. The presence of infeasible regions in the solution space presents significant challenges for optimization algorithms, requiring sophisticated techniques to leverage information from infeasible solutions without compromising the search for feasible optima [26] [55].
Problem Formulation and Quantitative Specifications
Design Variables and Objective Function
The TCSDP involves three primary design variables [56]:
- d (wire diameter): The thickness of the spring wire
- D (mean coil diameter): The average diameter of the spring coil
- N (number of active coils): The number of coils that actively contribute to spring deflection
The objective is to minimize the spring weight (or mass), which can be formulated as [56]: f(d, D, N) = (N + 2) × D × d²
This objective function captures the relationship between the spring's physical dimensions and its overall mass, with the goal of finding the minimal mass configuration that satisfies all constraints.
Optimization Constraints
The optimization must satisfy four key constraints that ensure the spring's functionality and safety [56]:
- Shear stress constraint: The maximum shear stress must not exceed the material's allowable limit
- Surge frequency constraint: The spring's natural frequency must be above a specified minimum to avoid resonance
- Minimum deflection constraint: The spring must deflect sufficiently under load
- Geometric constraints: The design must adhere to specified limits on the outer diameter and overall geometry
These constraints create a complex feasible region that challenges optimization algorithms to balance constraint satisfaction with objective minimization.
Standard Variable Bounds
Based on an exhaustive systematic review of metaheuristics applied to TCSDP, the standard bounds for design variables are [56]:
Table 1: Standard Variable Bounds for TCSDP
| Variable | Lower Bound | Upper Bound |
|---|---|---|
| d (wire diameter) | 0.05 | 2.0 |
| D (mean coil diameter) | 0.25 | 1.3 |
| N (number of active coils) | 2 | 15 |
Experimental Protocols and Optimization Methodologies
Evolutionary Algorithm Framework for Constrained Optimization
Evolutionary Algorithms (EAs) have been widely employed to solve complex constrained optimization problems like the TCSDP [26]. The general framework for constrained EAs involves several key components:
Constrained Optimization Evolutionary Algorithm Workflow
Advanced Constraint-Handling Techniques
Recent research has introduced sophisticated CHTs that specifically address the challenge of infeasible solutions:
1. Adaptive Penalty Functions (CdEA-SCPD) This approach assigns different weights to constraints based on their violation severity, varying the significance of each constraint to enhance interpretability and facilitate faster convergence toward the global optimum [26]. The penalty function is formulated as:
Fitness(x) = f(x) + Σ(wi × gi(x))
Where wi represents adaptively determined weights for each constraint gi(x) based on violation severity [26].
2. Dynamic Archiving Strategy This strategy adaptively regulates the number of infeasible solutions preserved in an archive based on fluctuations in population diversity observed during the evolutionary process [26]. By maintaining valuable infeasible solutions, the algorithm can more effectively explore the search space near constraint boundaries.
3. Shared Replacement Mechanism This technique guides population evolution by interactively leveraging diverse information from the archive of feasible and infeasible solutions [26]. Elite individuals from the archive replace less proficient individuals in the current population, accelerating convergence while maintaining diversity.
Performance Evaluation Metrics
When comparing algorithms for TCSDP, researchers should employ multiple performance metrics [56]:
- Best-found objective value: The minimal spring weight achieved
- Constraint satisfaction: Verification that all constraints are satisfied in the final solution
- Computational efficiency: Number of function evaluations (NFE) required
- Statistical significance: Non-parametric statistical tests like Wilcoxon signed-rank test
- Consistency: Performance across multiple independent runs
Troubleshooting Guide: Common Experimental Challenges
FAQ: Algorithm Convergence Issues
Q: My algorithm converges prematurely to suboptimal solutions. How can I improve exploration?
A: Implement a dynamic archiving strategy that maintains a diverse set of infeasible solutions [26]. This approach helps prevent premature convergence by preserving genetic diversity and enabling the algorithm to explore different regions of the search space. Adjust the archive size based on population diversity metrics, increasing it when diversity drops below a threshold.
Q: How should I handle equality constraints in the TCSDP?
A: Convert equality constraints to inequality constraints using a tolerance parameter δ [55]. For example, transform h(x) = 0 to |h(x)| - δ ≤ 0, where δ is a small positive value (e.g., 0.0001). This conversion makes the constraints more manageable for evolutionary algorithms while maintaining practical feasibility.
FAQ: Constraint Handling Difficulties
Q: My algorithm either converges to infeasible regions or ignores promising infeasible solutions. How can I balance this?
A: Implement the co-directed evolutionary algorithm with significance-based constraint handling (CdEA-SCPD) [26]. This approach automatically determines the significance of each constraint during evolution and assigns adaptive weights, allowing the algorithm to prioritize critical constraints while maintaining pressure toward feasibility.
Q: How can I improve computational efficiency when solving the TCSDP?
A: Utilize a shared replacement mechanism that strategically replaces poorly performing individuals in the population with elite solutions from the archive [26]. This approach accelerates convergence while reducing the number of function evaluations required to find high-quality solutions.
FAQ: Implementation and Validation
Q: How do I verify that my solution is truly feasible and optimal?
A: Conduct thorough constraint validation by checking each constraint separately with precise calculations [58]. For stress constraints, use the complete stress formula: S = (8 × P × D) / (π × d³), where P is the applied load. Compare the calculated stress with the material's allowable stress, ensuring a sufficient safety margin.
Q: What statistical tests are appropriate for comparing my algorithm's performance on TCSDP?
A: Use non-parametric statistical tests such as Wilcoxon's signed-rank test, which is recommended for comparing optimization algorithms [26] [56]. Additionally, Friedman's test can rank multiple algorithms across different problem instances. Report p-values to establish statistical significance of performance differences.
The Scientist's Toolkit: Research Reagent Solutions
Table 2: Essential Computational Tools for Spring Optimization Research
| Tool/Component | Function/Purpose | Implementation Notes |
|---|---|---|
| Adaptive Penalty Function Framework | Dynamically adjusts constraint weights based on violation severity | Core component of CdEA-SCPD; enhances interpretability of constraint significance [26] |
| Dynamic Archive | Stores valuable infeasible solutions to maintain population diversity | Size adjusted based on population diversity metrics; prevents premature convergence [26] |
| Shared Replacement Mechanism | Guides evolution using information from archive solutions | Accelerates convergence by replacing poor individuals with elite archive members [26] |
| Statistical Testing Suite | Validates algorithm performance significance | Includes Wilcoxon signed-rank and Friedman tests; essential for rigorous comparison [26] [56] |
| Spring Physics Calculator | Computes stress, deflection, and frequency constraints | Implements formulas for shear stress (S=8PD/πd³) and natural frequency [59] [58] |
Comparative Analysis of Algorithm Performance
Performance Benchmarking
Extensive experimental studies on benchmark functions from IEEE CEC2006, CEC2010, and CEC2017 have demonstrated the superiority of advanced constraint-handling techniques like CdEA-SCPD compared to existing competitive EAs [26]. On the benchmark functions from IEEE CEC2010, the proposed method yields ρ values lower than 0.05 in the multiple-problem Wilcoxon's signed-rank test and ranks first in Friedman's test [26].
Table 3: Algorithm Performance Comparison on TCSDP
| Algorithm Type | Best Reported Weight | Key Strengths | Constraint Handling Approach |
|---|---|---|---|
| CdEA-SCPD | Not specified | Superior convergence, interpretable constraint significance | Adaptive penalty function with significance-based weights [26] |
| Improved Firefly Algorithm (IFA) | Not specified | Effective for constrained optimization | Neighborhood method adaptation [57] |
| Classic Penalty Methods | Varies across studies | Simplicity, ease of implementation | Static penalty coefficients for all constraints [26] |
| Vibrating Particles System (VPS) | Not specified | Physics-inspired optimization | Free vibration of damped objects principle [57] |
Interpreting Results in the Context of Infeasible Solutions
The effectiveness of modern approaches to TCSDP highlights several key principles for handling infeasible solutions in constrained evolutionary optimization [26] [55]:
Significance-Based Constraint Processing: Treating constraints with uniform importance is suboptimal; adaptive weighting based on violation severity produces better results [26].
Strategic Preservation of Infeasible Solutions: Not all infeasible solutions are equal; maintaining those with superior objective values or those near constraint boundaries enhances search efficiency [26] [55].
Diversity Maintenance: Combining information from both feasible and promising infeasible regions prevents premature convergence and improves global search capability [26].
These insights from TCSDP optimization provide valuable guidance for addressing the broader challenges in constrained optimization research, particularly in developing more effective and interpretable approaches for handling infeasible solutions throughout the evolutionary process.
Optimization Strategies and Solutions for Complex Constrained Problems
Addressing Premature Convergence in Highly Constrained Search Spaces
Troubleshooting Guides
This guide addresses common issues you may encounter when applying Evolutionary Algorithms (EAs) to highly constrained search spaces, such as those in drug design and engineering optimization.
Guide 1: Diagnosing and Escaping Premature Convergence at Constraint Boundaries
Problem Description The algorithm converges to a suboptimal solution located on or near a constraint boundary, failing to explore other promising regions of the search space. This frequently occurs when the true optimum lies on the constraint boundary or in a vertex of the feasible search space [60] [61].
Symptoms
- Rapid decrease in population diversity early in the evolutionary process
- Stagnation of fitness improvement despite available infeasible regions
- Low success rate of mutation operations near constraint boundaries
- Population clustering around a few points near constraint boundaries
Diagnostic Table
| Diagnostic Metric | Measurement Method | Interpretation |
|---|---|---|
| Success Rate Analysis | Monitor acceptance rate of new offspring over generations [60] | A consistently low rate (<1/5) indicates premature convergence [61] |
| Population Diversity | Calculate average Euclidean distance between individuals in decision space | Rapidly decreasing values signal diversity loss |
| Feasible-Infeasible Ratio | Track percentage of feasible solutions in population [62] | Ratios <20% suggest difficulty maintaining feasibility |
| Step Size Monitoring | Observe self-adaptive step sizes in evolution strategies [60] | Prematurely small values indicate stagnation |
Resolution Protocol
- Implement Success Rule Step Control: Adapt step sizes based on Rechenberg's 1/5th success rule - increase mutation strength if success rate is high (>1/5), decrease if low [61]
- Introduce Valuable Infeasible Solutions: Identify and preserve infeasible solutions with strong convergence properties using multi-aspect assessment [62]
- Apply Weak Constraint-Pareto Dominance: Modify dominance relations to not always prioritize feasible over infeasible solutions [50]
Guide 2: Handling Complex Infeasible Regions Below Pareto Fronts
Problem Description The initial population arises in complex infeasible regions below the Pareto front, preventing the algorithm from discovering feasible regions and progressing toward optimal solutions [62].
Symptoms
- Inability to find feasible solutions even after many generations
- Population trapped in large infeasible regions with deceptive gradient information
- Constraint violations that don't monotonically decrease toward feasible regions
Resolution Strategies
| Strategy | Implementation | Applicable Scenarios |
|---|---|---|
| Multi-Archive Approach | Maintain separate archives for unconstrained optimization, constraint-feasibility balance, and full constraint handling [50] | CMOPs with discontinuous or complex feasible regions |
| Criterion-Based Selection | Use multi-aspect criterion to identify valuable infeasible solutions based on convergence, diversity, and boundary proximity [62] | Problems where slight constraint violation leads to better objective values |
| Balanced Reproduction | Implement restricted mating selection that strategically combines feasible solutions with valuable infeasible solutions [62] | Maintaining diversity while improving feasibility |
Experimental Validation Protocol
- Initialize population in known infeasible regions below Pareto front
- Apply criterion to identify valuable infeasible solutions across multiple aspects:
- Convergence: Objective value quality ignoring constraints
- Diversity: Contribution to population spread
- Boundary proximity: Distance to feasible regions [62]
- Compare performance against state-of-the-art methods using inverted generational distance (IGD) and feasibility ratio metrics
Frequently Asked Questions (FAQs)
FAQ 1: What are the most effective strategies for balancing feasible and infeasible solutions in constrained evolutionary optimization?
The most effective approaches involve strategic mixing rather than strict prioritization:
- Weak Constraint-Pareto Dominance: This relation integrates feasibility with objective performance, preventing premature elimination of infeasible solutions with strong convergence or diversity characteristics [50]
- Multi-Archive Systems: Maintain three cooperative archives:
- Unconstrained archive (ignores constraints for exploration)
- Constraint-feasibility archive (balances objectives and constraints)
- Fully constrained archive (ensures final feasibility) [50]
- Criterion-Based Identification: Assess infeasible solutions from multiple aspects and preserve those excelling in any dimension (convergence, diversity, or boundary proximity) [62]
FAQ 2: How can I adapt my evolutionary algorithm when the optimum lies on a constraint boundary?
When the optimum is on a constraint boundary, employ these specific techniques:
- Step Size Control: Implement self-adaptive step size mechanisms specifically designed for boundary regions [60]
- Boundary Bias Mutation: Modify mutation operators to bias search toward constraint boundaries while maintaining exploration capability [61]
- Success Rate Monitoring: Continuously monitor and adapt based on success rates near constraints, as low success probability often causes premature convergence in these regions [60]
- Meta-Models for Constraints: Use approximate models of constraint functions to check feasibility and repair infeasible mutations efficiently [61]
FAQ 3: What experimental protocols validate new constraint-handling techniques effectively?
Comprehensive validation requires multiple benchmark types and metrics:
Benchmark Suites for Validation
| Benchmark Type | Key Characteristics | Evaluation Focus |
|---|---|---|
| LYO Suite [62] | Complex infeasible regions below Pareto fronts | Ability to escape deceptive infeasible areas |
| MW & LIR-CMOP [50] | Various feasible region shapes and constraint types | Balance of convergence and diversity |
| Real-World Problems | Engineering design, drug discovery applications [63] [64] | Practical applicability and performance |
Essential Performance Metrics
- Feasibility Ratio: Percentage of feasible solutions in final population
- Inverted Generational Distance (IGD): Comprehensive convergence and diversity assessment
- Hypervolume: Measures dominated region of objective space
- Success Rate: Ability to find globally optimal feasible solutions [62] [50]
The Scientist's Toolkit: Research Reagent Solutions
Essential Methodological Components for Constrained Evolutionary Optimization
| Research Reagent | Function | Example Implementation |
|---|---|---|
| Weak Constraint-Pareto Dominance | Modifies dominance relations to retain promising infeasible solutions | Solution x dominates y if: (1) x has better objectives and equal constraints, OR (2) x has better constraints and equal objectives [50] |
| Angle Distance-Based Diversity | Maintains population spread while ensuring feasibility | Uses reference vectors to divide objective space, selects most feasible solution in each subspace [50] |
| Valuable Infeasible Criterion | Identifies useful infeasible solutions across multiple aspects | Evaluates convergence potential, diversity contribution, and feasibility proximity [62] |
| Multi-Archive Framework | Coordinates complementary search strategies | Three archives: unconstrained exploration, balanced search, and feasibility refinement [50] |
| Self-Adaptive Step Control | Prevents premature convergence at boundaries | Adjusts mutation strength based on success rates near constraints [60] [61] |
Experimental Protocol: Criterion-Based Valuable Infeasible Solution Identification
Methodology This protocol implements the valuable infeasible solution identification criterion for preventing premature convergence [62].
Workflow Visualization
Step-by-Step Implementation
Population Initialization and Evaluation
- Initialize population of size N*
- Evaluate objective values F(x) = (f₁(x), f₂(x), ..., fₘ(x)) for each solution
- Calculate constraint violations CV(x) = Σmax(0, gᵢ(x)) + Σ|hⱼ(x)|
Objective Transformation
- Transform objective values using reference points: f̄ᵢ(x) = fᵢ(x) - fᵢᵐⁱⁿ + 10⁻⁶
- where fᵢᵐⁱⁿ is the minimum value of the i-th objective found so far
Multi-Aspect Assessment Assess each infeasible solution across these dimensions:
- Aspect A (Unconstrained Performance): Quality when ignoring all constraints
- Aspect B (Diversity Contribution): Ability to improve population spread
- Aspect C (Boundary Proximity): Distance to feasible regions
Criterion Application
- Identify solutions that perform best in any single aspect
- Preserve these "valuable infeasible solutions" in a special archive
- Blend archive with feasible solutions during reproduction
Restricted Mating Selection
- Implement strategic pairing between feasible solutions and valuable infeasible solutions
- Balance exploration of promising infeasible regions with feasibility refinement
Validation Metrics
- Success rate improvement compared to standard constraint-handling techniques
- Diversity maintenance throughout evolutionary process
- Ability to discover globally optimal feasible solutions
- Performance on LYO benchmark suite with complex infeasible regions [62]
Balancing Exploration and Exploitation Through Infeasible Solution Management
Frequently Asked Questions (FAQs)
Q1: What is the core challenge in balancing exploration and exploitation when managing infeasible solutions? The core challenge lies in dynamically allocating resources between exploring new, potentially infeasible regions of the search space (which can provide valuable information and lead to better solutions) and exploiting known feasible regions to refine and improve current solutions. Over-emphasizing exploration slows convergence and may not ensure solution quality, while over-emphasizing exploitation can cause premature convergence to local optima. Infeasible solutions are crucial for maintaining diversity and bridging disconnected feasible regions, but they must be managed carefully to guide the search toward global optima [65] [3] [66].
Q2: My population is getting trapped in a local feasible region. How can I encourage exploration across infeasible regions to discover better, disconnected feasible areas?
This is a common issue in problems with complex constraints. Implement a multi-population strategy where one subpopulation (P1) is explicitly guided to explore across infeasible regions. Equip this population with a constraint-handling technique like the Feasible Search Boundary (CHT-FSB). This method dynamically adjusts the search boundary for each feasible solution using an activation function. Infeasible solutions within this boundary are considered promising candidates, allowing the population to search for new feasible regions while strategically navigating through infeasible space. This enhances overall exploration capability [9].
Q3: How can I effectively utilize the feasible solutions I have already found to improve exploitation?
Use the feasible non-dominated solutions you have discovered to guide exploitation. Implement a second subpopulation (P2) that uses a Feasible Non-Dominated Reference Set (FDP). This set identifies potential regions where the Constrained Pareto Front (CPF) is likely to exist. The FDP principle then guides this population to uniformly search these identified regions in the objective space, thereby enhancing the exploitation of high-quality, feasible areas and ensuring a comprehensive coverage of the CPF [9].
Q4: What is a practical method for explicitly controlling the balance between exploration and exploitation during the search process? Adopt a bipopulation framework with explicit transference strategies. This involves splitting your population into an exploration subpopulation and an exploitation subpopulation. The key is to implement triple-transference strategies that migrate individuals between these subpopulations:
- Exploitation Activation: Moves promising explorers to the exploitation group for refinement.
- Exploration Activation: Sends stuck individuals back to the exploration group to seek new areas.
- Exploitation Enhancement: Promotes the best exploiters to guide the overall search. This framework allows for direct and explicit control over the intensity of each phase [66].
Q5: Are there implicit methods to handle constraints and guide the search toward feasibility without complex parameter tuning?
Yes, consider the Boundary Update (BU) method. This implicit technique uses the problem's constraints to iteratively narrow the variable bounds, effectively cutting away infeasible search space over time. It helps the algorithm find the feasible region faster. To prevent the twisted search space from making optimization difficult, combine BU with a switching mechanism. For example, use the BU method initially, and then switch to a standard optimization process without BU once constraint violations reach zero across the entire population (Hybrid-cvtol) or when the objective space shows no improvement for several generations (Hybrid-ftol) [40].
Troubleshooting Guides
Problem: Premature Convergence to a Local Feasible Optimum
Symptoms
- Population diversity drops rapidly early in the run.
- The algorithm consistently converges to the same feasible solution, regardless of random seeds.
- No new feasible regions are discovered after the initial phases.
Solution Steps
- Implement a Diversity Controller (DC): Integrate a diversity controller based on a small-world network. Use fitness-distance correlation information to adjust the network's reconnection probability, which dynamically controls population diversity and helps maintain exploration pressure [3].
- Adopt a Two-Stage Infeasible–Feasible (IF) Strategy: Structure your constraint handling into two clear stages:
- Stage 1 (Boundary Search): Focus the search on the boundary between infeasible and feasible regions. This helps the population "feel" its way toward feasibility without immediately discarding all infeasible solutions.
- Stage 2 (Self-adaptive Epsilon Constraint): Once the boundary is approximated, switch to a self-adaptive epsilon constraint-handling method to refine solutions within the feasible region [3].
- Verify Operator Balance: Ensure your evolutionary operators (mutation, crossover) are not overly greedy. For Differential Evolution, you might use an exploration-oriented operator like adaptive Gaussian local search with reinitialization for the exploration subpopulation [66].
Problem: Inability to Find Any Feasible Solutions
Symptoms
- The best or average constraint violation does not improve over generations.
- The population remains entirely infeasible throughout the run.
Solution Steps
- Prioritize Feasibility in Selection: Immediately implement a feasibility-first rule in your selection process. The rules are:
- Warm-Start with a Pre-trained Model: If using a neural solver, leverage a technique like Universal Constrained Preference Optimization (UCPO). Start from a pre-trained model (even on an unconstrained version of your problem) and perform lightweight fine-tuning. UCPO uses a preference-based loss function to embed constraint satisfaction directly into the learning process, often achieving feasibility with only 1% of the original training budget [10].
- Relax Constraints Initially: Use an ε-constrained method with a large initial
εvalue. This effectively relaxes the constraints at the start of the run, allowing the population to inhabit a larger "almost feasible" space. Gradually reduceεto zero over generations to guide the population toward true feasibility [3].
Problem: Poor Performance on Problems with Disconnected or Narrow Feasible Regions
Symptoms
- The algorithm finds some parts of the constrained Pareto front but misses large sections.
- Performance is acceptable on problems with simple connected feasible regions but fails on more complex constraints.
Solution Steps
- Ensure Co-evolution of Exploration and Exploitation Populations: If using a multi-population approach, enforce information exchange between your exploration-guided (
P1) and exploitation-guided (P2) populations. This collaboration allowsP1to find new feasible regions, whichP2can then thoroughly exploit, enabling a comprehensive exploration of the objective space [9]. - Use a Mask-Agnostic Preference Optimization Loss: Move away from complex, problem-specific masking logic. Instead, adopt a framework like UCPO that uses a unified partial-order criterion. This criterion simply:
- Prefers feasible solutions over infeasible ones.
- Prefers infeasible solutions with lower constraint violation over those with higher violation. This approach eliminates the need for tuning sensitive Lagrange multipliers or designing intricate masks [10].
Experimental Protocols & Data
Protocol 1: Bipopulation with Triple-Transference (TRADE)
This protocol is designed for explicit control between exploration and exploitation [66].
- Initialization: Generate an initial population and split it into two subpopulations:
P_exploreandP_exploit. - Operator Assignment: Assign an exploration-oriented operator (e.g., multi-offspring Differential Evolution) to
P_exploreand an exploitation-oriented operator (e.g., adaptive Gaussian local search) toP_exploit. - Evaluation and Transference: For each generation:
- Evaluate both subpopulations.
- Apply the three transference strategies:
- Exploitation Activation: Select high-quality individuals from
P_exploreand move them toP_exploit. - Exploration Activation: Select low-quality individuals from
P_exploitand move them toP_explore. - Exploitation Enhancement: Identify the best individual in
P_exploitand use it to guide search directions.
- Exploitation Activation: Select high-quality individuals from
- Termination: Check stopping criteria (e.g., max generations, convergence).
Diagram: TRADE Framework Workflow
Protocol 2: Hybrid Boundary Update with Switching
This protocol uses an implicit method to find feasible regions fast and then switches to normal optimization [40].
- Initialization: Define the original variable bounds (
LB,UB). - Phase 1 - BU Method: For each generation:
- Update the bounds of decision variables using the BU method, which narrows the search space based on constraint violations.
- Perform evolutionary operations within the updated bounds.
- Monitor the switching threshold.
- Switching Condition Check:
- Method A (Hybrid-cvtol): Switch when the total constraint violation of the population is zero.
- Method B (Hybrid-ftol): Switch when the best objective value does not improve for a predefined number of generations.
- Phase 2 - Standard Optimization: Once the switch is triggered, continue the evolutionary process using the original variable bounds (
LB,UB) and a standard constraint-handling technique (e.g., feasibility rules).
Diagram: Hybrid BU Switching Strategy
Table 1: Comparison of Constrained Optimization Algorithms on CEC2017 Benchmarks (Mean Error)
| Algorithm | Unimodal Functions | Multimodal Functions | Hybrid Functions | Composite Functions |
|---|---|---|---|---|
| DC-SHADE-IF [3] | 0.00E+00 | 1.45E-01 | 2.10E+01 | 1.50E+01 |
| TRADE [66] | 0.00E+00 | 2.89E-03 | 1.05E+01 | 9.99E+00 |
| SHADE [3] | 5.23E-04 | 4.01E-01 | 3.51E+01 | 2.89E+01 |
Table 2: Feasibility Rates (%) on Complex Constrained Benchmarks
| Algorithm | TSPTW | CVRPTW | TSPDL | CVRPTWLV |
|---|---|---|---|---|
| UCPO [10] | 100% | 99.8% | 100% | 98.5% |
| Lagrangian Method [10] | 85.2% | 72.1% | 90.5% | 65.4% |
| Masking-Based Solver [10] | 45.7% | 30.3% | 95.8% | 25.1% |
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Key Computational Tools for Constrained Evolutionary Optimization
| Tool / Component | Function / Role | Application Context |
|---|---|---|
| Feasibility Rules [3] [40] | A simple, deterministic method for comparing two solutions by prioritizing feasibility and low constraint violation. | A robust baseline constraint-handling technique for most Evolutionary Algorithms (EAs). |
| ε-Constraint Handling [3] | Relaxes constraints by a tolerance ε that decreases over time, gradually guiding the search from infeasible to feasible regions. |
Useful for problems where finding an initial feasible solution is difficult. |
| Diversity Controller (DC) [3] | Dynamically controls population diversity using a small-world network model to prevent premature convergence. | Essential for maintaining exploration pressure in multimodal and complex constrained problems. |
| Preference Optimization Loss (UCPO) [10] | A mask-agnostic loss function that embeds constraint satisfaction as a preference for feasible solutions and lower violations. | Enables neural solvers to handle complex global constraints without intricate masking or Lagrangian tuning. |
| Boundary Update (BU) [40] | An implicit method that narrows the variable bounds over iterations to cut off infeasible search space. | Accelerates the initial discovery of feasible regions, especially in problems with known variable bounds. |
Handling Disconnected and Narrow Feasible Regions
Troubleshooting Guides
Troubleshooting Guide 1: Diagnosing and Resolving Infeasibility
Problem: The optimization algorithm fails to find a feasible solution, returning an infeasible status. Question: What steps can I take to identify and resolve the causes of infeasibility in my constrained optimization model?
Answer: Infeasibility occurs when no solution exists that satisfies all constraints simultaneously, often due to overly restrictive constraints or conflicting requirements. Follow this systematic approach to diagnose and resolve the issue:
Run an Infeasibility Diagnostic Tool: Utilize specialized tools like the Infeasibility Diagnostic Engine. This engine adds slack variables to all constraints and solves an augmented optimization problem focused on minimizing these slacks. The results explicitly show which constraints are violated and by how much, providing a direct indication of which constraints are causing the infeasibility [67]. The diagnostic output will appear in an Optimization Constraint Summary table.
Analyze Constraint Violations: Examine the diagnostic report to identify the specific constraints with the largest slack variables. These are the primary contributors to the infeasibility. For example, the results might indicate that a demand constraint for a specific customer cannot be met because no transportation lanes exist to serve it, suggesting the constraint should be relaxed or set to zero [67].
Implement Constraint Relaxation: Based on the diagnostic results, relax the problematic constraints. This can be done by:
- Adjusting the right-hand side values of binding constraints.
- Reviewing the logic and parameters of the constraints identified as the root cause.
- The diagnostic tool provides a quantitative measure of the required relaxation to achieve feasibility [67].
Troubleshooting Guide 2: Optimizing in Disconnected Feasible Regions
Problem: The algorithm converges to poor local optima or fails to explore all viable sections of a disconnected feasible region. Question: What strategies can improve search performance when the feasible region is not a single, connected area?
Answer: Disconnected regions pose a significant challenge as they require the algorithm to "jump" between isolated feasible zones. Employ the following strategies:
Adopt a Multi-Stage Search Approach: Use an algorithm that explicitly searches both infeasible and feasible regions. The Infeasible-Feasible (IF) Regions Constraint Handling Method is a two-stage approach specifically designed for this [3]:
- Stage 1 - Boundary Search: The first stage focuses on exploring the boundary between infeasible and feasible regions to map out the disconnected feasible patches.
- Stage 2 - Focused Feasible Search: The second stage uses a self-adaptive Epsilon constraint-handling method to refine solutions within the discovered feasible regions.
Control Population Diversity: Use a Diversity Controller (DC) to prevent premature convergence. A diversity controller based on a small-world network topology can dynamically regulate population diversity, helping to maintain exploration capability and navigate between disconnected regions [3].
Combine with Robust Constraint Handling: Integrate the above methods with a powerful algorithm like Success-History Based Adaptive Differential Evolution (SHADE). The combined DC-SHADE-IF algorithm has demonstrated superior performance in accurately solving problems with complex feasible region topologies [3].
Troubleshooting Guide 3: Navigating Narrow Feasible Regions
Problem: The algorithm struggles to locate or converge within a very narrow feasible region, especially in high-dimensional spaces. Question: Which techniques can efficiently guide the search into a thin feasible space?
Answer: Narrow feasible regions act like a "needle in a haystack." Direct random search is highly inefficient. Implicit constraint handling techniques that dynamically reshape the search space are particularly effective:
Employ a Boundary Update (BU) Method: The BU method is an implicit technique that iteratively updates the variable bounds based on the problem's constraints. It actively cuts away portions of the infeasible search space, effectively narrowing the search focus towards the viable region over time. This makes it easier for the algorithm to locate a narrow feasible space [40].
Implement a Hybrid Switching Mechanism: A pure BU method can twist the search landscape. To counter this, use a hybrid approach that switches off the BU method once the feasible region is found [40]. Two switching criteria are effective:
- Hybrid-cvtol: Switch when the constraint violation for the entire population reaches zero, indicating the population has entered a feasible region [40].
- Hybrid-ftol: Switch when no further improvement is observed in the objective space for a specified number of generations, suggesting the initial gains from BU have been exhausted [40].
Augment with an Explicit CHT: The BU method should be coupled with an explicit constraint handling technique, such as Feasibility Rules, to compare and select solutions based on both feasibility and objective function value [40].
Frequently Asked Questions (FAQs)
FAQ 1: What is the fundamental difference between a disconnected and a narrow feasible region? A feasible region is the set of all points that satisfy an optimization problem's constraints [68]. A disconnected feasible region consists of two or more isolated sub-regions, separated by infeasible space. A narrow feasible region is a single, connected region that is very thin in one or more dimensions. While both are challenging, they require different search strategies: navigating between disconnected islands versus locating a thin, winding path.
FAQ 2: When should I prefer the Boundary Update method over the Infeasible-Feasible method? The choice depends on the suspected nature of the feasible region:
- Use the Boundary Update (BU) method when you need to quickly find any feasible solution and suspect the feasible region is narrow or convoluted. It is excellent for initial feasibility discovery [40].
- Use the Infeasible-Feasible (IF) method when you suspect multiple disconnected feasible regions and want a thorough exploration to find the best one, not just the first one encountered [3]. The IF method is better for achieving a better trade-off between the objective function and constraints in complex landscapes.
FAQ 3: My model is infeasible. The diagnostic tool suggests relaxing a key constraint, but that compromises the problem's realism. What can I do? This indicates a fundamental conflict in your problem formulation. Instead of blindly relaxing constraints, consider:
- Reformulating the Problem: Re-examine the underlying assumptions of your model. The conflict may reveal an error in business logic or problem definition.
- Exploring Alternative Constraints: The infeasibility might be resolved by adding new options (e.g., creating a new transportation lane) rather than just relaxing a demand constraint [67].
- Using Advanced Penalties: For complex, real-world constraints that are difficult to handle with simple masking, consider frameworks like Universal Constrained Preference Optimization (UCPO), which uses preference learning to handle hard constraints without meticulous hyperparameter tuning [10].
FAQ 4: How do I know if my population has sufficient diversity to handle a disconnected feasible region? Implement a Diversity Controller (DC). You can monitor diversity using a metric based on a small-world network. If the population diversity falls below a certain threshold, the controller can increase the reconnection probability in the network, which promotes exploration and helps the algorithm jump to other feasible regions [3].
Comparative Analysis of Methods
The table below summarizes the core methodologies discussed for handling challenging feasible regions.
Table 1: Comparison of Advanced Constraint Handling Approaches
| Method Name | Core Principle | Best Suited For | Key Advantage | Experimental Consideration |
|---|---|---|---|---|
| Infeasibility Diagnostic [67] | Adds slack variables to constraints to identify minimal relaxation needed. | Diagnosing the root cause of a completely infeasible model. | Directly identifies violated constraints and quantifies the required relaxation. | Can be run as a standalone tool before the main optimization. |
| Boundary Update (BU) [40] | Iteratively tightens variable bounds to cut off infeasible space. | Locating narrow or hidden feasible regions faster. | An implicit method that reduces the viable search space, speeding up initial feasibility. | Should be used with a switching mechanism (Hybrid-cvtol/ftol) to avoid distorted landscapes. |
| Infeasible-Feasible (IF) [3] | Two-stage method: first searches the feasibility boundary, then refines inside. | Navigating disconnected feasible regions and achieving a good constraint-objective balance. | Systematically explores the boundary between feasible/infeasible space, mapping disconnected regions. | Requires integration with an optimizer like SHADE and a diversity controller for best results. |
| UCPO Framework [10] | Uses preference optimization to learn constraint satisfaction without Lagrange multipliers. | Problems with complex, global constraints where penalty tuning is difficult. | Mask-agnostic; avoids sensitive hyperparameter tuning (e.g., Lagrange multipliers). | Requires lightweight fine-tuning of a pre-trained model; uses a universal constrained preference loss function. |
Experimental Protocols
Protocol 1: Implementing the Hybrid Boundary Update Method
This protocol outlines the steps for implementing the Hybrid BU method with a switching mechanism to find a narrow feasible region [40].
- Initialization: Define the original problem with decision variable bounds (
LB,UB), objective functionF(x), and constraintsg_j(x). - BU Phase:
a. Select a "repairing variable"
x_ithat handles the greatest number of constraints. b. During optimization, dynamically update the bounds ofx_iusing the constraintsg_j(x). For each iteration, calculate the updated lower boundlb_i^uand upper boundub_i^uas:lb_i^u = min(max(l_{i,1}(x_{≠i}), ..., l_{i,k_i}(x_{≠i}), lb_i), ub_i)ub_i^u = max(min(u_{i,1}(x_{≠i}), ..., u_{i,k_i}(x_{≠i}), ub_i), lb_i)wherel_{i,j}andu_{i,j}are the dynamic bounds derived from thej-thconstraint. c. Use an explicit CHT (e.g., Feasibility Rules) for solution selection. - Switching Check: Monitor the specified switching criterion every generation.
- For Hybrid-cvtol: Calculate the total constraint violation
G(x)for all individuals. Switch ifG(x) == 0for the entire population. - For Hybrid-ftol: Track the change in the best objective value. Switch if the improvement is below a tolerance
ftolforNconsecutive generations.
- For Hybrid-cvtol: Calculate the total constraint violation
- Post-Switch Phase: Once the switching criterion is met, continue the optimization using the original variable bounds (
LB,UB) and the explicit CHT, without further BU.
Protocol 2: Implementing the Infeasible-Feasible (IF) Method
This protocol details the application of the two-stage IF method for handling disconnected regions within an evolutionary algorithm [3].
- Algorithm Setup: Embed the IF method into a suitable EA, such as SHADE.
- Stage 1 - Boundary Search: a. The population is initialized and begins evolution. b. The constraint handling method prioritizes searching for the boundaries of feasible regions. This is achieved by focusing selection pressure on individuals with low constraint violation, guiding the population toward the edges of feasible areas.
- Stage 2 - Epsilon Constraint Handling:
a. The algorithm transitions to this stage after a predefined condition (e.g., a number of generations or upon finding a feasible solution).
b. A self-adaptive
ɛvalue is used to compare individuals. Theɛvalue typically starts loose and tightens over time. c. Comparison Rules: * If the constraint violation of both individuals is less thanɛ, the one with a better objective function is preferred. * If the constraint violation is the same, the one with a better objective function is preferred. * Otherwise, the individual with a lower constraint violation is preferred. - Diversity Control: Integrate a Diversity Controller (DC) that uses a small-world network model to monitor and actively maintain population diversity, preventing premature convergence in one feasible sub-region.
Method Workflow Visualization
The following diagram illustrates the logical workflow of the Hybrid Boundary Update method, showcasing the switching mechanism between its two primary phases.
Figure 1: Workflow of the Hybrid Boundary Update Method with Switching Mechanism.
The Scientist's Toolkit: Research Reagent Solutions
This table lists key computational "reagents" – algorithms and methods – essential for experiments in constrained evolutionary optimization with difficult feasible regions.
Table 2: Essential Research Reagents for Constrained Optimization
| Reagent (Algorithm/Method) | Function/Benefit | Primary Application |
|---|---|---|
| Infeasibility Diagnostic Engine [67] | A diagnostic tool that identifies which constraints cause infeasibility and quantifies the required relaxation. | First-line diagnosis for models that fail to solve. |
| Slack Variables [67] | Artificial variables added to constraints to allow temporary violation, converting an infeasible problem into a feasible one for diagnostic purposes. | Core component of the infeasibility diagnostic engine. |
| Boundary Update (BU) [40] | An implicit constraint handling technique that dynamically updates variable bounds to cut away infeasible search space. | Efficiently locating narrow feasible regions. |
| Feasibility Rules [3] | An explicit constraint handling technique that uses three simple rules to compare solutions based on feasibility and objective value. | A robust and commonly used method for solution selection within EAs. |
| Diversity Controller (DC) [3] | A mechanism based on small-world networks to actively monitor and control population diversity during evolution. | Preventing premature convergence and exploring disconnected feasible regions. |
| UCPO Framework [10] | A plug-and-play framework using preference optimization to handle hard constraints without sensitive Lagrange multipliers. | Solving problems with complex, global constraints where traditional penalty methods fail. |
Adaptive Success Rate Prediction for Information Exchange Control
Frequently Asked Questions
Q1: What does "infeasible solution" mean in evolutionary optimization for drug development, and why should I keep them?
In constrained evolutionary optimization, an infeasible solution violates one or more problem constraints. Unlike traditional approaches that discard them, modern research shows that explicitly maintaining a small percentage of "good" infeasible solutions near constraint boundaries can significantly improve convergence rates. These solutions provide valuable information about constraint landscapes and enable approaches from both feasible and infeasible regions, which is particularly valuable when optimal solutions lie on constraint boundaries [14].
Q2: My adaptive prediction model performs well during training but deteriorates with real-world pharmaceutical data. What could be causing this?
This common issue, known as behavioral drift, occurs when agent processing speed, reliability, or resource availability changes over time due to wear, load fluctuations, or context shifts. Static performance models cannot capture such non-stationarity. Implement a two-layer architecture with adaptive controllers that predict task parameters via recursive regression with forgetting factors and selectively broadcast tasks based on current relevance and availability [69].
Q3: How can I handle delayed or noisy feedback in pharmaceutical success rate prediction?
Non-stationary and delayed feedback presents significant challenges for real-time adaptation. Consider implementing a Simultaneous Perturbation Stochastic Approximation (SPSA) approach combined with consensus-based synchronization. This maintains model consistency across distributed networks while accommodating noisy feedback environments common in pharmaceutical data streams [69].
Q4: What optimization algorithms work best for constrained problems in drug development?
For constrained optimization problems where optimal solutions lie on constraint boundaries, the Infeasibility Driven Evolutionary Algorithm (IDEA) has demonstrated superior performance compared to traditional approaches like NSGA-II. IDEA explicitly maintains marginally infeasible solutions and ranks "good" infeasible solutions higher than feasible ones, focusing search near constraint boundaries [14].
Troubleshooting Guides
Problem: Model Fails to Generalize Across Different Time Scales
Symptoms: Accurate predictions at fixed training intervals but significant performance degradation with varying observation rates.
Solution: Implement Time-Aware World Models (TAWM) that explicitly incorporate temporal dynamics:
- Condition your model on time-step size (Δt) rather than sampling at fixed intervals
- Train over diverse Δt values using log-uniform sampling from predefined intervals
- Incorporate numerical stabilization methods like fourth-order Runge-Kutta (RK4) for large Δt values
- Modify value models to accept Δt as additional input parameter [70]
Validation Protocol:
- Evaluate model performance across multiple time scales in Meta-World and PDE-control environments
- Compare Root Mean Square Error (RMSE) and accuracy metrics against fixed-Δt baselines
- Assess computational efficiency using same training samples and iterations
Problem: Exponential Computational Cost with Population Size
Symptoms: Model training becomes prohibitively expensive as problem complexity increases.
Solution: Implement hybrid optimization strategies:
| Approach | Mechanism | Best For |
|---|---|---|
| Archimedes Optimization (AOA) | Feature selection to reduce input parameters | High-dimensional data |
| AOA-ANN Hybrid | Combines AOA with Artificial Neural Networks | Construction EAC prediction |
| AOA-ANFIS Hybrid | Integrates AOA with Adaptive Neuro-Fuzzy Systems | Noisy pharmaceutical data |
| Infeasibility Driven EA | Maintains valuable infeasible solutions | Constrained optimization [71] [14] |
Implementation Steps:
- Conduct literature review to identify key variables
- Apply AOA for feature selection to identify significant parameters
- Develop hybrid models (AOA-ANN or AOA-ANFIS)
- Validate using statistical indicators (MAE, R-value, MSE)
Problem: Prediction Model Cannot Handle Multi-Source Heterogeneous Data
Symptoms: Inaccurate remaining useful life predictions with varied sensor data and failure modes.
Solution: Deploy ADAPT-RULNet framework integrating attention mechanisms and deep reinforcement learning:
Experimental Workflow for Pharmaceutical Equipment:
- Data Preprocessing: Apply Functional Alignment Resampling (FAR) to generate high-quality functional signals
- Degradation Staging: Use attention-enhanced Dynamic Time Warping to identify individual degradation stages
- Feature Extraction: Construct hybrid multi-scale network to extract local and global features
- Feature Fusion: Adaptively fuse multi-source features using Bayesian methods
- Parameter Optimization: Introduce Deep Deterministic Policy Gradient (DDPG) to optimize degradation stage parameters [72]
Problem: Infeasible Solutions Dominating Population
Symptoms: Evolutionary algorithm stagnates with too many constraint violations.
Solution: Implement controlled infeasibility management:
Constrained Optimization Protocol:
- Initialization: Generate population with random individuals
- Evaluation: Assess fitness and constraint violation for each individual
- Identification: Identify "good" infeasible solutions close to constraint boundaries
- Ranking: Rank high-quality infeasible solutions higher than feasible ones
- Maintenance: Explicitly maintain small percentage (typically 5-15%) of marginally infeasible solutions
- Convergence: Approach constraint boundaries from both feasible and infeasible regions [14]
Research Reagent Solutions
| Research Component | Function | Example Implementation |
|---|---|---|
| Fast Healthcare Interoperability Resources (FHIR) | Standardized data exchange for pharmaceutical quality data | HL7 FHIR APIs for Chemistry, Manufacturing, and Controls (CMC) data [73] |
| Time-Aware World Model (TAWM) | Adaptive prediction across varying temporal resolutions | Conditioning dynamics model on time-step size Δt [70] |
| Archimedes Optimization Algorithm (AOA) | Feature selection for high-dimensional data | AOA-ANN hybrid for Estimate-at-Completion prediction [71] |
| Infeasibility Driven EA (IDEA) | Constrained optimization handling | Maintaining marginally infeasible solutions near constraint boundaries [14] |
| Adaptive Neuro-Fuzzy Inference System (ANFIS) | Handling uncertainty in prediction models | ANFIS with AOA for construction cost prediction [71] |
| Deep Deterministic Policy Gradient (DDPG) | Continuous parameter optimization in prediction models | Adaptive optimization of degradation stage parameters [72] |
Performance Metrics Table
| Algorithm | Application Context | Key Metrics | Performance Results |
|---|---|---|---|
| Infeasibility Driven EA | Constrained single/multi-objective optimization | Convergence rate | Better convergence than NSGA-II on test problems [14] |
| AOA-ANN Hybrid | Estimate-at-completion prediction | MAE, R-value, MSE | Superior accuracy with minimum input parameters [71] |
| Time-Aware World Model | Control tasks with varying observation rates | RMSE, Accuracy | Consistent outperformance across varying Δt [70] |
| ADAPT-RULNet | Remaining Useful Life prediction | RMSE, Accuracy | Lower average RMSE on aircraft engines and railway wheels [72] |
| Two-layer Adaptive Control | Dynamic multi-agent task allocation | Scalability, Robustness | Effective under partial observability and noisy feedback [69] |
Diversity Preservation Techniques Using Infeasible Solutions
Frequently Asked Questions
Q1: Why does my constrained multi-objective algorithm converge prematurely on problems with complex feasible regions?
This commonly occurs when the algorithm's constraint-handling technique over-prioritizes feasibility at the expense of maintaining population diversity. If infeasible solutions with promising objective values are discarded too early, the population can become trapped in local feasible regions, particularly when the true constrained Pareto front is disconnected or complex. Strategies such as the weak constraint–Pareto dominance relation have been developed to prevent this by integrating both feasibility and objective performance into dominance comparisons, thereby preserving valuable infeasible solutions that can guide the search [50].
Q2: How can I determine which infeasible solutions are "useful" and worth preserving in the population?
Not all infeasible solutions are equally valuable. Promising infeasible solutions are typically characterized by either strong convergence (good objective values) or their ability to enhance population diversity. Specific techniques to identify them include:
- Feasible Search Boundary (CHT-FSB): An infeasible solution is considered promising if a feasible solution exists within a certain Euclidean distance (defined by a dynamic factor β) in the objective space [9].
- Global Diversity Strategy: Using weight vectors to divide the objective space into subregions and then selecting infeasible solutions from each subregion to maintain a well-distributed population [24].
- Fitness Evaluation: Employing a fitness function for infeasible solutions that balances the importance of both constraint violations and objective values [24].
Q3: My algorithm finds feasible solutions but they cluster in only a few regions of the Pareto front. How can I achieve better distribution?
This indicates a diversity loss. One effective method is the angle distance-based diversity maintenance strategy. This approach uses reference vectors to partition the objective space into evenly distributed subspaces. The most feasible solution within each subspace is then selected, ensuring a comprehensive exploration of the entire objective space and helping to discover all feasible regions, even when they are irregularly shaped [50].
Q4: Are there strategies that use multiple populations to handle constraints and diversity?
Yes, multi-population or multi-archive strategies are highly effective. For instance, the UICMO framework uses two co-evolving populations with different focuses:
- An exploration-guided population (
P1) uses techniques like CHT-FSB to explore across infeasible regions, searching for new feasible areas. - An exploitation-guided population (
P2) uses a dominance principle based on a feasible non-dominated reference set to uniformly search areas where the constrained Pareto front is likely to exist. The information exchange between these populations enables a more comprehensive search [9]. Similarly, the CMOEA-WA algorithm uses three external archives for unconstrained optimization, constraint-feasibility-based optimization, and fully constraint-based optimization, respectively [50].
Troubleshooting Guides
Problem: Population Stagnation in Local Feasible Regions
Symptoms
- The population converges quickly to a few feasible solutions.
- No improvement in objective space diversity over generations.
- Failure to discover disconnected segments of the constrained Pareto front.
Diagnosis and Solutions
| Diagnosis Step | Solution | Implementation Example |
|---|---|---|
| Check the proportion of infeasible solutions in mid-to-late generations. | Introduce a global diversity strategy. | In EGDCMO, a set of weight vectors divides the objective space. A specific number of infeasible solutions with the best diversity and convergence are preserved from each subregion to maintain global diversity [24]. |
| Analyze if feasible solutions are dominating all infeasible ones indiscriminately. | Implement a relaxed dominance principle. | Use a weak constraint–Pareto dominance relation. This method prevents a feasible solution from dominating an infeasible one if the feasible solution has inferior objective value(s), thereby protecting promising infeasible solutions [50]. |
| Determine if the search is stuck in one feasible segment. | Adopt a multi-archive or multi-population approach. | Implement the UICMO framework, where P1 explores infeasible regions to find new feasible areas, while P2 refines the search in identified promising regions. This balances exploration and exploitation [9]. |
Problem: Poor Performance on CMOPs with Disconnected Feasible Regions
Symptoms
- Algorithm finds one feasible region but misses others.
- Performance metrics show good convergence but poor diversity and coverage.
Diagnosis and Solutions
| Diagnosis Step | Solution | Implementation Example |
|---|---|---|
| Check if the algorithm's diversity mechanism relies solely on objective-space distance. | Combine angle-based selection with feasibility information. | Use an angle distance-based diversity maintenance strategy. The objective space is divided into sectors using reference vectors, and selection prioritizes feasibility within these pre-defined, diverse directions [50]. |
| Determine if the search is overly attracted to the unconstrained Pareto front (UPF). | Utilize feasible non-dominated solutions to guide the search. | Apply the Feasible non-dominated reference set Dominance Principle (FDP). This principle uses already found feasible non-dominated solutions to identify and uniformly search other potential regions where the constrained Pareto front might exist [9]. |
| Verify if the population lacks representatives in unexplored objective-space regions. | Maintain a separate archive for exploration. | As in CMOEA-WA, an "exploration-guided" archive can focus on unconstrained optimization, ignoring constraints to fully explore the objective landscape and provide diverse genetic material to other archives [50]. |
Experimental Protocols & Performance Data
Protocol 1: Implementing Weak Constraint–Pareto Dominance
This protocol is based on the method described in CMOEA-WA [50].
Objective: To modify the selection process to retain infeasible solutions that offer good convergence or diversity.
Procedure:
- Define Dominance: For two solutions
xandy,xweakly constraint-dominatesyif:xis feasible andyis infeasible only ifxalso has better or equal objective values thanyfor all objectives. Otherwise, the dominance is checked based on standard Pareto dominance considering both objectives and constraint violation.- This prevents a feasible solution with poor objective values from eliminating an infeasible solution with excellent convergence.
- Integrate with Selection: Use this redefined dominance relation in the environmental selection step of your evolutionary algorithm (e.g., instead of the standard constrained dominance principle in NSGA-II).
- Diversity Preservation: Follow this with an angle distance-based diversity maintenance strategy to select solutions from the non-dominated set.
Expected Outcomes: A more diverse set of solutions approaching the true constrained Pareto front, especially on problems like the LIR-CMOP test suite which have small or disconnected feasible regions [50].
Protocol 2: Two-Population Information Exchange (UICMO)
This protocol is based on the UICMO framework [9].
Objective: To balance exploration of new feasible regions and exploitation of known promising regions.
Procedure:
- Initialize: Create two populations,
P1(exploration-guided) andP2(exploitation-guided). - Co-evolve:
- For
P1: Apply the CHT-FSB method. Dynamically adjust a search boundary factorβ. Infeasible solutions falling within theβ-radius of any feasible solution are considered "promising" and retained to helpP1navigate through infeasible regions. - For
P2: Apply the FDP method. Maintain a feasible non-dominated reference set. This set is used to guideP2to search uniformly in regions of the objective space that are non-dominated with respect to this set, effectively identifying potential CPF regions.
- For
- Information Exchange: Allow periodic migration of individuals between
P1andP2(e.g., everyKgenerations) to share discovered information.
Validation Metrics: Use metrics like Inverted Generational Distance (IGD) and Hypervolume (HV) to measure both convergence and diversity. The following table summarizes sample performance gains observed in research:
| Algorithm | Benchmark Problem | Performance Metric | Result |
|---|---|---|---|
| CMOEA-WA [50] | LIR-CMOP | IGD | Achieved more effective balance of feasibility, convergence, and diversity compared to state-of-the-art CMOEAs. |
| UICMO [9] | LIR-CMOP3 | IGD | Consistently outperformed eight state-of-the-art CMOEAs, demonstrating superior exploration and exploitation. |
| EGDCMO [24] | CMOPs with small feasible regions | HV | Showed impressive performance by maintaining well-distributed infeasible solutions. |
The Scientist's Toolkit: Key Algorithmic Components
The following table details core algorithmic "reagents" used in the featured techniques.
| Component Name | Function | Implementation Example |
|---|---|---|
| Weak Constraint–Pareto Dominance Relation | Alters the selection pressure by not allowing poor feasible solutions to automatically dominate high-quality infeasible ones, preserving genetic material from promising areas of the search space. | A feasible solution does not always dominate an infeasible one; comparison integrates both constraint violation and objective values [50]. |
| Angle Distance-based Diversity Maintenance | Ensures the population spreads evenly across the objective space by selecting solutions based on their angular separation relative to predefined reference vectors, which is independent of the feasible region's shape. | The objective space is divided into sectors using reference vectors. The most feasible solution within each sector is selected for survival [50]. |
| Feasible Search Boundary (CHT-FSB) | Dynamically defines a neighborhood around feasible solutions. Infeasible solutions inside this boundary are considered helpful for exploration and are retained. | The boundary factor β is adjusted during the run. An infeasible solution x is re-classified as "promising" if a feasible solution exists within Euclidean distance β of x in objective space [9]. |
| Feasible non-dominated Reference Set | A fixed-size archive storing the best found feasible, non-dominated solutions. It is used to identify unexploited regions of the objective space that may contain parts of the Pareto front. | The reference set is updated at each generation. It serves as a guide for an exploitation-focused population to search uniformly in non-dominated regions [9]. |
| Global Diversity Weight Vectors | A set of predefined vectors used to decompose the multi-objective problem into multiple single-objective subproblems. This ensures a uniform spread of search effort across the objective space. | As in EGDCMO, weight vectors specify subregions. Infeasible solutions are selected from each subregion to maintain a globally diverse population [24]. |
Parameter Control in Multi-Stage and Multi-Task Frameworks
Frequently Asked Questions (FAQs)
1. What are the most effective strategies for handling infeasible solutions in constrained multi-task optimization? A highly effective strategy is the dynamic archiving of infeasible solutions combined with a shared replacement mechanism. This approach actively preserves valuable infeasible solutions that exhibit good objective function performance or are located near constraint boundaries. These archived solutions are then used to replace poorer-performing individuals in the main population, enriching population diversity and providing genetic material that can help the algorithm explore the feasible region boundary more effectively [26].
2. How can I prevent task interference in a parameter-efficient multi-task learning model? Implement a progressive task-specific adaptation architecture. In this setup, adapter modules are completely shared across all tasks in the early layers of a pre-trained model to enable knowledge transfer. As the network progresses toward the output layers, these adapters become increasingly task-specific. This structure balances shared representation learning with specialized processing, significantly reducing gradient conflicts and negative transfer between tasks [74].
3. What is a reliable method for assigning significance to different constraints in an optimization problem? Develop an adaptive penalty function that automatically weights constraints based on their violation severity during the evolutionary process. Unlike static methods, this approach investigates the intrinsic significance of each constraint spontaneously as the evolution progresses, assigning higher penalties to more severely violated constraints. This provides interpretable insights into constraint relationships and guides the population more rapidly toward the global optimum [26].
4. How can I compute task similarity to optimize knowledge sharing in multi-task frameworks? Use a gradient-based task similarity measure. This method computes similarity directly from the gradients of tasks during training, introducing minimal computational overhead. Tasks with similar gradient directions can be grouped to share adapter modules or other parameters, thereby enhancing positive transfer while reducing interference between dissimilar tasks [74].
Troubleshooting Guides
Problem: Catastrophic Forgetting When Dynamically Adding New Tasks
Symptoms
- Sharp performance drop on previously learned tasks when a new task is introduced.
- Inability to maintain stable performance across heterogeneous tasks in continuous learning scenarios.
Solution Implement a multi-task learning strategy with lightweight fine-tuning that enables dynamic adaptation to new tasks.
Step-by-Step Resolution
- Maintain a shared representation space using a pre-trained vision-language model as your backbone to ensure a unified foundation for all tasks [75].
- Introduce task-specific prompts or adapters for each new task, freezing the core model parameters to preserve existing knowledge [75] [74].
- Use a multi-task sharing network that allows new tasks to acquire features from semantically related intra-group tasks while maintaining inter-group correlations [75].
- Regularize parameter updates using techniques that constrain important weights for previous tasks, preventing significant alteration of shared representations crucial for earlier learning [76].
Problem: Severe Task Interference and Negative Transfer
Symptoms
- Simultaneous training of multiple tasks results in worse performance than single-task models.
- Highly variable performance across tasks, with some tasks dominating the learning process.
Solution Adopt a progressive task-specific architecture with intelligent task grouping.
Resolution Protocol
- Analyze task relationships using a gradient-based similarity measure before full model training [74].
- Design your network architecture such that early layers use shared adapters for all tasks, intermediate layers use adapters shared across similar task groups, and final layers employ task-specific adapters [74].
- Implement a balanced multi-task loss function that automatically weights the contribution of each task based on its learning status and uncertainty [76].
- For constrained optimization problems, extend this approach by creating task-specific constraint handling with shared knowledge of constraint significance across related tasks [26].
Problem: Poor Handling of Infeasible Solutions in Constrained Optimization
Symptoms
- Population prematurely converges to suboptimal feasible regions.
- Algorithm struggles to navigate complex feasible region boundaries with dispersed or discontinuous regions.
Solution Deploy a co-directed evolutionary algorithm with dynamic archiving and significance-based constraint handling.
Experimental Procedure
- Calculate constraint significance throughout the evolutionary process by analyzing the severity of violation for each constraint across the population [26].
- Apply an adaptive penalty function that assigns different weights to constraints based on their computed significance [26].
- Implement a dynamic archiving strategy that selectively preserves promising infeasible solutions based on both objective function quality and constraint violation patterns [26].
- Establish a shared replacement mechanism where elite archived solutions periodically replace low-performing individuals in the main population to maintain diversity [26].
- Balance the exploration of feasible and infeasible regions by adjusting the archive size based on population diversity metrics relative to initial diversity [26].
Experimental Protocols & Methodologies
Protocol 1: Progressive Task-Specific Multi-Task Adaptation
Purpose To enable parameter-efficient multi-task learning while minimizing task interference through structured knowledge sharing.
Materials
- Pre-trained transformer model (e.g., Swin Transformer, CLIP)
- Multi-task dataset (e.g., PASCAL, NYUD-v2)
- Implementation of LoRA or similar parameter-efficient fine-tuning method
Procedure
- Task Similarity Analysis Phase
- Compute task similarity using gradient-based measures during initial training epochs
- Group tasks with high similarity scores for shared adapter allocation
Adapter Architecture Configuration
- Early network layers: Implement shared adapters across all tasks
- Middle network layers: Deploy group-specific adapters for related tasks
- Final layers: Utilize task-specific adapters for specialized processing
Training Protocol
- Freeze all base model parameters
- Only train adapter modules and task-specific heads
- Use balanced multi-task loss weighting
- Validate on all tasks simultaneously after each epoch
Validation Metrics
- Relative improvement compared to single-task fine-tuning
- Number of trainable parameters compared to full fine-tuning
- Overall performance across all tasks [74]
Protocol 2: Co-Directed Evolutionary Algorithm with Dynamic Archiving
Purpose To efficiently handle infeasible solutions in constrained optimization problems while leveraging constraint significance.
Experimental Setup
- Benchmark functions from IEEE CEC2006, CEC2010, or CEC2017
- Population size: 100-500 individuals
- Termination criterion: 100,000-500,000 function evaluations
Algorithmic Steps
- Initialization Phase
- Initialize population with random solutions within decision space bounds
- Evaluate objective function and constraint violations for each individual
- Initialize empty archive for promising infeasible solutions
Investigation Phase (performed periodically)
- Calculate significance of each constraint based on violation severity across population
- Update adaptive penalty function weights according to constraint significance
Evolutionary Phase
- Apply genetic operators (crossover, mutation) to generate offspring
- Evaluate offspring and update population using feasibility rules
- Dynamically adjust archive size based on current population diversity
- Select promising infeasible solutions for archiving based on objective value and constraint violation
Convergence Phase
- Implement shared replacement mechanism between archive and main population
- Apply local search around promising feasible regions
- Return best feasible solution found [26]
Performance Assessment
- Success rate in locating known global optima
- Convergence speed and solution quality
- Statistical testing (Wilcoxon signed-rank test) against benchmark algorithms [26]
Research Reagent Solutions
Table 1: Essential Computational Tools for Multi-Stage Optimization Research
| Tool Name | Type | Primary Function | Application Context |
|---|---|---|---|
| CLIP | Pre-trained Vision-Language Model | Backbone architecture for unified representation space | Multi-task learning frameworks requiring cross-modal understanding [75] |
| LoRA | Parameter-Efficient Fine-Tuning Method | Adds low-rank decomposition matrices to model weights | Adapting large models to multiple tasks with minimal parameter overhead [74] |
| TGLoRA | Custom Adapter Layer | Implements progressive task-specific adaptation | Multi-task learning with task grouping and knowledge sharing [74] |
| Dynamic Archive | Constraint Handling Mechanism | Stores valuable infeasible solutions | Constrained optimization with complex feasible regions [26] |
| Adaptive Penalty Function | Optimization Component | Assigns weights to constraints based on violation severity | Interpretable constrained optimization with varying constraint significance [26] |
| Gradient-Based Similarity Measure | Task Analysis Tool | Computes task relationships from gradient directions | Intelligent task grouping in multi-task learning systems [74] |
Workflow Visualization
Progressive Task-Specific Multi-Task Architecture
Constrained Optimization with Infeasible Solution Handling
Performance Comparison Tables
Table 2: Multi-Task Learning Performance Comparison on PASCAL Dataset
| Method | Number of Trainable Parameters | Relative Improvement Over Single-Task | Task Interference Metric | Inference Speed (tasks/sec) |
|---|---|---|---|---|
| Progressive Task-Specific (Proposed) | ~1/5 of full fine-tuning | Highest | Lowest | Medium |
| Individual Single-Task Adaptation | Medium | Low | None | Low |
| Shared Multi-Task Adaptation | Lowest | Medium | Highest | Highest |
| MTLoRA | Low | Medium | High | High |
| Fully Fine-Tuned Multi-Task | Full model | High | Medium | Highest [74] |
Table 3: Constrained Optimization Algorithm Performance on CEC2010 Benchmarks
| Algorithm | Success Rate (%) | Mean Function Evaluations | Constraint Violation Reduction | Statistical Significance (Wilcoxon p-value) |
|---|---|---|---|---|
| CdEA-SCPD (Proposed) | Highest | Lowest | Most Effective | < 0.05 |
| Standard Penalty Function | Low | High | Limited | > 0.05 |
| Adaptive Penalty (Population-Based) | Medium | Medium | Moderate | ~0.05 |
| Feasibility Rules Only | Medium | High | Variable | > 0.05 [26] |
Strategies for Problems with Large Infeasible Barriers
Frequently Asked Questions
1. What does "infeasible solution" mean in optimization? An infeasible solution is a set of values for the decision variables that violates at least one of the model's constraints. In contrast, a feasible solution satisfies all constraints, and the set of all such solutions is called the feasible region [77] [78].
2. Why should I care about how an algorithm handles infeasible solutions? The strategy for dealing with infeasible solutions is a critical algorithmic component that significantly impacts performance, disruptiveness, and population diversity [11]. Explicitly defining this strategy is essential for the reproducibility of your results. Without a standard approach, different implementations of the same algorithm can produce notably different outcomes, making findings difficult to verify or compare [11].
3. My model is infeasible. How can I diagnose the problem? An Infeasibility Diagnostic Engine is a great starting point. This tool works by adding slack variables to all constraints and then solving a new optimization problem that minimizes the sum of these violations. The results pinpoint which constraints are violated and by how much, providing a clear direction for troubleshooting [67].
4. Are there real-world applications for these methods in health and drug development? Yes. Constrained optimization methods are widely used in health services research and pharmaceutical development. For example, they can determine the optimal mix of screening and vaccination strategies for preventing cervical cancer or find the best treatment strategy for patients with type 2 diabetes and hypercholesterolemia [79] [80].
5. What is the difference between a local and a global optimal solution? A global optimal solution is a feasible solution where no other feasible solution in the entire search space has a better objective function value. A local optimal solution is one where no other feasible solution in its immediate "vicinity" has a better objective value. Some solvers are designed to find global optima, but this is not always possible [77].
Troubleshooting Guide: Diagnosing Infeasibility
| Step | Action | Description & Expected Outcome |
|---|---|---|
| 1 | Run an Infeasibility Diagnostic [67] | Use a tool to automatically identify violated constraints. Outcome: A report listing which constraints are broken and the magnitude of their violation. |
| 2 | Audit Constraint Logic | Manually check the formulation of your constraints for mathematical errors. Outcome: Corrected model logic that accurately represents the real-world problem. |
| 3 | Check for Conflicting Constraints | Analyze if two or more constraints cannot be satisfied simultaneously. Outcome: Identification of a "show-stopper" conflict that must be resolved by relaxing one of the constraints. |
| 4 | Review Variable Bounds | Ensure that the lower and upper bounds placed on your decision variables are reasonable and do not artificially rule out feasible solutions. Outcome: A more realistic search space for the algorithm. |
| 5 | Validate Input Data | Scrutinize all parameters and constants used in your constraints for accuracy. Outcome: Elimination of infeasibility caused by incorrect data entry or processing. |
The following workflow outlines a systematic approach for diagnosing and resolving infeasibility in your optimization models:
The Scientist's Toolkit: Research Reagents & Solutions
The table below details key computational components used in advanced evolutionary optimization research, such as automated model merging [81].
| Research Component | Function & Explanation |
|---|---|
| Evolutionary Algorithm (e.g., CMA-ES) | A population-based optimization heuristic used to search for high-quality solutions by iteratively generating and selecting candidate solutions. |
| Infeasibility Diagnostic Engine | A solver tool that adds slack variables to constraints to identify which ones are causing infeasibility and quantifies the violations [67]. |
| Task Vectors | In model merging, a vector is created by subtracting a pre-trained model's weights from a fine-tuned model's weights, representing the "direction" of learning for a specific task [81]. |
| Model Merging (Parameter Space) | A technique to create a new model by combining the weights of multiple existing models, often using linear methods like weighted averaging [81]. |
| Model Merging (Data Flow Space) | A technique that creates a new model by defining a novel inference path that routes data through layers of multiple existing models, leaving their original weights untouched [81]. |
| Slack Variables | Auxiliary variables added to constraints to transform an infeasible model into a feasible one by absorbing the violation, which is then minimized [67]. |
Experimental Protocol: Evolutionary Model Merging
The following methodology is adapted from state-of-the-art research in evolutionary optimization for automatically merging machine learning models [81].
1. Problem Definition & Setup
- Objective: Automatically generate a merged foundation model from a collection of existing models that outperforms any individual model on a specified set of tasks.
- Input: A collection of N pre-trained foundation models.
- Search Spaces: Define two orthogonal spaces for exploration:
- Parameter Space (PS): The space of model weights. The goal is to find an optimal combination of these weights.
- Data Flow Space (DFS): The space of inference paths. The goal is to find an optimal path for data to travel through the layers of the different models.
2. Optimization in Parameter Space (PS)
- Representation: For each layer of the model (e.g., each transformer block), establish merging configuration parameters. These can include sparsification thresholds and weight mixing coefficients.
- Algorithm: Use an evolutionary algorithm, such as Covariance Matrix Adaptation Evolution Strategy (CMA-ES), to optimize these configuration parameters.
- Fitness Function: The performance of the merged model on selected benchmark tasks, measured by task-specific metrics (e.g., accuracy for math problems, ROUGE score for question answering).
3. Optimization in Data Flow Space (DFS)
- Representation: Define an indicator array that specifies the sequence of layers (from any of the N models) that the data will pass through during inference. This creates a new, complex model architecture from existing components.
- Algorithm: Employ an evolutionary algorithm to search the space of possible data flow paths. Due to the vast search space, heuristics are used to make the search tractable (e.g., by limiting the search to certain layer arrangements).
- Key Feature: In this space, the original weights of all models remain unchanged; only the path of the data is optimized.
4. Validation and Analysis
- The best-performing merged models from the evolutionary search are evaluated on held-out test sets to validate their performance and generalizability.
- The process can generate novel, cross-domain models (e.g., a Japanese LLM with math reasoning capabilities) that achieve state-of-the-art performance [81].
Performance Validation and Comparative Analysis of Constraint Handling Techniques
This technical support center provides guidance for researchers working with standard benchmark problems in constrained evolutionary optimization. A central challenge in this field is effectively handling infeasible solutions—candidate answers that violate some of the problem's constraints. This guide, framed within broader thesis research on managing infeasibility, offers troubleshooting and FAQs to assist scientists, particularly those in drug development, in configuring and executing experiments on the widely used CEC2006, CEC2010, and CEC2017 test suites. These suites provide a standard set of constrained, single-objective, real-parameter optimization problems for benchmarking algorithm performance [82] [3] [83].
Benchmark Suite Specifications
The table below summarizes the core characteristics of the three major CEC test suites for constrained optimization.
| Test Suite | Number of Problems | Problem Types | Key Features | Common Application in Research |
|---|---|---|---|---|
| CEC 2006 | 24 Problems [82] [83] | Single-objective, Constrained, Continuous [82] | Established, widely used benchmark; provides a foundation for later suites [83]. | Foundational algorithm comparison; testing basic constraint-handling techniques [83]. |
| CEC 2010 | 36 Test Instances [83] | Constrained Real-Parameter Optimization [83] | More specialized and complex test instances compared to CEC2006 [83]. | Evaluating algorithm scalability and performance on more complex, modern problems [83]. |
| CEC 2017 | 28 Constrained Optimization Problems [3] | Constrained Real-Parameter Optimization [3] | Used for evaluating modern algorithms; includes real-world problem applications [3]. | Testing state-of-the-art algorithms; validating methods on real-world engineering and design problems [3]. |
Common Experimental Challenges & Solutions (FAQs)
FAQ 1: My evolutionary algorithm fails to find any feasible solutions on several test problems. What is the root cause and how can I address this?
This common issue often stems from an imbalance in how your algorithm handles the trade-off between objective function performance and constraint satisfaction [3].
- Root Cause: The algorithm is overly penalizing infeasible solutions, prematurely discarding them before they can guide the search towards the feasible region boundary where the optimum often lies [3] [83].
- Solution Strategies:
- Implement an Infeasible-Feasible Regions Method: Adopt a multi-stage approach. The first stage should focus on searching the boundary between infeasible and feasible regions, encouraging discovery of the feasible space. The second stage can then use a method like the self-adaptive Epsilon constraint to refine feasible solutions [3].
- Use a Diversity Controller: To prevent premature convergence, integrate a mechanism to control population diversity, such as one based on a small-world network. This helps maintain exploration capability, making it more likely to discover feasible regions [3].
- Adopt a Multi-Operator Framework: No single evolutionary operator works best on all problems. Use a self-adaptive algorithm that employs multiple search operators (mutation, crossover) simultaneously. The sub-populations using each operator can adapt in size based on their success, dynamically tailoring the search strategy [83].
FAQ 2: How can I diagnose the specific constraints causing infeasibility in a solution during an experiment?
Diagnosing infeasibility is critical for both optimizing your algorithm and understanding problem structure.
- Analyze Constraint Violations: For an infeasible solution, calculate its constraint violation vector. The mathematical formulation for the total violation is typically:
G(x) = Σ max(g_i(x), 0) + Σ max(|h_j(x)| - δ, 0), whereg_i(x)are inequality constraints,h_j(x)are equality constraints, andδis a small tolerance (e.g., 0.0001) [3]. Inspecting individual terms in this sum pinpoints the most-violated constraints. - Concept of Conflict Sets: In mathematical programming, an Irreducible Inconsistent Subsystem (IIS) is a minimal set of constraints that, together, are infeasible. If any single constraint is removed from the IIS, the set becomes feasible. While directly finding an IIS may not be standard in all evolutionary algorithms, the concept is invaluable for understanding that infeasibility is often caused by a small, core set of conflicting constraints [2] [1].
FAQ 3: What are the primary methodological approaches for handling constraints within these benchmarks?
Researchers have developed several classes of Constraint Handling Techniques (CHTs). The table below summarizes the most common ones.
| Methodology | Core Principle | Advantages | Disadvantages |
|---|---|---|---|
| Feasibility Rules | Prioritizes feasible solutions; compares infeasible ones based on their constraint violation only [3] [83]. | Simple to implement and computationally efficient [83]. | May stagnate if feasible region is hard to find; can discard promising infeasible solutions. |
| Ɛ-Constrained Method | Relaxes feasibility by using a dynamic tolerance (Ɛ). Solutions with violation ≤ Ɛ are compared as feasible [3]. | Systematically balances objective and violation; gives more attention to objective function information [3]. | Performance sensitive to the schedule for reducing Ɛ to zero. |
| Stochastic Ranking | Sets a probability to choose between comparing individuals by objective function or by constraint violation [3]. | Provides a balanced trade-off between objective and constraints without hard rules. | The ranking probability is a parameter that may need tuning. |
| Penalty Functions | Combines objective value and constraint violation into a single metric using penalty coefficients [3]. | Conceptually straightforward, transforms a COP into an unconstrained one. | Performance highly depends on the choice of penalty coefficients, which can be difficult to set [3]. |
| Multi-Objective Methods | Treats constraints as additional objectives to be minimized [3]. | Leverages powerful multi-objective algorithms; maintains diversity. | Can be computationally intensive; transforms one problem into a more complex one [3]. |
Methodological Workflows
The following diagrams illustrate two advanced methodologies for handling infeasible solutions, as discussed in recent research.
Diagram 1: Infeasible-Feasible (IF) Boundary Search Workflow.
Diagram 2: Self-Adaptive Multi-Strategy Differential Evolution (SAMSDE).
The Scientist's Toolkit: Research Reagent Solutions
This table details key algorithmic components and software "reagents" essential for experiments with these benchmark suites.
| Tool / Component | Category | Function in Experiment | Example / Implementation Note |
|---|---|---|---|
| Diversity Controller (DC) [3] | Algorithmic Component | Controls population diversity to avoid premature convergence, using metrics like small-world network dynamics. | Dynamically adjusts the reconnection probability in a network based on fitness-distance correlation. |
| SHADE Algorithm [3] | Base Optimizer | A state-of-the-art Differential Evolution (DE) variant serving as a powerful search engine for COPs. | Often used as a foundation algorithm, enhanced with specialized constraint-handling methods. |
| Infeasible-Feasible (IF) Method [3] | Constraint-Handing Technique | A two-stage method that first searches for feasibility boundaries, then refines solutions. | Stage 1 targets the boundary; Stage 2 uses a self-adaptive Epsilon method. |
| Self-Adaptive Multi-Operator DE [83] | Algorithmic Framework | Employs multiple mutation/crossover strategies simultaneously, adapting their use based on performance. | Allocates more computational resources to the most successful search operators as the run progresses. |
| CPLEX / Gurobi [2] [1] | Mathematical Programming Solver | Used for feasibility analysis, conflict refinement, and as a benchmark for certain problem types. | Can compute Irreducible Inconsistent Subsystems (IIS) to explain infeasibility. |
| Slack Variables [2] [1] | Modeling Technique | Transforms hard constraints into soft constraints by allowing controlled violations, which are penalized. | Prevents model infeasibility; essential for modeling real-world scenarios with flexible constraints. |
Performance Metrics for Constrained Multi-Objective Optimization
Frequently Asked Questions (FAQs)
Q1: What are the primary challenges when evaluating solutions for Constrained Multi-Objective Optimization Problems (CMOPs)?
Evaluating solutions for CMOPs requires balancing two competing aspects: the quality of the objectives (convergence to the true Pareto front) and the satisfaction of all constraints. The primary goal is to find a set of feasible solutions that are close to the true Pareto front (good convergence), well-distributed along it (good diversity), and that cover its full extent (good spread) [84]. The key challenge is that the true Pareto front is often unknown, so metrics must assess the quality of an approximate front without this reference.
Q2: What is the critical first step in calculating performance metrics for a solution set?
The first and most critical step is to calculate the constraint violation for every solution in the set [55]. A solution is considered feasible only if it adheres to all constraints. The total constraint violation for a decision variable x is computed as the sum of its violations concerning each inequality and equality constraint. For an equality constraint, a small positive tolerance δ is often used to relax the strictness [55]. Any solution with a total constraint violation greater than zero is infeasible and typically should not be considered in the final evaluation of a Pareto front approximation.
Q3: My algorithm finds solutions with excellent objective values, but many are infeasible. How can metrics guide the improvement of constraint handling?
Performance metrics can diagnose this issue. A significant gap between the Unconstrained Pareto Front (UPF)—found by ignoring constraints—and the Constrained Pareto Front (CPF)—the actual goal—indicates challenging constraints [85]. Metrics should be used to track the performance of the feasible population separately. If metrics like the Hypervolume of the feasible population are poor, while the overall population (including infeasible solutions) shows good convergence, your constraint-handling technique needs refinement. Research has shown that classifying the relationship between the UPF and CPF can help select the most effective search strategy [85].
Q4: Which performance indicator is generally considered the most comprehensive for comparing algorithms?
The Hypervolume indicator is widely regarded as one of the most relevant metrics [84]. It measures the volume of the objective space dominated by an approximation set, bounded by a reference point. Its key advantage is that it simultaneously captures convergence, diversity, and spread—if one approximation set achieves a higher hypervolume than another, it is better in terms of convergence and diversity. However, its computational cost increases with the number of objectives, and the choice of reference point can influence the result [84].
Q5: How can I visualize the relationship between unconstrained and constrained search spaces?
The relationship can be visualized by plotting the Unconstrained Pareto Front (UPF) and the Constrained Pareto Front (CPF) together in the objective space. The diagram below illustrates the three primary classifications of this relationship.
Q6: Are there specific metrics for assessing the diversity and spread of a Pareto front approximation?
Yes, many metrics focus solely on distribution characteristics. Distribution and Spread Indicators quantify how uniformly and widely the points are distributed in the objective space [84]. Examples include the Spacing metric, which measures the spread of solutions, and the Spread (Δ) metric, which assesses both the distribution and extent of the front. These are crucial because a good algorithm should provide the decision-maker with a wide range of well-distributed trade-off options [84].
Performance Metrics Reference Tables
The following tables summarize key performance indicators, categorized by their primary property.
Table 1: Comprehensive List of Performance Indicators for Multi-Objective Optimization
| Category | Indicator Name | Primary Purpose | Key Strengths | Key Limitations |
|---|---|---|---|---|
| Cardinality [84] | Number of Pareto Points | Counts non-dominated solutions. | Simple, intuitive. | Does not assess quality of solutions. |
| Ratio of Non-dominated Points | Measures proportion of non-dominated solutions. | Provides a relative measure. | Sensitive to the reference set. | |
| Convergence [84] | Generational Distance (GD) | Measures average distance from approximation to true PF. | Simple, low computational cost. | Requires knowledge of the true PF. |
| Inverted Generational Distance (IGD) | Measures average distance from true PF to approximation. | Assesses both convergence and diversity. | Requires knowledge of the true PF. | |
| epsilon-Indicator | Measures smallest distance needed to transform approximation to dominate true PF. | Comprehensive, can be used without true PF. | More complex to compute. | |
| Distribution & Spread [84] | Spacing | Measures spread of solutions based on distance variance. | Assesses distribution uniformity. | Does not measure convergence. |
| Spread (Δ) | Measures extent and distribution of the front. | Combines spread and distribution. | Requires extreme points of the true PF. | |
| Hypervolume (HV) | Measures dominated volume. | Captures convergence, diversity, and spread in one metric. Unary and compliant. | Computationally expensive; choice of reference point affects results [84]. |
Table 2: Key Formulae for Prominent Performance Metrics
| Metric | Formula | Parameters | ||
|---|---|---|---|---|
| Constraint Violation (CV) [55] | ( CV(\vec{x}) = \sum{i=1}^{l+k} cv{i}(\vec{x}) ) ( cv{i}(\vec{x}) = \begin{cases} \max(0, g{i}(\vec{x})), & i=1,\ldots,l \ \max(0, \left | h_{i}(\vec{x}) \right | -\delta ), & i=1,\ldots,k \end{cases} ) | (gi): inequality constraints; (hi): equality constraints; (\delta): tolerance |
| Hypervolume (HV) [84] | ( HV(S) = \Lambda(\bigcup_{\vec{x} \in S} { \vec{y} \in \mathbb{R}^m | \vec{x} \preceq \vec{y} \preceq \vec{r} }) ) | (S): solution set; (\Lambda): Lebesgue measure; (\vec{r}): reference point | ||
| Inverted Generational Distance (IGD) | ( IGD(S, P^*) = \frac{1}{ | P^* | } \sum{\vec{v} \in P^*} \min{\vec{s} \in S} \text{dist}(\vec{v}, \vec{s}) ) | (S): approximation set; (P^*): true Pareto front; dist: distance function (e.g., Euclidean) |
Standard Experimental Protocol for Benchmarking
This section outlines a standard methodology for evaluating and comparing Constrained Multi-Objective Evolutionary Algorithms (CMOEAs) using the performance metrics described above.
Workflow Overview
The diagram below illustrates the end-to-end experimental process for benchmarking CMOEAs, from problem definition to result analysis.
Step-by-Step Protocol
Problem Definition: Select a diverse suite of CMOP benchmark test problems. These problems should have different characteristics, such as variable dimensionality, shape of the Pareto front, and complexity of constraints (e.g., separable/non-separable, linear/nonlinear) [55]. This ensures the algorithms are tested under various conditions.
Algorithm Selection: Choose the CMOEAs to be compared. These typically include state-of-the-art algorithms and classic baselines. Each algorithm should be configured with its recommended parameter settings as reported in the literature to ensure a fair comparison.
Experimental Runs: Execute each selected algorithm on every benchmark problem. Each run should use the same termination criterion to ensure fairness. Common criteria include a fixed number of objective function evaluations or a pre-defined computational time. To account for the stochastic nature of evolutionary algorithms, perform a sufficient number of independent runs (e.g., 20 or 30) for each algorithm-problem pair [84].
Data Collection: From each run, save the final approximated Pareto front after the termination criterion is met. This set of non-dominated solutions is the primary data for subsequent performance analysis.
Metric Calculation: Calculate the selected performance metrics for the final approximation set from each run. For metrics like Hypervolume, consistently use the same reference point for a given problem. If a metric requires the true Pareto front (e.g., IGD), use a pre-computed set of points that well-approximate the true PF for the benchmark problem.
Statistical Analysis: Perform statistical tests to determine the significance of the observed performance differences. Non-parametric tests like the Wilcoxon rank-sum test are commonly used to compare the results of two algorithms across multiple independent runs. Present the median, mean, and standard deviation of the metrics.
Result Visualization: Generate visualizations to intuitively present the results. Key visualizations include:
- Box plots of metric values across multiple runs.
- Scatter plots of the final approximated Pareto fronts in the objective space for representative runs, which allow for direct visual comparison of convergence and diversity.
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Computational Components for CMOEA Research
| Component / "Reagent" | Function / Purpose | Example Implementation |
|---|---|---|
| Constraint Violation Calculator | Computes the total degree of constraint violation for any solution, classifying it as feasible or infeasible [55]. | Implement Eq. (2) and (3) from the background section, using a small δ (e.g., 1e-6) for equality constraints. |
| Feasibility Rule | A simple yet powerful CHT that prioritizes feasible over infeasible solutions, and among infeasible solutions, prefers the one with a lower constraint violation [55]. | if (CV(x1)==0 and CV(x2)==0) compare by Pareto dominance; else if (CV(x1) < CV(x2)) x1 is better; else x2 is better; |
| ε-Constraint Handling | A more flexible CHT that allows some infeasible solutions with good objective values to be considered, helping to cross infeasible regions [55]. | Relax the feasibility condition by an ε parameter that decreases to zero over the run, allowing initially infeasible solutions to be considered if their CV < ε. |
| Dual-Population Framework | A sophisticated algorithmic structure using two populations: one to explore the UPF and another to search for the CPF, enabling adaptive search strategies [85]. | Maintain an auxiliary population (Pa) that ignores constraints and a main population (Pm) that respects constraints. Use knowledge from Pa to guide Pm based on the UPF-CPF relationship. |
| Stochastic Ranking | A method for balancing objectives and constraints by probabilistically ranking solutions based on their objective values or their constraint violations [55]. | Rank the population by a bubble-sort where two solutions are compared based on objective fitness with probability Pf and based on constraint violation with probability (1-Pf). |
Within the domain of constrained evolutionary optimization, a central challenge is the effective management of infeasible solutions—those candidate answers that violate one or more problem constraints. The strategy employed to handle these solutions is pivotal, as it directly influences the algorithm's ability to locate high-quality, feasible optima, particularly when these lie on complex constraint boundaries. This guide, framed within a broader thesis on constrained optimization, provides a practical resource for researchers tackling these issues in experimental settings. We focus on three predominant strategies: Penalty Functions, which discourage infeasibility by degrading objective function value; Feasibility Rules, which prioritize feasible solutions through selection; and Multi-Objective Methods, which recast constraints as separate objectives to be optimized.
The performance of an optimization algorithm is known to be largely dependent on its constraint-handling mechanism [14]. Often, optimal solutions to real-world problems lie on constraint boundaries, making the approach to these boundaries—from either the feasible or infeasible side—a critical factor in convergence speed and solution quality [14] [86]. This document provides troubleshooting guides and FAQs to address specific issues encountered when implementing these methods.
Core Methodologies & Comparative Analysis
This section breaks down the core methodologies, presenting their mechanisms, advantages, and inherent challenges in a structured format for easy reference and comparison.
Penalty Function Methods
Mechanism: Penalty functions add a punitive term to the objective function for any constraint violation, effectively transforming a constrained problem into an unconstrained one. The severity of the penalty can be static or dynamic.
- Typical Workflow:
- Evaluate the objective function, ( f(\vec{x}) ), for a solution ( \vec{x} ).
- Calculate the total constraint violation, ( \phi(\vec{x}) ).
- Construct a penalized objective function: ( F(\vec{x}) = f(\vec{x}) + P(\phi(\vec{x})) ), where ( P ) is the penalty function.
- Proceed with evolutionary selection based on ( F(\vec{x}) ).
Feasibility Rules (e.g., Death Penalty)
Mechanism: This is a straightforward feasibility-first approach. In its simplest "death penalty" form, any infeasible solution is immediately rejected from the population [87].
- Typical Workflow:
- Evaluate the feasibility of a solution ( \vec{x} ).
- If ( \vec{x} ) is feasible, evaluate its objective function ( f(\vec{x}) ) and retain it.
- If ( \vec{x} ) is infeasible, discard it ("death penalty") or assign it a poor rank compared to any feasible solution.
Multi-Objective Methods
Mechanism: These methods treat constraint satisfaction as one or more separate objectives. A common approach is to use the degree of constraint violation as an additional objective, turning a single-objective constrained problem into an unconstrained multi-objective problem where the goals are to optimize the original objective and minimize violation [14].
- Typical Workflow:
- For each solution ( \vec{x} ), calculate the objective function ( f(\vec{x}) ) and a measure of constraint violation ( \phi(\vec{x}) ).
- Use a multi-objective evolutionary algorithm (e.g., NSGA-II) to simultaneously optimize for ( f(\vec{x}) ) and ( \phi(\vec{x}) ).
- The final output is a Pareto front of solutions trading off objective performance and constraint violation, from which the feasible solution with the best ( f(\vec{x}) ) can be selected.
Structured Comparison of Methods
The table below provides a quantitative and qualitative summary of the three core methods, synthesizing information from the search results to aid in selection.
Table 1: Structured Comparison of Constraint-Handling Techniques
| Method | Key Mechanism | Reported Performance | Primary Advantages | Primary Challenges |
|---|---|---|---|---|
| Penalty Functions | Adds a penalty term to the objective function based on violation severity. | Highly sensitive to penalty parameter tuning; can outperform with correct settings [87]. | Simple to implement; transforms problem to unconstrained. | Choosing appropriate penalty parameters is difficult; poor parameters lead to premature convergence or inability to find feasible solutions. |
| Feasibility Rules (e.g., Death Penalty) | Strictly prefers any feasible solution over any infeasible one. | Works well when feasible region is convex and large [87]. Fails when feasible region is small or disconnected. | Very simple and computationally efficient. | Performs poorly when feasible regions are hard to find (e.g., small or disconnected); may get stuck. |
| Multi-Objective & Advanced Methods (e.g., IDEA) | Treats constraint violation as a separate objective to optimize. | IDEA showed better convergence than NSGA-II on test problems [14]. Maintains infeasible solutions near boundaries. | Can approach constraints from both sides; provides trade-off solutions; robust on complex boundaries. | Increased algorithmic complexity; requires management of a bi-objective Pareto front. |
The Scientist's Toolkit: Research Reagent Solutions
This table details key algorithmic components and their functions, analogous to research reagents in a wet lab, that are essential for implementing the discussed constraint-handling methods.
Table 2: Essential "Research Reagents" for Constrained Evolutionary Optimization
| Reagent / Component | Function in the Experiment | Key Considerations |
|---|---|---|
| Infeasible Solution Archive | Maintains a small population of "good" infeasible solutions close to constraint boundaries [14] [86]. | Crucial for IDEA; allows approach to optimum from infeasible side. Percentage kept in population is a key parameter. |
| Constraint Violation Measure (( \phi(\vec{x}) )) | Quantifies the total magnitude by which a solution ( \vec{x} ) violates all constraints. | Serves as the second objective in multi-objective methods and the basis for penalty functions. Normalization of different constraints is important. |
| Pareto Ranking Mechanism | Ranks solutions based on non-domination in both objective function ( f(\vec{x}) ) and constraint violation ( \phi(\vec{x}) ) [14]. | Core to multi-objective methods; allows balanced progress towards feasibility and optimality. |
| Dynamic Penalty Scheduler | Adjusts penalty parameters over the course of the evolutionary run [87]. | Aims to overcome the parameter-tuning problem in static penalty functions. |
Troubleshooting Guides & FAQs
Frequently Asked Questions
Q1: My optimization algorithm consistently fails to find any feasible solutions. What could be the cause and how can I address this?
- A: This is a common issue, particularly when using feasibility rules like the death penalty on problems where the feasible region is small or hard to locate [87]. The "death penalty" method simplifies the algorithm but has serious limitations when the initial population consists entirely of infeasible individuals [87].
- Solution: Switch from a feasibility-first rule to a method that actively uses infeasible solutions, such as the Multi-Objective approach or the Infeasibility Driven Evolutionary Algorithm (IDEA). These methods rank "good" infeasible solutions higher than poor feasible ones, providing selection pressure towards the feasible region [14] [86]. Alternatively, implement a dynamic penalty function that starts with low penalties to allow exploration of the infeasible space and gradually increases penalties to steer the population towards feasibility.
Q2: How does maintaining infeasible solutions, as in IDEA, improve performance compared to always preferring feasible ones?
- A: Most algorithms drive the population to feasibility first before optimizing the objective function, approaching constraint boundaries only from the feasible side. By explicitly maintaining a small percentage of marginally infeasible solutions, the algorithm can approach the optimal solution from both sides of the constraint boundary [14] [86]. This dual approach, especially in problems where the optimum lies on a boundary, often leads to a better rate of convergence. Furthermore, these marginally infeasible solutions are valuable for trade-off studies, showing what performance could be gained if constraints were relaxed slightly [14].
Q3: What is a key advantage of treating constraints via a multi-objective method compared to a penalty function?
- A: The primary advantage is the elimination of the need to carefully tune penalty parameters. Penalty functions are notoriously sensitive to their parameter settings; too weak a penalty and the population remains infeasible, too strong and it converges prematurely [87]. Multi-objective methods avoid this by treating constraint violation as a separate, competing objective. The algorithm then naturally finds a set of solutions representing the trade-off between performance and feasibility, from which the best feasible solution can be chosen.
Advanced Protocol: Implementing the IDEA Framework
The Infeasibility Driven Evolutionary Algorithm (IDEA) is a sophisticated protocol that effectively blends multi-objective principles with strategic retention of infeasible solutions. Below is a detailed methodology for implementing it, based on the cited research.
Aim: To enhance convergence in constrained optimization by explicitly maintaining and leveraging marginally infeasible solutions during evolution.
Detailed Methodology:
Initialization: Generate an initial random population of candidate solutions. Evaluate both the objective function ( f(\vec{x}) ) and the constraint violation function ( \phi(\vec{x}) ) for each individual.
Ranking and Selection:
- Combine and Rank: Combine parent and offspring populations. Instead of ranking based solely on ( f(\vec{x}) ) or feasibility, rank the combined population based on a modified multi-objective sorting. The two objectives are the original function ( f(\vec{x}) ) and the constraint violation ( \phi(\vec{x}) ) [14].
- Drive with Infeasibility: Crucially, during this ranking, "good" infeasible solutions (those with a low ( f(\vec{x}) ) and low ( \phi(\vec{x}) )) are ranked higher than feasible solutions with poor objective function values [14]. This focuses the search near promising constraint boundaries.
Population Maintenance for Next Generation:
- Select the top-ranked solutions to form the next generation.
- The algorithm explicitly ensures that a small, predefined percentage (e.g., 5%) of the new population consists of the best-performing infeasible solutions (those with the best ( f(\vec{x}) ) among infeasibles) [86]. This guarantees that information from the infeasible region near boundaries is preserved.
Termination and Output: Repeat steps 2-3 until a termination criterion is met (e.g., max iterations). The final output includes both the best feasible solution and a set of high-quality, marginally infeasible solutions for further analysis.
The workflow for this protocol is visualized below.
Troubleshooting Guides for Constrained Optimization
Welded Beam Design Optimization
Problem: Solver fails to find a feasible solution.
- Potential Cause 1: Initial design parameters violate geometric or stress constraints.
- Solution: Check that initial values satisfy simple geometric constraints first (e.g., weld thickness
x1≤ beam widthx4) [88]. - Potential Cause 2: Overly restrictive variable bounds prevent exploration of feasible regions.
- Solution: Implement a boundary update (BU) method to dynamically adjust variable bounds, cutting the infeasible search space over iterations [40].
Problem: Optimization results in an infeasible design with high constraint violation.
- Potential Cause: Algorithm is trapped in an infeasible region.
- Solution: Employ a two-stage approach. First, use a feasibility-oriented method like the Infeasible–Feasible (IF) regions constraint handling method to locate feasible boundaries. Then, switch to objective optimization while maintaining feasibility [3].
Problem: Poor convergence or solver performance on constrained problems.
- Potential Cause: Ineffective balancing of exploration and exploitation.
- Solution: Integrate a diversity controller (DC) based on a small-world network to maintain population diversity and prevent premature convergence [3].
Pressure Vessel Design Optimization
Problem: Design violates ASME BPVC standards after modification.
- Potential Cause: Changes in service conditions (contents, pressure, temperature) were not properly re-evaluated.
- Solution: Before any change, determine the original design basis and compare with new conditions. Perform engineering evaluation to ensure new loadings don't exceed original design loadings [89].
Problem: Relocated vessel fails inspection or exhibits performance issues.
- Potential Cause: New environmental conditions (wind loads, corrosive atmospheres) or attachment loads not considered.
- Solution: Review original design considerations from UG-22 of ASME Section VIII, Division 1, including weight of attachments, motors, agitators, and attached piping loads [89].
Frequently Asked Questions (FAQs)
Q1: What are the most effective constraint-handling techniques for engineering design problems like the welded beam?
A1: Research indicates several effective strategies:
- Hybrid methods that combine multiple techniques often outperform single-method approaches [8] [3].
- Multi-objective optimization transforms constrained problems into multi-objective ones, treating constraints as additional objectives [8] [3].
- EALSPM framework uses classification-collaboration constraint handling, decomposing original problems into subproblems with coordinated subpopulations [8].
Q2: How can I handle problems where the feasible region is very small or difficult to find?
A2: Advanced techniques include:
- Boundary Update (BU) with switching mechanisms: An implicit method that cuts infeasible search space, then switches to normal optimization once feasible region is found [40].
- Infeasible-Feasible regions approach: Specifically searches the boundary between infeasible and feasible regions in the first stage [3].
- Universal Constrained Preference Optimization (UCPO): A preference-based framework that embeds constraint satisfaction directly into the optimization objective [10].
Q3: What are common pitfalls when applying evolutionary algorithms to constrained engineering problems?
A3: Key pitfalls include:
- Over-reliance on penalty functions without proper parameter tuning [8] [10].
- Neglecting population diversity leading to premature convergence [3].
- Using generic algorithms without problem-specific customization [8].
Q4: How should pressure vessel redesign or relocation be properly managed?
A4: Essential steps include:
- Jurisdictional review: Consult the chief inspector of the relevant jurisdiction before proceeding [89].
- Comprehensive engineering analysis: Evaluate all original design considerations including pressure load, weight of attachments, and environmental factors [89].
- Professional fabrication: Use National Board "R" Certificate of Authorization holders for required modifications [89].
Experimental Protocols & Methodologies
Table 1: Welded Beam Design Optimization Formulation
| Component | Mathematical Formulation | Parameters |
|---|---|---|
| Design Variables | x = [h, l, t, b] = [x1, x2, x3, x4] |
- |
| Objective 1 (Cost) | F1(x) = 1.10471x1²x2 + 0.04811x3x4(14 + x2) [88] |
C = 4(14)³/(30×10⁶) ≈ 3.6587×10⁻⁴ [88] |
| Objective 2 (Deflection) | F2(x) = P/(x4x3³C) [88] |
P = 6,000 lbs [88] |
| Constraints | Shear stress τ(x) ≤ 13,600 psi [88] |
L = 14 in [88] |
| Variable Bounds | 0.125 ≤ x1 ≤ 5, 0.1 ≤ x2 ≤ 100.1 ≤ x3 ≤ 10, 0.125 ≤ x4 ≤ 5 [88] |
- |
Table 2: Pressure Vessel Key Design Considerations
| Aspect | Design Requirements | Standards Reference |
|---|---|---|
| Material Selection | Stainless steel (corrosion resistance), Carbon steel (cost-effectiveness) [90] | ASME BPVC Section II [90] |
| Fabrication Process | Cutting/forming, Welding (TIG, MIG, Laser, Submerged-arc), Inspection [90] | ASME BPVC Section VIII, IX [90] |
| Testing & Inspection | Ultrasonic Testing, Radiography, Hydrostatic testing [90] | ASME BPVC [90] |
| Constraint Types | Physical, Geometrical, Operational [40] | - |
Protocol 1: Multi-Objective Optimization with paretosearch and gamultiobj
- Problem Formulation: Define objective functions and nonlinear constraints as separate function handles [88].
- Solver Configuration: Set options for multi-objective solvers:
- Initial Point Strategy: Start from single-objective solutions obtained with
fminconto improve solver performance [88]. - Performance Analysis: Compare solution quality and function evaluation counts between different solvers [88].
Protocol 2: EALSPM for Complex Constrained Problems
- Constraint Classification: Randomly classify constraints into K classes, decomposing the original problem into K subproblems [8].
- Subpopulation Setup: Generate K subpopulations, each corresponding to a subproblem [8].
- Two-Stage Evolution:
- Predictive Modeling: Use an improved continuous domain estimation of distribution model based on high-quality individuals to predict offspring [8].
Workflow Visualization
Welded Beam Optimization Process
Pressure Vessel Design Assurance
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Optimization Algorithms & Techniques
| Tool | Type | Function | Application Context |
|---|---|---|---|
| paretosearch | Multi-objective solver [88] | Finds Pareto-optimal solutions [88] | Welded beam cost-deflection tradeoff [88] |
| gamultiobj | Genetic algorithm solver [88] | Evolutionary multi-objective optimization [88] | Alternative approach for welded beam [88] |
| EALSPM | Evolutionary algorithm framework [8] | Uses learning strategies and predictive model [8] | Complex COPs with multiple constraints [8] |
| DC-SHADE-IF | Constrained optimization approach [3] | Diversity controller with infeasible-feasible method [3] | Balancing exploration-exploitation tradeoff [3] |
| Boundary Update | Implicit constraint handling [40] | Dynamically adjusts variable bounds [40] | Finding feasible regions faster [40] |
| UCPO | Preference optimization framework [10] | Universal constrained combinatorial optimization [10] | Handling hard constraints without masking [10] |
Statistical Validation and Significance Testing of Algorithm Performance
This technical support center provides troubleshooting guides and FAQs for researchers, scientists, and drug development professionals working on the statistical validation of algorithms, particularly within the context of a thesis on handling infeasible solutions in constrained evolutionary optimization.
Troubleshooting Guide: Common Experimental Challenges
1. Problem: High Rate of Infeasible Solutions in Evolutionary Algorithms
- Question: "My constrained evolutionary algorithm (CEA) is producing a high number of infeasible solutions, stalling convergence. What strategies can I use?"
- Answer: A high proportion of infeasible solutions often indicates that the algorithm is not effectively navigating the problem's constraints. This is a known critical component affecting performance, disruptiveness, and population diversity [11].
- Methodology: Implement an adaptive penalty function that assigns different weights to constraints based on their violation severity, rather than treating all constraints equally. This enhances interpretability and guides the population more rapidly toward feasible, optimal regions [26].
- Actionable Protocol:
- Analyze Constraint Significance: During the evolution process, spontaneously investigate the "significance of each constraint." Calculate the degree of violation for each constraint for every individual.
- Assign Dynamic Weights: Develop a penalty function that assigns higher penalty coefficients to constraints with more severe violations.
- Archive Infeasible Solutions: Use a dynamic archiving strategy to store high-quality infeasible solutions (e.g., those with good objective function values or that violate constraints only slightly). This helps maintain population diversity and provides information about the feasible region's boundaries [26].
- Expected Outcome: This approach, as demonstrated in the CdEA-SCPD algorithm, leads to more interpretable optimization and faster convergence toward the global optimum on benchmark problems like those from IEEE CEC2010 and CEC2017 [26].
2. Problem: Statistically Insignificant Algorithm Comparison Results
- Question: "I've compared my new algorithm against a baseline, but the performance difference is not statistically significant. How can I improve my experimental design?"
- Answer: Statistical significance confirms that observed performance differences are real and not due to random chance. The standard benchmark is a 95% confidence level (p-value < 0.05) [91].
- Methodology: Use non-parametric statistical tests, which do not assume a normal distribution of data and are more robust for algorithm comparisons.
- Actionable Protocol:
- Multiple Runs: Execute multiple independent runs (e.g., 30 or more) of each algorithm on each benchmark problem to account for random variation.
- Collect Performance Data: Record the final solution quality (e.g., best objective value found) or convergence speed from each run.
- Apply Statistical Testing:
- Wilcoxon Signed-Rank Test: Use this for a pairwise comparison between your algorithm and one other on multiple problems. A resulting p-value lower than 0.05 indicates a statistically significant difference [26].
- Friedman Test: Use this to rank multiple algorithms across several datasets or problems. A higher average rank indicates better overall performance [26].
- Expected Outcome: A rigorous validation that provides credible evidence of your algorithm's superiority, inferiority, or equivalence, which is essential for publication and real-world application.
3. Problem: Validating Computational Drug Repurposing Predictions
- Question: "My computational model has generated a list of candidate drugs for repurposing. How do I validate these predictions to prioritize them for further study?"
- Answer: Validation is a critical step to reduce false positives and build confidence in your predictions. A multi-faceted approach is required [92].
- Methodology: Combine computational checks with external evidence from existing biomedical knowledge and clinical data.
- Actionable Protocol:
- Computational Validation:
- Retrospective Clinical Analysis: Search databases like
clinicaltrials.govto see if any active or completed clinical trials are testing your candidate drug for the new indication. This is strong validation as it indicates the hypothesis has already passed initial hurdles [92]. - Literature Support: Systematically mine existing biomedical literature (e.g., via PubMed) for studies that manually describe a connection between the drug and the disease. This can provide mechanistic support [92].
- Retrospective Clinical Analysis: Search databases like
- Non-Computational Validation:
- Computational Validation:
- Expected Outcome: A tiered list of repurposing candidates, with the strongest candidates supported by multiple lines of evidence, ready for costly and time-consuming in vivo studies or clinical trials.
Experimental Protocols & Data Presentation
Table 1: Statistical Tests for Algorithm Performance Validation
| Test Name | Use Case | Protocol Summary | Key Outcome Metric |
|---|---|---|---|
| Wilcoxon Signed-Rank Test | Pairwise comparison of two algorithms on multiple problems/datasets. | Non-parametric test that ranks the differences in performance between paired samples. | p-value < 0.05 indicates a statistically significant difference in performance [26]. |
| Friedman Test | Comparing the performance of multiple (≥2) algorithms across several problems. | Non-parametric test that ranks algorithms for each problem and compares average ranks. | Average Rank: A lower average rank signifies better overall performance [26]. |
Table 2: Key Reagent Solutions for Computational Research
| Research Reagent / Resource | Function in Validation | Example Tools / Databases |
|---|---|---|
| Benchmark Problem Sets | Provides standardized test functions to fairly evaluate and compare algorithm performance. | IEEE CEC2006, CEC2010, CEC2017 constrained optimization benchmarks [26]. |
| Clinical Trials Database | Validates drug repurposing predictions by checking for pre-existing clinical evidence. | ClinicalTrials.gov [92]. |
| Biomedical Literature Database | Provides supporting evidence for predicted drug-disease connections via literature mining. | PubMed [92]. |
| Statistical Analysis Software | Executes statistical tests to determine the significance of experimental results. | R, Python (with scipy.stats), MATLAB. |
Workflow and Relationship Visualizations
The following diagram illustrates the integrated workflow for developing and validating a constrained optimization algorithm, incorporating the handling of infeasible solutions.
Algorithm Validation Workflow
Frequently Asked Questions (FAQs)
Q1: Why is it crucial to explicitly specify how my algorithm handles solutions generated outside the domain (infeasible solutions)? A1: The strategy for dealing with infeasible solutions is not trivial; it significantly impacts your algorithm's performance, disruptiveness, and population diversity. Without a fully specified method, your results are not reproducible. Even for simple box constraints, this choice induces notably different behaviors, an effect that grows with problem dimensionality [11].
Q2: What is the minimum acceptable confidence level for reporting statistically significant results in my experiments? A2: The industry and academic standard for determining significant results is a 95% confidence level, which corresponds to a p-value of less than 0.05. This means there is less than a 5% probability that your observed results occurred by random chance [91].
Q3: In the context of my thesis on constrained optimization, what is the benefit of using an adaptive penalty function over a static one? A3: Static penalty functions treat all constraints equally, which is often inappropriate because constraints have varying levels of "significance" and difficulty. An adaptive penalty function assigns different weights to constraints spontaneously during the evolution process, based on their violation severity. This makes the optimization process more interpretable and helps the algorithm converge more rapidly toward the global optimum by dynamically focusing its search effort [26].
Analysis of Computational Efficiency and Convergence Behavior
Frequently Asked Questions (FAQs)
FAQ 1: What are the most common indicators of convergence problems in an evolutionary algorithm? You can identify convergence issues through several key indicators. A primary signal is a low Effective Sample Size (ESS), which suggests your samples from the posterior are highly autocorrelated and not independent [93]. You should also inspect the trace plots of parameters; poor mixing, where the chain gets stuck in one region for long periods or explores the space inefficiently, indicates convergence problems [93]. Furthermore, if the algorithm stops with a message like "Solver Cannot Improve the Current Solution" or "Solver has Converged to the Current Solution," it signifies that progress has stalled, which may or may not indicate a true optimum [94].
FAQ 2: My algorithm has converged to an infeasible point. What does this mean and how can I proceed? Convergence to an infeasible point means the algorithm cannot find a solution that satisfies all your constraints. This can occur if the constraints are too strict or contradictory [95]. In such cases, some methods, like Augmented Lagrangian Methods (ALMs) for convex problems, will converge to the solution of the "closest feasible problem" [96]. To troubleshoot, first verify that a feasible solution exists by relaxing constraints if possible. For population-based algorithms, you can also try increasing the Population Size and Mutation Rate to help the population escape local infeasible regions and maintain diversity to find feasible areas of the search space [94].
FAQ 3: How can I improve the mixing and efficiency of my MCMC sampler? Improving mixing often involves tuning the algorithm's operators. If a specific parameter is mixing poorly, you can try increasing the weight of its scale operator, which makes the algorithm propose new values for that parameter more frequently [93]. For highly correlated parameters, introducing an UpDown operator is very effective; this operator updates correlated parameters (e.g., one up, another down) in a single step, allowing for more efficient exploration of their joint distribution [93].
FAQ 4: How can I statistically compare the convergence performance of different evolutionary algorithms? To rigorously compare convergence speed beyond just final results, you can use statistical methods like Page's trend test [97]. This non-parametric test analyzes the trends in fitness values over multiple points during the run (not just the end) of different algorithms. It allows you to determine if one algorithm consistently converges faster than another, which is particularly useful when the final results are statistically similar [97].
FAQ 5: What is the role of molecular representation in evolutionary drug design, and which should I choose? The choice of molecular representation significantly impacts the efficiency of exploring chemical space. The SELFIES (SELF-referencing Embedded Strings) representation is often preferred because it guarantees that every string corresponds to a valid molecular structure, eliminating wasted computation on invalid molecules [98]. In contrast, the more traditional SMILES (Simplified Molecular-Input Line-Entry System) representation has a high probability of generating invalid structures through standard evolutionary operators, requiring repair mechanisms and reducing efficiency [98].
Troubleshooting Guides
Guide 1: Diagnosing and Resolving Poor Convergence
This guide addresses the common issue of an evolutionary algorithm or MCMC sampler failing to converge effectively or converging to a poor solution.
Table: Key Diagnostic Metrics and Their Interpretations
| Metric/Visualization | Description | Interpretation of Issues |
|---|---|---|
| Effective Sample Size (ESS) [93] | The number of effectively independent samples. | A low ESS (< 100-200 is often a concern) indicates high autocorrelation and poor mixing. |
| Trace Plot [93] | A time-series plot of a parameter's value over iterations. | A "hairy caterpillar" look is good. Stuck lines, sudden jumps, or slow drifts suggest poor exploration. |
| Average Fitness Trend | The progression of the best or average fitness over generations. | A premature plateau can indicate convergence to a local optimum or loss of population diversity. |
| Solver Messages [94] | Heuristic stopping messages from the software. | "Cannot Improve" suggests stalled progress; "Converged" may mean true convergence or lost diversity. |
Step-by-Step Protocol:
- Inspect Trace Plots and ESS: Load your output (e.g., a
.logfile) into an analysis tool like Tracer [93]. Check all parameters for low ESS and non-stationary trace plots. - Check for Parameter Correlations: Use a tool like Tracer to plot the joint-marginal distribution of parameters. Look for strong correlations (e.g., a strong negative correlation between
Tree.heightandclockRateis common in phylogenetics) [93]. - Implement Solutions Based on Diagnosis:
- For low ESS/poor mixing: Increase the chain length (number of iterations) [93]. For a specific parameter, increase the operator weight to propose changes more often [93].
- For parameter correlations: Add a joint operator, like an UpDown operator, that updates correlated parameters simultaneously [93].
- For premature convergence/lost diversity: Restart the run with a larger Population Size and/or increased Mutation Rate to reintroduce diversity [94].
The following workflow summarizes the diagnostic process:
Guide 2: Handling Infeasible Solutions and Problems
This guide provides a methodology for dealing with infeasibility within the context of constrained evolutionary optimization research.
Step-by-Step Protocol:
- Feasibility Analysis: First, determine if the problem itself is feasible. Analyze your constraints for potential contradictions. For complex nonlinear constraints, this may be difficult, but try to find any single constraint that is impossible to satisfy [95].
- Constraint Relaxation: If the problem is infeasible, consider which constraints can be relaxed or converted into soft constraints with penalty terms. This allows the algorithm to find a "close" solution, which can be informative.
- Leverage Specialized Algorithms: If working with convex problems, use algorithms like Augmented Lagrangian Methods (ALMs), which are proven to converge to the "closest feasible problem" when the original is infeasible [96].
- Algorithmic Tuning for Diversity: In population-based methods, maintain a diverse population. This increases the chance that some individuals will remain in or find feasible regions. Using a representation like SELFIES in drug design inherently avoids invalid molecules, thus sidestepping one major class of infeasibility [98].
The Scientist's Toolkit: Essential Research Reagents
Table: Key Computational Tools and Methods for Evolutionary Optimization
| Tool/Method Name | Function/Brief Explanation | Relevant Context |
|---|---|---|
| Tracer [93] | A software tool for analyzing MCMC output. It visualizes trace plots, calculates ESS, and checks parameter correlations to diagnose convergence. | General MCMC, Bayesian Phylogenetics |
| Page's Trend Test [97] | A non-parametric statistical test to compare the convergence speed of algorithms by analyzing fitness value trends over time. | Algorithm Performance Comparison |
| SELFIES [98] | A molecular string representation that guarantees 100% valid chemical structures, improving optimization efficiency in drug discovery. | Evolutionary Drug Design |
| UpDown Operator [93] | An MCMC operator that proposes updates to two (often negatively) correlated parameters simultaneously to improve sampling efficiency. | Bayesian Phylogenetics, MCMC |
| Augmented Lagrangian Method (ALM) [96] | An optimization algorithm for constrained problems that can handle infeasibility by converging to the "closest" feasible solution. | Convex Constrained Optimization |
| RosettaEvolutionaryLigand (REvoLd) [63] | An evolutionary algorithm specifically designed for ultra-large library screening in drug discovery, incorporating flexible docking. | Structure-Based Drug Design |
Frequently Asked Questions & Troubleshooting
Q1: Why does my building energy optimization simulation fail to find any feasible solutions?
Your model may be over-constrained or contain conflicting requirements that create an infeasible search space. This commonly occurs when:
- Occupancy profiles or weather data are inaccurate, creating unrealistic HVAC load constraints [99]
- Overly ambitious energy reduction targets conflict with minimum comfort standards [100]
- Simplifications in shoebox or zone-merged models deviate significantly from actual building behavior, with some simplified models showing energy consumption deviations as high as 21% compared to detailed models [100]
Q2: How can I identify which constraints are causing infeasibility in my energy model?
Implement a sequential constraint relaxation protocol:
- Remove all constraints and verify your optimization can find solutions
- Add constraints back in groups (e.g., all thermal comfort constraints)
- Monitor when feasible solutions disappear
- Use visualization tools to plot constraint violations [101]
For building energy applications, pay particular attention to occupancy constraint conflicts with equipment capacity limits [99].
Q3: What practical steps can I take when my building energy optimization repeatedly produces infeasible solutions?
- Constraint Analysis: Identify which specific constraints are being violated most frequently [101]
- Model Simplification Verification: Validate that any model simplifications (e.g., zone merging, material property approximation) maintain physical realism [100]
- Occupancy Data Validation: Verify that real-time occupancy data from elevators, sensors, or other sources accurately reflects actual building usage patterns [99]
Q4: How do I balance computational efficiency with model accuracy in building energy optimization?
There is always a trade-off between computational speed and predictive accuracy. The table below summarizes performance characteristics of different simplification approaches:
Table: Building Energy Model Simplification Approaches
| Simplification Type | Computational Time Reduction | Energy Deviation | Best Use Cases |
|---|---|---|---|
| Detailed Model (Baseline) | Reference (21.65 hours) | Reference | Final validation phase [100] |
| Shoebox Model | 96% time savings (0.39 hours) | 11-21% deviation | Early-stage exploration [100] |
| Three-Zone Model | 40% time reduction | 7-14% deviation | Balanced accuracy-efficiency needs [100] |
| R-Value Model | 3% time reduction | <2% deviation | High-precision requirements [100] |
Experimental Protocols & Methodologies
Protocol 1: Multi-Zone Simplification for Computational Efficiency
Objective: Reduce computational burden while maintaining reasonable accuracy through thermal zone abstraction [100].
Methodology:
- Zone Classification: Group spaces with similar usage patterns, orientation, and thermal characteristics
- Load Calculation: Calculate combined thermal loads for each zone group
- Validation: Compare simplified model predictions against detailed model with <15% deviation target [100]
- Optimization: Apply NSGA-II or similar evolutionary algorithms to simplified model
Troubleshooting: If accuracy falls outside acceptable range, adjust zone grouping strategy or introduce weighting factors for critical spaces.
Protocol 2: Real-Time Occupancy-Driven HVAC Optimization
Objective: Optimize HVAC operation based on actual building occupancy to reduce energy consumption while maintaining comfort [99].
Methodology:
- Data Collection: Gather real-time occupancy data from elevator systems, Wi-Fi connectivity, or occupancy sensors
- Profile Development: Create dynamic occupancy profiles reflecting actual usage patterns rather than design assumptions [99]
- Setpoint Adjustment: Implement automated HVAC setpoint adjustments based on actual occupancy levels
- Validation: Monitor tenant comfort complaints and energy consumption
Case Study Results: A commercial building implementation achieved 36% energy savings (45,000 kWh annually) without tenant comfort complaints [99].
Research Reagent Solutions: Essential Tools for Building Energy Optimization
Table: Key Computational Tools for Building Energy Optimization Research
| Tool Category | Specific Examples | Research Application | Constraints/Considerations |
|---|---|---|---|
| Optimization Algorithms | NSGA-II, NSGA-III, MOEA/D [98] | Multi-objective optimization for energy vs. comfort tradeoffs | Parameter tuning sensitive; may require parallel computing [100] |
| Simulation Engines | EnergyPlus, Modelica | Detailed building energy performance simulation | Computationally intensive; requires simplification for optimization loops [100] |
| Simplification Approaches | Shoebox models, Zone merging, R-value methods [100] | Reducing computational burden for iterative optimization | Accuracy tradeoffs must be quantified and validated [100] |
| Constraint Handling | Penalty functions, Feasibility rules [101] | Managing conflicting design requirements | Implementation choices significantly impact solution quality [101] |
Visualization of Optimization Workflows
Building Energy Optimization Workflow
Infeasibility Resolution Protocol
Conclusion
The strategic handling of infeasible solutions represents a crucial advancement in constrained evolutionary optimization, transitioning from simple rejection to intelligent utilization that enhances global search capability and solution quality. The integration of multi-stage frameworks, adaptive constraint handling, and cooperative multi-task optimization demonstrates significant improvements in navigating complex feasible regions and avoiding premature convergence. For biomedical and clinical research applications, these approaches enable more effective exploration of complex solution spaces in drug design, treatment optimization, and clinical trial design. Future research directions should focus on developing problem-aware adaptive mechanisms, scaling these techniques for high-dimensional optimization, and creating specialized frameworks for multimodal constrained problems specific to biomedical domains. The continued evolution of these methodologies promises to address increasingly complex constrained optimization challenges in personalized medicine and pharmaceutical development.
References
- 1. Handling Infeasibility in Optimization Models [https://www.decisionspot.com/post/handling-infeasibility-in-optimization-models]
- 2. Handling Infeasibility with Optimization Models | by AlainChabrier | Medium [https://medium.com/@AlainChabrier/handling-infeasibility-with-optimization-models-fd409f767dad]
- 3. DC-SHADE-IF: An infeasible–feasible regions constrained ... [https://www.sciencedirect.com/science/article/abs/pii/S0957417423005018]
- 4. Handling infeasibility [https://www.fico.com/fico-xpress-optimization/docs/latest/evalguide2/dhtml/eg2sec4.html]
- 5. How do I determine why my model is infeasible? [https://support.gurobi.com/hc/en-us/articles/360029969391-How-do-I-determine-why-my-model-is-infeasible]
- 6. Constraint Violation - an overview [https://www.sciencedirect.com/topics/engineering/constraint-violation]
- 7. Useful Infeasible Solutions in Engineering Optimization ... [https://link.springer.com/chapter/10.1007/11579427_66]
- 8. An evolutionary algorithm based on learning strategies and ... [https://www.sciencedirect.com/science/article/abs/pii/S2210650225003657]
- 9. Utilizing feasible non-dominated solution information for ... [https://www.sciencedirect.com/science/article/abs/pii/S0020025524017262]
- 10. UCPO: A Universal Constrained Combinatorial ... [https://arxiv.org/html/2511.10148v1]
- 11. dealing with infeasible solutions in Differential Evolution ... [https://arxiv.org/abs/2203.03512]
- 12. Trade-offs in Encapsulation Efficiency and Drug Release [https://www.sciepublish.com/article/pii/344]
- 13. Understanding Evolutionary Optimization Algorithms ... [https://www.ai-futureschool.com/en/computing/understanding-evolutionary-optimization-algorithms-efficiently.php]
- 14. Infeasibility Driven Evolutionary Algorithm for Constrained ... [https://link.springer.com/chapter/10.1007/978-3-642-00619-7_7]
- 15. A two-stage ensemble evolutionary algorithm for ... [https://www.sciencedirect.com/science/article/abs/pii/S2210650225003700]
- 16. Two-Stage Archive Evolutionary Algorithm for Constrained ... [https://www.mdpi.com/2227-7390/13/3/470]
- 17. E-BRM: A constraint handling technique to solve ... [https://www.sciencedirect.com/science/article/abs/pii/S1568494618304368]
- 18. From penalty function to learning-driven: evolution and ... [https://www.sciencedirect.com/science/article/pii/S2210650225001646]
- 19. Constraint Consensus assisted Evolutionary Algorithm for ... [https://www.sciencedirect.com/science/article/pii/S1568494625006945]
- 20. Constrained evolutionary optimization based on dynamic ... [https://www.sciencedirect.com/science/article/abs/pii/S0957417423029524]
- 21. Infeasibility in mathematical optimization models [https://or.stackexchange.com/questions/1215/infeasibility-in-mathematical-optimization-models]
- 22. A Guide on Evolutionary Algorithms [https://www.ultralytics.com/blog/what-is-an-evolutionary-algorithm-a-quick-guide]
- 23. A Novel Ranking Scheme for the Performance Analysis ... [https://arxiv.org/html/2406.00154v1]
- 24. A constrained multi-objective optimization algorithm using an efficient... [https://link.springer.com/article/10.1007/s40747-022-00851-1]
- 25. A Dual- Population -Based NSGA-III for Constrained Many-Objective... [https://pmc.ncbi.nlm.nih.gov/articles/PMC9858107/]
- 26. Exploring interpretable evolutionary optimization via ... [https://www.sciencedirect.com/science/article/abs/pii/S2210650224002177]
- 27. Molecule discovery and optimization via evolutionary ... [https://www.nature.com/articles/s41598-024-75515-w]
- 28. Karush–Kuhn–Tucker conditions [https://en.wikipedia.org/wiki/Karush%E2%80%93Kuhn%E2%80%93Tucker_conditions]
- 29. Constrained Optimization and the KKT Conditions [https://towardsdatascience.com/constrained-optimization-and-the-kkt-conditions-a3541d57a994/]
- 30. Solving optimization problem using KKT conditions [https://math.stackexchange.com/questions/4624750/solving-optimization-problem-using-kkt-conditions]
- 31. The Central Path - by Ben Recht [https://www.argmin.net/p/the-central-path]
- 32. Efficient implicit constraint handling approaches for ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC10899602/]
- 33. Constrained optimization with heuristic algorithm in actual ... [https://or.stackexchange.com/questions/12186/constrained-optimization-with-heuristic-algorithm-in-actual-production]
- 34. Genetic algorithm [https://en.wikipedia.org/wiki/Genetic_algorithm]
- 35. Introduction to Optimization with Genetic Algorithm [https://medium.com/data-science/introduction-to-optimization-with-genetic-algorithm-2f5001d9964b]
- 36. Crossover and mutation: An introduction to two operations ... [https://blogs.sas.com/content/iml/2021/10/18/crossover-mutation.html]
- 37. A color image contrast enhancement method based on ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC9910741/]
- 38. An Adaptive Penalty Method for Inequality Constrained ... [https://arxiv.org/abs/2201.02425]
- 39. Evolutionary constrained optimization with hybrid ... [https://www.sciencedirect.com/science/article/abs/pii/S0957417422017006]
- 40. Efficient implicit constraint handling approaches for ... [https://www.nature.com/articles/s41598-024-54841-z]
- 41. A multi-stage multi-task evolutionary algorithm for ... [https://www.sciencedirect.com/science/article/abs/pii/S0020025525006929]
- 42. Feedback Tracking Constraint Relaxation Algorithm for ... [https://www.mdpi.com/2227-7390/13/4/629]
- 43. Feasibility-guided evolutionary optimization of pump ... [https://www.nature.com/articles/s41598-025-17630-w]
- 44. Modified Differential Evolution Algorithm for Solving ... [https://www.techscience.com/cmc/v74n1/49770/html]
- 45. Dynamic Constrained Boundary Method for ... [https://www.mdpi.com/2227-7390/10/23/4459]
- 46. Getting infeasible solutions when objective function has ... [https://community.ibm.com/community/user/discussion/getting-infeasible-solutions-when-objective-function-has-been-scaled-up]
- 47. Infeasible solution to a feasible problem [https://support.gurobi.com/hc/en-us/community/posts/13944470989969-Infeasible-solution-to-a-feasible-problem]
- 48. Co-evolutionary algorithm with a region-based diversity ... [https://link.springer.com/article/10.1007/s40747-025-01819-7]
- 49. A data-driven co-evolutionary exploration algorithm for ... [https://www.sciencedirect.com/science/article/abs/pii/S1568494624006318]
- 50. A Constrained Multi-Objective Evolutionary Algorithm with ... [https://www.mdpi.com/2227-7390/13/22/3696]
- 51. A Coevolutionary Algorithm Based on Constraints ... [https://link.springer.com/article/10.1007/s44196-025-00830-7]
- 52. Adaptive Constraint Relaxation-Based Evolutionary ... [https://www.mdpi.com/2227-7390/12/19/3075]
- 53. An Efficient Approach for Solving Expensive Constrained ... [https://arxiv.org/html/2405.13298v1]
- 54. A constrained multi-objective evolutionary algorithm using ... [https://www.sciencedirect.com/science/article/abs/pii/S2210650221001826]
- 55. Evolutionary constrained multi-objective optimization [https://link.springer.com/article/10.1007/s44336-024-00006-5]
- 56. A qualitative systematic review of metaheuristics applied to ... [https://www.sciencedirect.com/science/article/abs/pii/S0952197622005115]
- 57. Solving the Tension/Compression Spring Design Problem ... [https://www.semanticscholar.org/paper/Solving-the-Tension-Compression-Spring-Design-by-an-Celik-Kutucu/cb2a064c995dc4f5caa714d82641f3d7e7a3806b]
- 58. Stress Formula - The Final Factor of Design Integrity [https://www.mwspring.com/stress-formula-the-final-factor-of-design-integrity/]
- 59. Compression Springs Formula [https://www.acxesspring.com/compression-springs-formula.html?srsltid=AfmBOorsthR172pqAl8XQE3SLDTpNRBzsaZrRnY2mQYF-FCTjA-k4wZ6]
- 60. Premature Convergence in Constrained Continuous Search Spaces | SpringerLink [https://link.springer.com/chapter/10.1007/978-3-540-87700-4_7]
- 61. [PDF] Premature Convergence in Constrained Continuous Search Spaces | Semantic Scholar [https://www.semanticscholar.org/paper/Premature-Convergence-in-Constrained-Continuous-Kramer/4828c33b841590ea032cd30c0d00db6379272656]
- 62. A constrained multi-objective evolutionary algorithm using ... [https://www.sciencedirect.com/science/article/pii/S2210650221001826]
- 63. Ultra-large library screening with an evolutionary algorithm ... [https://www.nature.com/articles/s42004-025-01758-x]
- 64. Constrained search space selection based optimization approach for enhanced reduced order approximation of interconnected power system models | Scientific Reports [https://www.nature.com/articles/s41598-025-91913-0]
- 65. Balancing exploration and exploitation with information ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC7654823/]
- 66. A case study of differential evolution [https://www.sciencedirect.com/science/article/abs/pii/S0020025523012410]
- 67. Troubleshooting With the Infeasibility Diagnostic Engine [https://optilogic.com/resources/help-center/docs/troubleshooting-with-the-infeasibility-diagnostic-engine]
- 68. Feasible region [https://en.wikipedia.org/wiki/Feasible_region]
- 69. Decentralized adaptive task allocation for dynamic multi ... [https://www.nature.com/articles/s41598-025-21709-9]
- 70. Time-Aware World Model for Adaptive Prediction and Control [https://arxiv.org/html/2506.08441v1]
- 71. Estimate-at-completion (EAC) prediction using Archimedes ... [https://www.sciencedirect.com/science/article/abs/pii/S0926580524003893]
- 72. An Adaptive Framework for Remaining Useful Life ... [https://www.mdpi.com/1424-8220/25/20/6354]
- 73. Review Real-time algorithmic exchange and processing of ... [https://www.sciencedirect.com/science/article/pii/S0378517323007627]
- 74. Parameter-Efficient Multi-Task Learning via Progressive ... [https://arxiv.org/html/2509.19602v1]
- 75. A multi-task learning framework with prompt-based hybrid ... [https://www.sciencedirect.com/science/article/abs/pii/S0925231225007933]
- 76. Multitask Learning 1997–2024: Part III Applications [https://hdsr.mitpress.mit.edu/pub/lgmkutcd]
- 77. Solver Tutorial - Interpreting Solutions [https://www.solver.com/interpreting-solutions]
- 78. Feasible Solution - (Intro to Industrial Engineering) [https://fiveable.me/key-terms/introduction-industrial-engineering/feasible-solution]
- 79. Mathematical Optimization Techniques in Drug Product ... [https://www.sciencedirect.com/science/article/pii/S0022354915376048]
- 80. Application of Constrained Optimization Methods in Health ... [https://pubmed.ncbi.nlm.nih.gov/30224103/]
- 81. Evolutionary optimization of model merging recipes [https://www.nature.com/articles/s42256-024-00975-8]
- 82. CEC 2006 Problem Suite (single-objective, constrained) [https://esa.github.io/pagmo2/docs/cpp/problems/cec2006.html]
- 83. On an evolutionary approach for constrained optimization ... [https://www.sciencedirect.com/science/article/abs/pii/S1568494612002499]
- 84. Performance indicators in multiobjective optimization [https://www.sciencedirect.com/science/article/abs/pii/S0377221720309620]
- 85. Handling Constrained Multi-objective Optimization ... [https://dc-china-simulation.researchcommons.org/journal/vol36/iss4/10/]
- 86. (PDF) Infeasibility Driven Evolutionary for Algorithm ... Constrained [https://www.academia.edu/5913138/Infeasibility_Driven_Evolutionary_Algorithm_for_Constrained_Optimization]
- 87. Evolutionary Optimization of Constrained Problems [https://link.springer.com/chapter/10.1007/978-3-540-39883-7_3]
- 88. Design Optimization of a Welded Beam - MATLAB & Simulink [https://www.mathworks.com/help/gads/multiobjective-optimization-welded-beam.html]
- 89. Pressure Vessels: Analyzing Change [https://www.nationalboard.org/index.aspx?pageID=164&ID=212]
- 90. Pressure Vessel Fabrication: Standards, Design & Process [https://www.bakerindustriesinc.com/blog/pressure-vessel-fabrication-2024-best-practices/]
- 91. Statistical Significance in SEO Testing: Complete Guide [https://seotesting.com/blog/statistical-significance-in-seo-testing/]
- 92. Validation approaches for computational drug repurposing [https://pmc.ncbi.nlm.nih.gov/articles/PMC10785886/]
- 93. Troubleshooting-convergence-issues [https://taming-the-beast.org/tutorials/Troubleshooting-convergence-issues/]
- 94. Evolutionary Solving Method Stopping Conditions [https://www.solver.com/excel-solver-evolutionary-solving-method-stopping-conditions]
- 95. How to solve the problem of convergence at the infeasible ... [https://www.mathworks.com/matlabcentral/answers/1953744-how-to-solve-the-problem-of-convergence-at-the-infeasible-point]
- 96. Augmented Lagrangian methods for infeasible convex ... [https://arxiv.org/abs/2506.22428]
- 97. Analyzing convergence performance of evolutionary ... [https://www.sciencedirect.com/science/article/abs/pii/S0020025514006276]
- 98. Optimized Drug Design using Multi-Objective Evolutionary ... [https://arxiv.org/html/2405.00401v1]
- 99. Building optimization - Case study [https://www.siteflow.kone.com/building-optimization-case-study]
- 100. Enhancing building energy optimization efficiency [https://www.sciencedirect.com/science/article/pii/S235271022500796X]
- 101. Feasible and Infeasible Solutions [https://allen.in/jee/maths/feasible-and-infeasible-solutions]