Adaptive Constraint Handling Techniques for Evolutionary Optimization: From Foundations to Biomedical Applications
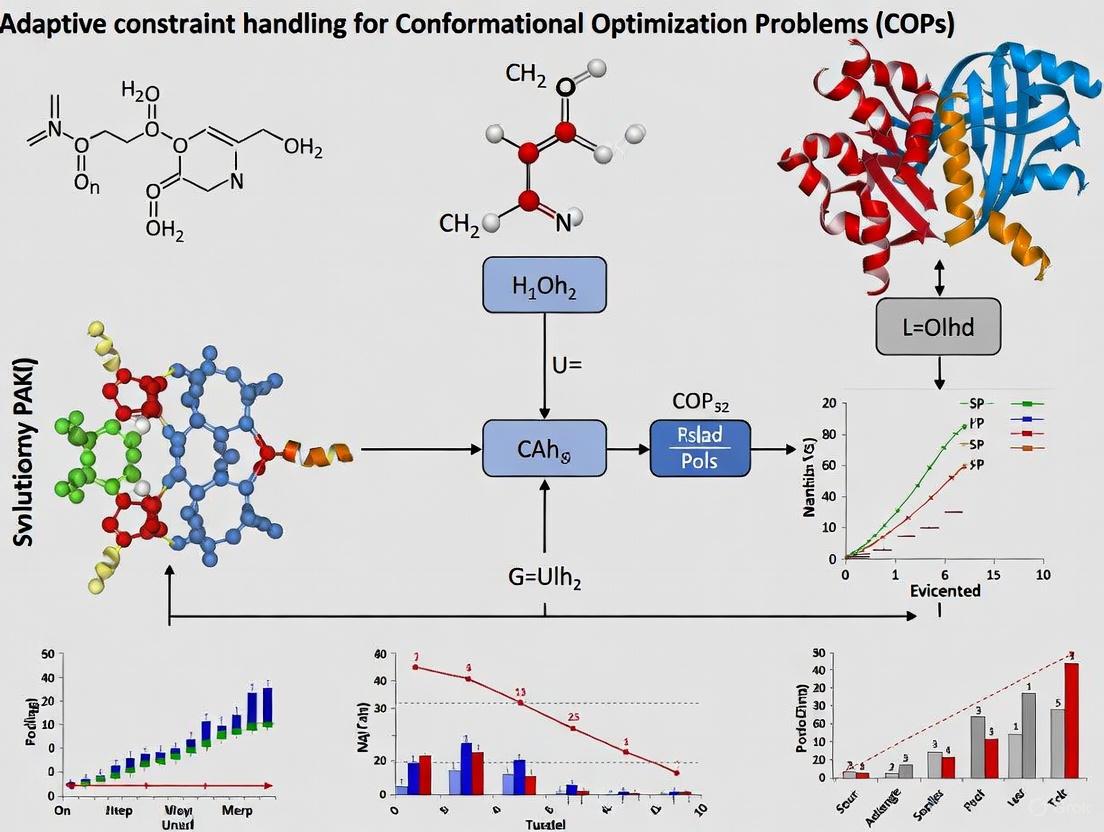
Constrained Optimization Problems (COPs) present significant challenges across scientific domains, particularly in drug development where complex biochemical constraints must be balanced with multiple optimization objectives.
Adaptive Constraint Handling Techniques for Evolutionary Optimization: From Foundations to Biomedical Applications
Abstract
Constrained Optimization Problems (COPs) present significant challenges across scientific domains, particularly in drug development where complex biochemical constraints must be balanced with multiple optimization objectives. This comprehensive review explores adaptive constraint handling techniques (CHTs) for evolutionary algorithms, addressing four critical dimensions: fundamental principles of constrained multi-objective optimization, innovative methodological approaches including deep reinforcement learning and repair mechanisms, troubleshooting strategies for complex constraint landscapes, and rigorous validation frameworks. By synthesizing cutting-edge research in adaptive CHTs, we provide researchers and drug development professionals with actionable insights for navigating discontinuous feasible regions, avoiding local optima, and accelerating convergence in computationally expensive optimization scenarios prevalent in biomedical research.
Understanding Constrained Optimization: Core Concepts and Challenges
Mathematical Definition of CMOPs
A Constrained Multi-Objective Optimization Problem (CMOP) can be mathematically defined by three key components: multiple objective functions to be optimized simultaneously, a set of constraints that solutions must satisfy, and decision variables with their boundaries [1] [2].
The standard formulation is as follows [1] [2]:
Minimize ( F(\mathbf{x}) = (f1(\mathbf{x}), f2(\mathbf{x}), \dots, f_M(\mathbf{x})) )
Subject to: [ \begin{align} g_i(\mathbf{x}) & \leq 0, \quad i = 1, \dots, p \ h_j(\mathbf{x}) & = 0, \quad j = p+1, \dots, L \ \mathbf{x} & \in S \subseteq \mathbb{R}^D \end{align} ]
Where:
- ( F(\mathbf{x}) ) is the objective vector comprising ( M ) conflicting sub-objectives
- ( \mathbf{x} = (x1, x2, \dots, x_D) ) is the decision vector in the D-dimensional space
- ( g_i(\mathbf{x}) ) represents inequality constraints
- ( h_j(\mathbf{x}) ) represents equality constraints
- ( S ) defines the feasible decision space bounded by variable constraints
Constraint Violation Measurement
To quantify how much a solution violates constraints, researchers use a constraint violation (CV) function [1] [2]:
[ CV(\mathbf{x}) = \sum{i=1}^{p} \max(0, gi(\mathbf{x})) + \sum{j=p+1}^{L} \max(0, |hj(\mathbf{x})| - \delta) ]
Here, ( \delta ) is a very small positive parameter (typically ( 10^{-4} )) used to relax equality constraints, making them numerically manageable [2]. A solution ( \mathbf{x} ) is considered feasible if ( CV(\mathbf{x}) = 0 ), and infeasible otherwise.
Constrained Dominance Principle
For comparing solutions in CMOPs, the constrained dominance principle (( \precc )) is widely used [2]. A solution ( \mathbf{a} ) constrained-dominates a solution ( \mathbf{b} ) (( \mathbf{a} \precc \mathbf{b} )) if any of the following conditions hold:
- Both solutions are feasible, and ( \mathbf{a} ) dominates ( \mathbf{b} ) in objective space
- Solution ( \mathbf{a} ) is feasible while ( \mathbf{b} ) is infeasible
- Both solutions are infeasible, but ( \mathbf{a} ) has a smaller constraint violation than ( \mathbf{b} )
Real-World Applications of CMOPs
CMOPs arise frequently in real-world applications across various domains. The table below summarizes key application areas and examples:
Table: Real-World Application Areas of CMOPs
| Application Domain | Specific Examples | Key Constraints & Objectives |
|---|---|---|
| Drug Discovery [3] | Molecular optimization for protein-ligand binding (4LDE protein) [3], Glycogen synthase kinase-3 (GSK3) inhibitors [3] | Objectives: Improve bioactivity, drug-likeness (QED), synthetic accessibility [3]. Constraints: Structural alerts, ring size restrictions, reactive groups [3]. |
| Healthcare & Medical Decision Making [4] | Optimal cervical cancer screening/vaccination strategies [4], Statin start time optimization for diabetes patients [4], Radiation therapy treatment planning [4] | Objectives: Maximize health outcomes, minimize costs [4]. Constraints: Resource availability, clinical guidelines, dosage limits [4]. |
| Mechanical & Structural Design [2] | Robot gripper optimization [1] [5], Tall building design [5], Composite structures [5] | Objectives: Maximize performance, minimize weight/cost [2]. Constraints: Physical laws, safety regulations, material limits [2]. |
| Energy Systems [1] | Power system optimization [2], Energy-saving strategies [1] | Objectives: Minimize cost, maximize efficiency/reliability [1] [2]. Constraints: Demand-supply balance, transmission limits, emission caps [2]. |
| Transportation & Logistics [1] | Vehicle scheduling [1], Vehicle routing with time windows [5] | Objectives: Minimize travel time/distance, maximize service level [1] [5]. Constraints: Time windows, capacity limits, route continuity [5]. |
In-Depth Application: Constrained Molecular Optimization
In drug discovery, CMOPs are formulated to optimize multiple molecular properties while satisfying chemical constraints [3]. For a molecule ( \mathbf{m} ), the problem can be defined as:
Minimize ( F(\mathbf{m}) = (f1(\mathbf{m}), f2(\mathbf{m}), \dots, f_M(\mathbf{m})) )
Subject to: [ \begin{align} C_i^{\text{ineq}}(\mathbf{m}) & \leq 0, \quad i = 1, \dots, p \ C_j^{\text{eq}}(\mathbf{m}) & = 0, \quad j = p+1, \dots, L \ \end{align} ]
Where ( f_k(\mathbf{m}) ) represents molecular properties like biological activity or drug-likeness, and constraints ( C(\mathbf{m}) ) include structural requirements like ring size limitations or avoidance of toxic substructures [3].
Classification of CMOPs
Based on the relationship between constrained and unconstrained Pareto fronts, CMOPs can be categorized into four types [2]:
Table: Classification of CMOP Types
| Type | Description | Challenge Level |
|---|---|---|
| Type I | Constrained Pareto Front (CPF) is identical to unconstrained Pareto Front (UPF) | Low |
| Type II | CPF is a subset of UPF | Medium |
| Type III | CPF partially overlaps with UPF | Medium-High |
| Type IV | CPF and UPF have no common regions | High |
This classification helps researchers select appropriate constraint-handling techniques, as the required balance between minimizing objectives and satisfying constraints varies across types [2].
Experimental Setup and Benchmarking
Standard Benchmark Problems
For standardized performance evaluation, researchers have developed benchmark suites of real-world CMOPs. The CEC'2020 test suite contains 57 real-world constrained optimization problems [6], while other suites offer up to 50 RWCMOPs collected from various domains [2].
Table: Real-World CMOP Benchmark Suites
| Benchmark Suite | Number of Problems | Application Domains Covered |
|---|---|---|
| CEC'2020 [6] | 57 problems | Engineering design, energy systems, process control |
| RWCMOP Suite [2] | 50 problems | Mechanical design (21), Chemical engineering (7), Process design (9), Power electronics (6), Power systems (7) |
Performance Metrics for CMOP Algorithms
When evaluating constrained multi-objective evolutionary algorithms (CMOEAs), researchers use multiple performance indicators [2]:
- Inverted Generational Distance (IGD): Measures convergence and diversity
- Hypervolume (HV): Measures the volume of objective space dominated by solutions
- Feasibility Ratio: Percentage of feasible solutions in the final population
- Success Rate: Percentage of successful runs reaching predefined targets
Frequently Asked Questions (FAQs)
Fundamental Concepts
Q: What is the key difference between constrained single-objective and multi-objective optimization?
A: While single-objective constrained optimization aims to find a single optimal solution satisfying constraints, CMOPs must find a set of trade-off solutions (Pareto front) that balance multiple conflicting objectives while satisfying all constraints [1] [2]. The additional complexity arises from maintaining diversity among feasible solutions while approaching the true Pareto front.
Q: How do constraints affect the feasible region in CMOPs?
A: Constraints can significantly reshape the feasible space by [5] [2]:
- Making large portions of the search space infeasible
- Dividing the feasible space into narrow, disconnected regions
- Rendering parts of the unconstrained Pareto front infeasible
- Creating complex feasible boundaries that are challenging to navigate
Implementation Challenges
Q: Why do many algorithms struggle with Type III and Type IV CMOPs?
A: Type III and IV CMOPs present particular challenges because [2]:
- They require careful balancing between objective optimization and constraint satisfaction
- The constrained and unconstrained Pareto fronts have minimal or no overlap
- Algorithms must navigate through large infeasible regions to find feasible solutions
- Traditional penalty function methods often fail without proper adaptation
Q: What is the main limitation of penalty function methods for constraint handling?
A: The main limitations include [6]:
- Difficulty in setting appropriate penalty parameters without trial and error
- Different degrees of constraint violations require different penalty scales
- Poor performance when feasible regions are small or disconnected
- Tendency to get trapped in local optima when penalty parameters are too large
Algorithm Selection
Q: What are the advantages of multi-stage approaches for solving CMOPs?
A: Multi-stage frameworks (like MSEFAS) provide several advantages [5]:
- They can adaptively balance exploration and exploitation across different evolutionary phases
- Early stages can utilize promising infeasible solutions to maintain diversity
- Later stages can focus on convergence to the feasible Pareto front
- They can dynamically adjust search behavior based on population state
Q: How do adaptive constraint-handling techniques improve upon static methods?
A: Adaptive techniques (like dynamic ε) offer significant benefits [6] [1]:
- They dynamically adjust constraint tolerance based on feasible ratio and iteration count
- They maintain a reasonable proportion of virtual feasible solutions throughout optimization
- They can reshape individual positions adaptively based on constraint violation magnitude
- They eliminate the need for manual parameter tuning during the optimization process
Troubleshooting Common Experimental Issues
Problem: Population Lacks Feasible Solutions
Symptoms:
- Zero or very few feasible solutions after many generations
- Population converging to infeasible regions
- Inability to improve constraint violation over iterations
Solutions:
- Implement dynamic ε-constraint handling [6]: Gradually relax constraints early in optimization, then tighten them progressively
Use multi-population approaches [1]: Maintain separate populations focusing on objective improvement and constraint satisfaction
Apply adaptive boundary constraint handling [6]: Reshape individual positions based on constraint violation extent to increase diversity
Problem: Premature Convergence to Suboptimal Feasible Regions
Symptoms:
- Algorithm finds feasible but poor-quality solutions
- Lack of diversity in the obtained Pareto front
- Inability to explore disconnected feasible regions
Solutions:
- Implement multi-stage optimization [5]: Divide optimization into stages with different goals:
- Stage 1: Encourage approaching feasible region with diversity preservation
- Stage 2: Enable spanning large infeasible regions to accelerate convergence
- Stage 3: Refine solutions considering CPF-UPF relationship
Use population state discrimination [1]: Monitor relative positions of main and auxiliary populations to dynamically switch search strategies
Incorporate knowledge transfer mechanisms [5]: Enable information exchange between populations exploring different regions
Problem: Poor Performance on Specific CMOP Types
Symptoms:
- Algorithm works well on some problem types but fails on others
- Inconsistent performance across different benchmark problems
- Difficulty maintaining balance between constraints and objectives
Solutions:
- Employ algorithm selection based on problem characteristics [2]:
- Type I/II: Focus more on objective optimization
- Type III/IV: Prioritize constraint satisfaction initially
Implement cooperative coevolution [1]: Use multiple populations with different constraint-handling techniques:
- Main population: Focus on CPF with strict constraints
- Auxiliary population: Explore UPF with relaxed constraints
Apply adaptive resource allocation [1]: Distribute computational resources between populations based on their contribution to improvement
Essential Research Reagents and Tools
Table: Key Algorithmic Components for CMOP Research
| Component | Function | Examples/Implementation |
|---|---|---|
| Constraint Handling Techniques (CHTs) | Balance objective optimization with constraint satisfaction | ε-constraint [6], Stochastic Ranking [2], Adaptive Penalty [2] |
| Multi-Objective Evolutionary Algorithms (MOEAs) | Base optimizer for handling multiple objectives | NSGA-II [1], MOEA/D [2], NSGA-III [2] |
| Benchmark Suites | Performance assessment and comparison | RWCMOP Suite [2], CEC'2020 [6], MFs, CFs [2] |
| Performance Metrics | Quantitative evaluation of algorithm performance | IGD, HV [2], Feasibility Ratio, Success Rate [2] |
| Visualization Tools | Analysis of Pareto front and population distribution | Parallel coordinates, 2D/3D scatter plots, Heat maps of constraint violations |
Methodological Workflows
The following workflow diagrams illustrate common experimental setups for CMOP research:
Dynamic ε-Constraint Handling Workflow
Multi-Stage Optimization Framework
Dual-Population Cooperative Framework
Frequently Asked Questions
1. What is a constraint violation (CV) and how is it calculated for a single constraint?
The constraint violation (CV) quantitatively measures how much a candidate solution x fails to satisfy a single constraint. The calculation differs for inequality and equality constraints [7] [8].
For an inequality constraint of the form gi(x) ≤ 0, the violation is calculated as:
CV_i(x) = max(0, gi(x))
This means the violation is zero if the constraint is satisfied (gi(x) ≤ 0), and positive otherwise [9] [7].
For an equality constraint of the form hj(x) = 0, it is typically relaxed into an inequality using a tolerance δ (often set to 0.0001 or 10^-4) [9] [10]. The violation is then calculated as:
CV_j(x) = max(0, |hj(x)| - δ)
A solution is considered to satisfy the equality constraint only if the absolute value of hj(x) is less than or equal to δ [10].
2. How is the overall constraint violation for a solution computed?
The overall constraint violation G(x) or CV(x) is a single metric that aggregates the violation across all m constraints. This is typically done by summing the individual violations for each constraint [10] [7] [8]:
G(x) = ∑ from i=1 to p of max(gi(x), 0) + ∑ from j=p+1 to m of max(|hj(x)| - δ, 0)
A solution is considered feasible if and only if its overall constraint violation G(x) is equal to zero [9].
3. Our algorithm often gets trapped in local optima. How can adaptive constraint handling help? Standard methods might prematurely reject all infeasible solutions, losing valuable information. Adaptive techniques dynamically adjust how constraints are treated during the optimization process to improve global exploration [8].
One method is Adaptive Constraint Relaxation, which starts with relaxed constraint boundaries to allow exploration of promising infeasible regions. As the optimization progresses, the constraints are gradually tightened, guiding the population toward the feasible region [7]. Another approach is the ε-constraint method, where a parameter ε controls the tolerance for accepting slightly infeasible solutions. This ε value can be adaptively decreased based on the iteration count or the feasibility ratio of the population, balancing the use of objective and constraint information over time [9].
4. What are the best practices for measuring convergence in constrained evolutionary algorithms? Measuring convergence requires assessing both the quality of objective function values and the feasibility of solutions.
- Use Feasibility Rates: Track the proportion of feasible solutions in the population over generations. A successful run should show this rate increasing over time [10].
- Monitor Key Metrics: Record the best, median, and worst objective values from the feasible solutions in the population across independent runs. This helps gauge the algorithm's accuracy and robustness [10].
- Employ Quality Indicators: For multi-objective problems, use established metrics like:
- Perform Statistical Validation: Conduct a sufficient number of independent runs (e.g., 31) and use statistical tests to ensure the significance of the results [10].
5. How can surrogate models be used for expensive constrained optimization? In real-world applications like drug discovery, evaluating objectives and constraints can be computationally prohibitive [3] [11]. Surrogate-Assisted Evolutionary Algorithms (SAEAs) address this by using approximate models.
- Global Surrogates: Models like Radial Basis Functions (RBF) or Gaussian Processes (GPs) are built using all historically evaluated solutions. These surrogates are used to prescreen a large number of candidate solutions cheaply, selecting only the most promising ones for exact evaluation [11].
- Constrained Bayesian Optimization: A common approach uses the Constrained Expected Improvement (CEI) acquisition function. CEI is the product of the Expected Improvement (EI) for the objective and the Probability of Feasibility (POF) for the constraints, guiding the search toward optimal and feasible regions with minimal expensive function evaluations [12] [11].
Troubleshooting Guides
Problem: The population lacks diversity and converges to an infeasible local optimum.
- Potential Cause 1: Overly strict constraint handling that prematurely discards all infeasible solutions, some of which may be close to feasible regions and carry valuable objective information [7].
- Solution:
- Implement a two-stage strategy. In the first stage, relax constraints to explore the search space and identify promising regions, even if they are infeasible. In the second stage, strictly enforce constraints to refine solutions and achieve feasibility [7] [8].
- Use an archive mechanism to store promising infeasible solutions. These solutions can be used later to provide diversity and help the population cross large infeasible regions [8].
- Potential Cause 2: The mutation and crossover strategies are not effectively maintaining population diversity.
- Solution:
- Design evolution strategies for a dynamic population. For example, use different base solution selection rules for top-performing individuals and others to emphasize exploitation in promising regions while maintaining exploration elsewhere [11].
- Integrate a diversity-based ranking into the selection process to prevent convergence on a small subset of the feasible region [8].
Problem: The optimization is computationally slow due to expensive constraint evaluations.
- Potential Cause: Each constraint evaluation requires a costly simulation or experiment.
- Solution: Implement a surrogate-assisted framework [11].
- Build Surrogates: Construct approximation models (e.g., RBF, Kriging) for both the objective and constraint functions using an initial set of evaluated solutions.
- Prescreen Candidates: Use these surrogates to predict the performance of a large number of candidate solutions, filtering out poor or highly infeasible ones.
- Select for Exact Evaluation: Choose only a few high-potential solutions, as predicted by an infill criterion (e.g., CEI), for evaluation with the exact, expensive functions. This drastically reduces the number of costly evaluations required [11].
Problem: The algorithm struggles with problems that have disconnected feasible regions.
- Potential Cause: The feasible regions are scattered and separated by large infeasible "gaps," making it difficult for the population to find and transition between all feasible patches [7].
- Solution:
- Apply a constraint-tightening strategy. Begin the search with highly relaxed constraints to connect the disparate feasible regions. Gradually tighten the constraints as the run progresses, guiding the population toward the true, disconnected feasible areas [7].
- Utilize information from "promising infeasible solutions"—those with good objective values but moderate constraint violations. An adaptive step-size adjustment can use these solutions to guide the population across infeasible valleys toward other feasible regions [7].
Constraint Violation Metrics and Handling Techniques at a Glance
| Metric / Technique | Formula / Key Mechanism | Application Context | ||
|---|---|---|---|---|
| Single Constraint Violation [7] [8] | CV_i(x) = max(0, gi(x)) (Inequality) `CV_j(x) = max(0, |
hj(x) | - δ)` (Equality) | Fundamental building block for calculating overall violation for any type of constraint. |
| Overall Constraint Violation [9] [10] | `G(x) = ∑ max(gi(x), 0) + ∑ max( | hj(x) | - δ, 0)` | Determining if a solution is feasible (G(x)=0) and for comparing infeasible solutions. |
| ε-Constraint Handling [9] | Relaxed comparison: if CV(x) ≤ ε, compare by objective; else, compare by CV. |
Balancing objective and constraint search; ε can be self-adaptive based on population's feasibility ratio. |
||
| Feasibility Rule (CDP) [9] | 1) Feasible dominates infeasible. 2) Between feasible, better objective wins. 3) Between infeasible, lower CV wins. |
Simple and popular method for comparing two solutions during selection. | ||
| Two-Stage Methods [7] | Stage 1: Explore with relaxed constraints. Stage 2: Exploit with strict constraints. | Solving problems with disconnected feasible regions or when the global optimum lies on a constraint boundary. |
Experimental Protocols for Evaluating Constraint Handling Techniques
Protocol 1: Benchmarking on Standard Test Suites To validate a new constraint handling technique, it is crucial to test it against established benchmark problems.
- Select Benchmark Problems: Use standardized test suites like CEC2010 or CEC2017 for constrained real-parameter optimization [10]. These suites contain problems with diverse characteristics, such as separable/non-separable objectives and rotated constraints.
- Configure Experimental Settings: Set the search space dimensionality (e.g., D=10, 30) and the maximum number of function evaluations (MaxFEs) as defined by the benchmark (e.g., 200,000 for D=10) [10].
- Run Algorithms: Compare your algorithm against several state-of-the-art constrained evolutionary algorithms (e.g., IMODE, SHADE) [10].
- Performance Measurement: Execute multiple independent runs (e.g., 31) to ensure statistical significance. Compare results using performance metrics like best/median/worst objective values of found feasible solutions and feasibility rates [10].
Protocol 2: Real-World Validation in Molecular Optimization For techniques aimed at applications like drug discovery, testing on real-world problems is essential [3].
- Problem Formulation: Define the constrained multi-objective optimization problem. Treat multiple molecular properties (e.g., bioactivity, drug-likeness) as objectives to be optimized. Stringent drug-like criteria (e.g., ring size constraints, substructure alerts) are treated as constraints [3].
- Algorithm Implementation: Implement a framework like CMOMO that uses a dynamic constraint handling strategy. This involves an initial unconstrained search for good properties, followed by a constrained search to find feasible molecules [3].
- Evaluation: Use a pre-trained encoder to embed molecules into a continuous latent space for efficient optimization. The success of the algorithm is measured by its ability to identify molecules with multiple desired properties that also strictly adhere to all drug-like constraints [3].
The Scientist's Toolkit: Essential Reagents for Constrained Optimization
| Item | Function in Constrained Optimization |
|---|---|
| CEC Benchmark Suites | Provides a standardized set of constrained optimization problems (e.g., CEC2010, CEC2017) for fair and reproducible comparison of algorithms [10]. |
| Differential Evolution (DE) | A versatile and popular evolutionary algorithm framework that serves as a foundation for many advanced constrained optimization algorithms (e.g., SHADE) [9]. |
| Radial Basis Function (RBF) / Gaussian Process (GP) | Surrogate models used to approximate expensive black-box objective and constraint functions, drastically reducing computational cost in SAEAs [11]. |
| Probability of Feasibility (POF) | A metric, often derived from a Gaussian process model, that estimates the likelihood that a candidate solution will satisfy all constraints. Used in acquisition functions like CEI [12] [11]. |
| Constraint Dominance Principle (CDP) | A simple yet powerful rule for comparing two solutions during selection, prioritizing feasibility and guiding the population toward feasible regions [8]. |
Workflow: Adaptive Constraint Handling
The following diagram illustrates a generalized workflow for an adaptive constraint handling technique, integrating concepts from two-stage methods and surrogate assistance.
Framework for Constrained Molecular Optimization
This diagram outlines the CMOMO framework, a specific two-stage approach for constrained multi-objective molecular optimization in drug discovery [3].
Frequently Asked Questions
Q: What is the No Free Lunch (NFL) Theorem in the context of optimization?
- A: The No Free Lunch Theorem states that when the performance of all optimization algorithms is averaged across all possible problems, they all perform equally well [13] [14]. This means there is no single "best" constraint-handling technique (CHT) that is superior for every Constrained Optimization Problem (COP) you may encounter [15].
Q: If no single technique is the best, how should I select a CHT for my research?
- A: Since no algorithm has a priori superiority, your selection strategy is crucial. The NFL theorem implies that you must leverage problem-specific knowledge to choose or design a CHT [14]. Success comes from tailoring the algorithm's inductive biases to the specific structure of your problem, rather than seeking a universal method [16] [17].
Q: My population is getting stuck in local optima. What CHT strategies can help?
- A: This is a common issue. Advanced CHTs incorporate mechanisms to escape local optima. For example, one approach is to use a simple population restart mechanism when a specific criterion indicates the population is trapped in a local optimum, particularly in the infeasible region [18]. Another strategy is to use a hybrid technique that adapts its search strategy based on the population's state [18].
Q: How can I handle problems with a large number of constraints?
- A: One effective method is to decompose the problem. A classification-collaboration constraint handling technique randomly classifies constraints into
Kclasses, decomposing the original problem intoKsimpler subproblems [19]. Each subpopulation then evolves to handle its assigned subset of constraints, and they interact through learning strategies to collaboratively solve the original problem [19].
- A: One effective method is to decompose the problem. A classification-collaboration constraint handling technique randomly classifies constraints into
Q: Are hybrid CHTs more effective than single-method approaches?
- A: Often, yes. Hybrid techniques are designed to leverage the strengths of different methods. For instance, a Hybrid Constraint-handling Technique (HCT) might define different population situations (infeasible, semi-feasible, feasible) and apply a tailored CHT for each situation [18]. This adaptive behavior can lead to more robust performance across various problem types.
Troubleshooting Common Experimental Issues
| Problem Description | Possible Causes | Recommended Solutions |
|---|---|---|
| Premature Convergence (Population loses diversity and gets stuck early) | Overly greedy feasibility rules; lack of diversity-preserving mechanisms. | Implement a restart mechanism [18]. Use a multi-objective approach to maintain a diverse set of solutions [20]. Introduce elite replacement strategies to accumulate experience [18]. |
| Inability to Find Feasible Solutions | Population is far from the feasible region; constraints are too restrictive. | For the "infeasible situation," use techniques that help the population move toward feasibility, like an elite replacement strategy [18]. Employ a repair strategy, such as Random Direction Repair (RDR), to guide infeasible solutions toward the feasible region [19]. |
| Poor Performance on Specific Problem Types | The chosen CHT's inductive bias does not align with the problem's structure. | Switch the CHT based on the problem's features (e.g., number of constraints, location of the optimum) [14]. Use an adaptive framework like ECO-HCT that automatically switches strategies based on population information [18]. |
| High Computational Cost | Complex CHTs; expensive fitness evaluations for feasibility. | Decompose the problem using a classification-collaboration technique to reduce the complexity per evaluation [19]. Use a predictive model like an estimation of distribution algorithm to guide the search and reduce evaluations [19]. |
Experimental Protocols & Methodologies
1. Protocol for Comparing CHT Performance
This protocol provides a standardized way to evaluate and compare different CHTs on your specific set of COPs.
- Objective: To empirically determine the most effective CHT for a given class of COPs.
- Benchmark Sets: Utilize standard constrained test suites such as IEEE CEC2006 (24 functions) and IEEE CEC2017 (28 functions) to ensure comparable results [18] [19].
- Performance Metrics: Define and measure the following for each algorithm:
- Best Feasible Objective Value: The best
f(x)found whereG(x) = 0. - Feasibility Rate: The percentage of runs that find at least one feasible solution.
- Average Computational Cost: Measured in number of function evaluations or time.
- Best Feasible Objective Value: The best
- Experimental Setup:
- Run each algorithm over a significant number of independent runs (e.g., 30).
- Use statistical tests (e.g., Wilcoxon signed-rank test) to validate the significance of performance differences.
2. Protocol for Implementing a Hybrid CHT (e.g., ECO-HCT)
This methodology outlines the steps to implement an adaptive hybrid technique.
- Step 1: Define Population Situations. Categorize the population's state based on the number of feasible individuals [18]:
- Infeasible Situation: Most individuals are infeasible.
- Semi-feasible Situation: A mix of feasible and infeasible individuals.
- Feasible Situation: Most or all individuals are feasible.
- Step 2: Assign CHTs to Situations.
- Infeasible: Focus on minimizing total constraint violation
G(x). Use an elite replacement strategy to preserve good infeasible solutions that are close to feasibility [18]. - Semi-feasible: Balance objective and constraints using methods like stochastic ranking or an
ɛ-constraint method [18] [19]. - Feasible: Focus on minimizing the objective function
f(x)while maintaining feasibility.
- Infeasible: Focus on minimizing total constraint violation
- Step 3: Implement a Restart Mechanism. Define a criterion (e.g., no improvement in best feasible solution for
Ngenerations) to trigger a population restart and help escape local optima [18].
The Scientist's Toolkit: Research Reagent Solutions
| Item / Concept | Function in Constrained Optimization |
|---|---|
| Constraint Violation (G(x)) | A metric quantifying how much a solution x violates all constraints. It is the foundation for most CHTs [18] [19]. |
| Feasibility Rule | A simple, powerful CHT that prefers feasible solutions over infeasible ones, and among feasible solutions, prefers those with a better objective value [19]. |
| ɛ-Constraint Method | A CHT that relaxes the feasibility requirement by allowing solutions with a constraint violation below a threshold ɛ to be treated as feasible, enabling a more gradual approach to the feasible region [19]. |
| Stochastic Ranking | A technique that introduces a probability P to balance the influence of objective function and constraint violation during selection, preventing overly greedy behavior [19]. |
| Multi-Objective Transformation | A method that transforms a COP into a multi-objective problem, treating constraint violations as separate objectives to be minimized [20]. |
| Penalty Function | A method that combines the objective function and constraint violation into a single function using penalty coefficients, which can be fixed, dynamic, or adaptive [19]. |
| Hybrid CHT (HCT) | A framework that combines different CHTs and switches between them adaptively based on the current state of the population during evolution [18]. |
Frequently Asked Questions
1. What are the fundamental types of constraints encountered in optimization problems? Optimization problems typically involve four main types of constraints [21]:
- Bound Constraints: These are simple lower and upper limits on individual variables (e.g., ( x ≥ l ) and ( x ≤ u )).
- Linear Inequality Constraints: Expressed in the matrix form ( A·x ≤ b ), they represent multiple linear conditions that the solution must not exceed.
- Linear Equality Constraints: Expressed as ( A{eq}·x = b{eq} ), they define exact linear relationships that the solution must satisfy.
- Nonlinear Constraints: These are general constraints of the form ( c(x) ≤ 0 ) and ( ceq(x) = 0 ), where ( c ) and ( ceq ) can be scalar or vector functions.
2. How should I efficiently formulate a constraint? For both efficiency and numerical stability, use the lowest-numbered constraint type possible from the following hierarchy [21]:
- Bounds
- Linear equalities
- Linear inequalities
- Nonlinear equalities
- Nonlinear inequalities For example, a constraint like ( 5x ≤ 20 ) should be formulated as a bound ( x ≤ 4 ) instead of a linear or nonlinear inequality [21].
3. What is the standard mathematical representation for problems with both equality and inequality constraints? A constrained optimization problem is often written in the standard form [22]: Maximize ( f(x) ) Subject to: ( gi(x) ≤ 0 ), for ( i = 1, ..., m ) ( hj(x) = 0 ), for ( j = 1, ..., p ) Note that any "greater than or equal to" inequality can be converted to this "less than or equal to" form by multiplying by -1 [21] [22].
4. What is a major challenge when optimizing molecular properties under drug-like constraints? A key challenge is the disconnected and irregular feasible molecular space created by stringent drug-like constraints (e.g., specific ring sizes) [23]. This makes it difficult to find molecules that are both high-performing and feasible. Effective strategies must balance property optimization with constraint satisfaction, often by dynamically handling constraints during the search process [23].
5. What are the Karush-Kuhn-Tucker (KKT) conditions? The KKT conditions are first-order necessary conditions for a solution to be optimal in a constrained nonlinear optimization problem. They extend the method of Lagrange multipliers to include inequality constraints [22]. For a solution to be a candidate optimum, there must exist Lagrange multipliers ( ( λi ) for inequalities and ( μj ) for equalities) such that the gradient of the Lagrangian function is zero, the constraints are satisfied, and the complementary slackness condition holds: ( λi \cdot gi(x) = 0 ) [22]. This means either an inequality constraint is active ( ( g_i(x) = 0 ) ) or its corresponding multiplier is zero.
Experimental Protocol: Dynamic Cooperative Optimization for Constrained Molecular Problems
This protocol is adapted from the CMOMO framework for constrained multi-property molecular optimization [23].
1. Objective To simultaneously optimize multiple molecular properties while satisfying several structural or drug-like constraints.
2. Materials and Reagents
| Item | Function in the Experiment |
|---|---|
| Lead Molecule (SMILES string) | The starting point for optimization, represented by its Simplified Molecular Input Line Entry System string. |
| Public Molecular Database | Used to construct a "Bank" library of high-property molecules similar to the lead for high-quality population initialization. |
| Pre-trained Molecular Encoder | A model that converts discrete molecular structures (SMILES) into continuous vector representations for efficient search. |
| Pre-trained Molecular Decoder | A model that converts continuous vectors back into valid molecular structures for property evaluation. |
| Property Evaluation Software | Tools to compute the target molecular properties (e.g., QED, PlogP) for each generated molecule. |
| Constraint Checking Scripts | Custom scripts to verify if a generated molecule adheres to the defined structural constraints (e.g., ring size rules). |
3. Methodology
Step 1: Population Initialization
- Construct a Bank library from a public database containing molecules with high desired properties that are structurally similar to the lead molecule.
- Encode the lead molecule and all molecules in the Bank library into a continuous latent space using the pre-trained encoder.
- Generate an initial population of molecules by performing linear crossover between the latent vector of the lead molecule and the latent vectors of molecules in the Bank library.
Step 2: Dynamic Cooperative Optimization This step involves an iterative evolutionary process that dynamically handles constraints.
- A. Unconstrained Scenario Search:
- Use a Vector Fragmentation-based Evolutionary Reproduction (VFER) strategy on the latent population to generate offspring in the continuous space.
- Decode both parent and offspring molecules back to discrete chemical structures (SMILES) using the pre-trained decoder.
- Evaluate the properties of all molecules.
- Select the best molecules for the next generation using a multi-objective selection strategy (e.g., NSGA-II) based solely on their property values, ignoring constraints at this stage. The goal is to first find molecules with good convergence and diversity of properties.
- B. Transition to Constrained Scenario:
- After iterating in the unconstrained scenario, shift the focus to finding molecules that are both high-performing and feasible.
- The selection criteria are modified to prioritize molecules that satisfy all constraints while maintaining good property values.
- C. Iteration:
- Repeat the reproduction, evaluation, and selection steps until a termination criterion is met (e.g., a maximum number of generations or convergence of the population).
4. Expected Results The algorithm is expected to output a set of Pareto-optimal molecules that represent the best trade-offs between the multiple optimized properties, all while satisfying the predefined drug-like constraints.
The Scientist's Toolkit: Research Reagent Solutions
| Reagent / Solution | Function |
|---|---|
| Pre-trained Molecular Encoder/Decoder | Enables a smooth and efficient search for molecules by translating between discrete chemical space (SMILES) and a continuous, meaningful latent space. |
| Constraint Handling Strategy (e.g., Dynamic) | Manages how constraints are applied during optimization. A dynamic strategy can first focus on finding high-performance solutions before filtering for feasibility, preventing premature convergence. |
| Multi-Objective Selection Algorithm (e.g., NSGA-II) | Manages the trade-offs between conflicting property objectives by selecting a diverse set of solutions that are non-dominated, forming a Pareto front. |
| Feasible Region Analyzer | A diagnostic tool to understand the search space defined by the constraints, helping to identify whether it is connected, convex, or disjoint, which impacts algorithm choice. |
Constraint Types in Optimization
The table below summarizes the primary constraint types used in numerical optimization, which form the basis for more complex constraint landscapes [21].
| Constraint Type | Standard Form | Key Characteristics |
|---|---|---|
| Bound Constraints | ( x ≥ l ) and ( x ≤ u ) | Simplest form; define min/max values for each variable. |
| Linear Inequality | ( A·x ≤ b ) | Define a convex, multi-dimensional half-space. |
| Linear Equality | ( A{eq}·x = b{eq} ) | Restrict solutions to a line or plane; reduce solution space dimension. |
| Nonlinear Constraints | ( c(x) ≤ 0 ) and ( ceq(x) = 0 ) | Most general form; can create non-convex, complex feasible regions. |
Adaptive Constraint Handling Workflow
The following diagram illustrates the logical flow of the dynamic cooperative optimization method (CMOMO) for handling complex constraints, which transitions from an unconstrained to a constrained search to effectively balance property optimization with constraint satisfaction [23].
Constrained Multi-Objective Optimization Problems (CMOPs) require the simultaneous optimization of multiple conflicting objectives while satisfying various constraints. These problems are ubiquitous in real-world applications, including engineering design, resource allocation, scheduling optimization, and drug development [24] [25]. A CMOP can be mathematically formulated as follows [25]:
Minimize: F(x) = (f₁(x), f₂(x), ..., fₘ(x))
Subject to: gᵢ(x) ≤ 0, i = 1, ..., l hᵢ(x) = 0, i = 1, ..., k x = (x₁, x₂, ..., xD)T ∈ ℝ
Here, F(x) represents the objective vector with m conflicting objectives, gᵢ(x) are inequality constraints, hᵢ(x) are equality constraints, and x is a D-dimensional decision vector within the search space ℝ [25]. The core challenge lies in balancing objective optimization with constraint satisfaction, a task for which Multi-Objective Evolutionary Algorithms (MOEAs) have proven particularly effective due to their population-based approach and ability to handle complex, non-linear landscapes [25].
Frequently Asked Questions (FAQs)
Q1: What is the fundamental difference between handling constraints in single-objective versus multi-objective optimization?
In single-objective optimization, the goal is to find a single optimal solution that satisfies all constraints. In multi-objective optimization, the aim is to find a set of trade-off solutions, known as the Pareto front. When constraints are involved, this becomes the Constrained Pareto Front (CPF). The challenge is magnified because you must balance not only multiple objectives but also ensure a diverse set of solutions satisfies all constraints. The principle remains similar—feasible solutions are preferred over infeasible ones—but the techniques must be integrated into the environmental selection process of a Multi-Objective Evolutionary Algorithm (MOEA) to manage a population of solutions, not just a single one [25].
Q2: My algorithm converges prematurely to a local optimum. How can I encourage better exploration of the search space?
Premature convergence often occurs when the algorithm is overly greedy in selecting feasible solutions early on, trapping the population in a limited feasible region. Several strategies can mitigate this:
- Implement a Multi-Stage Framework: Relax constraints in the initial stage to allow exploration of infeasible regions that might contain useful information. In subsequent stages, gradually enforce strict constraints to pull promising solutions toward feasibility [26] [8].
- Use a Multi-Population Approach: Maintain separate populations with different tasks. For example, one population can focus on optimizing objectives without considering constraints, while another works on finding feasible solutions. Allowing knowledge transfer between these populations can enhance overall exploration [26].
- Employ an Archive Mechanism: An external archive can store promising infeasible solutions or those from under-explored regions. This information can be used later to guide the population out of local optima [8].
Q3: What does a "good" feasible solution proportion look like during evolution, and when should I intervene?
There is no universally ideal proportion, as it is highly problem-dependent. However, monitoring this proportion is crucial for adaptive techniques. A very low proportion of feasible solutions (e.g., near 0%) throughout the run suggests the constraints are very difficult, and your algorithm might need to relax them to find any feasible region. Conversely, a very high proportion (e.g., near 100%) very early might indicate premature convergence. A common intervention is to use an adaptive constraint relaxation mechanism. For instance, you can dynamically adjust a relaxation parameter ε based on the current feasible ratio, tightening it as more feasible solutions are found to refine the search [8].
Q4: How can I handle problems where the global optimum lies on a narrow feasible boundary?
This is a classic challenge. Techniques that are overly strict with feasibility can easily miss these narrow regions. Consider the following:
- ε-Constraint Method: This technique allows infeasible solutions with a constraint violation below a threshold
εto be treated as feasible. This enables the algorithm to "tunnel through" infeasible regions to reach distant or narrow feasible areas. The thresholdεcan be adaptively decreased during the evolutionary process [27] [28]. - Stochastic Ranking: This method introduces a probability
Pof comparing infeasible solutions based on their objective function value, rather than always ranking by constraint violation. This provides a chance for infeasible solutions with good objective values (which might be near a narrow feasible boundary) to survive and contribute to the search [27] [19].
Troubleshooting Common Experimental Issues
Issue 1: Poor Diversity in Final Solution Set
- Symptoms: The obtained solutions are clustered in a small area of the Constrained Pareto Front (CPF), failing to cover its full extent.
- Potential Causes:
- Over-emphasis on Feasibility: The Constraint Dominance Principle (CDP) can be too greedy, causing the population to lose diversity once it enters a feasible region.
- Poor Mating Selection: Selection pressure focuses only on convergence and feasibility, neglecting diversity maintenance.
- Solutions:
- Integrate Diversity Metrics: Incorporate diversity measures, such as crowding distance or angle-based selection, into the environmental selection process. This ensures that solutions in sparser regions are preserved [26].
- Use Decomposition-Based MOEAs: Algorithms like MOEA/D decompose the problem into several single-objective subproblems. This naturally promotes diversity by forcing the population to spread across these subproblems [25].
- Diversity-Based Archive Ranking: When updating an archive, rank solutions not only by feasibility and convergence but also by their contribution to population diversity [8].
Issue 2: Inability to Find Any Feasible Solutions
- Symptoms: The algorithm terminates without finding a single feasible solution.
- Potential Causes:
- Overly Strict Equality Constraints: Equality constraints are too tight, making the feasible space extremely small or a set of measure zero.
- Insufficient Exploration: The algorithm is not effectively exploring the search space and is missing feasible regions entirely.
- Solutions:
- Relax Equality Constraints: Convert equality constraints
h(x) = 0into inequality constraints|h(x)| - δ ≤ 0, whereδis a small tolerance value (e.g., 1e-4 or 1e-6). This is a standard and necessary practice [27] [25]. - Employ a Push-Pull Framework: In the "Push" stage, completely ignore constraints to encourage global exploration of the objective space. In the "Pull" stage, apply constraint handling techniques to guide the discovered promising solutions toward feasibility [26].
- Adaptive Relaxation: Implement an algorithm like ACREA, which adaptively relaxes constraints based on the current population's state, making it easier to find initial feasible solutions and then tightening the relaxation over time [8].
- Relax Equality Constraints: Convert equality constraints
Issue 3: High Computational Cost
- Symptoms: The algorithm takes an impractically long time to converge, especially when function evaluations are expensive.
- Potential Causes:
- Inefficient Constraint Handling: The method for calculating and comparing constraint violations is computationally heavy.
- Lack of Surrogate Models: Every solution is evaluated using the true, expensive functions.
- Solutions:
- Surrogate-Assisted Evolution: Train machine learning models (e.g., Kriging, neural networks) to approximate the objective and constraint functions. The evolutionary algorithm then works primarily on these cheap surrogates, only occasionally calling the true expensive functions [27].
- Ensemble Constraint Handling: Techniques like RECHT use a ranking-based ensemble to dynamically select the most effective constraint handling technique, which can reduce the number of function evaluations required to find a good solution [28].
- Feasibility-Aware Mating Selection: Before generating offspring, ensure that parents are selected in a way that promotes the generation of feasible or promising infeasible solutions, reducing wasted evaluations [19].
Experimental Protocols for Key Constraint Handling Techniques
Protocol 1: Evaluating a Two-Stage Archive (CMOEA-TA) Algorithm
This protocol is based on the CMOEA-TA framework, which uses different strategies at different stages of evolution [26].
- Initialization: Randomly generate an initial population P and an empty archive A.
- Stage 1 - Exploration with Relaxed Constraints:
- Constraint Relaxation: Calculate the proportion of feasible solutions in the population. Based on this proportion and the overall constraint violation, relax the constraints. For example, treat a solution as "relaxed-feasible" if its total constraint violation
CV(x)is less than a dynamically adjusted thresholdε. - Archive Update: The archive A stores the best solutions found under these relaxed constraints, focusing on optimizing the objectives.
- Goal: Encourage the population to explore the entire search space, including promising infeasible regions, to build a global picture of the Pareto front.
- Constraint Relaxation: Calculate the proportion of feasible solutions in the population. Based on this proportion and the overall constraint violation, relax the constraints. For example, treat a solution as "relaxed-feasible" if its total constraint violation
- Stage 2 - Exploitation with Strict Constraints:
- Information Sharing: Merge the archive A with the current population P.
- Strict Constraint Handling: Switch to a strict constraint handling method, such as the Constraint Dominance Principle (CDP), to refine the solutions.
- Angle-Based Selection: To maintain diversity, use an angle-based selection strategy that prioritizes solutions that increase the spread of the population on the Pareto front.
- Termination: Repeat Stage 2 until a termination criterion (e.g., maximum number of evaluations) is met. The output is the set of non-dominated feasible solutions from the final population and archive.
Protocol 2: Implementing an Adaptive Constraint Relaxation (ACREA)
This protocol focuses on dynamically adjusting how constraints are handled based on the algorithm's progress [8].
- Initialization: Generate an initial population. Initialize the relaxation parameter
εto a large value. - Main Loop:
- Evaluate & Classify: Evaluate all individuals and calculate their constraint violation
CV(x). Classify them as feasible or infeasible based on the currentε. - Archive Management: Maintain an archive that stores high-quality solutions (both feasible and promising infeasible ones) using a diversity-based ranking to ensure a good spread.
- Mating Selection: For parent selection, use a strict domination principle that strongly favors feasible solutions and high-quality infeasible solutions with low constraint violation.
- Adapt
ε: Periodically, adjust the relaxation parameterεbased on feedback from the population. A simple rule is to decreaseεif the proportion of feasible solutions is high, and increase it if the proportion is too low. This adaptively balances exploration and exploitation.
- Evaluate & Classify: Evaluate all individuals and calculate their constraint violation
- Termination: The algorithm outputs the non-dominated feasible solutions from the final population and archive.
Quantitative Data on Algorithm Performance
The following table summarizes the reported performance of several state-of-the-art algorithms on standard benchmark problems, as found in the literature. Metrics like IGD (Inverted Generational Distance) and HV (Hypervolume) are commonly used, where lower IGD and higher HV values indicate better performance.
Table 1: Performance Comparison of State-of-the-Art CMOEAs
| Algorithm | Key Mechanism | Reported Performance (vs. Competitors) | Best For |
|---|---|---|---|
| CMOEA-TA [26] | Two-Stage with Archive | "Far superior" in IGD and HV on 54 benchmark CMOPs. | Complex feasible regions, maintaining diversity. |
| ACREA [8] | Adaptive Constraint Relaxation | Best IGD in 54.6% and best HV in 50% of 44 benchmark tests. Best in 7 of 9 real-world problems. | Problems with large or narrow infeasible regions. |
| EALSPM [19] | Learning Strategies & Predictive Model | "Competitive performance" on CEC2010 and CEC2017 benchmarks. | Leveraging information from good individuals for faster convergence. |
| RECHT [28] | Ranking-Based Ensemble | "Superior performance" on CEC benchmarks, reduces function evaluations. | General-purpose, robust performance across diverse problems. |
Research Reagent Solutions: Essential Algorithmic Components
In experimental optimization, think of these core algorithmic components as your essential "reagents" for designing a successful CMOEA.
Table 2: Essential Components for a CMOEA Framework
| Component / "Reagent" | Function | Examples |
|---|---|---|
| Base MOEA | Provides the core multi-objective optimization engine. | NSGA-II, MOEA/D, SPEA2 [25] |
| Constraint Handling Technique (CHT) | Manages how constraints are evaluated and used to guide selection. | Constraint Dominance Principle (CDP), ε-Constraint, Stochastic Ranking [27] [25] |
| Archiving Mechanism | Stores high-quality solutions (feasible and infeasible) during evolution for later use. | Two-Stage Archive, Diversity-Based Archive [26] [8] |
| Relaxation Strategy | Dynamically adjusts the strictness of constraints to aid exploration. | Adaptive ε-Level, Feasibility Proportion-based Relaxation [8] |
| Surrogate Model | Approximates expensive objective/constraint functions to reduce computational cost. | Kriging, Neural Networks, Polynomial Regression [27] |
Visualized Workflows
The following diagrams illustrate the logical structure of two prevalent algorithmic frameworks for solving CMOPs.
Diagram 1: Two-Stage Archive (CMOEA-TA) Workflow. This framework separates exploration (with relaxed constraints) from exploitation (with strict constraints), using an archive to bridge the two stages [26].
Diagram 2: Adaptive Constraint Relaxation (ACREA) Workflow. This algorithm features a continuous feedback loop where the constraint relaxation parameter ε is dynamically adapted based on the population's state [8].
Advanced Adaptive CHT Methodologies: Techniques and Implementations
Frequently Asked Questions (FAQs)
Q1: What are the common reasons for slow learning convergence when using DRL for CHT selection? Slow learning convergence is often caused by a poorly designed state representation. If the state does not succinctly capture task-relevant information like feasibility, convergence, and diversity of the population, the agent struggles to learn an effective policy. Using raw coordinates or data that includes irrelevant information forces the agent to learn complex relationships from scratch, significantly reducing sample efficiency [29]. Furthermore, a lack of diversity in the training data, which can be mitigated by using multiple co-evolving populations, also hampers the learning process [30].
Q2: How can I design an effective state representation for my COP agent? An effective state representation should be compact, informative, and generalizable. Instead of raw coordinates, it should encode meaningful relationships. A proven approach includes [29]:
- Directional information: Representing the direction to a goal as a compass direction.
- Distance information: Using normalized distance to a goal.
- Constraint awareness: Including information about constraint violations or the "danger" from nearby constrained regions.
- Diversity and convergence metrics: Incorporating information on the population's feasibility, convergence, and diversity to guide the search in COPs [30]. This transforms raw data into features that directly inform the optimal policy.
Q3: My DRL agent fails to satisfy state-wise constraints. What methods can help? The State-wise Constrained Policy Optimization (SCPO) algorithm is specifically designed for this challenge. Unlike traditional Constrained MDP (CMDP) frameworks that often only consider cumulative constraints, SCPO provides guarantees for state-wise constraint satisfaction in expectation. It introduces the framework of Maximum Markov Decision Process and has been demonstrated to effectively bound the worst-case safety violation in high-dimensional tasks like robot locomotion [31].
Q4: Can Q-learning be integrated with other architectures to solve complex scheduling COPs? Yes. A powerful example is the Two-stage Graph Attention Networks and Q-learning (TSGAT+Q-learning) framework for maintenance task scheduling. This method uses a graph neural network (GNN) to embed complex graph-structured information about the problem (like technicians and tasks). The output of this network is then used as the input state for a Q-learning agent, which makes the final scheduling decisions. This hybrid approach combines the representational power of GNNs with the decision-making capabilities of Q-learning to solve large-scale, constrained problems [32].
Troubleshooting Guides
Issue 1: Poor Generalization Across Different COP Datasets Problem: Your DRL agent, trained on one dataset, performs poorly on another with a different distribution of constraints or objective functions. Solution:
- Implement an Adaptive Learning Framework: Use a framework like Adaptive-DTA, which employs reinforcement learning to automatically search for and optimize the neural network architecture based on the specific dataset and task. This reduces reliance on fixed, manually-designed architectures [33].
- Use Multiple CHTs: Incorporate multiple constraint handling techniques (CHTs) within a co-evolutionary framework. Different populations can be assigned different CHTs, enhancing the algorithm's versatility and ability to handle a wider range of problems [30].
- Verify State Representation: Ensure your state representation is not over-fitted to the training dataset. Features should be relative (e.g., directional information, normalized distances) rather than absolute (e.g., specific coordinates) to improve generalization [29].
Issue 2: Inefficient or Unstable Training of the Q-Network Problem: The Q-network fails to converge, or the training process is unstable with high variance in rewards. Solution:
- Design a Better Reward Function: The reward should closely reflect the overall improvement of the population. In CEDE-DRL, rewards are based on the degree of improvement in feasibility, convergence, and diversity. For scheduling problems, novel rewards like an exponential reward function have been shown to speed up training [30] [32].
- Improve State Representation: Revisit the state design. A well-structured state that provides relevant information is crucial for stable learning. Poor state representations are a primary cause of slow and unstable training [29].
- Ensure Diverse Training Data: In co-evolutionary DRL, use multiple populations to generate diverse training samples. This improves the accuracy of the neural network model and stabilizes training by providing a richer set of experiences [30].
Issue 3: Agent Cannot Handle State-Wise Safety Constraints Problem: The agent violates hard constraints that must be satisfied at every step (state-wise), not just on average. Solution:
- Adopt a State-Wise Constrained Algorithm: Move beyond standard CMDP algorithms. Implement the SCPO algorithm, which is a general-purpose policy search method designed specifically for state-wise constrained reinforcement learning. It provides theoretical guarantees for state-wise constraint satisfaction [31].
- Refine State and Reward: Integrate explicit constraint violation metrics into the state representation. The reward function should also provide a strong, clear penalty for any state-wise constraint violation to guide the agent away from unsafe states.
Experimental Protocols & Methodologies
Protocol 1: CEDE-DRL for Constrained Optimization This protocol is for solving COPs using a co-evolutionary framework with DRL [30].
- Initialization: Create four sub-populations, each assigned a different CHT to ensure generality.
- State Representation: For each population, define the state
sto include metrics for:- Feasibility (e.g., degree of constraint violation)
- Convergence (e.g., improvement in objective function)
- Diversity (e.g., distribution of solutions)
- Action and Reward: The DQN agent selects a parent population for mutation. The reward is the overall improvement of the population.
- Training: Train the DQN model using experiences generated from the co-evolving populations. An archive elimination mechanism helps avoid local optima.
- Evaluation: Compare performance against state-of-the-art algorithms on benchmark sets like CEC2017 and real-world problems from CEC2020.
Protocol 2: Optimal Adaptive Allocation in Clinical Trials This protocol uses DRL for adaptive patient allocation in phase II dose-ranging trials [34].
- Problem Setup: Predetermine
Kdiscrete dose levels and the total number of subjectsN. - State Definition: The state
sis a vector containing:- The mean response difference from placebo for each dose
(Ȳ₂-Ȳ₁, Ȳ₃-Ȳ₁, ..., Ȳκ-Ȳ₁) - The standard deviation of responses for each dose
(σ̂₁, ..., σ̂κ) - The proportion of subjects allocated to each dose
(n₁/N, ..., nκ/N)
- The mean response difference from placebo for each dose
- Action: Allocate the next block of patients to a dose based on the policy.
- Reward: The reward is based on the selected performance metric to be optimized, such as:
- Statistical Power
- Accuracy of Model Selection (MS)
- Accuracy of the Target Dose (TD)
- Mean Absolute Error (MAE) of the dose-response curve
- Optimization: Use DRL to find an allocation rule
π*that directly optimizes the chosen metric, outperforming equal allocation or asymptotic methods like D-optimal.
The Scientist's Toolkit: Research Reagent Solutions
| Item/Component | Function in the Experimental Framework |
|---|---|
| Co-evolutionary Populations | Maintains multiple populations with different CHTs to ensure sample diversity and improve neural network training accuracy [30]. |
| Deep Q-Network (DQN) | The core RL agent that evaluates the population state and selects suitable parent populations for mutation, guiding evolutionary direction [30]. |
| Directed Acyclic Graph (DAG) | Defines a flexible search space for neural network architectures, enabling automated model design in frameworks like Adaptive-DTA [33]. |
| Graph Neural Network (GNN) | Processes graph-structured data (e.g., molecular structures, task-agent networks) to learn meaningful embeddings for downstream decision-making [33] [32]. |
| State-wise Constrained Policy Optimization (SCPO) | A specialized algorithm for enforcing state-wise safety constraints, providing satisfaction guarantees in expectation [31]. |
| Exponential Reward Function | A specially designed reward signal (e.g., in TSGAT+Q-learning) to accelerate model training convergence in REINFORCE algorithms [32]. |
Workflow and System Diagrams
The following diagram illustrates the typical workflow for integrating Deep Q-Learning with state representation for adaptive CHT selection:
This diagram outlines the integration of a co-evolutionary structure with the DRL agent for more robust training:
Frequently Asked Questions
Q1: What is the primary advantage of using a multi-stage framework over a single-stage approach for Constrained Multi-Objective Optimization Problems (CMOPs)?
A multi-stage evolutionary framework addresses a key limitation of single-stage approaches: their inability to adapt to the changing characteristics of a population during the search process. By dividing the optimization into distinct phases, each with a specialized strategy, these frameworks can more effectively balance the conflict between constraint satisfaction and objective optimization. For example, the Multi-Stage Evolutionary Framework with Adaptive Selection (MSEFAS) uses different stages to encourage promising infeasible solutions to approach the feasible region, increase diversity, span large infeasible regions to accelerate convergence, and finally handle the relationship between constrained and unconstrained Pareto fronts. This adaptive, staged approach has demonstrated effectiveness in handling a wide range of CMOPs with complex feasible regions [5].
Q2: How does an algorithm adaptively determine when to switch between stages?
Advanced frameworks use performance metrics or population state features to trigger stage transitions autonomously. The MSEFAS framework, for instance, treats the optimization stage with higher validity of selected solutions as the first stage and the other as the second, effectively using solution quality to determine execution order [5]. Other approaches, like the Evolutionary Algorithm assisted by Learning Strategies and a Predictive Model (EALSPM), divide the evolutionary process into random learning and directed learning stages, where subpopulations interact using different strategies [19]. Furthermore, Deep Reinforcement Learning (DRL)-based methods can model this as a Markov Decision Process, using neural networks to learn the optimal policy for stage transitions based on real-time population state features [35].
Q3: Why does my algorithm converge to locally optimal, feasible solutions instead of exploring the global Pareto front?
This common issue, known as "feasibility-driven greediness," occurs when the algorithm prioritizes constraint satisfaction over objective optimization too aggressively. This is particularly problematic in CMOPs where the global optimum lies near constraint boundaries or where feasible regions are disconnected. To address this:
- Implement Feasibility Rules with Objective Information: Approaches like FROFI (Feasibility Rule with Objective Function Information) utilize objective function information to mitigate the well-known greediness of feasibility rules [19].
- Balance Search Efforts: Ensure your framework includes stages that specifically enable the population to span large infeasible regions. This helps maintain diversity and prevents premature convergence to the first encountered feasible region [5].
- Adaptive Constraint Handling: Techniques like the adaptive ε-constraint method control the level of constraint relaxation through heuristic rules based on the current population's constraint violation information, helping the population traverse infeasible regions to reach better feasible areas [19].
Q4: How can I effectively utilize infeasible solutions during the optimization process?
Infeasible solutions can provide valuable information about promising search directions, especially when feasible regions are disconnected or narrow. The key is a balanced approach:
- Controlled Acceptance: Some multi-stage frameworks deliberately encourage promising infeasible solutions to approach the feasible region while increasing diversity in the early stages of optimization [5].
- Information Mining: Techniques like CORCO (Constraint and Objective Relationship Guided Optimization) mine the correlation between constraints and the objective to guide evolution, leveraging information from both feasible and infeasible solutions [19].
- Co-evolutionary Techniques: Algorithms like C-TAEA, CCMODE, and CCMO maintain multiple populations to achieve a balanced search in both feasible and infeasible regions [5].
Q5: What are the signs of poor stage sequencing, and how can it be diagnosed?
Poor stage sequencing manifests as:
- Slow Convergence: The population takes too long to approach the feasible region or the Pareto front.
- Diversity Loss: The population lacks spread across the Pareto front, often getting stuck in one area.
- Premature Convergence: The algorithm converges to a local optimum early in the process.
Diagnosis should involve monitoring key population metrics:
- Track the proportion of feasible solutions over generations.
- Monitor the change in population diversity (e.g., using spread or spacing metrics).
- Observe the rate of improvement in objective values and overall constraint violation.
Q6: How can surrogate models be integrated into multi-stage evolutionary frameworks?
Surrogate models address computational cost by approximating expensive function evaluations. The Multi-Surrogate Framework with an Adaptive Selection Mechanism (MSFASM) demonstrates a two-stage integration:
- Algorithm Selection Stage: A reduced-dimensional Broad Learning System (BLS) adaptively selects the evolutionary algorithm with the best performance during the current optimization period.
- Optimization Stage: A multi-objective algorithm (e.g., NSGA-II) finds Pareto solutions that perform well on multiple surrogate models. An optimal point criterion then selects the final solutions without burdening the numerical simulator [36]. This approach improves adaptability to various problem types by addressing both algorithm and model selection [36].
Troubleshooting Guides
Issue 1: Population Diversity Collapse in Later Stages
Problem: The population loses diversity during the late-phase search, resulting in a poor approximation of the entire Pareto front.
Solution: Implement mechanisms to preserve diversity specifically in later stages.
- Recommended Technique: Introduce a diversity archive or modify the third stage of frameworks like MSEFAS to specifically consider the distribution of solutions along the Pareto front. Avoid relying solely on adaptive penalty terms in late optimization, as this can reduce diversity [5].
- Experimental Protocol:
- Setup: Use a CMOP benchmark with a disconnected feasible region or a discrete Pareto front (e.g., C-DTLZ series).
- Implementation: Augment your algorithm's final stage with a separate diversity archive. Use a crowding distance metric or a niche count to maintain a spread of solutions.
- Evaluation: Compare the performance (using metrics like Inverted Generational Distance and Spread) of the standard algorithm versus the diversity-augmented version over 30 independent runs.
Issue 2: Ineffective Handling of Problems with Disconnected Feasible Regions
Problem: The algorithm fails to find all disconnected feasible components, converging to only one.
Solution: Employ co-evolutionary or multi-population techniques that can explore multiple regions simultaneously.
- Recommended Technique: Adopt a classification-collaboration constraint handling technique, as seen in EALSPM. Here, constraints are randomly classified into K groups, decomposing the problem into K subproblems. K subpopulations then solve these subproblems, interacting through learning strategies [19].
- Experimental Protocol:
- Setup: Configure the EALSPM framework on a benchmark with disconnected feasible regions from CEC2010 or CEC2017.
- Parameters: Set the number of constraint classes, K. Subpopulation sizes can be equal. The random learning and directed learning stages facilitate interaction.
- Metrics: Measure the ratio of found feasible components to total known components and the coverage of the Pareto front over multiple runs.
Issue 3: Poor Adaptive Selection of Evolutionary Operators
Problem: The framework's performance is highly variable because it fails to select the most effective evolutionary operator (e.g., mutation strategy) for different problems or search stages.
Solution: Implement a learning-based auto-configuration system.
- Recommended Technique: Integrate a foundation model like SuperDE, which uses Deep Reinforcement Learning (DDQN) for component auto-configuration. Trained offline on diverse COPs, it can recommend optimal per-generation configurations (like mutation strategies and constraint handling techniques) for unseen problems in a zero-shot manner [35].
- Experimental Protocol:
- Setup: Use the SuperDE model or implement a similar DRL-based controller. Define a pool of candidate components (e.g., 4 mutation strategies and 7 constraint handling techniques).
- State Features: Design state features that reflect the population's distribution regarding decision variables, objectives, and constraints.
- Training/Execution: For a new problem, use the pre-trained SuperDE model to map the current population state to the most suitable algorithm components for each generation.
- Validation: Compare the performance against state-of-the-art algorithms on benchmark test suites to verify generalization and optimization performance [35].
Experimental Protocols & Methodologies
Protocol 1: Validating a Multi-Stage Framework (MSEFAS)
This protocol outlines the steps to test the core adaptive mechanics of a multi-stage framework like MSEFAS [5].
1. Objective: Verify that the adaptive stage sequencing and the three-stage process lead to superior performance on CMOPs with varying characteristics.
2. Materials (Benchmarks): A diverse set of 56 CMOP benchmarks, including problems where the unconstrained Pareto front is partially or completely infeasible.
3. Procedure:
- Step 1: For the early phase, run the two initial stages (diversity-focused and convergence-focused) and measure the "validity of selected solutions" to determine the adaptive execution order.
- Step 2: Proceed with the selected stage order, allowing the population to evolve.
- Step 3: In the late phase, activate the third stage to handle the relationship between the constrained and unconstrained Pareto fronts.
- Step 4: Terminate upon reaching the maximum function evaluations.
4. Comparison: Compare results against 11 state-of-the-art constrained multi-objective evolutionary algorithms (CMOEAs).
5. Key Metrics:
- Inverted Generational Distance (IGD)
- Hypervolume (HV)
- Feasibility Ratio
Protocol 2: Testing a Two-Stage Algorithm with Learning (EALSPM)
This protocol tests an algorithm that divides evolution into random and directed learning stages [19].
1. Objective: Evaluate the effectiveness of classification-collaboration constraint handling and the two-stage learning process.
2. Materials: Benchmark functions from CEC2010 and CEC2017, plus two practical problems.
3. Procedure:
- Initialization: Randomly classify all constraints into K classes, creating K subproblems. Generate K corresponding subpopulations.
- Stage 1 - Random Learning: Subpopulations evolve their subproblems and interact using random learning strategies.
- Stage 2 - Directed Learning: Subpopulations interact using directed learning strategies to generate potentially better solutions for the original problem.
- Offspring Prediction: An improved estimation of distribution model, based on good individuals, is used to predict offspring.
4. Key Metrics:
- Best Objective Function Value Found
- Consistency in Finding Feasible Solutions
- Statistical Significance Tests (e.g., Wilcoxon rank-sum test)
Research Reagent Solutions
The table below details key algorithmic components and their functions in adaptive multi-stage evolutionary frameworks.
| Research Reagent | Function / Purpose | Example Implementation |
|---|---|---|
| Feasibility Rule | A constraint handling technique that gives selection preference to feasible solutions over infeasible ones. Can be too greedy if used alone [19]. | A method where a feasible solution wins over an infeasible one; between two feasible solutions, the one with better objectives wins; between two infeasible solutions, the one with smaller constraint violation wins [19]. |
| Adaptive Penalty Function | Dynamically adjusts penalty coefficients applied to infeasible solutions based on evolutionary feedback (e.g., the proportion of feasible individuals) [19]. | In ASCHEA, penalty coefficients are adjusted each generation: if the proportion of feasible solutions is below a target, coefficients are increased [35]. |
| ε-Constraint Method | Relaxes constraints by a tolerance parameter ε, allowing some infeasible solutions to be considered, which helps in crossing wide infeasible regions. An adaptive version controls ε based on current population violation [19]. | A method where the constraint violation Gj(x) must be ≤ ε to be considered satisfied. The parameter ε can be adapted based on the population's CV information [19]. |
| Multi-Objective Optimization Technique | Transforms a Constrained Optimization Problem (COP) into an equivalent multi-objective problem, often treating constraint violation as an additional objective(s) to be minimized. | Converting a COP into a bi-objective optimization problem (BOP) minimizing both the original objective and the total constraint violation [19]. |
| Differential Evolution (DE) Operators | A set of mutation and crossover strategies used to generate new candidate solutions. Different strategies balance exploration and exploitation. | A pool of mutation strategies (e.g., DE/rand/1, DE/best/1) can be adaptively selected from during the evolutionary process [35]. |
| Surrogate Model (e.g., BLS, RBF) | A data-driven model that approximates expensive objective or constraint functions, drastically reducing computational cost in many real-world problems. | Using a Reduced-Dimensional Broad Learning System (BLS) to adaptively select the best-performing evolutionary algorithm during an optimization period [36]. |
Framework Workflow and Signaling
The following diagram illustrates the high-level logical structure and flow of information in a generalized multi-stage evolutionary framework with adaptive selection.
Multi-Stage Evolutionary Framework Logic
Component Configuration with DRL
For advanced frameworks, the adaptive selection mechanism can be powered by Deep Reinforcement Learning. The diagram below visualizes this DRL-assisted auto-configuration process as used in the SuperDE model.
DRL-Assisted Component Auto-Configuration
This workflow demonstrates the closed-loop interaction where the DRL agent (trained offline on diverse problems) observes the population state and selects optimal components for the next generation, receiving a reward based on the progress made, thus enabling online adaptation for unseen COPs [35].
Frequently Asked Questions
FAQ 1: What is variable-constraint mapping and why is it critical for repair-based constraint handling? Variable-constraint mapping is a binary matrix that defines which design variables significantly influence each constraint in a problem [37]. In repair-based constraint handling techniques (CHTs), this mapping is essential because it tells the optimization algorithm which specific variables to modify when a particular constraint is violated. Without this knowledge, repair CHTs require users to define complex, problem-specific heuristics, which is often difficult or impossible for real-world engineering problems with many nonlinear constraints [37]. An automated mapping makes the repair process fully autonomous.
FAQ 2: How can I automatically discover the variable-constraint mapping for my optimization problem? You can use a procedure based on feed-forward Artificial Neural Networks (ANNs) to autonomously discover this mapping [37]. The methodology is as follows:
- Data Collection: During the initial stages of optimization, collect data on all design vectors and their corresponding constraint function values.
- ANN Training: Train a separate ANN for each constraint. Each network takes the complete set of design variables as input and predicts the value of its specific constraint.
- Significance Analysis: Perform a sensitivity analysis on each trained ANN to determine which input variables have the most significant effect on the output (the constraint value).
- Matrix Construction: Construct the binary mapping matrix based on the results of the sensitivity analysis. A nonzero entry at position (i, j) indicates that variable
jsignificantly affects constrainti[37].
FAQ 3: My repaired solutions are causing a loss of diversity in the population. How can I mitigate this? This can occur if the same donor solutions are used repeatedly for repair. The modified repair-based CHT addresses this by repairing each constraint violation separately [37]. Instead of using a single solution to repair all violated constraints in an infeasible solution, identify the nearest solution in the objective space that does not violate a specific constraint and use only the relevant variables from that solution to repair that particular constraint. This approach utilizes knowledge from the broader population and helps maintain genetic diversity [37].
FAQ 4: How does the performance of the neural network-enabled repair CHT compare to other methods? The ANN-enabled repair CHT has been shown to obtain significantly better results than NSGA-II with other CHTs, including the constraint domination principle (CDP), static penalty, and dynamic penalty methods, across various test problems [37]. It improves both convergence speed and the diversity of solutions. The table below summarizes a quantitative comparison from a study implemented in NSGA-II.
Table 1: Performance Comparison of Different CHTs in NSGA-II
| Constraint Handling Technique (CHT) | Key Principle | Advantages | Disadvantages |
|---|---|---|---|
| Repair with ANN Mapping | Repairs infeasible solutions using donor solutions and automated variable-constraint mapping. | Fully autonomous; improves convergence and diversity [37]. | Requires initial data collection for ANN training. |
| Constraint Domination Principle (CDP) | Favors feasible over infeasible solutions; compares infeasibles by violation severity. | No parameters to tune; widely used [37]. | Can stall in problems with narrow feasible regions. |
| Static Penalty | Adds a fixed penalty to objectives for constraint violations. | Simple to implement. | Requires careful tuning of penalty factors [37]. |
| Dynamic Penalty | Increases penalty factors over generations. | More adaptive than static penalty. | Still requires setting initial parameters and a penalty schedule [37]. |
FAQ 5: What are the essential components for implementing the automated repair mechanism? The core components form a logical workflow, as shown in the diagram below.
Experimental Protocols
Protocol 1: Methodology for ANN-Based Variable-Constraint Mapping Discovery
This protocol details the steps to automatically generate the mapping between variables and constraints [37].
- Initial Sampling: Run the optimization algorithm for a initial number of generations (e.g., 50) using a basic CHT like CDP to gather a dataset of design vectors and their corresponding constraint values.
- Network Architecture: For each constraint, create a separate feed-forward ANN. The input layer should have a number of neurons equal to the number of design variables. The output layer has a single neuron predicting the constraint value.
- Training: Train each ANN on the collected dataset. The objective is to minimize the error between the predicted and actual constraint values.
- Sensitivity Analysis: Use a method like connection weight analysis or partial derivatives to assess the importance of each input variable to the network's output for each constraint ANN.
- Thresholding: Apply a threshold to the importance values to create a binary mapping matrix. Variables with importance values above the threshold are deemed significant for that constraint.
Table 2: Research Reagent Solutions for Implementation
| Item Name | Function in the Experiment |
|---|---|
| NSGA-II Algorithm | Provides the multi-objective optimization framework for implementing and testing the repair CHT [37]. |
| Feed-Forward ANN Library (e.g., TensorFlow, PyTorch) | Used to create, train, and perform sensitivity analysis on the networks that discover variable-constraint relationships [37]. |
| Benchmark Problems (e.g., OSY, 10-bar/25-bar truss) | Serve as standardized test cases to validate the efficacy and efficiency of the proposed method against known CHTs [37]. |
Protocol 2: Procedure for the Modified Repair-Based Constraint Handling Technique
This protocol describes how to use the discovered mapping to repair infeasible solutions [37].
- Identification: In each generation, identify infeasible solutions that are valuable (e.g., have good objective function values but violate one or more constraints).
- Constraint-Specific Repair: For each violated constraint in an infeasible solution:
- Consult the mapping matrix to find which variables are linked to that constraint.
- From the current population, find the nearest feasible or minimally-infeasible solution (in objective space) that does not violate this specific constraint.
- Copy the values of the linked variables from this "donor" solution to the infeasible solution.
- Re-evaluation: After repairing all violated constraints (one by one, potentially with different donors), re-evaluate the repaired solution's objective and constraint functions.
- Integration: Insert the feasible repaired solution back into the population for the next generation.
The logical relationship of the repair process is visualized below.
Frequently Asked Questions
Q1: What is adaptive constraint relaxation and why is it used in optimization? Adaptive constraint relaxation is a constraint-handling technique where the algorithm's strictness in enforcing constraints changes dynamically during the search process. This is used because the feasible regions in complex optimization problems, such as molecular design, can be narrow, disconnected, or irregular. By dynamically adjusting how constraints are handled, algorithms can better explore the search space, avoid getting trapped in local optima, and more effectively balance the goals of finding high-performance solutions while satisfying all constraints [3] [5].
Q2: What is the difference between a "static" and a "dynamic" penalty method? In a static penalty method, the coefficient that balances objective function optimization with constraint satisfaction is fixed throughout the entire evolutionary process. In contrast, a dynamic or adaptive penalty method adjusts this coefficient based on the algorithm's progress. For example, one approach uses a high, static coefficient in the early stages to push the population toward feasibility, and then an exponentially decreasing coefficient in later stages to refine solutions and optimize the objective function [38].
Q3: My algorithm is converging to a feasible but sub-optimal region. How can I improve exploration? This is a common challenge when feasible regions are isolated. Advanced methods use multi-stage frameworks to address this. In one stage, the algorithm may temporarily relax pressure to satisfy all constraints, allowing the population to traverse infeasible regions to discover other, more promising feasible areas. Another stage then focuses on driving these promising solutions toward full feasibility and optimality. This strategy helps the population span large infeasible regions to accelerate convergence to a better overall solution [5].
Q4: How can I provide feedback on the performance of this adaptive system? Your primary feedback mechanism is the data from the population itself. You should monitor key metrics such as the proportion of feasible solutions in the population, the average constraint violation, and the quality (fitness) of the best solutions. The trends in these metrics across generations inform the system's adaptive rules. For instance, the transition between optimization stages can be triggered when a sufficient number of feasible solutions is found [38].
Troubleshooting Guides
Problem: The optimization fails to find any feasible solutions.
- Potential Cause 1: Overly strict constraints in the initial population.
- Solution: Implement a two-stage approach. Begin the optimization by temporarily treating the problem as unconstrained or weakly constrained to first find molecules with good properties. Subsequently, introduce the full constraints to steer these high-quality solutions toward feasibility [3].
- Potential Cause 2: The penalty coefficient is too high too early, overly restricting the search.
- Solution: Apply a stage-based adaptive penalty method. In the early phase, use moderate static penalty coefficients to encourage movement toward the feasible region without excessive restriction. As the run progresses and feasible solutions emerge, gradually decrease the penalty coefficient [38].
Problem: The algorithm finds feasible solutions but their objective performance is poor.
- Potential Cause: The algorithm is overly greedy for feasibility, converging to the first feasible region it finds, which may be of low quality.
- Solution: Dynamically coordinate the search between objective and constraint spaces. Incorporate a specific optimization stage that encourages the population to explore more by leveraging promising infeasible solutions, increasing diversity and helping the search escape low-performance feasible areas [5].
Problem: High variability in results between different runs of the algorithm.
- Potential Cause: An ineffective dynamic termination criterion that does not reliably predict convergence.
- Solution: Research suggests that some dynamic termination criteria based on confidence intervals may not reliably predict estimation errors. Instead, using a fixed number of trials or evaluations, potentially determined through prior simulation, can lead to more consistent and predictable performance across runs [39].
Experimental Protocols for Dynamic Threshold Adjustment
The following table outlines the core methodologies from key research papers on adaptive constraint handling.
| Method Name | Core Adaptive Mechanism | Reported Application & Performance |
|---|---|---|
| CMOMO [3] | A two-stage dynamic constraint handling strategy. Initially operates in an unconstrained scenario to optimize properties, then switches to a constrained scenario to find feasible molecules with desired properties. | Application: Constrained molecular multi-property optimization.Performance: Outperformed five state-of-the-art methods on benchmark tasks and demonstrated a two-fold improvement in success rate for a glycogen synthase kinase-3 (GSK3) inhibitor optimization task. |
| MSEFAS [5] | A multi-stage framework with adaptive selection. Employs different stages in the early search: one encourages convergence to feasible regions, and another promotes diversity by spanning infeasible regions. | Application: General constrained multi-objective optimization problems (CMOPs).Performance: Effectively handled a wide range of 56 benchmark CMOPs, showing particular strength on problems with disconnected feasible regions and discrete Pareto fronts. |
| SAPDE [38] | A stage-based adaptive penalty method. Uses static penalty coefficients in the initial stage. Once feasible solutions emerge, it switches to an exponential function to gradually decrease the penalty coefficient over generations. | Application: Constrained evolutionary optimization.Performance: Demonstrated competitive performance on IEEE CEC 2010 benchmark suites and six engineering design problems. |
Research Reagent Solutions
The table below lists key computational tools and components used in implementing adaptive constraint relaxation algorithms.
| Item / Concept | Function in the Experimental Setup |
|---|---|
| Pre-trained Molecular Encoder/Decoder [3] | Maps discrete molecular structures (e.g., SMILES strings) to and from a continuous latent vector space, enabling efficient evolutionary operations. |
| Constraint Violation (CV) Aggregation [3] [5] | A single metric that quantifies the total degree to which a solution violates all constraints, used to guide the search and classify solutions as feasible/infeasible. |
| Differential Evolution (DE) [38] | A population-based search algorithm often used as the core engine to generate new candidate solutions (offspring) within the evolutionary optimization framework. |
| Feasibility Rules [38] | A simple constraint-handling technique that prioritizes solutions based first on their feasibility and then on their objective function value. Often used as a baseline or component in hybrid methods. |
| Latent Vector Fragmentation (VFER) [3] | An evolutionary reproduction strategy designed to effectively generate promising new molecules (offspring) within the continuous latent space. |
Workflow of an Adaptive Constraint Relaxation System
The following diagram illustrates the logical flow and decision points of a multi-stage adaptive system.
Troubleshooting Common Experimental Challenges
FAQ: My algorithm converges prematurely to a local feasible region and cannot explore further. What strategies can help?
- Problem Analysis: This occurs when the algorithm's selection pressure toward feasibility is too high, causing the population to become trapped in the first feasible region it encounters, potentially missing the global optimum [40] [5].
- Recommended Solution: Implement a dual-population approach with differentiated roles.
- Main Population: Uses a strict constraint-handling technique like the Constrained Dominance Principle (CDP) to focus on converging within feasible regions [41] [42].
- Auxiliary/Driving Population: Evolves without considering constraints, focusing purely on objective optimization. This allows it to explore the entire search space, including infeasible regions, and carry beneficial information back to the main population [41] [42].
- Collaboration Mechanism: Allow periodic information exchange between the populations. The auxiliary population can provide diverse genetic material to the main population, helping it escape local optima [40] [43].
FAQ: The diversity of my solutions is poor, even when using a dual-population approach. How can I improve it?
- Problem Analysis: Poor diversity often results from an over-emphasis on convergence speed at the expense of maintaining a spread of solutions across the Pareto front, especially in complex feasible regions [40] [43].
- Recommended Solution:
- For the Objective-Optimizing Population: Integrate a Shift-based Density Estimation (SDE) mechanism. SDE selects solutions not only based on convergence but also on their contribution to diversity, effectively preserving individuals that expand the spread of the population [41].
- For the Constraint-Handling Population: Employ a Niche-based Truncation strategy. This strategy first removes solutions that contribute least to convergence, then uses a distance-based subset selection to balance diversity between the decision and objective spaces [43].
- Dynamic Resource Allocation: If the Unconstrained Pareto Front (UPF) and Constrained Pareto Front (CPF) are disconnected, reduce the size of the auxiliary population in later evolutionary stages. This reallocates computational resources to the main population for better refinement of the true CPF, improving diversity where it matters most [42].
FAQ: How should I handle problems where the feasible regions are disconnected or very narrow?
- Problem Analysis: These problems create significant barriers for traditional algorithms, as populations struggle to cross large infeasible regions to discover all discrete feasible patches [40] [5].
- Recommended Solution: Adopt a multi-stage strategy or a coevolutionary framework with adaptive collaboration.
- Multi-Stage Strategy: In the early phase, use one stage to encourage promising infeasible solutions to approach the feasible region, and another stage to allow the population to span large infeasible regions to accelerate convergence. An adaptive selector can choose the order of these stages based on their effectiveness [5].
- Adaptive Co-evolution: Design an algorithm that first learns the relationship between the UPF and CPF. Based on this learned alignment, it can then dynamically switch the auxiliary population's strategy between positive co-evolution (directly assisting the main population) and inverse co-evolution (exploring more broadly) to better maintain diversity [40].
- Gradient-Based Repair: For problems where gradient information is available, an adaptive gradient-based repair method can be incorporated. This technique uses gradient information from both constraints and the objective function to efficiently pull promising infeasible solutions into the nearest feasible region without overly compromising objective quality [44].
FAQ: My algorithm performs well on one type of CMOP but fails on others. How can I design a more robust solver?
- Problem Analysis: Different CMOPs have different characteristics, such as the degree of overlap between the UPF and CPF. An algorithm tuned for one type may not generalize well [40] [5].
- Recommended Solution: Implement a framework that can automatically adapt its search strategy.
- Relationship Learning: Incorporate an initial learning phase where the algorithm analyzes the problem's characteristics, specifically the topological relationship between the UPF and CPF [40].
- Adaptive Strategy Switching: Based on the learned information, the algorithm can then activate the most suitable collaboration strategy for the evolving phase. For instance, if the UPF and CPF are well-aligned, a stronger collaboration can be used. If they are separated, the populations might work more independently to preserve diversity [40].
- Meta-Optimization with LLMs: For the highest level of automation, explore using Large Language Models (LLMs) as meta-optimizers. An LLM can be trained on diverse COPs to automatically generate and refine update rules for a constrained evolutionary algorithm, creating a highly adaptive and generalizable solver without the need for manual intervention [10].
The table below summarizes recommended algorithm configurations for different types of constrained multi-objective optimization problems (CMOPs).
| Problem Type | Recommended Algorithm Structure | Key Coordination Mechanism | Primary Advantage |
|---|---|---|---|
| CMOPs with complex but connected feasible regions | Dual-Population with static roles [41] [42] | Periodic information exchange during reproduction [41] | Balances objective optimization and constraint satisfaction effectively |
| CMOPs with disconnected or narrow feasible regions | Multi-Stage or Adaptive Dual-Population [40] [5] | Dynamic switching between co-evolution strategies based on UPF-CPF relationship [40] | Enhances ability to cross infeasible regions and find discrete feasible patches |
| Multimodal MOPs (Multiple PSs map to one PF) | Dual-Population with weak interaction [43] | Auxiliary population explores PS locations; main population balances convergence/diversity [43] | Prevents loss of equivalent Pareto optimal solutions in the decision space |
| Problems with unknown characteristics / seeking generalizability | Meta-Black-Box Optimization using LLMs [10] | LLM generates update rules based on problem description and historical performance [10] | Requires no human intervention; adapts to diverse and novel problem domains |
Experimental Protocols for Key methodologies
Protocol 1: Implementing the AACMO Algorithm
This protocol details the steps for implementing the AACMO algorithm, which uses a learning phase to adapt its co-evolutionary strategy [40].
- Initialization: Initialize two populations: the Main Population (MP) and the Auxiliary Population (AuxPop).
- Learning Phase:
- Allow both populations to evolve for a predefined number of generations.
- The MP uses a combination of Genetic Algorithm (GA) and Differential Evolution (DE) operators to quickly approximate the Constrained Pareto Front (CPF).
- The AuxPop focuses on learning the structure of the Unconstrained Pareto Front (UPF).
- At the end of this phase, analyze the degree of alignment between the learned UPF and CPF.
- Evolving Phase:
- Based on the UPF-CPF relationship, select a co-evolution strategy for the AuxPop:
- Positive Co-evolution: Used when UPF and CPF are well-aligned. The AuxPop directly assists the MP in refining the CPF.
- Inverse Co-evolution: Used when UPF and CPF are disconnected. The AuxPop explores areas that the MP cannot easily access, focusing on maintaining overall diversity.
- Based on the UPF-CPF relationship, select a co-evolution strategy for the AuxPop:
- Environmental Selection & Termination: Select survivors for both populations based on their respective goals (feasibility and convergence for MP; diversity and objective quality for AuxPop). Continue evolution until a termination criterion (e.g., max function evaluations) is met.
Protocol 2: Dynamic Resource Allocation in DPVAPS
This protocol is for algorithms where the auxiliary population's computational budget is dynamically adjusted [42].
- Framework Setup: Establish a dual-population framework: Population A (main) handles the original CMOP, while Population B (auxiliary) ignores constraints.
- External Archive Setup: Initialize an empty external archive.
- Evolution with Monitoring:
- Evolve both populations. Any feasible solutions found by Population B are stored in the external archive.
- Monitor the overlap between the UPF (from Population B and the archive) and the CPF (from Population A).
- Dynamic Size Adjustment:
- If the UPF and CPF are found to be largely disconnected, gradually reduce the size of Population B over successive generations.
- Reallocate the saved computational resources to Population A.
- Information Transfer: The external archive periodically injects its stored feasible solutions into Population A to enhance its diversity.
The Scientist's Toolkit: Essential Reagents & Solutions
The table below lists key components used in advanced constrained evolutionary algorithms, analogous to research reagents in a lab.
| Tool/Component | Function in the Algorithmic "Experiment" |
|---|---|
| Dual-Population Framework | The core architecture that separates the tasks of objective optimization and constraint handling, allowing for a more balanced search [40] [41] [42]. |
| Constrained Dominance Principle (CDP) | A fundamental rule used in the main population to compare solutions, giving strict priority to feasibility and ensuring convergence to the constrained Pareto front [41] [42]. |
| Shift-based Density Estimation (SDE) | A diversity preservation metric used in the objective-optimizing population. It helps maintain a spread of solutions across the Pareto front by selecting individuals that improve both convergence and diversity [41]. |
| ε-Constraint Method | A technique that relaxes the feasibility requirement by allowing slightly infeasible solutions with good objective values to survive, helping the population cross infeasible regions [44]. |
| Gradient-Based Repair | An operator that acts as a "local search" tool, using gradient information to quickly pull promising infeasible solutions into the feasible region, improving convergence speed [44]. |
| Meta-Black-Box Optimizer (LLM) | An automated, adaptive "strategist" that can analyze problem characteristics and generate effective update rules, reducing the need for manual algorithm design and tuning [10]. |
Workflow for Adaptive Dual-Population Coevolution
The diagram below illustrates the logical workflow of an adaptive dual-population algorithm that incorporates a learning phase.
Technical Support Center
Frequently Asked Questions (FAQs)
Q1: My LLM-generated update rules lead to premature convergence. How can I improve population diversity? The framework's RTO²H prompt design includes a 'History Feedback' component that archives the performance of previously generated rules. To mitigate premature convergence, explicitly prompt the LLM to analyze rules that maintained high diversity (e.g., those that used multiple mutation strategies or archive information) and incorporate their principles. Furthermore, ensure your prompt's 'Task Description' provides comprehensive information on the current population's diversity metrics to guide the LLM effectively [45] [10].
Q2: What is the best way to structure a prompt for generating feasible solutions in problems with very small feasible regions? The prompt should heavily emphasize constraint information within the 'Task Description' section. Structure it to include:
- Detailed constraint violation data (
G(x)) for the current population. - The proportion of feasible solutions (feasibility ratio).
- Information about the best feasible and best infeasible solutions. The 'Operating Requirement' should explicitly instruct the LLM to prioritize update rules that reduce constraint violation while cautiously improving the objective, perhaps by leveraging techniques inspired by the best infeasible solution concept [19] [46].
Q3: How can I validate that the LLM-generated algorithm is generalizing well and not overfitting to my training problems? The recommended protocol is to perform extensive testing on a diverse set of benchmark problems (like CEC2010 or CEC2017) with varying characteristics. Conduct a minimum of 31 independent runs for statistical significance. Compare the performance (solution accuracy, feasibility rate, computational efficiency) of your LLM-designed algorithm against established state-of-the-art methods like IMODE or SHADE across all these problems to assess generalizability [45] [19] [10].
Q4: The computational cost of meta-training the LLM-based meta-optimizer is high. Are there ways to improve efficiency? Yes, efficiency can be improved by:
- Smart Sampling: Carefully select a diverse but smaller subset of training problems (COPs) that represent different challenge types (separable/non-separable, linear/non-linear constraints).
- Parallel Evaluation: The framework is designed to evaluate populations in parallel. Ensure your implementation leverages this by using batch processing for the LLM and parallel function evaluations [10].
- Iteration Limits: During the meta-training phase, you can limit the number of function evaluations (MaxFE) used to assess each candidate update rule on a training problem to get a faster, though less precise, performance estimate [10].
Troubleshooting Guides
Problem: Generated update rules consistently violate constraints. Diagnosis: The LLM is not sufficiently prioritizing constraint satisfaction information. Solution:
- Audit Your Prompt: Verify that the 'Role Definition' clearly states the goal is to solve a Constrained Optimization Problem (COP). The 'Task Description' must provide detailed, quantitative data on constraint violations for the initial population [10].
- Incorporate Advanced CHTs: Guide the LLM by including examples or principles from successful constraint handling techniques (CHTs) in the 'History Feedback'. This could include concepts from:
- Adaptive Ranking (AR-DE): Which uses information from the best infeasible solution to guide the search [46].
- Ensemble CHT (ECHT): Which probabilistically combines multiple CHTs like feasibility rules, penalty functions, and stochastic ranking [47].
- Classification-Collaboration: Which decomposes the problem by classifying constraints into groups [19].
Problem: The LLM outputs update rules in an incorrect or non-executable format. Diagnosis: The 'Output Format' section of the prompt is likely ambiguous or not strictly enforced. Solution:
- Specify a Strict Template: In the 'Output Format' section, provide a clear, unambiguous template for the LLM to follow. Use placeholders and specify the exact syntax required for the update rule (e.g.,
Rule: [Rule Name]; Mutation: [Strategy]; Crossover: [Type]; Selection: [Method]). - Post-Processing Check: Implement a script that parses the LLM's output to check for conformity with the required format before the rule is sent for evaluation. Non-conforming outputs can be fed back to the LLM with a request for correction [10].
Problem: Algorithm performance is highly sensitive to the initial population provided in the prompt. Diagnosis: The LLM is overfitting to the specific state of the initial population. Solution:
- Provide Multiple Contexts: During meta-training, provide the LLM with historical data from multiple runs and different initial populations for the same problem. This helps it learn robust update rules that are effective across various population states [10].
- Feature Generalization: Instead of raw solution vectors, consider providing the LLM with generalized features of the population, such as measures of diversity, average constraint violation, and fitness distribution, to encourage the generation of more universally applicable rules [45].
Experimental Protocols & Data
Core Experimental Protocol for Evaluating LLM-Generated Algorithms
This protocol is based on the methodology used to validate frameworks like AwesomeDE and llmEA [45] [10].
- Benchmark Problems: Use standard benchmark suites for Constrained Optimization Problems (COPs), such as CEC2010 or CEC2017. These suites provide scalable problems with diverse characteristics (separable/non-separable, with inequality/equality constraints).
- Algorithm Comparisons: Compare your LLM-generated algorithm against a set of state-of-the-art algorithms. Common choices include:
- Classical Differential Evolution (DE)
- Manually-improved algorithms (e.g., IMODE, SHADE)
- Other constraint-handling EAs (e.g., AR-DE, ECHT-based algorithms)
- Parameter Settings:
- Search Dimension (D): 10 and 30.
- Max Function Evaluations (MaxFE): 200,000 for D=10; 600,000 for D=30.
- Independent Runs: 31 per problem to ensure statistical significance.
- Population Size: Typically follows the standard of the base algorithm (e.g., DE).
- Performance Metrics: Record the best, median, and worst objective values found, along with the feasibility rate of the final population. Algorithm complexity can be measured using normalized computation times.
Meta-Training Protocol for the LLM-Based Meta-Optimizer
This describes the inner workings of the Meta-Black-Box Optimization (MetaBBO) framework [10].
- Objective: To train the LLM to act as a meta-optimizer that generates effective update rules for CEAs.
- Process: The process involves a bi-level optimization loop, illustrated in the workflow diagram below.
- Outer Loop (Meta-Optimization):
- Archive: Maintain a history of generated update rules and their performance on training COPs.
- Generation: The LLM generates new candidate update rules conditioned on the archived history.
- Feedback: Performance metrics from the inner loop are used to update the history.
- Inner Loop (Algorithm Execution):
- Rule Deployment: The candidate update rule is deployed to form a CEA.
- Problem Solving: The CEA is run on a set of sampled training COPs.
- Evaluation: The performance of the CEA is measured and fed back to the outer loop.
Prompt Design Protocol (RTO²H Framework)
A standardized protocol for constructing prompts is crucial for success [10].
- Role Definition: Define the LLM's role (e.g., "You are a meta-optimizer designed to create update rules for constrained evolutionary algorithms").
- Task Description: Provide detailed information about the COP, including:
- Decision variable bounds.
- Objective function values of the current population.
- Constraint violation data (
G(x)) for all individuals.
- Operating Requirement: Specify the steps the LLM should take and any requirements for the update rules (e.g., "Generate a rule that balances objective improvement with constraint satisfaction").
- History Feedback: Supply records of previously generated rules and their performance on the target problem.
- Output Format: Define a strict, machine-parsable format for the LLM's output to ensure consistency.
Table 1: Key Performance Metrics from Comparative Studies
This table synthesizes common performance metrics and outcomes reported in constrained optimization literature, illustrating what to look for when evaluating your own LLM-generated algorithms [45] [19] [47].
| Algorithm / Method | Key Feature | Reported Performance (Typical Context) | Feasibility Rate (FR) | Success Rate (SR) |
|---|---|---|---|---|
| AwesomeDE / llmEA | LLM-generated update rules via MetaBBO | Outperforms existing methods in computational efficiency and solution accuracy on CEC2010 [45] [10]. | High | High |
| EALSPM | Classification-collaboration constraint handling | Demonstrates competitive performance on CEC2010 & CEC2017 benchmarks [19]. | High | High |
| JADE-ECHT | ECHT integrated into self-adaptive JADE | Better SR but lower FR compared to SaDE-ECHT on CEC'06 test problems [47]. | Lower | Higher |
| SaDE-ECHT | ECHT integrated into self-adaptive SaDE | Better FR but lower SR compared to JADE-ECHT on CEC'06 test problems [47]. | Higher | Lower |
| AR-DE | Adaptive ranking using best infeasible solution | Shows better overall results on engineering design problems compared to other CHTs [46]. | High | High |
Table 2: Essential Research Reagent Solutions
This table details key computational "reagents" required to implement and experiment with LLM-assisted algorithm generation [45] [19] [10].
| Item Name | Function / Role in the Experiment | Specifications / Examples |
|---|---|---|
| Benchmark Problem Suites | Provides standardized testbeds for evaluating algorithm performance. | CEC2010, CEC2017 constrained optimization benchmarks. |
| Base Evolutionary Algorithm | Serves as the foundational algorithm whose update rules are to be automated. | Differential Evolution (DE) with its population-based structure. |
| Constraint Handling Techniques (CHTs) | Provides methods for handling constraints; can be integrated or used as inspiration for LLM prompts. | Superiority of Feasible Solutions, ε-Constraint, Stochastic Ranking, Self-Adaptive Penalty (often used in ensembles). |
| Large Language Model (LLM) | Acts as the meta-optimizer to generate and evolve algorithmic update rules. | Models like Deepseek R1, used to produce update rules based on prompts [10]. |
| Performance Evaluation Framework | A standardized procedure to run, compare, and statistically validate algorithm performance. | Protocol including 31 independent runs, statistical tests (e.g., Wilcoxon), and metrics like feasibility rate. |
Workflow and System Diagrams
MetaBBO Training Workflow
RTO²H Prompt Structure
Constraint Handling Taxonomy
Overcoming Practical Challenges: Optimization Strategies for Complex COPs
This technical support center provides troubleshooting guides and FAQs for researchers facing challenges with disconnected feasible regions in Constrained Optimization Problems (COPs). The content is framed within a broader thesis on adaptive constraint handling techniques.
Frequently Asked Questions
Q1: Why does my optimization algorithm fail to find all feasible regions in my problem? Your algorithm may be overly prioritizing feasibility or convergence in a single region. Techniques like multi-population strategies [48] [49] or adaptive constraint handling that temporarily preserves useful infeasible solutions [50] can help explore the search space more broadly before converging to all feasible patches.
Q2: How can I improve performance when problem constraints create complex, irregular feasible regions? Consider decomposing complex constraints. A coevolutionary framework that breaks the problem into simpler, single-constraint subproblems can effectively decouple complex interactions and help the algorithm discover all feasible areas [48]. For very high-dimensional problems (large-scale CMOPs), variable grouping strategies that separate convergence-related and diversity-related variables are crucial [49].
Q3: What is the most efficient way to utilize limited evaluation budgets on expensive problems with disconnected feasibility? For expensive CMOPs, surrogate-assisted evolution is key [51]. These methods build approximate models of the objective and constraint functions to pre-select promising candidates. To handle disconnections, ensure your surrogate model and infill sampling criterion account for model uncertainty to guide exploration across infeasible barriers [51].
Q4: How do I balance feasibility, convergence, and diversity when feasible regions are discrete? Employ multi-stage algorithms and collaborative populations [52] [49]. A common effective strategy uses an initial stage to quickly approach the unconstrained Pareto front (UPF), ignoring constraints. A second stage then uses a main and auxiliary population to collaboratively guide solutions from the UPF to the various segments of the constrained Pareto front (CPF) while maintaining diversity [49].
Comparison of Core Techniques for Disconnected Feasible Regions
The table below summarizes the primary algorithmic strategies discussed in recent literature for handling disconnected feasible regions.
| Technique Category | Key Mechanism | Best Suited For | Key Considerations |
|---|---|---|---|
| Coevolutionary Frameworks [48] [52] | Decomposes CMOP into simpler subproblems (e.g., by constraint) using multiple collaborating populations. | Complex problems with multiple interacting constraints and very small or irregular feasible regions. | Increases computational complexity; requires careful design of information sharing between populations. |
| Two-Stage Search [49] | Separates search into distinct phases: first ignores constraints to find UPF, then focuses on satisfying constraints and diversifying. | Problems where the UPF and CPF are significantly different or separated by large infeasible regions. | Performance depends on a well-designed trigger for switching from the first to the second stage. |
| Surrogate-Assisted Evolution [51] | Uses approximation models (e.g., Kriging) to reduce expensive function evaluations; leverages model uncertainty to explore. | Computationally expensive problems (ECMOPs) where each evaluation is time-consuming or resource-intensive. | Model accuracy is critical; performance can degrade if the surrogate cannot capture the true landscape complexity. |
| Adaptive CHT Selection [50] | Uses machine learning (e.g., Deep Reinforcement Learning) to dynamically select the best constraint-handling technique during the optimization process. | Problems where no single CHT performs well throughout the entire search or for a diverse set of benchmark problems. | Requires designing a state representation and reward function; initial training phase adds overhead. |
Experimental Protocols for Key Methods
Protocol for Coevolutionary Framework with Constraint Decomposition (CCMOEA)
This protocol is based on the CCMOEA algorithm designed to solve CMOPs with complex constraints [48].
- Objective: To obtain a well-converged and diverse set of feasible solutions for a CMOP with disconnected or irregular Pareto fronts.
- Algorithm Structure:
- Main Population: Focuses on solving the original CMOP.
- Auxiliary Subpopulations:
qsubpopulations (whereqis the number of constraints) each optimize a simplified single-constraint MOP.
- Experimental Procedure:
- Initialization: Randomly initialize the main population and all
qauxiliary subpopulations. - Two-Stage Evolution:
- Stage 1 (Evolution): All populations evolve simultaneously. The main population periodically collects non-dominated and feasible solutions from the auxiliary populations to enrich its search.
- Stage 2 (Improvement): The main population continues evolving, focusing on refining the solutions collected in Stage 1.
- State Detection: An evolutionary state detection strategy monitors the convergence of each auxiliary subpopulation. If a subpopulation stops improving, its evolution is halted to conserve computational resources.
- Termination: The algorithm runs for a fixed number of generations or until another termination criterion (e.g., stability of the main population) is met.
- Initialization: Randomly initialize the main population and all
- Key Parameters: Population sizes for main and auxiliary populations, number of constraints
q, communication frequency between populations, and state detection threshold.
Protocol for Adaptive CHT Selection via Deep Reinforcement Learning (CMOEA-DRL)
This protocol outlines the method for dynamically selecting CHTs and operators during the evolutionary process [50].
- Objective: To dynamically select the most appropriate constraint-handling technique and search operator at different stages of evolution to improve overall performance.
- Algorithm Components:
- Actions: A portfolio of CHTs (e.g., penalty functions, superiority of feasible solutions, ε-constraint) and search operators (e.g., Genetic Algorithm (GA), Differential Evolution (DE)).
- State Representation: A vector capturing the current population's state, including information on objective values and constraint violations.
- Reward Calculation: A metric quantifying the improvement in population quality (e.g., reduction in constraint violation, improvement in objective values) after applying an action.
- Experimental Procedure:
- Two-Stage Training:
- Stage 1 (Random Exploration): The DQN initially selects CHTs and operators randomly for several episodes to collect a diverse set of state-action-reward samples, which are stored in a replay buffer.
- Stage 2 (Network Training): The DQN is trained using the samples from the replay buffer to learn a Q-value function that predicts the long-term reward of taking a given action in a specific state.
- Execution:
- The current state of the population
s_tis fed into the trained DQN. - The DQN outputs Q-values for all possible actions (CHT + operator pairs).
- The action with the highest Q-value is selected and applied to generate the next population.
- The reward
r_tfor this action is calculated and the new population states_{t+1}is observed.
- The current state of the population
- This cycle repeats until a termination criterion is met.
- Two-Stage Training:
- Key Parameters: DQN architecture (layers, neurons), learning rate, discount factor, exploration rate (ε-greedy), and reward function weights.
The Scientist's Toolkit: Research Reagent Solutions
The table below lists key algorithmic components essential for implementing the advanced techniques discussed.
| Research Reagent (Algorithmic Component) | Function in the Experiment |
|---|---|
| Kriging (Gaussian Process) Surrogate Model [51] | Provides both an approximate value and an uncertainty measure for expensive objective/constraint functions, enabling informed candidate selection. |
| Constraint Decomposition [48] | Breaks down a complex CMOP into simpler subproblems with single constraints, making it easier to find feasible regions. |
| Deep Q-Network (DQN) [50] | A deep reinforcement learning model that learns to map the state of an evolving population to the most beneficial constraint-handling technique and operator. |
| Main-Auxiliary Population Structure [52] [49] | Uses multiple populations that cooperate or compete to maintain diversity, explore different regions, and handle constraints effectively. |
| ε-Constraint Handling Technique [48] [50] | Allows mildly infeasible solutions to be considered feasible, helping algorithms cross large infeasible regions by relaxing the feasibility threshold. |
Workflow Diagram for Navigating Disconnected Feasible Regions
The diagram below visualizes a high-level, integrated workflow combining several advanced techniques to tackle disconnected feasible regions.
Troubleshooting Guides
Frequently Asked Questions
1. How can I diagnose and resolve an infeasible optimization model? An infeasible model, where no solution satisfies all constraints, is a common challenge. The resolution process involves systematic diagnosis and strategic relaxation of constraints [53].
- Verification Steps: Begin by verifying input data accuracy and model correctness, checking for coding errors in variable types, indexing, bounds, and constraint definitions [53].
- IIS Analysis: Use solvers like Gurobi, XPRESS, or CPLEX to compute an Irreducible Inconsistent Subsystem (IIS). An IIS is a minimal set of constraints and variable bounds that is inherently infeasible; removing any single member makes the subsystem feasible. Analyzing the IIS pinpoints core conflicts [53] [54].
- Constraint Relaxation: Introduce slack variables to hard constraints and penalize their violations in the objective function, effectively transforming them into soft constraints. This not only manages infeasibility but can also reflect real-world economic trade-offs, such as the cost of hiring temporary workers or renting extra space [53].
2. My algorithm converges to a local optimum. How can I escape it? Convergence to local optima is a fundamental limitation of many algorithms. Escaping requires techniques that allow the search process to accept non-improving moves under controlled conditions [55].
- FeReRA Multi-Agent Strategy: In multi-agent systems, an agent's local best performance does not always contribute to the system's global best. The FeReRA approach forces agents to choose sub-optimal moves after reaching a penalty threshold, allowing other agents to find better moves and improve the overall solution [56].
- Diversity Maintenance: In constrained multiobjective optimization, retaining and leveraging a diverse set of infeasible solutions can help the population explore across separated feasible regions and avoid getting trapped [57] [58].
3. How can I maintain solution diversity in constrained multiobjective optimization? When constraints fragment the feasible region into disconnected patches, maintaining diversity is critical for finding a well-distributed set of Pareto-optimal solutions [58].
- Staged Diversity Enhancement Method (SDEM): This method divides the evolutionary process into three distinct stages [58]:
- Early Stage: Uses a niching-based constraint dominance principle to guide the population toward optimal feasible regions.
- Middle Stage: Implements a diversity enhancement dominance principle, actively retaining well-distributed offspring to explore potential discrete feasible regions.
- Late Stage: Optimizes all solutions under constraint dominance to finalize convergence, diversity, and feasibility.
- Epsilon Constraint Method with Diversity Maintenance: An advanced epsilon constraint method incorporates a specific strategy for solutions whose constraint violation is greater than epsilon. Instead of discarding them, it maintains their diversity, ensuring a broader exploration of the search space [57].
4. What is the role of infeasible solutions in solving Constrained Optimization Problems (COPs)? Infeasible solutions are not merely failures; they are valuable sources of information. The key challenge is to utilize them effectively without derailing the search for feasibility [19].
- Balanced Search: Relying solely on feasible solutions can lead to premature convergence, especially if the initial feasible region is small or disconnected. Infeasible solutions act as bridges, allowing the algorithm to traverse infeasible "barriers" to discover other, potentially better, feasible regions [58].
- Hybrid and Staged Approaches: Many modern algorithms use multi-population or staged strategies. One population or stage may focus on converging to feasible regions, while another deliberately explores infeasible regions to preserve diversity and improve convergence [19] [58].
Experimental Protocols for Key Techniques
Protocol 1: Implementing the IIS Diagnostic Workflow This protocol helps identify the minimal set of conflicting constraints in an infeasible model [53] [54].
- Objective: To locate an Irreducible Inconsistent Subsystem (IIS) in an infeasible optimization model.
- Procedure:
- Model Submission: After the solver returns a model infeasible status, instruct it to compute an IIS (e.g., use
IIScommand in Gurobi orXPRSiisfirstin FICO Xpress). - IIS Extraction: The solver returns a set of constraints and/or variable bounds that form one IIS.
- Analysis: Examine the constraints/bounds in the IIS. The infeasibility arises from the interaction within this specific set.
- Iteration (Optional): Use functions like
XPRSiisnextto find further independent IISs, as multiple distinct conflicts may exist. - Resolution: For each constraint in the IIS, determine if it can be relaxed, modified, or if the input data driving it is incorrect.
- Model Submission: After the solver returns a model infeasible status, instruct it to compute an IIS (e.g., use
- Interpretation: The IIS provides a highly focused starting point for debugging. Resolving the issues in the IIS(s) is necessary to make the overall model feasible.
Protocol 2: Applying the Staged Diversity Enhancement Method (SDEM) This protocol outlines the steps for implementing the SDEM algorithm to enhance diversity in CMOPs [58].
- Objective: To find a diverse set of Pareto-optimal solutions for CMOPs with discrete or complex feasible regions.
- Procedure:
- Initialization: Initialize a population and an external archive
Afor storing elite feasible solutions. - Stage 1 - Early Convergence:
- Apply a niching-based constraint Pareto dominance principle for selection.
- The goal is to drive the population toward the promising feasible regions.
- Continuously update the external archive
Awith the best feasible solutions found.
- Stage 2 - Mid-Term Diversity Enhancement:
- (Optional) Perform a directed sampling of the population to break convergence and re-inject diversity.
- Switch to a diversity enhancement dominance principle. This principle favors infeasible solutions that are well-distributed in the objective space relative to the feasible solutions in archive
A. - The goal is to explore the search space more broadly and discover separated feasible regions.
- Stage 3 - Late-Stage Balancing:
- Revert to a standard constraint dominance principle to ensure final output is feasible.
- Optimize the population to fine-tune convergence and diversity within the feasible regions located.
- Initialization: Initialize a population and an external archive
- Interpretation: By temporally separating the goals of convergence and diversity, SDEM mitigates the conflict between them, leading to better performance on problems with complex feasible regions.
Comparative Analysis of Constraint Handling Techniques (CHTs)
The table below summarizes various CHTs discussed in the search results, highlighting their core mechanisms and applications [19].
| Technique Category | Core Mechanism | Key Advantage(s) | Representative Algorithms |
|---|---|---|---|
| Penalty Functions | Combines objective and constraint violation into a single function using penalty factors. | Simple to implement; transforms COP into an unconstrained problem. | Unified DE (UDE), Two-stage PDE (TPDE) [19]. |
| Feasibility Preference | Strictly prefers feasible over infeasible; uses rules or stochastic ranking. | Directly pushes population toward feasibility. | NSGA-II, Feasibility Rule (FR), Stochastic Ranking [19]. |
| ε-Constraint Method | Relaxes acceptance threshold for infeasible solutions via a decaying ε parameter. | Balances exploration (using infeasible solutions) and exploitation. | MOEA/D-Epsilon, MOEA/D-IEpsilon [19]. |
| Multi-Objective Methods | Converts constraints into additional objective(s) to optimize. | Leverages powerful multi-objective optimizers; provides a global view of constraints. | C-TAEA, CCMO, DeCODE [19]. |
| Hybrid & Staged Methods | Combines or sequences different CHTs during the evolutionary process. | Adapts search strategy to the current state; balances multiple goals effectively. | PPS, MOEA/D-DAE, CMOEA-MS, SDEM [58]. |
The Scientist's Toolkit
Research Reagent Solutions
This table details key algorithmic components and strategies essential for advanced research in constrained optimization.
| Reagent / Method | Primary Function | Application Context |
|---|---|---|
| IIS (Irreducible Inconsistent Subsystem) | Diagnostic tool to identify the minimal core of conflicting constraints in an infeasible model [53] [54]. | Debugging and refining infeasible mathematical programming models (MIP, LP). |
| Slack Variables | Relaxes hard constraints by measuring violation, which is then penalized in the objective function [53]. | Converting hard constraints to soft ones to ensure model feasibility and model real-world costs of violation. |
| FeReRA (Feedback and Reinforcement) | A multi-agent strategy that penalizes agents for lack of global contribution, forcing sub-optimal moves to escape local optima [56]. | Distributed constraint satisfaction problems where local agent optimization harms global performance. |
| ε-Constraint Method | Controls the acceptance of infeasible solutions by defining a dynamic threshold (ε), promoting exploration [57] [19]. | Constrained single- and multi-objective optimization, especially when the global optimum is near the feasibility boundary. |
| SDEM (Staged Diversity Enhancement Method) | A three-stage algorithm that explicitly separates convergence, diversity, and feasibility goals during evolution [58]. | Solving CMOPs with disconnected feasible regions where maintaining solution diversity is challenging. |
| Hybrid CHTs (Constraint Handling Techniques) | Uses multiple constraint handling methods (e.g., multi-objective + feasibility rules) adaptively or in parallel [19]. | Complex COPs where no single CHT performs well throughout the entire search space. |
Methodologies and Workflows
SDEM Three-Stage Workflow
This diagram illustrates the adaptive, three-stage workflow of the Staged Diversity Enhancement Method (SDEM) for constrained multiobjective optimization.
Infeasibility Diagnosis and Repair Protocol
This flowchart details the systematic troubleshooting protocol for diagnosing and resolving an infeasible optimization model, from initial checks to advanced solver-based diagnostics.
Frequently Asked Questions (FAQs)
FAQ 1: What are the primary strategies for reducing the number of constraint evaluations in evolutionary optimization? A key strategy is the use of a classification-collaboration constraint handling technique. This method randomly classifies all constraints into K groups, effectively decomposing the original problem into K simpler subproblems. A separate subpopulation is then assigned to each subproblem. This reduces the "constraint pressure" on any single part of the algorithm and allows the complementary information from different constraints to be utilized more efficiently. The evolutionary process is further divided into two stages—a random learning stage and a directed learning stage—where these subpopulations interact to generate potentially better solutions without requiring excessive constraint evaluations [19].
FAQ 2: How can I ensure reliability when using surrogate models for constraint evaluation? Simply replacing the true constraint function with a surrogate can lead to convergence issues. To improve reliability, incorporate a trust-region filter (TRF) solution strategy. This framework manages the interaction between the surrogate model and the true function. The surrogate is used to propose new candidate points, but these points are only accepted if they lead to sufficient improvement when evaluated with the true, expensive constraint function. The trust region controls the step size to ensure the surrogate's approximations remain valid. Kriging and Artificial Neural Network (ANN) models have been shown to converge quickly (in as few as two iterations) within this framework, while ALAMO offers a good balance between efficiency and reliability [59].
FAQ 3: Which surrogate models are most effective for constraint handling, and how do they compare? The choice of surrogate model involves a trade-off between accuracy, computational cost, and convergence reliability. The table below summarizes the performance of five common approaches based on a benchmark study [59]:
| Surrogate Model | Computational Efficiency | Convergence Reliability | Key Characteristics |
|---|---|---|---|
| ALAMO | High | Balanced | Most computationally efficient in "one-shot" optimization [59]. |
| Kriging | Low (High CPU time) | High with TRF | Achieved fastest convergence (two iterations) with a trust-region filter [59]. |
| ANN | Medium | High with TRF | Also converged in two iterations within a trust-region framework [59]. |
| RBF | Medium | Medium | High accuracy on training data but may require more iterations [59]. |
| Polynomials | Medium | Medium | A traditional approach, performance can vary significantly with problem structure [59]. |
FAQ 4: My optimization is stuck in an infeasible region. What adaptive techniques can help? The state of the population (e.g., infeasible, semi-feasible, or feasible) should dictate the constraint handling technique. One adaptive approach involves situation-dependent techniques. The algorithm first identifies whether the population is largely infeasible, near the feasible region boundary, or mostly feasible. Different strategies are then activated for each situation. For example, in the early stages when the population is infeasible, the focus can be shifted towards minimizing overall constraint violation. As feasible individuals are found, the strategy can adapt to balance objective improvement and feasibility maintenance [19]. Another method is a two-stage algorithm; the first stage uses a multi-objective approach to push the population toward feasibility, and the second stage uses a differential evolution operator to speed up convergence within the feasible region [19].
FAQ 5: How are these methods applied in real-world domains like drug development? In computational drug repurposing and development, these optimization methods are crucial for navigating complex biological constraints. For instance, in Alzheimer's disease research, computational methods are used for target identification, virtual screening, and multi-target directed ligand design. The optimization challenges involve constraints derived from molecular docking scores, toxicity predictions, and ADMET (Absorption, Distribution, Metabolism, Excretion, and Toxicity) properties, which are often computationally expensive to evaluate. Using surrogate models to approximate these costly predictions allows researchers to efficiently search vast chemical spaces and identify promising drug candidates for further experimental validation [60] [61].
Troubleshooting Guides
Problem: The optimization algorithm fails to find feasible solutions. Solution: Apply a multi-stage approach or a classification-collaboration technique.
- Recommended Protocol: Implement a two-stage evolutionary algorithm [19].
- Stage 1 - Feasibility Search: Use an enhanced dynamic multi-objective evolutionary algorithm (DCMOEA) focused on minimizing constraint violations. The goal is to steer the population toward the feasible region.
- Stage 2 - Objective Optimization: Once a sufficient number of feasible solutions is found, switch to a differential evolution (DE) operator to minimize the objective function and converge to an optimal solution.
- Alternative Method: Use the classification-collaboration constraint handling technique [19]. Decompose the problem into subproblems, each handling a subset of constraints, to reduce the burden of satisfying all constraints at once during the initial search.
Problem: Surrogate models for constraints are inaccurate, leading to poor optimization results. Solution: Implement a trust-region filter (TRF) framework and select an appropriate surrogate model [59].
- Recommended Protocol:
- Initial Sampling: Design an initial set of experiments (e.g., Latin Hypercube Sampling) to evaluate the true, expensive constraints and build an initial surrogate model.
- Iteration Cycle:
- Proposal: Within a defined trust region, solve an auxiliary optimization problem using the current surrogate models to propose a new candidate point.
- Evaluation: Evaluate the proposed candidate using the true constraint functions.
- Update: Update the surrogate models with the new data.
- Adjustment: If the candidate point leads to sufficient improvement, accept it and potentially expand the trust region. If not, reject it and reduce the trust region.
- Visualization: The following workflow diagram illustrates the trust-region surrogate model process.
Problem: The algorithm converges slowly due to high computational cost of evaluating all constraints. Solution: Use a hybrid or adaptive constraint handling technique that dynamically adjusts its focus [19].
- Recommended Protocol: Design an algorithm that switches strategies based on population information.
- Diagnose Population State: Periodically calculate the proportion of feasible solutions in the population.
- Select Strategy:
- If feasibility ratio is very low: Prioritize minimizing the sum of constraint violations (cv) for all individuals.
- If feasibility ratio is medium: Use an ɛ-constraint method, which allows a controlled degree of constraint violation to enable a more effective search across infeasible regions.
- If feasibility ratio is high: Switch to a feasibility rule that favors feasible solutions and focuses on optimizing the objective function.
The Scientist's Toolkit: Key Research Reagent Solutions
The following table details essential computational tools and methodologies for implementing surrogate-assisted constrained optimization in research.
| Research Reagent | Function/Brief Explanation |
|---|---|
| Classification-Collaboration Technique [19] | A constraint handling method that decomposes a problem by grouping constraints, reducing evaluation pressure. |
| Trust-Region Filter (TRF) [59] | A solution strategy that manages surrogate model inaccuracy to ensure reliable convergence. |
| ALAMO [59] | (Automated Learning of Algebraic Models for Optimization) A surrogate modeling tool known for high computational efficiency. |
| Kriging / Gaussian Process [59] | A surrogate model type that provides uncertainty estimates, excellent within a TRF framework. |
| Radial Basis Functions (RBFs) [59] [62] | A type of surrogate model often used in derivative-free optimization algorithms. |
| Bayesian Optimization (BO) [62] | A model-based optimization framework that uses probabilistic surrogates to balance exploration and exploitation. |
| Two-Stage Evolutionary Algorithm [19] | A hybrid method that first drives for feasibility before refining solutions in the feasible region. |
| ɛ-Constraint Method [19] | An adaptive technique that relaxes feasibility requirements early in the search to navigate complex landscapes. |
In the domain of Constrained Optimization Problems (COPs), the balance between exploration (searching new regions for potential solutions) and exploitation (refining known good solutions) is a fundamental determinant of algorithmic performance [63]. Effective management of this balance becomes particularly critical when complex constraints render large portions of the search space infeasible. Adaptive constraint handling techniques have emerged as powerful strategies to dynamically guide this process, using information gathered during the search to adjust the algorithm's focus between finding feasible regions and optimizing the objective function [19] [5].
The core challenge in constrained evolutionary optimization is the inherent conflict between satisfying all constraints and optimizing the primary objective function [44]. This article establishes a technical support framework, providing troubleshooting guidance and methodological protocols for researchers implementing these advanced techniques in scientific and drug discovery applications where computational models must adhere to strict biological, chemical, or physical constraints.
Frequently Asked Questions (FAQs) & Troubleshooting
Q1: My evolutionary algorithm converges prematurely to a suboptimal feasible solution. How can I encourage greater exploration without sacrificing convergence speed?
A: Premature convergence often indicates an over-emphasis on exploitation. Implement a multi-stage approach that temporally separates exploration and exploitation [5]. In early stages, consciously permit searches through infeasible regions that provide valuable information about the objective landscape. The Adaptive Multi-Stage Evolutionary Framework with Adaptive Selection (MSEFAS) demonstrates this by maintaining two parallel optimization processes in its early phase: one encouraging promising infeasible solutions to approach feasible regions while increasing diversity, and another enabling the population to span large infeasible regions to accelerate convergence [5]. Additionally, consider incorporating directed exploration strategies that explicitly bias the search toward uncertain regions using information bonuses added to the value function [64].
Q2: How can I handle problems where the feasible region is extremely small or disconnected?
A: Problems with narrow or disconnected feasible regions require specialized constraint handling. The ε-constrained method gradually relaxes constraints during early generations, allowing productive movement through infeasible space [44]. This approach enables information sharing between feasible and infeasible regions, creating stepping stones to isolated feasible basins. The classification-collaboration constraint handling technique also shows promise by decomposing constraints into subgroups, reducing overall constraint pressure [19]. For severely constrained problems, consider gradient-based repair methods that actively move infeasible solutions toward feasible regions using local gradient information, though these require differentiable constraints [44].
Q3: What metrics can I use to quantitatively evaluate the exploration-exploitation balance during optimization?
A: While standard performance metrics measure final solution quality, monitoring exploration-exploitation balance requires specialized assessments. Track these metrics:
- Population Diversity: Measure the spread of solutions throughout the search space using mean Euclidean distance or entropy-based metrics [63].
- Feasibility Ratio: Monitor the percentage of feasible solutions in the population over generations [5].
- Archived Solution Quality: Assess the improvement rate of elite solutions in adaptive archives [19].
Many advanced algorithms now incorporate automatic balance assessment. For instance, the Scale-Adaptive Balancing approach handles distributions with different scales by considering reward variance, leading to more accurate balance evaluation [65].
Q4: How do I choose between penalty functions, multi-objective approaches, and feasibility rules for my specific problem?
A: Each technique has distinct strengths. Implement an ensemble approach that combines multiple constraint handling techniques with a voting mechanism [66]. The Framework of Ensemble Parameter Adapted Evolutionary Algorithm (FEPEA) successfully employs this strategy, dynamically selecting the most appropriate technique based on problem characteristics [66]. For problems where constraint violations can be categorized by severity, use hybrid techniques that handle different constraint types differently—for example, applying repair heuristics for hard constraints while using adaptive penalty functions for soft constraints [67].
Experimental Protocols & Methodologies
Protocol: Implementing Multi-Stage Evolutionary Framework
Purpose: To dynamically balance exploration and exploitation across different evolutionary phases for complex COPs.
Materials: CEC2017 or CEC2020 benchmark suite, computational environment with MATLAB/Python.
Procedure:
- Initialization: Generate initial population with sampling techniques (Latin Hypercube recommended for improved diversity).
- Stage 1 (Exploration-Focused):
- Stage Transition: Monitor population feasibility ratio and diversity metrics. Trigger transition when feasibility ratio exceeds 40% or diversity drops below threshold.
- Stage 2 (Exploitation-Focused):
- Archive Management: Maintain elite solutions from both feasible and informative infeasible regions. Update archive using Pareto dominance criteria considering both objective function and constraint violation [5].
Troubleshooting Notes:
- If convergence stagnates, increase exploration duration or introduce periodic diversity injection.
- If feasible region not found, relax ε parameter or adjust constraint classification strategy.
Protocol: Ensemble Constraint Handling Technique
Purpose: To leverage multiple constraint handling techniques adaptively without manual parameter tuning.
Materials: FEPEA framework, real-world constrained optimization benchmarks.
Procedure:
- Technique Pool: Implement four core constraint handling techniques: adaptive penalty functions, feasibility rules, ε-constrained method, and stochastic ranking [66].
- Voting Mechanism: Each technique evaluates and ranks population members. Maintain performance history for each technique.
- Selection: Apply techniques proportional to their recent performance using a probability distribution updated every generation.
- Knowledge Sharing: Implement junior-senior knowledge transfer mechanism where promising solutions from subpopulations share information [66].
- Parameter Adaptation: Automatically adjust mutation rates, crossover parameters, and population size based on success rates of operators.
Validation: Test on CEC2020 real-world constrained optimization benchmark with 57 problems. Compare against individual techniques using statistical significance tests.
Performance Data & Comparative Analysis
Table 1: Comparison of Constraint Handling Techniques on CEC2010 Benchmark Problems
| Technique | Average Feasibility Rate | Success Rate on Disconnected Feasible Regions | Computational Overhead | Parameter Sensitivity |
|---|---|---|---|---|
| Adaptive Penalty Functions | 87.3% | Medium | Low | High |
| ε-Constrained Method | 92.1% | High | Medium | Medium |
| Multi-Objective Conversion | 89.7% | High | High | Low |
| Gradient-Based Repair | 95.4% | Low | High | Medium |
| Hybrid Technique (Classification-Collaboration) | 96.2% | High | Medium | Low |
Table 2: Exploration-Exploitation Balance Metrics in Different Algorithmic Frameworks
| Algorithm | Exploration Intensity (Early Stage) | Exploitation Intensity (Late Stage) | Balance Adaptation | Performance on CEC2017 |
|---|---|---|---|---|
| Standard DE | 0.78 | 0.82 | Manual | 0.56 |
| MSEFAS [5] | 0.85 | 0.88 | Adaptive Stage-based | 0.89 |
| EALSPM [19] | 0.82 | 0.86 | Learning Strategy-based | 0.85 |
| εMODE-AGR [44] | 0.79 | 0.91 | Gradient-Adaptive | 0.87 |
| LLM-assisted [10] | 0.83 | 0.89 | Meta-Learned | 0.90 |
Signaling Pathways & Workflow Diagrams
Research Reagent Solutions
Table 3: Essential Algorithmic Components for Constrained Optimization Research
| Component | Function | Implementation Example |
|---|---|---|
| Adaptive Penalty Function | Dynamically balances objective and constraint violation based on search progress | Lemonge et al. adaptive penalty scheme [19] |
| ε-Level Control | Gradually relaxes/restricts constraint tolerance during evolution | Zhang et al. adaptive ε-control method [19] |
| Gradient-Based Repair | Moves infeasible solutions toward feasible regions using local gradient information | Adaptive Gradient-based Repair (AGR) [44] |
| Classification-Collaboration Handler | Decomposes constraints into manageable subgroups for cooperative solution | EALSPM constraint classification [19] |
| Multi-Stage Controller | Manages temporal transition between exploration and exploitation phases | MSEFAS adaptive stage selection [5] |
| Ensemble Voting Mechanism | Combines multiple constraint handling techniques adaptively | FEPEA ensemble with four CHTs [66] |
| Archive Management System | Preserves diverse elite solutions throughout search process | Pareto-based adaptive archives [5] |
Frequently Asked Questions (FAQs)
1. What are the signs that my penalty function is poorly tuned? A poorly tuned penalty function often leads to two main issues: premature convergence to a local optimum or an inability to find a feasible solution. You may observe that your evolutionary algorithm stagnates early in the search process, or that the population remains largely or entirely infeasible after many generations. This indicates an improper balance between exploring the objective function and satisfying constraints [27].
2. How can I adaptively balance exploration and exploitation when handling constraints? A powerful strategy is to implement a stage-based adaptive method. In the early stages of evolution, prioritize finding feasible regions by applying stronger penalties to constraint violations. As the search progresses and feasible solutions emerge, gradually reduce the penalty pressure to allow for a more refined search towards the optimal objective function value. This mimics a shift from broad exploration to focused exploitation [38].
3. My algorithm is converging to infeasible solutions. How can I correct this? This typically occurs when the penalty for constraint violations is too weak. You can correct this by:
- Increasing your penalty coefficients to make infeasible regions less attractive.
- Implementing a feasibility rules approach, where any feasible solution is automatically considered better than any infeasible one.
- Using an adaptive method that dynamically increases the penalty if the population remains infeasible after a certain number of generations [38] [27].
4. What is a key difference between static and adaptive penalty methods? The key difference lies in the need for extensive pre-tuning. Static penalty methods require you to find a fixed, optimal penalty coefficient before the main run, which can be time-consuming and problem-specific. Adaptive penalty methods automate this process by dynamically adjusting the penalty parameters during the run based on feedback from the search process, such as the current proportion of feasible solutions or the best solution found [27].
Troubleshooting Guides
Problem: Algorithm Performance is Highly Sensitive to Initial Penalty Parameters
Symptoms: Small changes in the initial penalty coefficient lead to vastly different optimization results. The algorithm performs well on one problem instance but fails on another, seemingly similar, instance.
Diagnosis: This is a classic limitation of static penalty functions. A single, fixed parameter cannot effectively guide the search through different phases (exploration vs. exploitation) or adapt to the unique landscape of different problems [27].
Solution: Implement a Stage-based Adaptive Penalty Method (SAPDE).
- Initialization Phase: If no feasible solutions exist in the initial population, assign static, high penalty coefficients to strongly drive the search toward feasibility [38].
- Adaptation Phase: Once feasible solutions begin to appear, switch to a dynamic adjustment strategy. A recommended method is to use an exponential function to gradually decrease the penalty coefficient as evolutionary generations increase. This allows for a smooth transition from prioritizing constraint satisfaction to optimizing the objective function [38].
Verification: Run the adapted algorithm on multiple benchmark problems. A well-tuned adaptive method should show consistent and robust performance across different problems without needing to re-tune parameters for each one [38].
Problem: Population Lacks Diversity and is Trapped in Local Optima
Symptoms: The population converges quickly, and all candidate solutions are very similar. The algorithm fails to improve the best solution over many generations, even when starting from different initial populations.
Diagnosis: The search strategy is over-exploiting certain regions and lacks mechanisms to escape local optima. This can happen even with adaptive penalties if the search operators themselves are not diverse enough [68] [38].
Solution:
- Integrate Multiple Search Strategies: Use more than one mutation or crossover strategy in your differential evolution (DE) or evolutionary algorithm. For example, employ two different DE strategies to generate offspring, which helps explore the search space more thoroughly [38].
- Apply a Mutation Scheme: Introduce an additional mutation step specifically designed to enhance population diversity and help the algorithm jump out of local optima [38].
- Consider a Repair Strategy: For challenging constraints, implement a repair strategy that attempts to "fix" infeasible solutions by moving them toward the feasible region, thereby preserving potentially useful genetic information [38].
Verification: Monitor the diversity of your population (e.g., by tracking the variance of objective function values or decision variables). You should observe that the population maintains higher diversity for a longer period and that the algorithm can find improved solutions after appearing to stagnate.
Experimental Protocols & Data
Protocol 1: Implementing a Stage-Based Adaptive Penalty Method
This protocol is based on the SAPDE method [38].
Parameter Definition:
- Let
Gbe the current generation number. - Let
MaxGbe the maximum number of generations. - Let
λ(G)be the penalty coefficient at generationG. - Define a threshold generation
G_t(e.g., 20% ofMaxG) to separate stages.
- Let
Algorithm:
- Stage 1 (G ≤ G_t):
- If the population has no feasible solutions, use a fixed, high penalty coefficient (e.g.,
λ(G) = λ_max). - The goal is to aggressively steer the population toward the feasible region.
- If the population has no feasible solutions, use a fixed, high penalty coefficient (e.g.,
- Stage 2 (G > G_t):
- Apply an exponential decay to the penalty coefficient:
λ(G) = λ_max * exp(-k * (G - G_t)) - Here,
kis a decay constant that controls the rate of decrease. - This gradual reduction allows the algorithm to focus more on optimizing the objective function once feasibility is likely achieved.
- Apply an exponential decay to the penalty coefficient:
- Stage 1 (G ≤ G_t):
Protocol 2: Benchmarking Constraint Handling Techniques (CHTs)
Use this protocol to evaluate the performance of any new adaptive parameter control method against established benchmarks [38] [27].
- Benchmark Suite: Select a standard set of constrained optimization problems, such as the CEC 2010 benchmark suite [38].
- Performance Metrics: For each algorithm run, record:
- Feasibility Rate (FR): The percentage of runs that find at least one feasible solution.
- Best Objective Function Value: The value of
f(x)for the best feasible solution found. - Constraint Violation (CV): The degree to which the constraints are violated by the best solution.
- Experimental Setup:
- Run each algorithm (e.g., your new method, a static penalty method, a feasibility rules method) 25 times on each benchmark problem to account for stochasticity [38].
- Use the same population size and maximum number of function evaluations (
MaxFES) for all compared algorithms.
- Analysis: Compare the mean and standard deviation of the performance metrics across all 25 runs. Statistical tests (e.g., Wilcoxon signed-rank test) can confirm if performance differences are significant.
The following table summarizes example performance data for various CHTs on a standard benchmark, allowing for quick comparison. Note: Data is illustrative based on search results [38].
| Constraint Handling Technique | Type | Key Tuning Parameters | Best Performance (Example) |
|---|---|---|---|
| Static Penalty | Static | Fixed penalty coefficient | Highly variable; requires problem-specific tuning [27]. |
| Feasibility Rules | Separation | None | Fast convergence but may get stuck in local optima if feasible region is disjoint [27]. |
| ε-Constraint Method | Adaptive | ε threshold and its update rate | Effective balance; relies on a good ε-update schedule [27]. |
| Stage-based Adaptive (SAPDE) | Adaptive | Initial penalty (λ_max), decay rate (k), stage threshold (G_t) |
Competitive and robust performance across diverse benchmark problems [38]. |
Workflow Visualization
The following diagram illustrates the logical workflow and decision process for a stage-based adaptive penalty method.
Diagram: Stage-Based Adaptive Penalty Workflow
The Scientist's Toolkit: Research Reagent Solutions
This table lists key computational "reagents" essential for experimenting with self-adjusting parameters in constrained evolutionary optimization.
| Item / Concept | Function in the Experiment | Key Consideration |
|---|---|---|
| Benchmark Suites (e.g., CEC 2010) | Provides a standardized set of constrained problems to validate and compare algorithm performance fairly [38]. | Ensure the suite contains a mix of problems with different characteristics (e.g., linear/nonlinear constraints, separable/non-separable variables). |
| Differential Evolution (DE) | Serves as the core search engine (metaheuristic) for generating new candidate solutions [38] [27]. | The choice of DE mutation strategy (e.g., DE/rand/1, DE/best/1) can significantly impact exploration and exploitation balance. |
| Feasibility Rules | A constraint-handling technique used as a baseline or component in hybrid methods; it strictly prioritizes feasible over infeasible solutions [27]. | Its greedy nature can be beneficial but may require combination with other techniques to maintain diversity. |
| ε-Constraint Method | An adaptive CHT that relaxes the feasibility requirement, allowing slightly infeasible solutions with good objective values to be considered [27]. | Performance is highly dependent on the strategy for adapting the ε parameter over time. |
| Repair Algorithms | A method to "fix" infeasible solutions by projecting them onto the feasible region, preserving their genetic information [38]. | The repair mechanism must be computationally efficient and designed to not bias the search. |
Performance Evaluation: Benchmarking and Comparative Analysis of Adaptive CHTs
For researchers developing adaptive constraint handling techniques for Constrained Optimization Problems (COPs), standardized benchmark suites are indispensable tools. They enable fair, reproducible, and comparable performance assessments of new algorithms. The Congress on Evolutionary Computation (CEC) sponsors several renowned competition problem suites that have become gold standards in the field. These suites provide a diverse range of challenges, from single-objective engineering design problems to complex multi-objective scenarios, reflecting real-world difficulties such as small feasible regions and disconnected Pareto fronts [5] [2].
FAQ: Key Benchmark Suites and Their Applications
Q1: What are the primary CEC benchmark suites for constrained optimization, and what are their key characteristics?
A: The CEC sponsors several competition problem suites. The table below summarizes the key benchmark suites for constrained optimization [69] [70] [2]:
Table 1: Key CEC Benchmark Suites for Constrained Optimization
| Suite Name | Problem Types | Key Characteristics | Number of Problems | Notable Features |
|---|---|---|---|---|
| CEC2020 Real-World Suite [69] | Single-Objective, Constrained | Real-world engineering design problems | 7 | Includes problems like speed reducer design and tension/compression spring |
| CEC2009 [70] | Multi-Objective, Constrained & Unconstrained | Includes constrained (CF) and unconstrained (UF) problems | 10 CF, 10 UF | Standardized for performance assessment of multi-objective algorithms |
| Real-World Constrained Multi-Objective Suite [2] | Multi-Objective, Constrained | Collected from various real-world applications | 50 | Covers mechanical design, chemical engineering, power systems |
Q2: What specific engineering problems are included in the CEC2020 Real-World Suite?
A: The CEC2020 suite is a seven-problem set focusing on real-world single-objective constrained engineering optimization [69] [71]:
- RC15 – Speed Reducer Weight Minimization
- RC17 – Tension/Compression Spring Design
- RC19 – Welded Beam Design
- RC20 – Three-Bar Truss Design
- RC23 – Step-Cone Pulley Design
- RC28 – Rolling Element Bearing Design
- RC31 – Gear Train Design
This suite is commonly used to evaluate algorithms like GWO, DE, SSA, and others using performance metrics such as mean objective value, standard deviation, and Friedman ranking [69].
Q3: How are constraints mathematically defined in these benchmark problems?
A: A Constrained Optimization Problem (COP) is typically formulated as follows [19]:
Minimize ( f(\mathbf{x}) ), where ( \mathbf{x} = (x1, \ldots, xD) \in S ) Subject to: ( gj(\mathbf{x}) \leq 0, \quad j=1,\ldots,l ) ( hj(\mathbf{x}) = 0, \quad j=l+1,\ldots,m )
Here, ( f(\mathbf{x}) ) is the objective function, ( gj(\mathbf{x}) ) are inequality constraints, and ( hj(\mathbf{x}) ) are equality constraints. The constraint violation for a solution ( \mathbf{x} ) is calculated as [19] [2]:
[ Gj(\mathbf{x}) = \begin{cases} \max(0, gj(\mathbf{x})), & 1 \leq j \leq l \ \max(0, |h_j(\mathbf{x})| - \delta), & l+1 \leq j \leq m \end{cases} ]
The total constraint violation is ( G(\mathbf{x}) = \sum{j=1}^m Gj(\mathbf{x}) ). A solution is feasible if ( G(\mathbf{x}) = 0 ) [19].
Q4: What are the categories of Constrained Multi-Objective Problems (CMOPs), and why is this classification important?
A: CMOPs are classified into four types based on the relationship between the constrained Pareto front and the unconstrained one [2]:
Table 2: Classification of Constrained Multi-Objective Optimization Problems (CMOPs)
| Type | Relationship to Unconstrained PF | Challenge Level |
|---|---|---|
| Type I | Constrained PF is identical to unconstrained PF | Low (No need to minimize constraint violation) |
| Type II | Constrained PF is a subset of unconstrained PF | Medium |
| Type III | Constrained PF partially overlaps with unconstrained PF | Medium-High |
| Type IV | Constrained PF and unconstrained PF have no common region | High (Requires significant focus on constraint violation) |
This classification is crucial for selecting and developing appropriate constraint-handling techniques, as the required balance between minimizing objectives and satisfying constraints varies significantly across types [2].
CMOP Classification and Challenge Level
Troubleshooting Common Experimental Issues
Q5: What are common reasons for an algorithm's poor performance on CEC benchmark problems, and how can they be addressed?
A: Common failure modes and solutions when working with CEC suites include:
Issue: Inability to Find Feasible Regions
- Causes: Overly strict constraint handling that prematurely eliminates promising infeasible solutions; population diversity loss.
- Solutions: Implement multi-stage approaches that initially allow promising infeasible solutions to guide the search toward feasible regions [5]. Use adaptive techniques that balance objective optimization and constraint satisfaction based on population status [19].
Issue: Poor Convergence Near Feasibility Boundaries
- Causes: Inadequate handling of problems where the optimum lies on or near constraint boundaries (common in real-world problems).
- Solutions: Employ epsilon-constraint methods that adaptively control the tolerance for constraint violations [19]. Hybrid techniques combining feasibility rules with objective function information (FROFI) can mitigate the greediness of pure feasibility rules [19].
Issue: Algorithm Performs Well on Synthetic Problems but Poorly on Real-World Suites
- Causes: Synthetic Benchmark Problems (SBPs) may include unrealistic properties that don't reflect real-world challenges, leading to overestimation or underestimation of algorithm performance [2].
- Solutions: Test algorithms on both synthetic benchmarks and real-world suites like the CEC2020 or the 50-problem RWCMOP suite [2]. Real-world problems often have more complex feasible regions and different characteristics.
Q6: What is a standard experimental protocol for evaluating new constraint-handling techniques?
A: A rigorous experimental methodology should include:
Problem Selection: Choose a diverse set from multiple suites (e.g., CEC2009 CF, CEC2020, RWCMOP) covering different CMOP types and challenge levels [2].
Performance Metrics:
Comparison Baselines: Compare against state-of-the-art algorithms. For example, in single-objective constrained optimization, common baselines include DE, IMODE, and SHADE [10].
Experimental Rigor: Conduct multiple independent runs (e.g., 31 runs) to ensure statistical significance [10]. Report computational complexity measures where possible.
Experimental Evaluation Workflow
The Scientist's Toolkit: Essential Research Reagent Solutions
Table 3: Key Algorithmic Components for Constrained Optimization Research
| Component | Function | Examples from Literature |
|---|---|---|
| Constraint Handling Techniques (CHTs) | Balance objective optimization with constraint satisfaction | Penalty functions, Feasibility rules, ε-constraint, Stochastic ranking [19] |
| Multi-Stage Frameworks | Divide optimization into phases with different strategies | MSEFAS uses three stages: promising infeasible solutions, spanning infeasible regions, and handling PF-CPF relationship [5] |
| Multi-Objective Conversion | Transform COPs into multi-objective problems | Convert to dynamic CMOP (DCMOP) or bi-objective problem (BOP) [19] |
| Hybrid CHTs | Combine multiple techniques based on population status | Classification-collaboration technique decomposes constraints into subproblems [19] |
| Learning Strategies | Utilize machine learning to guide search | EALSPM uses random and directed learning stages with a predictive model [19] |
FAQs and Troubleshooting Guide
This technical support center provides solutions for researchers and scientists encountering issues when using the Inverted Generational Distance (IGD) and Hypervolume (HV) metrics in experiments on Constrained Multi-objective Optimization Problems (CMOPs).
Frequently Asked Questions
FAQ 1: My algorithm finds feasible solutions, but both IGD and HV metrics are poor. What is wrong? This typically indicates that the solutions are feasible but converge poorly or have low diversity against the true Pareto front.
- Theory of Probable Cause: The reference set (true Pareto front) used for calculating the metrics is incorrect or incomplete [72].
- Plan of Action:
- Verify the reference set is correct and well-distributed.
- Check if your algorithm's solutions cover all regions of the reference set.
- Ensure the normalization of objective spaces is consistent between your solutions and the reference set.
- Resolution: Re-generate or update the reference set using a combination of algorithms known to perform well on your benchmark problem. Re-calculate the metrics.
FAQ 2: The Hypervolume value is inconsistent across different runs, even with the same algorithm and problem. This is often related to the setup of the Hypervolume calculation, particularly the reference point.
- Theory of Probable Cause: The reference point for the Hypervolume calculation is not fixed or is chosen inappropriately [72].
- Plan of Action:
- Ensure the reference point is identical for all experimental runs.
- Confirm the reference point is dominated by all points in the approximation set.
- Resolution: Establish a standardized protocol for setting the Hypervolume reference point, typically as a point slightly worse than the worst possible value in each objective across all algorithm runs. Document this point for reproducibility.
FAQ 3: How should I handle infeasible solutions when calculating IGD and HV? The treatment of infeasible solutions is critical and depends on your experimental goals.
- Theory of Probable Cause: Infeasible solutions are included in the final approximation set provided to the metric calculators.
- Plan of Action:
- Decide if your metric should only reflect the performance of feasible, non-dominated solutions.
- Consider if you want to penalize the presence of infeasible solutions.
- Resolution: The most common practice is to filter out all infeasible solutions before calculating IGD and HV. This ensures the metrics only evaluate the quality of the feasible solution set. Document your filtering methodology clearly.
FAQ 4: My constrained optimization algorithm stalls and cannot find feasible solutions. How can I improve feasibility rates? This is a core challenge in constrained optimization related to the constraint-handling technique (CHT).
- Theory of Probable Cause: The algorithm's CHT is not effective for the specific constraints of your problem [72] [73].
- Plan of Action:
- Resolution: Implement an adaptive or ensemble-based CHT that can dynamically adjust its strategy based on the search landscape [72] [74]. Test simpler feasibility rules first.
Experimental Protocols for Metric Calculation
Protocol 1: Standardized Calculation of Inverted Generational Distance (IGD) IGD measures both convergence and diversity by calculating the average distance from each point in the true Pareto front (P*) to the nearest point in the approximated solution set (S).
Formula: [ IGD(P^, S) = \frac{\sum_{v \in P^} d(v, S)}{|P^*|} ] where ( d(v, S) ) is the minimum Euclidean distance between point ( v ) and any point in set ( S ) in the objective space.
Methodology:
- Obtain a True Pareto Front (P*): Use a known reference set for standard benchmarks, or generate one by combining non-dominated solutions from multiple algorithms run for a long time.
- Normalize Objectives: Scale objective values to a common range (e.g., [0,1]) using the min and max values from P* to prevent dominance by a single objective.
- Calculate Distances: For each point in P*, compute the Euclidean distance to every point in your algorithm's final, feasible approximation set (S). Record the minimum distance.
- Compute Average: Sum all minimum distances and divide by the number of points in P*.
- Interpretation: A lower IGD value indicates better convergence and diversity.
Protocol 2: Standardized Calculation of Hypervolume (HV) HV measures the volume of the objective space dominated by an approximation set (S) and bounded by a reference point (r).
Methodology:
- Define a Reference Point (r): Select a point that is worse than or equal to the worst performance in each objective across all sets being compared. This point must be dominated by all solutions in S.
- Filter Solutions: Use only feasible, non-dominated solutions from your algorithm's final population for the HV calculation.
- Calculate the Volume: The HV is the union of the hypercubes defined by each solution in S and the reference point r. Use an efficient HV calculation algorithm, such as the WFG algorithm.
- Interpretation: A higher HV value indicates a better combination of convergence and diversity.
Performance Metrics and Constraint-Handling Techniques
The choice of Constraint-Handling Technique (CHT) directly impacts algorithm performance, as measured by IGD and HV. The table below summarizes common CHTs adapted for CMOPs.
Table 1: Common Constraint-Handling Techniques (CHTs) in Constrained Multi-Objective Optimization
| Technique Category | Core Principle | Key Considerations for IGD/HV |
|---|---|---|
| Penalty Functions [72] [76] | Penalizes infeasible solutions by adding a constraint violation term to the objective function. | Simplicity. Performance highly sensitive to the choice of penalty parameters. |
| Multi-objective Approaches [75] | Treats constraint satisfaction as an additional objective to be optimized. | No need for parameters. Can complicate the Pareto front and slow convergence. |
| Feasibility Rules | Gives strict precedence to feasible solutions over infeasible ones. | Simple and effective for problems with moderate constraints. May get stuck in feasible but suboptimal regions. |
| Ensemble Methods [72] [74] | Combines multiple CHTs adaptively during the search process. | Can be more robust across different problem types. Increases algorithmic complexity. |
| Separation-based | Separates the handling of objectives and constraints, often using different populations. | Effective for complex constraints. Good for maintaining diversity among feasible solutions, positively impacting HV. |
Table 2: Troubleshooting Common Experimental Scenarios
| Observed Scenario | Potential Diagnosis | Recommended Action |
|---|---|---|
| Good IGD, Poor HV | The solution set converges well but lacks diversity at the extremes. | Check the HV reference point. Encourage more diverse solutions via mutation or niche-preservation. |
| Good HV, Poor IGD | The solution set is diverse but has poor convergence to the true Pareto front. | The algorithm may be exploiting a large but shallow region. Focus search operators on improving convergence. |
| High Variance in Metrics | The algorithm's performance is unstable, or the metric setup is inconsistent. | Fix the reference point (for HV) and reference set (for IGD). Increase the number of independent runs for statistical significance. |
| No Feasible Solutions Found | The CHT is too weak, or the search operators cannot generate feasible solutions. | Switch to a more powerful CHT (e.g., ensemble method). Implement a dedicated feasibility-first initialization. |
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Computational Tools and Metrics for CMOPs Research
| Item | Function in CMOPs Research |
|---|---|
| Reference Pareto Front (P*) | The ground-truth set of optimal trade-off solutions used as a benchmark for calculating performance metrics like IGD. |
| Hypervolume Reference Point (r) | A crucial point in objective space that defines the region of interest for calculating the Hypervolume indicator. |
| Normalization Bounds | The minimum and maximum values for each objective, used to scale objectives to a common range and prevent bias in metric calculations. |
| Feasibility Threshold | A defined tolerance level for determining whether a constraint is satisfied, converting a hard constraint into a soft one for numerical stability. |
| Performance Metric Calculator | Specialized software (e.g., PlatEMO, pymoo) that implements standardized algorithms for computing IGD, HV, and other metrics. |
Experimental Workflow and Metric Interpretation
The following diagram illustrates the logical workflow for evaluating a constrained multi-objective optimizer using IGD and Hypervolume metrics.
Advanced Diagnostics: Constraint-Handling Landscape
Understanding the interaction between the algorithm's search and the constraint boundaries is key to advanced diagnostics. The diagram below visualizes this relationship and its impact on performance metrics.
In both single- and multi-objective optimization problems found in fields from engineering to drug development, Constraint Handling Techniques (CHTs) are essential for finding solutions that satisfy all problem limitations while optimizing objectives [25] [77]. Real-world problems often require optimizing multiple conflicting objectives while satisfying complex constraints, making traditional mathematical methods prone to becoming trapped in local optima [25]. Evolutionary Algorithms (EAs) combined with CHTs have demonstrated powerful capabilities for solving these complex constrained optimization problems (COPs) [77].
This technical support center document focuses on three prominent CHT paradigms—penalty functions, stochastic ranking, and ε-constraint methods—within the context of advanced research on adaptive constraint handling. These techniques enable population-based algorithms to effectively navigate feasible and infeasible regions of search spaces, gradually steering solutions toward optimality while maintaining feasibility [28] [77]. As research in this field evolves, ensemble methods that dynamically combine these approaches are showing particular promise for handling diverse problem structures [28].
Core Concepts and Definitions
Constrained Multi-Objective Optimization Problems (CMOPs) are mathematically defined as [25]:
- Minimize: $\vec{F}(\vec{x})=(f{1}(\vec{x}), f{2}(\vec{x}), \ldots, f_{m}(\vec{x}))^{T}$
- Subject to:
- $g{i}(\vec{x}) \le 0, i=1, \ldots, l$ (inequality constraints)
- $h{i}(\vec{x})=0, i=1, \ldots, k$ (equality constraints)
- Where: $\vec{x}=(x{1}, x{2}, \ldots, x_{D})^{T} \in \mathbb{R}$ (decision vector)
The total constraint violation is calculated as $CV(\vec{x})=\sum{i=1}^{l+k} cv{i}(\vec{x})$, where $cv_{i}$ represents the violation degree for the i-th constraint [25]. A solution is considered feasible when $CV(\vec{x})=0$, and infeasible otherwise.
Comparative Analysis of CHT Approaches
Table 1: Core Characteristics of Primary CHT Paradigms
| Technique | Core Mechanism | Key Advantages | Common Challenges |
|---|---|---|---|
| Penalty Functions | Converts constrained problem to unconstrained by adding penalty terms for constraint violations [77] | Simple implementation; Wide applicability [77] | Sensitivity to penalty parameter tuning; Performance depends on penalty magnitude [77] |
| Stochastic Ranking | Balances objective and feasibility using probabilistic ranking during selection [78] | Effective balance between exploration/exploitation; Reduces parameter sensitivity [28] [78] | Ranking probability requires calibration; May prematurely discard promising infeasible solutions [78] |
| ε-Constraint Method | Uses tolerance value (ε) that gradually decreases to allow controlled infeasibility [77] | Systematic approach to feasibility; Controlled transition from exploration to feasibility [28] [77] | ε-reduction schedule affects performance; Initial ε value selection is critical [77] |
| Feasibility Rules | Prioritizes feasibility over objective performance using simple comparison rules [77] | No parameters needed; Simple and computationally efficient [77] | May converge to boundary-optimal solutions; Struggles with disconnected feasible regions [77] |
Troubleshooting Common Experimental Issues
FAQ: Penalty Function Implementation
Q1: How can I determine appropriate penalty weights for my specific optimization problem?
A: Determining optimal penalty weights remains challenging. Start with adaptive penalty methods that adjust weights based on population feasibility ratios. Monitor the proportion of feasible solutions in your population—if it remains consistently below 10-15%, your penalties may be too lenient; if above 85-90%, you may be over-penalizing and missing promising regions. Implement a stepwise adaptation method that increases penalties when feasibility stagnates, and decreases them when diversity drops excessively.
Q2: Why does my algorithm converge to suboptimal solutions when using penalty functions?
A: This common issue typically stems from excessive penalty magnitudes that create deceptive landscapes. Implement dynamic penalty adjustment that gradually increases penalty pressure as generations progress. Alternatively, consider switching to a multi-objective approach that treats constraint violation as a separate objective to avoid this problem entirely. The RECHT framework demonstrates that combining penalty functions with other CHTs in an ensemble can mitigate this issue [28].
FAQ: Stochastic Ranking Challenges
Q1: How do I set the appropriate ranking probability (Pf) for my problem?
A: The optimal Pf value depends on your problem's characteristics. For problems with relatively large feasible regions, start with Pf = 0.4-0.5 to balance objective and feasibility considerations. For highly constrained problems with small feasible regions, increase Pf to 0.6-0.7 to emphasize feasibility. Implement self-adaptive stochastic ranking (SSR) that automatically adjusts Pf based on population feasibility statistics, as demonstrated in MOEA/D-SSR [78].
Q2: My stochastic ranking implementation shows high performance variance across runs. Is this expected?
A: Some variance is inherent in stochastic methods, but excessive variance suggests issues with probability calibration or population diversity. Ensure your ranking probability isn't too extreme (avoid values below 0.3 or above 0.8). Implement diversity preservation mechanisms and consider hybridizing with ε-constraint methods to stabilize performance. The self-adaptive version automatically tunes parameters based on evolutionary state information [78].
FAQ: ε-Constraint Method
Q1: What ε-updating strategy works best for different problem types?
A: The optimal ε-updating strategy depends on problem characteristics:
- For problems with connected feasible regions: Use linear decrease ε(t) = ε₀(1 - t/T)
- For problems with disconnected or small feasible regions: Use slow initial decrease with accelerated later-phase reduction
- For unknown problem structures: Implement adaptive methods that adjust ε based on current population feasibility ratio
Q2: How should I set the initial ε value for constrained optimization?
A: Set initial ε₀ to the constraint violation of the top 20-30% infeasible solutions in your initial population. This provides sufficient search space while maintaining selection pressure. Avoid setting ε₀ too high, as it may lead to premature convergence to infeasible regions. The ensemble approach in RECHT dynamically adjusts ε values as part of its adaptive framework [28].
Advanced Ensemble approaches
Recent research demonstrates that ensemble-based CHTs that combine multiple techniques often outperform individual approaches. The RECHT framework integrates penalty functions, feasibility rules, stochastic ranking, and ε-constrained methods within a ranking-based ensemble that dynamically adjusts constraint-handling strategies [28].
Table 2: Ensemble CHT Components and Their Roles
| Component Technique | Primary Role in Ensemble | Activation Conditions |
|---|---|---|
| Feasibility Rules | Rapid convergence to feasible regions | Early generations; High proportion of infeasible solutions |
| ε-Constraint Method | Controlled exploration near feasibility boundaries | Middle generations; Moderate feasibility ratio |
| Stochastic Ranking | Balanced objective/feasibility trade-off | Steady-state phase; Diverse population |
| Penalty Functions | Fine-tuning within feasible regions | Late generations; High feasibility ratio |
Diagram 1: Adaptive Ensemble CHT Workflow - This diagram illustrates the dynamic selection process for constraint-handling techniques within an ensemble framework based on optimization state.
Experimental Protocols and Performance Analysis
Benchmarking Methodology
For rigorous evaluation of CHT performance, implement the following experimental protocol:
- Problem Selection: Choose diverse benchmark problems from CEC competitions or established suites like PBO, BBOB, DTLZ, and WFG with varying characteristics [28] [78] [79].
- Algorithm Configuration:
- Population size: 100-500 based on problem dimensionality
- Termination: Maximum function evaluations (e.g., 10,000-100,000)
- Multiple independent runs (typically 25-31) to account for stochasticity
- Performance Metrics:
- Solution Quality: Inverted Generational Distance (IGD), Hypervolume (HV)
- Constraint Satisfaction: Feasibility Rate, Constraint Violation
- Efficiency: Function Evaluations to Target, Convergence Speed
Statistical Analysis Protocol
Implement robust statistical analysis using severity-based ranking schemes [79]:
- Perform pairwise algorithm comparisons using bootstrapping-based hypothesis testing
- Calculate practical significance considering effect sizes, not just p-values
- Apply football league-inspired ranking that considers both win/loss records and magnitude of performance differences
- Generate comprehensive performance profiles across multiple problems
Table 3: Essential Research Reagents for CHT Experimentation
| Reagent/Category | Specific Examples | Primary Function in CHT Research |
|---|---|---|
| Benchmark Suites | CEC Problems, PBO Suite, DTLZ, WFG [78] [79] | Standardized performance evaluation across problem types |
| Performance Metrics | IGD, Hypervolume, Feasibility Ratio [78] [79] | Quantitative comparison of algorithm effectiveness |
| Statistical Frameworks | Severity-Based Ranking, Bootstrapping [79] | Robust statistical analysis of performance differences |
| Algorithm Frameworks | MOEA/D, NSGA-II, RECHT [28] [78] [25] | Implementation foundation for CHT integration |
Implementation Guidelines
Selection Heuristics for CHT Paradigms
Based on problem characteristics, use the following guidelines for CHT selection:
- For problems with known, large feasible regions: Prioritize stochastic ranking or ε-constraint methods
- For highly constrained problems with small feasible regions: Begin with feasibility rules, transitioning to ε-constraint methods
- For problems with unknown feasibility characteristics: Implement ensemble approaches like RECHT [28]
- For real-time applications with limited function evaluations: Use adaptive penalty methods with warm-start strategies
Parameter Configuration Strategies
Diagram 2: CHT Parameter Configuration Strategy - This workflow shows the process for initial parameter setting and adaptive adjustment based on performance monitoring.
The comparative analysis reveals that no single CHT dominates across all problem types, underscoring the value of adaptive ensemble approaches like RECHT [28]. Penalty functions offer simplicity but suffer from parameter sensitivity, stochastic ranking provides effective balance but requires calibration, while ε-constraint methods enable controlled exploration but need careful reduction schedules.
Future CHT research should focus on:
- Self-adaptive mechanisms that automatically adjust CHT selection and parameters based on problem characteristics and search state [78]
- Hybrid CHTs that leverage the complementary strengths of different approaches [28] [77]
- Problem-aware CHTs that utilize knowledge about constraint types and feasible region structures
- Scalable CHTs for high-dimensional and large-scale optimization problems
For practical implementation, researchers should begin with ensemble approaches that provide robust performance across diverse problem structures, then specialize based on specific domain characteristics and performance requirements.
Technical Support Center: Troubleshooting Guides and FAQs
This section provides targeted support for researchers implementing adaptive Constrained Optimization Problem (COP) solvers, addressing common experimental and algorithmic challenges.
Frequently Asked Questions (FAQs)
Q1: My evolutionary algorithm converges to infeasible solutions. How can I guide it toward the feasible region? A1: This is a common issue often related to an imbalance between objective function optimization and constraint satisfaction. Implement an adaptive ranking-based constraint handling technique (AR-DE). This method identifies both the best feasible solution and the "best infeasible solution" (the infeasible solution with the lowest constraint violation) in the population. Using these two guides, the algorithm can strategically navigate toward the feasible region from both inside and outside its boundaries [46].
Q2: How can I handle problems with a large number of complex constraints without making the search process too slow? A2: Consider a classification-collaboration constraint handling technique. This approach decomposes the original problem by randomly classifying its constraints into several groups (K classes), creating K simpler subproblems. A corresponding subpopulation is then assigned to each subproblem. These subpopulations interact through random and directed learning strategies, effectively managing constraint pressure and leveraging complementary information from different constraints [19].
Q3: Which constraint handling technique (CHT) should I choose for my specific problem? A3: According to the No Free Lunch theorem, no single CHT outperforms all others on every problem. A robust solution is to use an Ensemble of Constraint Handling Techniques (ECHT). Probabilistically combine multiple CHTs, such as:
- Superiority of feasible solutions
- Self-adaptive penalty
- ε-constraint handling technique
- Stochastic ranking This allows the algorithm to adaptively select the most effective strategy during different stages of the search process [47].
Q4: How many test units or experimental replications are needed to validate a solution statistically? A4: The sample size must be scaled to the failure rate of the problem. A key guideline is the formula n = 3/p, where 'p' is the failure rate you are trying to resolve. For example, to validate an improvement for an issue with a 10% failure rate (p=0.1), you should test at least n = 3 / 0.1 = 30 units and observe zero failures to have statistical confidence (α=0.05) that the solution is effective [80].
Q5: My algorithm performs well on benchmark functions but fails on my real-world biomedical problem. What could be wrong? A5: This often stems from a disconnect between simulation and reality.
- Validate your test with the real world: Ensure that your computational experiments and lab assays accurately simulate real-world conditions. For instance, a robot might test a button-press differently than a human, leading to uncaught failure modes in the field [80].
- Check for implicit constraints: Real-world systems often contain unmodeled physical, temporal, or geometric constraints. Perform a sensitivity analysis to identify these implicit constraints and incorporate them into your model [46].
The performance of advanced COP algorithms is typically evaluated on standard test suites. The table below summarizes key performance metrics from recent research, providing a benchmark for comparison.
Table 1: Performance Comparison of Selected Adaptive Constrained Optimization Algorithms
| Algorithm Name | Core Constraint Handling Strategy | Test Benchmarks Used | Key Performance Metrics | Reported Findings |
|---|---|---|---|---|
| EALSPM [19] | Classification-collaboration decomposition & learning strategies | CEC2010, CEC2017 | Feasibility Rate, Success Rate | Competitive performance against state-of-the-art methods on benchmark and practical problems. |
| AR-DE [46] | Adaptive ranking utilizing best feasible & best infeasible solutions | CEC'06, 5 Engineering Design Problems | Best Objective Value, Statistical Significance (e.g., Wilcoxon test) | Overall results were better than other compared methods, showing effectiveness in feasible region exploration. |
| SaDE-ECHT [47] | Ensemble of 4 CHTs (feasibility rules, penalty, ε-constraint, ranking) | 24 COPs from CEC'06 | Feasibility Rate (FR), Success Rate (SR) | SaDE-ECHT surpassed JADE-ECHT in Feasibility Rate (FR). |
| JADE-ECHT [47] | Ensemble of 4 CHTs hybridized with JADE algorithm | 24 COPs from CEC'06 | Feasibility Rate (FR), Success Rate (SR) | JADE-ECHT outperformed SaDE-ECHT in Success Rate (SR). |
Experimental Protocols and Methodologies
Protocol: Validating a COP Solver on Engineering Design Problems
This methodology outlines the steps for experimentally validating an adaptive constraint handling algorithm using standard engineering design problems [46] [47].
- Algorithm Implementation: Code the evolutionary algorithm (e.g., Differential Evolution) and integrate the chosen adaptive constraint handling technique (e.g., AR-DE, ECHT).
- Parameter Tuning: Set the core algorithmic parameters (e.g., population size, scaling factor F, crossover rate Cr). For adaptive methods, define the rules for parameter adjustment.
- Benchmark Selection: Select a suite of well-known constrained engineering problems for evaluation (e.g., Pressure Vessel Design, Welded Beam Design).
- Experimental Runs:
- Execute a statistically significant number of independent runs (e.g., 30 runs) for each algorithm on each problem to account for stochasticity.
- Record the best feasible solution found, the constraint violation, and the number of function evaluations (or iterations) in each run.
- Data Collection & Analysis:
- Calculate performance metrics like Best, Median, Worst, and Standard Deviation of the objective function for feasible solutions.
- Perform non-parametric statistical tests (e.g., Wilcoxon signed-rank test) to determine if performance differences between algorithms are statistically significant.
- Validation: Compare the best-found design variables and objective values against known literature values to verify the physical correctness and competitiveness of the solution.
Protocol: Development and Testing of a Mobile Expert System for Biomedical Equipment Repair
This protocol details the experimental validation of a decision-support system in a biomedical context, a key real-world application [81].
- Needs Assessment & Survey: Conduct a preliminary survey (e.g., via online tools like Qualtrics) of the target users (e.g., biomedical technicians) to identify specific barriers, current practices, and resource gaps.
- System Design (Application Development):
- Develop a mobile application (e.g., for Android) containing troubleshooting guides structured as decision trees with "yes/no" pathways.
- Integrate resource libraries (e.g., manuals, skill tutorials) and, if possible, a feature to connect with remote experts.
- Design the system to function primarily offline, syncing data only when connected.
- Usability Testing:
- Recruitment: Use convenience sampling to recruit a group of target users (e.g., 33 technicians) for pilot testing.
- Task Execution: Provide users with a malfunctioning piece of standard medical equipment (e.g., a pulse oximeter with a known fault like an occluded sensor or frayed wire). Ask them to diagnose and repair the fault using only the application.
- Data Collection:
- Record the task success rate (e.g., 100% successful repair).
- Administer post-task surveys using standardized tools to quantitatively measure Usability (e.g., via a modified Usability.gov tool) and Content Validity (user perception of content accuracy and usefulness) on a 5-point Likert scale (Strongly Disagree to Strongly Agree).
- Data Analysis: Analyze survey results, focusing on high-level usability perceptions and specific feedback on content value to identify strengths and areas for improvement in the system.
Visual Workflows and System Diagrams
Adaptive COP Solver Architecture
Biomedical Troubleshooting System
The Scientist's Toolkit: Research Reagent Solutions
Table 2: Essential Components for COP and Biomedical Experimental Validation
| Category | Item / Technique | Function & Explanation |
|---|---|---|
| Algorithmic Core | Differential Evolution (DE) | A simple, efficient, population-based stochastic optimizer that serves as the foundation for many advanced COP solvers [46] [47]. |
| Ensemble of CHTs (ECHT) | A probabilistic blend of multiple constraint handling methods (e.g., feasibility rules, penalty, ranking) to robustly address diverse problems without relying on a single technique [47]. | |
| Validation & Analysis | CEC Benchmark Suites | Standard sets of constrained optimization problems (e.g., CEC2006, CEC2010, CEC2017) used to compare algorithm performance fairly and rigorously against state-of-the-art methods [19] [47]. |
| Statistical Tests (e.g., Wilcoxon) | Non-parametric statistical tests used to verify that the performance improvements of a new algorithm are statistically significant and not due to random chance [46]. | |
| Biomedical Application | Mobile Application Platform | Provides on-the-job, contextual guidance to technicians via decision trees and skill tutorials, often without needing a continuous internet connection [81]. |
| Standardized Usability Surveys | Validated tools (e.g., from Usability.gov) used to quantitatively measure end-users' perceptions of a system's ease of use and utility, critical for adoption [81]. |
Troubleshooting Guides and FAQs
Frequently Asked Questions
Q1: What does it mean if my algorithm comparison shows a statistically significant result (p < 0.05) but the effect size is very small? This scenario indicates that while the observed difference is unlikely to be due to random chance alone, the magnitude of the difference may not be practically meaningful in real-world applications [82] [83]. You should interpret this result by considering the context of your specific optimization problem—a tiny performance improvement might be critical for high-stakes applications but negligible for others. Report both statistical significance and effect size to provide a complete picture [83].
Q2: How do I handle multiple comparisons when testing multiple algorithms against each other? When conducting multiple statistical tests simultaneously, the risk of false positives (Type I errors) increases [82]. To address this, employ correction techniques such as the Bonferroni correction, which adjusts the significance level (α) by dividing it by the number of comparisons being made. This ensures the overall family-wise error rate remains controlled.
Q3: My algorithm's performance metrics show high variability across runs. How does this affect significance testing? High variability makes it more difficult to detect genuine differences between algorithms, reducing the statistical power of your tests [82]. To mitigate this, you can increase your sample size (number of independent runs) or employ techniques like standardization to reduce unnecessary variance. Ensuring consistent experimental conditions across all runs is also crucial.
Q4: What is the difference between statistical significance and practical significance in algorithm comparison? Statistical significance (quantified by p-values) indicates whether an observed effect is likely genuine versus due to random chance [82] [83]. Practical significance refers to whether the magnitude of the performance difference matters in real-world applications, which is determined by effect size and domain context [83]. An algorithm can show statistically significant improvement that is too small to be practically useful.
Q5: How can I determine if my optimization algorithm has truly converged? Convergence analysis typically involves tracking performance metrics across iterations until they stabilize within an acceptable tolerance [84] [85]. For ACCES games, the CCDO and CCDO-RL algorithms provide theoretical convergence guarantees to Nash equilibrium [84]. In practice, you can monitor the relative improvement per iteration—when this value falls below a predetermined threshold consistently, convergence is likely achieved.
Experimental Protocols and Methodologies
Protocol 1: Statistical Comparison of Optimization Algorithms
Objective: To determine whether performance differences between two or more optimization algorithms are statistically significant.
Materials Needed: Computing infrastructure, algorithm implementations, benchmark problem sets, data collection framework.
Procedure:
- Experimental Design: Select appropriate benchmark problems that represent your problem domain. Determine the number of independent runs needed (typically 30+ per algorithm to account for random variation).
- Data Collection: Execute each algorithm on all benchmark problems, recording relevant performance metrics (e.g., solution quality, convergence speed, constraint satisfaction).
- Normality Testing: Check if performance data follows a normal distribution using Shapiro-Wilk or Kolmogorov-Smirnov tests.
- Test Selection: Based on normality results and number of groups compared, select an appropriate statistical test.
- Significance Testing: Execute chosen statistical test(s) with appropriate multiple comparisons corrections.
- Effect Size Calculation: Compute effect size measures (e.g., Cohen's d for group differences) to quantify the magnitude of observed effects.
- Interpretation: Analyze both statistical significance (p-values) and practical significance (effect sizes) to draw meaningful conclusions.
Protocol 2: Convergence Analysis for Constrained Optimization Algorithms
Objective: To analyze and compare the convergence properties of algorithms solving constrained multi-objective optimization problems.
Materials Needed: Algorithm implementations, constrained benchmark problems, performance metrics, visualization tools.
Procedure:
- Metric Selection: Define convergence metrics appropriate for your problem type (e.g., inverted generational distance for multi-objective problems [85], distance to reference Pareto front).
- Iteration Tracking: Execute algorithms while recording selected metrics at regular intervals throughout the optimization process.
- Convergence Detection: Apply stopping criteria based on relative improvement thresholds or statistical tests for metric stabilization.
- Comparative Analysis: Plot convergence curves for different algorithms and analyze differences in convergence speed and solution quality.
- Statistical Validation: Perform significance tests on final solution qualities and convergence rates across multiple independent runs.
Table 1: Statistical Tests for Algorithm Performance Comparison
| Test Name | Variables Compared | When to Use | Assumptions | Effect Size Measures |
|---|---|---|---|---|
| Independent t-test | Means of 2 independent groups [86] | Comparing 2 algorithms on the same problem [86] | Normal distribution, equal variances [86] | Cohen's d [83] |
| ANOVA | Means of 3+ groups [86] | Comparing multiple algorithms simultaneously [86] | Normal distribution, homogeneity of variance [86] | Eta-squared (η²) [83] |
| Mann-Whitney U / Wilcoxon Rank-Sum | Distributions of 2 independent groups [86] | Non-normal data or ordinal rankings [86] | Independent observations | Rank-biserial correlation |
| Kruskal-Wallis H | Distributions of 3+ independent groups [86] | Multiple algorithm comparison with non-normal data [86] | Independent observations, ordinal data | Epsilon-squared (ε²) |
| Pearson's r | Linear relationship between 2 continuous variables [86] | Examining correlation between algorithm parameters and performance [86] | Linear relationship, normal distribution | Coefficient of determination (R²) |
Table 2: Convergence Metrics for Optimization Algorithms
| Metric Name | Application Context | Interpretation | Advantages | Limitations | ||||
|---|---|---|---|---|---|---|---|---|
| Inverted Generational Distance (IGD) | Multi-objective optimization [85] | Measures distance from reference Pareto front to obtained solutions | Comprehensive quality assessment | Requires reference Pareto front | ||||
| Constraint Violation (CV) | Constrained optimization [85] | Quantifies total violation of all constraints: CV(x)=∑j=1J | gj(x) | +∑k=1K | hk(x) | [85] | Direct feasibility measurement | Doesn't account for objective quality |
| Performance Profiles | Benchmarking across multiple problems | Probability an algorithm is within a factor τ of the best solution | Robust to outlier problems | Computational intensive | ||||
| Hypervolume Indicator | Multi-objective optimization | Volume of objective space dominated by solutions | Pareto-compliant, no need for reference front | Computational complexity increases with objectives |
Experimental Workflows and Relationships
Diagram 1: Statistical Testing Workflow
Diagram 2: Constrained Optimization Convergence Analysis
Research Reagent Solutions
| Resource Category | Specific Tools/Solutions | Primary Function | Application Context |
|---|---|---|---|
| Optimization Algorithms | NSGA-II, MOEA/D, SPEA2 [85] [87] | Multi-objective optimization core engines | Finding Pareto-optimal solutions for conflicting objectives |
| Constraint Handling Techniques | Penalty Functions, ε-Constraint, Stochastic Ranking [85] | Managing feasibility in constrained optimization | Ensuring solutions satisfy problem constraints |
| Statistical Analysis Packages | SciPy (Python), R Stats, MATLAB Statistics | Performing significance tests and effect size calculations | Validating performance differences between algorithms |
| Benchmark Problem Sets | CEC Competition Problems, ZDT, DTLZ, LSMOP | Standardized testing and validation | Comparative algorithm performance assessment |
| Performance Metrics | Inverted Generational Distance, Hypervolume, Spread [85] | Quantifying solution quality and diversity | Objective evaluation of optimization results |
| Visualization Tools | Matplotlib, Plotly, Tableau | Creating convergence plots and performance graphs | Interpreting and presenting optimization results |
Conclusion
Adaptive constraint handling techniques represent a paradigm shift in solving complex constrained optimization problems, moving beyond static penalty functions to dynamic, self-adjusting methodologies that respond to evolutionary state feedback. The integration of deep reinforcement learning enables intelligent CHT selection tailored to specific problem characteristics and optimization stages, while multi-stage frameworks and repair mechanisms provide robust strategies for navigating challenging constraint landscapes. For biomedical and clinical research, these advancements promise accelerated drug discovery through more efficient molecular optimization, clinical trial design, and treatment protocol development under complex biochemical and regulatory constraints. Future directions include developing domain-specific adaptive CHTs for pharmaceutical applications, enhancing interpretability of LLM-generated optimization strategies, and creating standardized validation frameworks tailored to biomedical constraint profiles. As adaptive CHTs continue to evolve, they will play an increasingly critical role in addressing the multifaceted optimization challenges inherent in personalized medicine and complex therapeutic development.
References
- 1. A Constrained Multi-Objective Optimization Algorithm with ... [https://www.mdpi.com/2227-7390/13/5/688]
- 2. A Benchmark-Suite of real-World constrained multi ... [https://www.sciencedirect.com/science/article/abs/pii/S2210650221001231]
- 3. CMOMO: a deep multi-objective optimization framework for ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12240737/]
- 4. Application of Constrained Optimization Methods in Health ... [https://www.sciencedirect.com/science/article/pii/S1098301518322009]
- 5. Adaptive multi-stage evolutionary search for constrained ... [https://link.springer.com/article/10.1007/s40747-024-01542-9]
- 6. Dynamic ε-multilevel hierarchy constraint optimization with ... [https://www.sciencedirect.com/science/article/abs/pii/S1568494623011900]
- 7. Constraint-tightening based adaptive two-stage ... [https://www.sciencedirect.com/science/article/abs/pii/S2210650225002950]
- 8. Adaptive Constraint Relaxation-Based Evolutionary ... [https://www.mdpi.com/2227-7390/12/19/3075]
- 9. DC-SHADE-IF: An infeasible–feasible regions constrained ... [https://www.sciencedirect.com/science/article/abs/pii/S0957417423005018]
- 10. Large Language Model Assisted Automated Algorithm ... [https://arxiv.org/html/2509.13251v2]
- 11. Computationally expensive constrained problems via ... [https://link.springer.com/article/10.1007/s40747-024-01745-0]
- 12. Convergence Rates of Constrained Expected Improvement [https://arxiv.org/html/2505.11323v1]
- 13. No free lunch theorem [https://en.wikipedia.org/wiki/No_free_lunch_theorem]
- 14. No Free Lunch Theorem for Machine Learning [https://www.machinelearningmastery.com/no-free-lunch-theorem-for-machine-learning/]
- 15. What is No Free Lunch Theorem [https://www.geeksforgeeks.org/machine-learning/what-is-no-free-lunch-theorem/]
- 16. No Free Lunch Theorem and Its Foundational Implications ... [https://medium.com/@adnanmasood/no-free-lunch-theorem-and-its-foundational-implications-for-algorithm-selection-in-artificial-5fc49c218d76]
- 17. The No Free Lunch Theorem, Kolmogorov Complexity, and ... [https://arxiv.org/html/2304.05366v2]
- 18. Evolutionary constrained optimization with hybrid ... [https://www.sciencedirect.com/science/article/abs/pii/S0957417422017006]
- 19. An evolutionary algorithm based on learning strategies and ... [https://www.sciencedirect.com/science/article/abs/pii/S2210650225003657]
- 20. A Generalized Framework for Multi-objective-based ... [https://link.springer.com/article/10.1007/s12555-024-0445-8]
- 21. Types of Constraints - MATLAB & Simulink [https://www.mathworks.com/help/optim/ug/types-of-constraints.html]
- 22. Equality and Inequality Constraints [https://mat.tepper.cmu.edu/classes/QUANT/NOTES/chap4/node6.html]
- 23. Balancing property optimization and constraint satisfaction ... [https://arxiv.org/html/2411.15183v1]
- 24. Constrained multi-objective optimization problems [https://www.sciencedirect.com/science/article/pii/S0950705124006324]
- 25. Evolutionary constrained multi-objective optimization [https://link.springer.com/article/10.1007/s44336-024-00006-5]
- 26. Two-Stage Archive Evolutionary Algorithm for Constrained ... [https://www.mdpi.com/2227-7390/13/3/470]
- 27. Constraint handling techniques for metaheuristics: a state- ... [https://link.springer.com/article/10.1007/s11081-022-09782-9]
- 28. Recht: a ranking-based ensemble constraint handling ... [https://ui.adsabs.harvard.edu/abs/2025INSAP.tmp...90M/abstract]
- 29. Designing Effective State Representations in ... [https://codesignal.com/learn/courses/advanced-rl-techniques-optimization-and-beyond/lessons/designing-effective-state-representations-in-reinforcement-learning]
- 30. Deep reinforcement learning assisted co-evolutionary ... [https://www.sciencedirect.com/science/article/abs/pii/S2210650223001608]
- 31. State-wise Constrained Policy Optimization [https://openreview.net/forum?id=NgK5etmhz9]
- 32. Two-stage graph attention networks and Q-learning based ... [https://link.springer.com/article/10.1007/s10489-025-06249-z]
- 33. Designing an adaptive learning framework for predicting ... [https://www.sciencedirect.com/science/article/abs/pii/S0952197624016300]
- 34. Optimal adaptive allocation using deep reinforcement ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC9298337/]
- 35. Deep Reinforcement Learning-Assisted Component Auto ... [https://arxiv.org/html/2509.11016v1]
- 36. Multi-surrogate framework with an adaptive selection ... [https://www.sciencedirect.com/science/article/pii/S199582262300225X]
- 37. Neural network-enabled discovery of mapping between ... [https://www.sciencedirect.com/science/article/abs/pii/S0950705123007827]
- 38. A stage-based adaptive penalty method for constrained ... [https://www.sciencedirect.com/science/article/abs/pii/S0957417424032184]
- 39. Utility of a dynamic termination criterion in the ZEST ... [https://www.sciencedirect.com/science/article/pii/S0042698902003966]
- 40. A new dual-population evolutionary algorithm leveraging ... [https://www.sciencedirect.com/science/article/abs/pii/S2210650225003098]
- 41. Dual-Population Cooperative Correlation Evolutionary ... [https://www.mdpi.com/2227-7390/13/9/1441]
- 42. A dual-population constrained multi-objective evolutionary ... [https://link.springer.com/article/10.1007/s40747-023-01042-2]
- 43. A dual-population coevolutionary algorithm for balancing ... [https://www.sciencedirect.com/science/article/abs/pii/S1568494624005441]
- 44. An ɛ-constrained multiobjective differential evolution with ... [https://www.sciencedirect.com/science/article/abs/pii/S1568494623012206]
- 45. Large Language Model Assisted Automated Algorithm ... [https://arxiv.org/abs/2509.13251]
- 46. Differential evolution improvement by adaptive ranking ... [https://link.springer.com/article/10.1007/s00500-023-08335-1]
- 47. On the Efficacy of Ensemble of Constraint Handling ... [https://www.mdpi.com/2227-7390/7/7/635]
- 48. A Coevolutionary Algorithm Based on Constraints ... [https://link.springer.com/article/10.1007/s44196-025-00830-7]
- 49. An individual adaptive evolution and regional collaboration ... [https://www.sciencedirect.com/science/article/abs/pii/S2210650225000835]
- 50. Adaptive constraint handling technique selection for ... [https://www.sciencedirect.com/science/article/abs/pii/S221065022400021X]
- 51. An Efficient Approach for Solving Expensive Constrained ... [https://arxiv.org/html/2405.13298v1]
- 52. Efficient constrained large-scale multi-objective ... [https://link.springer.com/article/10.1007/s10489-023-04663-9]
- 53. Handling Infeasibility in Optimization Models [https://www.decisionspot.com/post/handling-infeasibility-in-optimization-models]
- 54. Infeasibility, Unboundedness and Instability [https://www.fico.com/fico-xpress-optimization/docs/latest/solver/optimizer/HTML/chapter3.html]
- 55. Escaping Local Optima | SpringerLink [https://link.springer.com/chapter/10.1007/978-3-662-07807-5_6]
- 56. Escaping Local Optima in Multi-Agent Oriented Constraint Satisfaction | SpringerLink [https://link.springer.com/chapter/10.1007/978-0-85729-412-8_8]
- 57. An infeasible solutions diversity maintenance epsilon ... [https://link.springer.com/article/10.1007/s00500-021-05880-5]
- 58. A staged diversity enhancement method for constrained ... [https://www.sciencedirect.com/science/article/abs/pii/S0020025524009952]
- 59. Surrogate model optimization: a comparison case study ... [https://www.sciencedirect.com/science/article/pii/S0098135425002030]
- 60. Computational drug repurposing: approaches, evaluation ... [https://pubmed.ncbi.nlm.nih.gov/40102635/]
- 61. Application of computational methods in the drug discovery ... [https://www.sciencedirect.com/science/article/pii/S2211383525005179]
- 62. Surrogate-Based Optimization Techniques for Process ... [https://arxiv.org/html/2412.13948v1]
- 63. Methods to balance the exploration and exploitation in ... [https://www.sciencedirect.com/science/article/abs/pii/S0925231223010226]
- 64. Balancing exploration and exploitation with information ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC7654823/]
- 65. Scale-Adaptive Balancing of Exploration and Exploitation ... [https://arxiv.org/abs/2305.09840]
- 66. Framework of Ensemble Parmeter Adapted Evolutionary ... [https://www.preprints.org/manuscript/202208.0307]
- 67. Target Assignment for UAV Swarms: A Novel Genetic ... [https://www.mdpi.com/2504-446X/9/10/722]
- 68. An experimental study of adaptive control for evolutionary ... [https://www.sciencedirect.com/science/article/abs/pii/S1568494615003658]
- 69. CEC2020 Real-World Constrained Engineering ... [https://ieee-dataport.org/documents/cec2020-real-world-constrained-engineering-optimization-seven-problem-suite]
- 70. CEC 2009 Problem Suite (multi-objective, constrained and ... [https://esa.github.io/pagmo2/docs/cpp/problems/cec2009.html]
- 71. CEC2020 Real-World Constrained Engineering ... [https://data.mendeley.com/datasets/nvjkfdycpw/1]
- 72. Bibliographies: 'Constraint Handling Techniques' [https://www.grafiati.com/en/literature-selections/constraint-handling-techniques/]
- 73. Constrained optimization [https://en.wikipedia.org/wiki/Constrained_optimization]
- 74. Convergence Performance - an overview [https://www.sciencedirect.com/topics/computer-science/convergence-performance]
- 75. 13 Market Performance Metrics [https://www.caiso.com/content/monthly-market-performance/may-2023/market-performance-metrics-1.html]
- 76. Use a Troubleshooting Methodology for More Efficient IT ... [https://www.comptia.org/en-us/blog/use-a-troubleshooting-methodology-for-more-efficient-it-support/]
- 77. A Review on Constraint Handling Techniques for ... [https://link.springer.com/article/10.1007/s11831-022-09859-9]
- 78. On self-adaptive stochastic ranking in decomposition many ... [https://www.sciencedirect.com/science/article/abs/pii/S0925231221019251]
- 79. A Novel Ranking Scheme for the Performance Analysis ... [https://arxiv.org/html/2406.00154v1]
- 80. Guide to DOEs (Design of Experiments) - Instrumental [https://instrumental.com/build-better-handbook/guide-to-does]
- 81. Design and preliminary validation of a mobile application- ... [https://www.dovepress.com/design-and-preliminary-validation-of-a-mobile-application-based-expert-peer-reviewed-fulltext-article-MDER]
- 82. A Comprehensive Guide to Statistical Significance [https://www.statsig.com/perspectives/a-comprehensive-guide-to-statistical-significance]
- 83. Statistical significance [https://en.wikipedia.org/wiki/Statistical_significance]
- 84. Can Reinforcement Learning Solve Asymmetric Combinatorial ... [https://arxiv.org/html/2502.01252v1]
- 85. Adaptive constraint handling technique selection for ... [https://www.sciencedirect.com/science/article/pii/S221065022400021X]
- 86. Choosing the Right Statistical Test | Types & Examples [https://www.scribbr.com/statistics/statistical-tests/]
- 87. Inter-Algorithm Multiobjective Cooperation for Phylogenetic ... [https://pubmed.ncbi.nlm.nih.gov/32915754/]